The 12 Cyber Risk Questions Every Audit Committee Should Ask Before Approving the Annual Plan (Plus a One-Page Agenda Template)
Use Audit Committee Cyber Risk Questions to approve an annual cyber plan that cuts real business harm, plus a one-page agenda you can reuse.


You're about to approve an annual plan that mixes tech spend, compliance work, and major change to address cybersecurity risk. The deck looks busy. The milestones look neat. Yet the real risk isn't that the plan is missing tasks. It's that you approve a plan that doesn't reduce the most likely business harm.
Cyber plans often drift into activity, while your actual exposure stays the same despite board oversight. Meanwhile, the business keeps shipping new products, changing vendors, migrating systems, and pushing more work through the same people without effective risk management.
This article gives you 12 Audit Committee Cyber Risk Questions you can ask in a single meeting, without turning the audit committee into a technical review board. You'll also get a copy-ready, one-page agenda template you can reuse every year, so your plan approval meeting produces clear decisions, not vague comfort.
Key takeaways you can use in your next audit committee meeting
You'll name the top cybersecurity risks in business terms (money, downtime, legal exposure including disclosure compliance, trust), not tool terms.
You'll confirm risk ownership (who is on the hook) and what choices require board input.
You'll force clarity on what will be stopped or delayed so the plan stays realistic.
You'll connect security work to business goals, like faster delivery, fewer outages, or smoother audits.
You'll identify which risks you are accepting, reducing, or transferring this year to strengthen cyber resilience, and document it plainly.
You'll agree on 3 to 5 measurable outcomes for security performance so you can tell, by year end, what's truly better.
You'll walk out with follow-ups and deadlines, instead of "we'll circle back" notes.
The 12 Audit Committee Cyber Risk Questions to ask before you approve the annual plan
You're not trying to run security. You're trying to approve a plan that reduces the cybersecurity risk your organization is most likely to face. Use these questions to make that reduction visible.
Risk and accountability questions that clarify what you are really approving
1) What are the top 3 to 5 cyber risks to the business this year, stated as impact?
Why it matters: If you can't name the risks beyond vulnerabilities, you can't judge the plan.
Strong answer sounds like: "Ransomware could stop order fulfillment for 3 days," or "A vendor breach could expose customer data and trigger notifications."
Red flag: A list of vulnerabilities, tools, or "we're doing zero trust."
Decision or follow-up: Ask for a one-page risk summary with likelihood, impact, and a plain-language scenario.
2) Which risks are we accepting, and what is our risk appetite in practical terms?
Why it matters: Every plan contains tradeoffs. If you don't choose them, you inherit them.
Strong answer sounds like: "We accept low-impact phishing risk, but we won't accept a week of downtime in core operations."
Red flag: "Our appetite is low" with no thresholds.
Decision or follow-up: Require thresholds, such as maximum tolerable outage hours, data types you won't risk, and dollar loss bands.
3) Who owns each top risk, and who decides when to escalate to the board?
Why it matters: When incidents hit, confusion wastes time. Time becomes cost.
Strong answer sounds like: Named executives own each top cybersecurity risk (CFO for payment risk, COO for operational downtime, CIO for platforms), with escalation triggers.
Red flag: "Security owns it," or "IT owns everything."
Decision or follow-up: Approve decision rights and escalation thresholds, then ask management to publish them.
4) What will we stop, delay, or de-scope to make the plan achievable?
Why it matters: Overcommitted plans fail quietly, then fail loudly during an event.
Strong answer sounds like: "We're pausing two low-value reports to fund identity fixes," or "We're delaying a non-critical tool rollout."
Red flag: "We can do it all," or "We'll just work harder."
Decision or follow-up: Request a prioritized list with capacity assumptions, then approve the top priorities only.
If the plan can't say what it won't do, it's not a plan. It's a wish list.
Exposure questions that connect cyber risk to real business harm
5) What are our "crown jewels," and how does the plan reduce their exposure?
Why it matters: Protection should follow value. Otherwise, you spend evenly and protect unevenly.
Strong answer sounds like: A short list (revenue systems, patient data, pricing models, donor database) with specific controls and expected risk reduction.
Red flag: "Everything is critical," because then nothing is prioritized.
Decision or follow-up: Ask for a crown-jewel map that includes who uses it, where it lives, and the top abuse paths.
6) Which third parties could hurt us most, and what's our concentration risk?
Why it matters: Your biggest incident may start in someone else's environment.
Strong answer sounds like: "Our payroll provider and cloud identity provider represent our highest third-party risk, including supply chain dependencies, and are high-impact single points of failure," plus a plan for contract terms, monitoring, and fallback options.
Red flag: A vendor questionnaire program that doesn't change decisions.
Decision or follow-up: Require a top-10 critical vendor list, plus what you'll do if any one of them is down for 72 hours.
7) How are we reducing identity and access risk, especially for admins and remote access?
Why it matters: Most serious attacks rely on stolen access, not fancy exploits.
Strong answer sounds like: "We will cut standing admin access, enforce phishing-resistant MFA for privileged roles, and tighten vendor remote access."
Red flag: "We have MFA" without coverage details (who, where, and what type).
Decision or follow-up: Ask for a coverage report: percent of privileged accounts protected, percent of critical apps behind strong authentication, and the timeline to strengthen our cybersecurity posture.
8) How quickly can we detect and contain an attack, and what will improve this year?
Why it matters: The longer an attacker stays, the more data leaves, and the bigger the bill gets.
Strong answer sounds like: Current detection and containment times, top gaps, and a specific improvement target tied to fewer business-impact hours.
Red flag: "We monitor 24/7" with no measured response times.
Decision or follow-up: Request baseline numbers (even if imperfect), then approve a year-end target and evidence expectations.
For more board-ready ways to keep reporting clear and decision-focused, review these audit committee cyber oversight briefings.
Readiness and performance questions that prove the plan will work
9) Are we ready to run incident response with legal, comms, and operations at the table?
Why it matters: A technical response without legal and comms creates avoidable exposure.
Strong answer sounds like: A named incident leadership team, on-call expectations, outside counsel plan, and a communications approach for customers and regulators.
Red flag: "IT handles incidents," or "We'll call someone if it happens."
Decision or follow-up: Ask for an incident roles chart and a contact roster, and confirm who has authority to make time-sensitive calls.
10) Do our recovery objectives match business reality, and have we tested them?
Why it matters: Backups aren't recovery. Recovery is meeting business time needs under stress.
Strong answer sounds like: Clear RTO and RPO for the most critical services, plus results from recovery tests and fixes planned this year.
Red flag: "We back up everything nightly," with no proof of restore at scale.
Decision or follow-up: Require at least one full restore test for a critical service, with a dated report and lessons learned to bolster business continuity.
11) What did our last tabletop exercise reveal, and what changed because of it?
Why it matters: Exercises are only useful if they change behavior and reduce confusion.
Strong answer sounds like: "We found decision delays around shutdown authority, so we pre-approved criteria and practiced it."
Red flag: Tabletop slides, no after-action report, no owners.
Decision or follow-up: Approve two executive-level tabletop exercises per year (one ransomware-style, one vendor outage), and require tracked actions.
12) By year end, what will be measurably better, and how will we prove it?
Why it matters: Plans should produce outcomes you can inspect. Activity metrics hide risk.
Strong answer sounds like: "Phishing-resistant MFA for all admins," "restore critical service in under X hours," "reduced privileged accounts by Y%," or "contract terms updated for top vendors."
Red flag: Only counting training completion, tickets closed, or tools purchased.
Decision or follow-up: Approve 3 to 5 outcome metrics as key performance indicators, plus quarterly evidence (screenshots, test results, audit artifacts, or independent validation).
Turn the questions into a one-page annual plan approval agenda you can run in 45 minutes
A tight agenda keeps you out of technical weeds and forces decisions. Use this template as your annual reset, then reuse it each year with updated inputs.
Meeting goal (say this out loud): Approve an annual cyber plan that reduces the most likely business harm, with clear owners, tradeoffs, and measurable outcomes.
Pre-reads (distributed 48 hours prior, one page each when possible):
Risk register summary (top 5 risks, changes since last quarter)
Last year plan: committed vs delivered, and why gaps occurred
Incident and near-miss summary (what happened, business impact, lessons)
Third-party risk snapshot (top 10 critical vendors, concentration points)
Metrics dashboard (3 to 5 trend metrics, with targets)
Major business and tech changes that shift risk (migrations, M&A, new channels, financial reporting)
45-minute flow (time-boxed):
5 min, Context: What changed in the business, threat trends, regulatory trends, and key assumptions.
10 min, Top risks: Review the 3 to 5 risks and confirm risk appetite.
10 min, Plan choices and tradeoffs: What you fund, what you de-scope, and why.
10 min, Readiness and recovery: Incident roles, tabletop schedule, RTO/RPO testing plan.
5 min, Metrics: Approve outcome metrics and quarterly evidence expectations.
5 min, Approvals: Record decisions, owners, deadlines, and any conditions.
Decisions and actions to record (keep it brief):
Top risks accepted vs reduced vs transferred (plain language)
Budget changes and what they buy (risk reduction, not activity)
Approved outcome metrics and year-end targets
Follow-ups required, owners, and due dates
When you want a neutral facilitator to keep this meeting decision-focused, consider working with a CISO advisor.
Pre-reads that keep you out of the weeds
Ask for brevity, not volume. A strong team can explain risk on one page. If you receive an 80-slide deck, you've already lost the meeting.
Request pre-reads that answer three things: what changed, what matters most, and what decisions you need to make, connecting the cyber plan to the broader internal audit function. The risk register summary should read like a business memo. The metrics page should show trends, not a pile of counts. The incident summary should state cost, downtime, customer impact, and what changed afterward.
If management can't compress the story, ask them to try again. That work often surfaces unclear ownership and fuzzy priorities before you approve anything.
Decision checklist so you leave with clear approvals, not vague comfort
Capture decisions in the minutes using simple language that holds up later. You're creating a record of board oversight, not a technical artifact.
Risk acceptance statement: "The committee accepts the risk of X scenario through (date) because (reason), with these compensating actions (if any)."
Funding decision: "Approved $X for Y outcome, and deferred Z work."
Quarterly metrics: Choose 3 to 5 measures with targets and evidence, including internal controls.
Accountability: Name an executive owner per top risk and per major initiative.
Follow-ups: List due dates for items like recovery testing results, vendor contract updates, and exercise after-action reports.
The minutes should show what you decided, why you decided it, and who owns the next move.
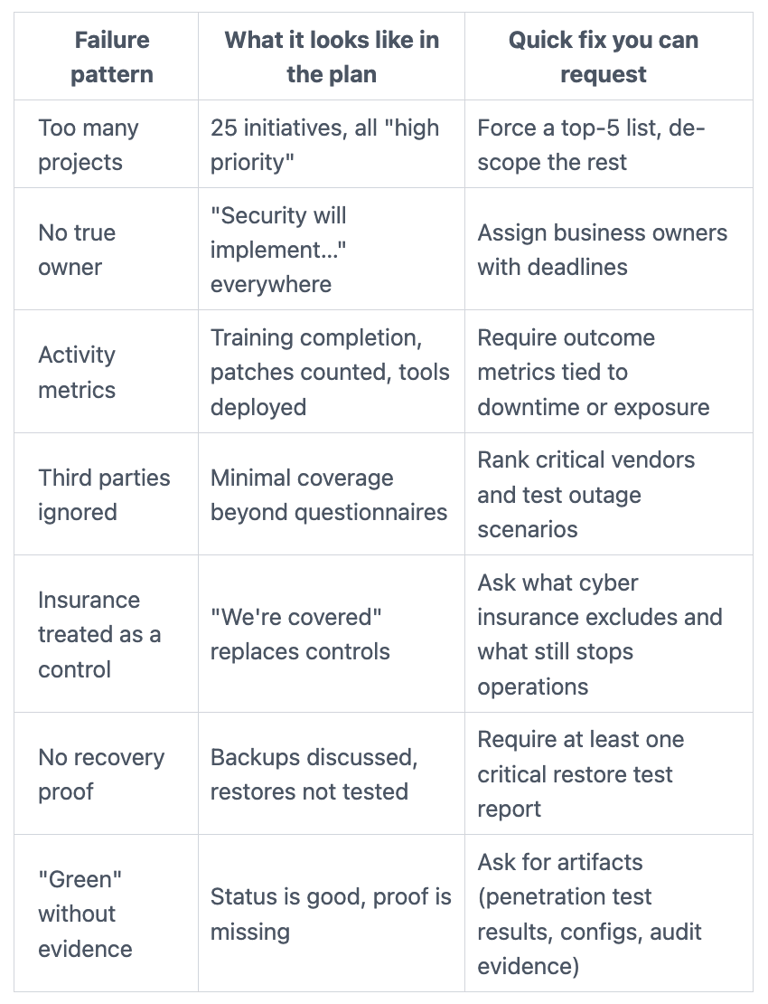
Common failure patterns that make an annual cyber plan look good but fail in real life
Some plans fail because they're weak. Others fail because they're busy. You can spot both by looking for a mismatch between the work list and the harm you fear.
Here are practical failure patterns, plus a fix you can request immediately:
A quick gut-check: does the plan reduce risk or just add tasks?
Run one simple test: If this plan succeeds, what bad outcome becomes less likely, or less damaging? If nobody can answer in one sentence, the plan is task-heavy.
Ask for before-and-after statements. For example, "Today we'd need 5 days to restore order processing, by year end it will be 24 hours." Then stop work that doesn't move those statements. You're not cutting security, you're cutting noise.
If you need outside perspective to reset scope, owners, and proof, an experienced CISO board oversight strategies approach can help you get to a plan that holds up under pressure.
FAQs audit committees ask about cyber risk plan approval
How many cyber metrics should you track? Keep it to 3 to 5. Track trends and targets, not dozens of counts.
How do you talk about risk appetite without sounding technical? Use thresholds: max downtime for critical services, which data types you won't risk, and financial loss bands.
What if management can't answer these questions in the meeting? Pause approval for the unclear items. Ask for a one-page follow-up within two weeks.
How do you judge a cyber budget request? Tie dollars to reduced harm. Ask what downtime, legal exposure, or fraud risk drops because of the spend.
How often should you review the plan? Quarterly is usually right. Review progress, metrics, and major changes in business or vendors.
What if new regulations appear mid-year? Ask what changes to scope, timeline, and funding are needed, then decide what gets de-scoped to make room.
What evidence should you ask for, beyond slides? Restore test results, tabletop after-action reports, access coverage reports, and vendor contract clauses for key providers.
When should you bring in independent help? When ownership is unclear, metrics don't exist, or incidents keep repeating. A digital trust expert on board cyber risks can give you an outside view without turning it into a months-long project.
Conclusion
Approving the annual cyber plan is one of your clearest moments of influence. When you ask the right questions, you get better tradeoffs, fewer surprises, and a plan that reduces real harm, not just busywork.
Reuse the one-page agenda each year, and keep quarterly oversight focused on a small set of outcome metrics. That rhythm helps you spot drift early, before drift turns into downtime, legal exposure, or lost customer trust.
If risk ownership, decision rights, or proof still feel fuzzy, schedule a focused working session before you approve the final plan. Strong oversight is calm, documented, and measurable, and it's easier with leaders who are certified frameworks for board cyber questions and can translate risk into decisions.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
