Board Cyber Governance Best Practices. What Great Boards Do Differently in 2026
Board Cyber Governance Best Practices, set risk appetite, demand trend metrics, test incident readiness, and hold clear owners so cyber risk drops.


If you're on the board of directors, cyber risk isn't a cybersecurity "IT problem." It's business risk that demands effective risk management. It can hit revenue through fraud, cyber threats, and downtime, disrupt operations through stalled fulfillment or payroll, damage your brand through public loss of trust, and in some sectors it can put people's safety at risk.
Here's the hard part: most board conversations about security stop at updates. You hear about tools deployed, patches applied, and training completed. That's activity, not governance. Real governance shows up when you make decisions, accept tradeoffs, assign accountability, and demand proof that risk is going down.
This post breaks down Board Cyber Governance Best Practices in plain language, with examples you can use right away. You'll see what great boards do differently across four areas: decision-focused board oversight, a small set of meaningful metrics, incident readiness for the day something goes wrong, and smart use of outside leadership when the stakes rise.
Key takeaways you can use in your next board meeting
Ask for a one-page cyber dashboard tied to your top business services.
Agree on a clear enterprise risk appetite, including downtime, data breach, and data loss limits.
Require owners for each top cyber risk, not shared accountability.
Review exceptions and "accepted risks" as formal board decisions.
Demand trends over time, not one-time scores or busy metrics.
Schedule a board-level incident tabletop each year with real decisions.
Treat critical vendors as part of your attack surface for business operations, because they are.
Bring in independent cyber leadership when gaps persist or stakes spike.
What great boards do differently, they govern cyber like any other enterprise risk
Great boards don't try to run security. You set direction, define boundaries, and hold leaders accountable. Management executes under cybersecurity leadership, reports progress, and escalates when reality conflicts with plan.
Good governance has a few clear traits: explicit decisions, clear owners, a steady cadence, and evidence that actions reduced risk. You want fewer "we're working on it" updates, and more "we decided X, we funded Y, we accepted Z, and here's what changed."
In practice, boards often approve and review:
Risk appetite statements (what you will tolerate, and what you won't).
Funding priorities (what gets fixed first when resources are limited).
Accountability (who owns risk outcomes, not tasks).
Major exceptions (why you're accepting a gap, and for how long).
If you're not getting decision-ready material, you may need help shaping it. An experienced CISO advisor for board-level oversight with technology expertise, who is IT savvy, can translate technical status into board decisions, and help management bring you clean options with tradeoffs.
Make cyber risk decisions explicit, risk appetite, priorities, and tradeoffs
"Reasonable security" means nothing until you pin it to thresholds. Your job is to turn fuzzy comfort words into decisions the business can live with.
Start with a few plain limits, informed by data such as a governance survey. For example, how many hours of outage can you accept for payments, scheduling, dispatch, or customer login? What types of data loss are unacceptable, even once? Which issues must be fixed in 30 days, no matter what?
Use questions that force clarity without creating fear:
What's our maximum acceptable downtime for each critical service?
Which data types can never leave our control (even encrypted)?
What cyber vulnerabilities must be remediated in 30 days, and what can wait 90?
Where are we consciously accepting risk, and what's the expiry date?
If we cut one initiative this quarter, what risk goes up?
When you ask these, you move from "security reporting" to governance.
Put the right structure in place, committee coverage, cadence, and clear ownership
You need a structure that fits your company's size and risk. Some boards keep cyber oversight with the full board because it ties directly to strategy. Others place it with the audit committee or risk committees to go deeper more often. Either way works if ownership and cadence are clear.
A simple rhythm helps:
Monthly: a short metrics review, focused on trends and exceptions.
Quarterly: a deeper review of top risks, major changes, and funding.
Annually: a board tabletop exercise that tests decisions under pressure.
Ownership matters more than org charts. In most companies, the CEO owns enterprise risk, the CISO owns the security program, the CIO or CTO owns key systems, legal owns disclosure posture, and operations owns recovery priorities. "Ownership" means someone can commit resources, set deadlines, and explain outcomes to you without deflection.
The board's dashboard, the few metrics that show real cyber health
Boards often get flooded with numbers that don't answer board questions. A thousand people completed training is fine, but it doesn't tell you if your business can detect an intrusion fast, contain it, and recover.
Ask your cybersecurity professionals to report cyber health the same way you'd review financial health: a small set of indicators, tied to what the business runs on. That means mapping risk to services like point of sale, online checkout, call center, manufacturing lines, claims processing, or donor systems, not to security tools.
You'll get better reporting when leaders have a model to follow, like those used in the cybersecurity market. This is where practical CISO insights for executives and boards can help you standardize how risk is explained, so meetings become faster and more decisive.
If you can't see trends, owners, and exceptions on one page, you don't have a board dashboard yet. You have a status report.
Use a one-page cyber scorecard tied to critical services and crown jewels
A one-page scorecard forces focus. It also makes it harder to hide behind volume. Keep the format consistent every month so you can spot drift and patterns.
What belongs on the page:
Top 5 enterprise cyber risks (written in business impact terms).
The critical services affected, plus the "crown jewels" strategic assets data involved.
3 to 6 key cyber defenses that reduce those risks, with simple status.
Trend arrows (improving, stable, worsening) and a short reason.
Incident readiness status (backup health, recovery tests, key gaps).
Third-party exposure summary, focused on the most critical vendors.
Major initiatives and a short "what could slip" note.
Exceptions needing board decisions, with options and tradeoffs.
Consistency is the win. Your goal is fewer surprises, not prettier charts.
Ask for trends and targets, not perfect numbers
Some cyber metrics will be messy. That's normal. What you can demand is honesty, direction over time, and targets everyone agrees on.
Look for targets like "contain high-severity incidents within X hours," "recover critical services within Y hours," or "patch critical issues within Z days." Then ask for confidence levels, because false precision is a quiet risk.
Three red flags should stop you:
Always-green cybersecurity dashboards, even after major change or growth.
No backlog, no exceptions, and no uncomfortable tradeoffs.
"We're compliant" used as a substitute for measured risk reduction.
When you see these, ask what changed in the business, what new exposures came with it, and which risks are being deferred to fund something else.
Resilience is the goal, be ready for the day things go wrong
Prevention matters, but it will never be perfect. A board that only funds prevention is betting the company on best-case outcomes. Great boards plan for failure the same way they plan for supply chain shocks, a sudden loss of a key facility, or a data breach.
Incident readiness has three board-level angles: decision authority, communications, and recovery priorities. Before a crisis, you should pre-agree on a response plan for decision points that become messy under stress, like your stance on ransom demands, disclosure triggers, and who can take systems offline to stop spread.
This is also where trust gets earned. Customers and regulators judge you less on whether you were attacked, and more on how you behaved afterward. If you want a clear model for that posture, outside experts focused on resilience and transparency can help you set expectations that match your values and your obligations.
Run a board-level incident tabletop that tests decisions, not slides
A tabletop fails when it becomes theater. You don't need more slides. You need a timed scenario that forces hard calls with limited information.
A simple format works well:
A realistic cyber risk scenario tied to your business (ransomware, vendor breach, data exposure).
Timed injects every 10 to 15 minutes (new facts, rumors, regulator notice).
A decision log capturing who approved what, and why.
A draft external statement written during the exercise, not after.
An after-action report with owners, dates, and a re-test plan.
Make sure the right people are in the room: CEO, CISO, legal, communications, operations, and the executive who owns the most critical service. During the exercise, you should practice approvals, customer posture, regulator posture, and when to shut something down to protect the whole enterprise.
Treat third parties and critical vendors like part of your attack surface
Vendor incidents become your incidents because your data, workflows, uptime, and business operations depend on them. If a payroll provider goes down, your workforce feels it. If a claims platform is breached, your customers blame you, not the vendor.
Keep oversight practical. Ask management to tier vendors (critical, important, routine), set minimum controls for each tier, and confirm breach notification timelines in contracts. In addition, require a backup plan for each critical vendor, plus a view of concentration risk (too much dependence on one provider, one region, or one admin model).
You don't need legal jargon to govern this. You need three answers: which vendors can stop the business, what you require of them, and how fast you can switch or operate without them.
When you need outside help, how great boards use experienced cyber leadership
Sometimes you need an independent voice, even with strong leaders in place. That moment often comes during a major incident, a rapid growth phase, an acquisition, regulator pressure, board recruitment, executive search, a first-time CISO transition or succession planning, or repeated audit findings that don't seem to move.
Great boards use outside cyber leadership to raise the quality of decisions, not to generate more documents. The right advisor can translate risk into business impact, pressure-test plans, and help management execute without creating drag.
If you need short-term, high-trust leadership, consider bringing in an experienced CISO for hire for high-stakes periods. That model can stabilize priorities, tighten reporting, and improve readiness while you build long-term capacity with a cyber savvy board director candidate.
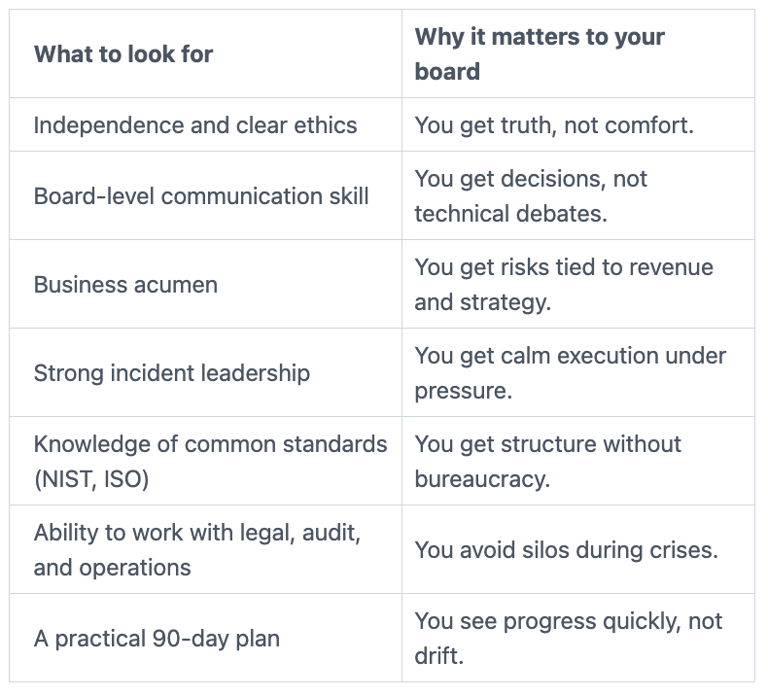
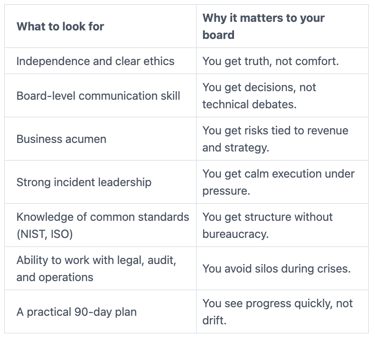
A simple checklist for picking the right board-level cyber advisor
This table gives you a fast way to screen for fit.
Then use a few direct interview questions as the hiring manager in talent acquisition:
How will you measure progress in 90 days?
Tell us about a time you disagreed with leadership, what happened next?
How do you work with legal, audit, and operations during an incident?
What dashboards have you used that boards actually like?
What would you stop doing first if resources are tight?
Conclusion: Better cyber governance starts with better board decisions
Great boards don't "learn cybersecurity." You govern it. That means you set cyber risk appetite, demand a small set of meaningful trends, and prepare for the day the plan gets tested. When you do those three things, you protect revenue, operations, and trust, without turning board meetings into technical reviews.
Here's a simple 30-day action plan to help your board become board ready that you can start now:
Agree on downtime and data loss limits, as well as capital allocation guidelines, for your top services.
Approve a one-page dashboard format with owners and trend targets, to be shared through a board portal with directors.
Schedule an incident tabletop and require an after-action plan.
Review your top vendor list, tier it, and confirm notification terms.
Confirm who can take systems offline, and who approves disclosures.
Quick FAQ: board cyber oversight
How often should the board discuss cyber risk?
You should review a short dashboard monthly or at each meeting. Then hold a deeper quarterly review tied to business changes and top risks.
Should cyber oversight sit with the full board or a committee?
Either can work if the cadence is real and owners are clear. Many boards use the audit committee or risk committees for collaborative oversight and depth, with key decisions brought to the full board.
What's the most common board mistake with cyber dashboards?
You accept activity metrics as proof of reduced risk. Ask instead for outcomes, trends, exceptions, and regulatory compliance red flags that require decisions.
How do you know your incident plan is real?
Run a tabletop that forces approvals and communications under time pressure. If owners, timelines, and messages aren't clear, the plan isn't ready.
If you want help strengthening oversight and execution, work with someone certified to lead complex cybersecurity leadership and transformation work so your board of directors gets clearer decisions, steadier progress, and fewer surprises as a strategic business enabler.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
