CISO Transition Support. How to Hand Off Risk Without Losing Control
CISO Transition Support helps you hand off risk with clear owners, open-loops lists, and a 30 to 60-day cadence, so oversight stays steady.


A Chief Information Security Officer (CISO) transition can feel like changing pilots mid-flight. The plane keeps moving, yet your view of risk management can blur fast. Decisions get made in side conversations, exceptions live in old tickets, and open incidents sit in someone's inbox. Then, weeks later, surprises show up as audit findings, outages, or uncomfortable board questions.
"Handing off risk" in the context of succession planning isn't about transferring a spreadsheet. It's about transferring ownership, visibility, and decision authority so the business keeps making good calls. "Losing control" looks like stalled projects, unknown exposures, duplicated work, and unclear accountabilities when something breaks.
In February 2026, regulators, customers, and partners still expect steady oversight, even during leadership change. This practical CISO Transition Support playbook shows you how to stabilize the handoff, ensure leadership continuity, and keep control in the first 30 to 60 days.
Key takeaways you can use in your next CISO transition
These form a practical Transition Plan to ensure a seamless handover.
Freeze and document all risk exceptions (including "temporary" ones that became permanent).
Confirm who can accept risk and who pays to reduce it, then write it down.
Publish an "open loops" list for incidents, investigations, and post-incident actions.
Create a one-page risk snapshot for knowledge transfer with owners, due dates, and decisions needed.
Set a weekly executive checkpoint so risk questions don't wait a month.
Run a biweekly risk decision meeting to approve exceptions and fund fixes.
Align audit and regulatory compliance deadlines to named owners, with next dates.
Protect delivery speed and business continuity by time-boxing reviews and using short pre-reads.
Start by locking down what "risk" means here and who can accept it
Before you hand anything off, you need a shared definition of "risk." Otherwise, one leader talks about vulnerabilities while another worries about regulatory exposure. Both are right, yet the transition fails when you treat risk as a single technical problem.
In your org, risk usually comes in four buckets:
First, technology risk: known vulnerabilities, weak identity controls, legacy systems, and risky configurations.
Next, third-party risk: vendors with access to data, outsourced IT, SaaS tools bought on a credit card, and partners you depend on for uptime.
Then, compliance and legal risk: audit gaps, contract commitments, privacy obligations, and reporting timelines that don't pause for leadership change.
Finally, operational and trust risk: fragile processes, unclear incident roles, poor backups, weak change control, and customer promises that security supports but doesn't own.
These buckets form the foundation of your Cybersecurity Strategy, ensuring alignment with the overall security vision.
Your goal is not perfect documentation. Your goal is clear decisions. During a transition, the business must still answer basic questions: Are we accepting this risk, reducing it, transferring it (insurance, contracts), or avoiding it (changing the plan)? If nobody can answer quickly, you don't have control, you have hope.
A simple move helps: define risk in plain terms, tie it to business impact, and assign a decision owner. That owner may not be the Chief Information Security Officer. In many companies, the "real" risk owner sits in product, operations, finance, or legal.
Control comes from decision rights and follow-through, not from a bigger risk register. This builds Organizational Resilience across the business.
Map the real decision rights before you hand anything off
Start by mapping who approves risk acceptance, who funds remediation, and who owns outcomes when things go wrong. You can do this without a new framework. A plain-language RACI-style view in prose is enough to drive Stakeholder Engagement:
The CEO (or board sponsor) sets risk appetite and breaks ties.
The COO owns operational continuity and cross-team execution.
The CTO owns engineering priorities and technical debt tradeoffs, providing Technical Leadership.
The GC (general counsel) owns legal exposure, privilege strategy, and notifications.
The Privacy lead owns personal data handling rules and regulatory response.
IT owns endpoint, identity operations, and core service reliability.
Security owns risk clarity, control design, and independent challenge.
If your CISO reporting line changes (for example, moving under the CIO), call it out early. Otherwise, teams will guess who has authority, and "approval" will become a rumor. Put the updated decision path in writing, then share it in the first week.
If you need stability while that structure settles, it helps to see how an experienced CISO for hire can stabilize a transition and keep decisions moving.
Create a one-page risk snapshot that your Board of Directors will actually read
The Board of Directors doesn't need a 40-page slide deck during a handoff. They need a one-page view that answers: what's changing, what could hurt the business, and what decision is required. This format supports clear Executive Communication.
Use this simple format and keep it honest:
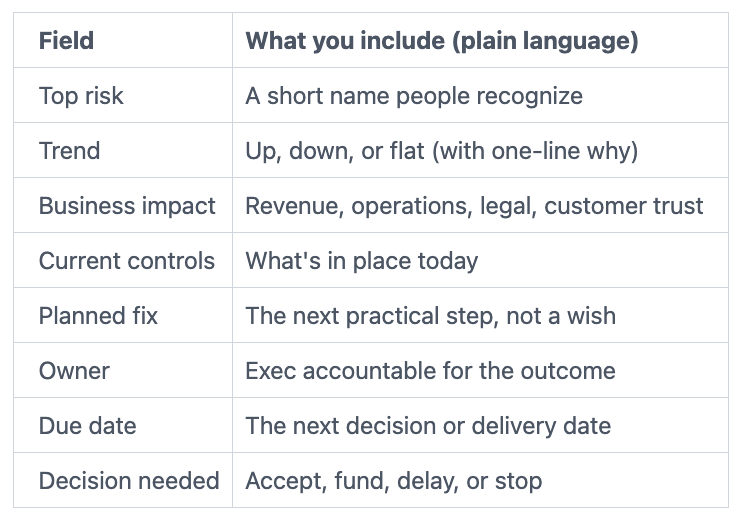
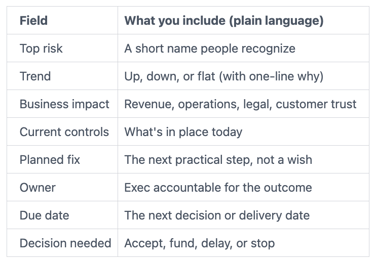
Add a red, amber, green status, but don't hide uncertainty. If you don't know, say so, then give the next date when you will know. That single habit cuts surprises later.
If you want a simple way to connect risk work to customer confidence, use a practical lens on building digital trust when you write the snapshot.
Build a clean handoff package, so the next CISO does not inherit surprises
A good handoff package facilitates effective Knowledge Transfer, like a well-labeled circuit breaker panel. You're not rewriting the house wiring, you're making it safe for the next Chief Information Security Officer to operate it.
Focus on continuity of decisions and execution. That means your handoff should make it easy to answer, within minutes, these questions:
What incidents are open right now? What commitments have you made to customers or regulators? Which risks are accepted, and until when? What's the security roadmap, and which parts are funded? Which vendors matter, and what renewals are coming? Which audits are scheduled, and what evidence is due?
Keep it tight. If you build a perfect binder, you'll burn time and still miss the parts that matter. Instead, ship a minimum set of assets that keeps control:
A current risk register (even if rough), with owners and next dates.
An exceptions log with expirations and approvals.
A short security roadmap tied to business outcomes and budgets.
A view of budget and headcount, including open reqs and key skills gaps.
Access Revocation and Security Separation status for departing personnel, legacy accounts, and the offboarding leader.
A list of critical tools and vendors, with contract dates and service owners.
A calendar of audit and regulatory obligations, with a named lead for each.
Write it like you're handing it to someone smart who has no context. Because that's what a new leader feels like on day three.
Capture the "open loops" list: incidents, investigations, and near misses
Open loops are where control disappears. If your transition drops one thread, it's usually here.
Your open loops list should include:
Active Incident Response activities and their current status, ongoing investigations and forensics findings, post-incident actions not completed, cyber insurance notifications, any law enforcement touches, customer or partner commitments, and planned disclosures (even if only being discussed). Also track near misses that keep repeating, because they often point to weak controls.
Add one simple rule: nothing closes without an owner and a next date. Closure is a decision, not a feeling.
If you want practical thinking that connects incident readiness to business resilience, read CISO insights on resilience and incident readiness and mirror that mindset in your open loops list.
Freeze, review, and reapprove risk exceptions and compensating controls
Risk exceptions are where hidden exposure lives in your Cybersecurity Posture. They're also where teams learn that "no" is temporary if they wait long enough. During a transition, that pattern gets worse unless you stop it.
Freeze new exceptions for a short window (often one to two weeks), except for true business-critical needs. Then review what you already have. For each exception, capture a minimum set of facts:
Exception owner (a person, not a team)
Reason (business rationale, not "we were busy")
Scope (systems, data types, users, regions)
Compensating control (what reduces the risk today)
Expiry date (required, not optional)
Monitoring (how you'll notice failure)
Approver (who accepted the risk)
Inherited "permanent" exceptions need a reset. Convert them into time-bound approvals with a new decision date. If the business still wants the exception, fine, but make that choice visible and current. Control improves when leaders re-own the decision.
Keep control in the first 30 to 60 days with a simple transition operating rhythm
You keep control by creating a rhythm that supports knowledge transfer and makes risk decisions routine again. Without it, every choice becomes urgent, emotional, and delayed. Meanwhile, delivery teams keep shipping, and risk drifts in the background.
A lightweight cadence works because it reduces the time between "we noticed a risk" and "someone decided what to do." It also keeps the board out of the weeds while still informed.
Here's a simple operating rhythm you can run whether you have a permanent Chief Information Security Officer, an Interim CISO, or shared coverage:
Weekly executive checkpoint (30 minutes): the top risks, open incidents, and any decisions blocked.
Biweekly risk decision meeting (45 to 60 minutes): exceptions, funding asks, and major change reviews.
Monthly board or committee summary (one page): top risks, trend, and decisions needed.
Keep pre-reads short. Two pages is plenty. Also time-box discussion and park deep technical debates for follow-up with owners.
To avoid slowing delivery teams and ensure business continuity, don't turn this into a new approval maze. Instead, set thresholds. For example, only changes that touch regulated data, identity controls, or critical uptime paths come to the decision meeting.
Run a short decision cadence that clears blockers fast
A decision cadence is not a status meeting. It's where you remove friction, address crisis management, and make clear calls.
Use a repeating agenda:
Start with the top three risks needing a decision. Move next to funding asks tied to those risks. Then review exception approvals and expirations. After that, cover major change reviews (cloud moves, identity changes, new vendors). End with vendor renewals and incident posture (are you stable, strained, or in active response?).
Send pre-reads 24 hours ahead. Ask owners to write the decision they want and the tradeoff. During the meeting, you're aiming for a yes, no, or "come back on this date with these facts."
If you're building this muscle as a new leader, it helps to see what it looks like to keep learning and adapting as a modern CISO and apply that same discipline to your transition rhythm.
Know when to bring in outside transition support
Sometimes your internal team can run the transition. Other times, you need outside help because the risk is too high or the window is too tight.
Common triggers include a leadership gap, active regulatory pressure such as SEC Regulations, a recent incident, a major cloud migration, an M&A event, or a security program that has stalled and lost executive trust. Another strong signal is when nobody can name the top five risks with confidence.
In week one, you should expect outside support to triage and stabilize: confirm decision rights, get a real view of open loops, and produce a board-ready risk snapshot. By month two, that support should shift to governance reset and roadmap clarity: align funding, set metrics people respect, rebuild operating cadence, and foster cybersecurity culture.
If you need that kind of help, start with how to engage a CISO advisor for CISO Transition Support so you can move quickly without adding confusion.
FAQs about CISO Transition Support and risk handoffs
What is the fastest way to reduce risk during a CISO transition?
Do three things immediately to bolster Business Continuity through effective Risk Management. First, confirm decision rights, so risk acceptance doesn't float. Next, document open incidents and exceptions in one place, with owners and next dates. Then set a weekly decision cadence with the CEO or board sponsor, so actions don't stall.
How do you hand off risk without creating a paperwork project?
Build a minimum viable handoff first. Start with a one-page risk snapshot, an open loops list, and an exception register. After that, add detail only where decisions depend on it, for example regulatory deadlines or customer commitments.
Should the board be involved in the transition, and how much?
Yes, but keep it focused. The Board of Directors needs top risks, trend, and decisions required. It doesn't need tool details, org charts, or vulnerability counts without context. A monthly one-page update works well, with an extra update if an incident is active.
How long should a CISO transition plan take to build?
You can stabilize and document the essentials in one to two weeks if you focus, which is especially useful for a First-time CISO. Expect 30 to 60 days to reset the roadmap and governance when onboarding a successor, because budgets, priorities, ownership, and Emerging Technologies often need real negotiation. Speed comes from clarity, not from long documents.
Conclusion
You don't keep control during a Chief Information Security Officer change by trying to know everything. You keep control by making decision rights explicit, keeping open work visible to preserve institutional knowledge, and running a steady cadence that forces choices into the open. Treat the transition like a change program, with a focus on leadership continuity, stakeholder engagement, executive communication, and organizational resilience; include owners, dates, and crisp outputs that executives can read in one sitting.
If the stakes are high in crisis management, don't try to muscle through alone. Get targeted support to stabilize the handoff through robust security controls, align leadership, and keep trust intact. Factor in the full executive lifecycle, including administrative offboarding and severance package details. When you're evaluating outside help, look for credentials that support trusted executive leadership and a track record of shaping cybersecurity strategy, bolstering cybersecurity posture, ensuring regulatory compliance, and positioning security as a business enabler without slowing the business.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
