Cybersecurity Program Assessment Checklist: What to Review First
Use this cybersecurity program assessment checklist to spot top risks fast, verify identity, backups, and incident roles, then build a 90-day plan.

You don't need a full audit to get control of your security posture. You need a cybersecurity program assessment that answers a few hard questions fast, in a way you can defend in information security leadership meetings.
If you're a CEO, founder, or board member, your real problem isn't a lack of tools. It's limited time and attention. When security reviews start with tooling and policies, you get noise, not decisions. When they start with what can actually hurt the business, you get clarity.
"Good" is simple to define. You can explain your top risks in plain language, show evidence the basics work, and point to a clear 90-day plan with owners and dates. The order matters because if you review things out of sequence, you'll spend your best hours debating details that don't change risk. If you want an outside view to gauge your security program maturity and compress the timeline, you can start by clarifying scope and expectations through https://tysonmartin.com/engage-ciso-advisor.
Key takeaways you can use in the next 30 minutes
These risk management takeaways deliver strategic actions you can implement immediately.
Start with your crown jewels, then name the top loss scenarios that could shut you down.
Verify identity and access controls with evidence, not promises (especially admin access).
Validate backup and recovery following best practices by reviewing restore tests, not backup job "success" rates.
Confirm incident response roles, decision rights, and board escalation triggers before a crisis hits.
Review third-party risk based on business criticality, not vendor paperwork volume.
Use leadership-ready metrics you can inspect, not vanity dashboards (https://tysonmartin.com/the-hidden-value-of-cyber-metrics).
Step one, confirm what you are protecting and what could take you down
Think of this step like labeling the breakers in your electrical panel during your initial risk assessment. If you don't know what feeds what, you'll panic in the dark and flip the wrong switches.
Start by framing scope in business terms through a risk assessment. What services must stay up? What data must stay controlled? What dependencies would turn a "security issue" into a revenue issue, a safety issue, an operational risk, or a trust issue?
You're aiming for two outputs you can say out loud:
"These are the few things we can't afford to lose."
"These are the most likely ways we'd lose them."
That's also where materiality starts to become real. A minor incident in a test environment is annoying. The same event in identity systems, payments, or patient care can become a board topic in hours.
List your crown jewels in business language, not in system names for your information systems
Pick 5 to 10 critical processes, not 50 applications. Use plain categories like revenue intake, order fulfillment, patient care, manufacturing, donor operations, payroll, customer support, or core product delivery to address technology-related risks.
For each process, tie it to:
The data involved (PII, PHI, payment data, IP, donor data, employee data).
The systems that enable it (keep it short, a few key platforms).
The teams required (operations, finance, IT, product, third parties).
The "failure cost" in downtime, cash, legal exposure, or customer trust.
A quick rule: if downtime or data loss triggers regulatory notice, contractual penalties, safety risk, or headline risk, it's a crown jewel.
Name your most likely loss scenarios, then map them to controls in a cybersecurity framework
You don't need fantasy threats. Use scenarios you see in real incidents as part of your risk assessment:
Ransomware outage that halts operations.
Account takeover that leads to wire fraud or payroll diversion.
Cloud misconfiguration that exposes data.
Vendor breach that becomes your breach.
Insider mistake (oversharing, wrong permissions, accidental delete).
Lost laptop or phone with active tokens.
For each scenario, ask for one piece of evidence that shows a control works. Examples include MFA coverage reports, backup restore test results, cloud posture findings, and a vendor list ranked by criticality. If ransomware is on your list (it should be), align leaders on readiness expectations using https://tysonmartin.com/board-ransomware-readiness-briefing.
If you only do one thing this week, do this mini-check from your risk assessment:
Identify your top 5 services and the data they touch.
Write your top 3 loss scenarios in one sentence each.
Ask for one proof artifact per scenario, then review it in a 30-minute meeting.
Step two, validate the security basics that prevent most incidents
Now you review the boring basics, security controls that stop common attacks. This isn't about "having a policy." It's about being able to say, "Show me."
When answers stay vague, you've found risk. When evidence of security controls is crisp, you've found strength. Either way, you're turning uncertainty into decisions.
A simple test: if your team can't produce proof in a week, the security control probably isn't operating the way you think it is.
Identity and access, prove who can get in and what they can do
Identity is your front door, and too many companies hand out spare keys. Focus on coverage and control for the accounts that matter most: executives, finance, admins, and anyone with broad access.
What "good" looks like, following best practices:
MFA and SSO, as internal controls, are enforced for all remote access and admin accounts.
SSO is used where it reduces password sprawl.
Privileged access is limited, logged, and reviewed.
Joiner-mover-leaver changes happen fast, including contractors.
Shared accounts are eliminated or tightly controlled.
Quarterly access reviews exist for key apps (email, ERP, HRIS, CRM, cloud console) to ensure compliance and meet regulatory needs.
Ask questions that require receipts on these security controls:
Can you show an MFA coverage report for email, VPN, and cloud admin?
Who has admin rights today, and why (export the list)?
How fast do you disable access after termination (show recent tickets)?
Where do shared accounts still exist, and what's the removal plan?
How do you manage service accounts, and when were credentials rotated last?
When was the last access review for ERP or finance tooling, and what changed?
Do you alert on impossible travel, new device sign-ins, or risky OAuth grants?
If you want this to stay business-aligned instead of turning into tool debates, anchor executive oversight around decision-ready strategy using https://tysonmartin.com/cybersecurity-strategy-advisor-for-ceos.
Vulnerability and endpoint hygiene, reduce easy attacker wins
Attackers love old software, unmanaged devices, and weak configurations. Your goal is to reduce the "easy wins" that turn a minor mistake into a major incident.
Ask for evidence in four areas:
Asset inventory basics: do you know what you have, especially internet-facing, through vulnerability scanning?
Patch speed: critical fixes happen in days, not months.
Endpoint coverage: EDR is deployed on laptops and servers that matter.
Device protection: disk encryption is enforced, and admin rights are limited.
While vulnerability scanning identifies issues, penetration testing provides a comprehensive view by simulating real attacks.
Use a small metric set you can track monthly:
Endpoint coverage percentage (EDR and encryption).
Age of the oldest critical patch on crown-jewel systems.
Count of high-risk exposures (internet-facing, known exploited).
Number of exceptions, each with an owner and an expiry date.
For a leadership-friendly way to track execution under pressure, borrow the "confidence-building metrics" mindset from https://tysonmartin.com/leading-through-cyber-crisis-command-center-metrics-that-inspire-confidence.
If you find gaps, fix in this order: privileged access first, then email security, then endpoints on executives and admins, then patch the exposed perimeter, then expand coverage.
Step three, test your ability to respond, recover, and report to leadership
Controls reduce risk. Response and recovery reduce damage through a risk-based approach. In a fast security assessment, you're checking whether the organization can act decisively when facts are messy.
Minimum artifacts to review (and they must be current):
Incident response plan and a working call tree.
Named decision rights (who declares, who shuts down systems).
Communications plan (internal, customers, regulators, for regulatory compliance).
Backup strategy, including SaaS coverage.
Last restore test results and what you learned.
Tabletop exercise notes and follow-up actions.
Board escalation triggers (what qualifies as "call the chair now").
"Tested" means people practiced decisions, and you can show changes made afterward. A tabletop that ends with "great discussion" and no actions doesn't count.
Incident Response Readiness, Know Roles, Decision Rights, and When the Board is Notified
Most incident failures happen at handoffs. You prevent that by clarifying who does what, before you need it.
Confirm:
Who can declare an incident, and who is backup after hours.
Who talks to customers and partners, and who approves messaging.
Who engages outside counsel, forensics, and insurance, and when.
Who can approve a ransom-related decision (even if your stance is "don't pay").
What gets documented as the single source of truth during the first 24 hours.
For board and audit committee oversight in risk management, keep it simple:
A set cadence for readiness review (at least annually).
Clear escalation thresholds tied to impact (downtime, data, fraud).
After-action reviews that track owners and dates.
If you want a board-ready lens on oversight expectations, use https://tysonmartin.com/board-incident-response-oversight.
Backups and Recovery, Focus on Restore Confidence, Not Backup Volume
Backups are only valuable when you can restore quickly and cleanly, under stress. In this security assessment, evaluate recovery capabilities to build confidence.
Focus on these truths:
Backups are immutable or protected from deletion.
Credentials for backup systems are separate and tightly controlled (consider FISMA requirements for government-related or highly regulated entities).
SaaS data is backed up (not assumed), aligned with NIST CSF.
Recovery time objectives exist for your top services.
Restore tests happen on a schedule, and results are recorded.
Scenario check: If ransomware hits your ERP on Monday morning, what happens by Tuesday? You should be able to answer: what's offline, what's restored first, who approves the order, and how you communicate delays.
To make recovery readiness inspectable at the leadership level for risk management, align metrics and oversight expectations with https://tysonmartin.com/board-oversight-and-ciso-performance-metrics.
Red flags to treat as urgent in your security assessment:
No recent restore test you can show.
Backups accessible with the same admin accounts as production.
An incident plan without named roles and alternates.
Unclear board notification triggers ("we'll decide at the time").
A simple way to score what you found and turn it into a 90-day plan
You don't need a complex model for risk assessment. You need a one-page score of your maturity level you can explain to the board, then a backlog you can execute.
Use this simple scoring lens for risk assessment:
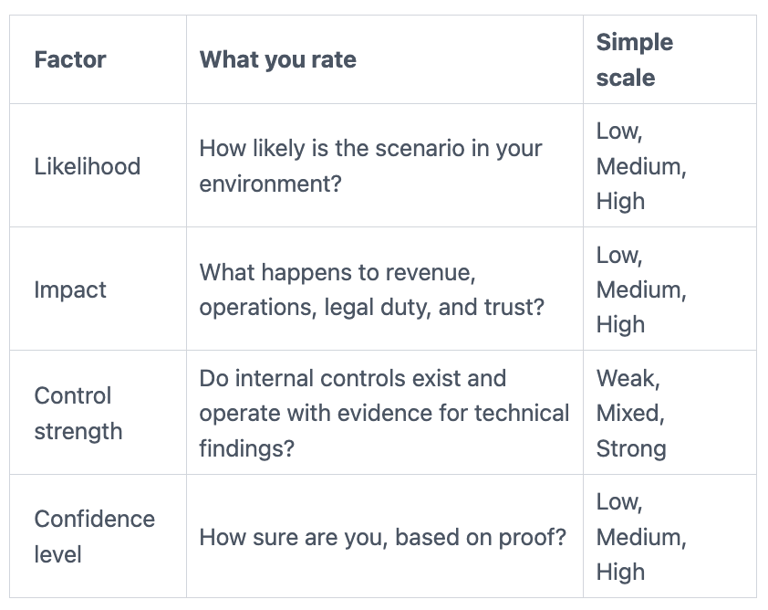
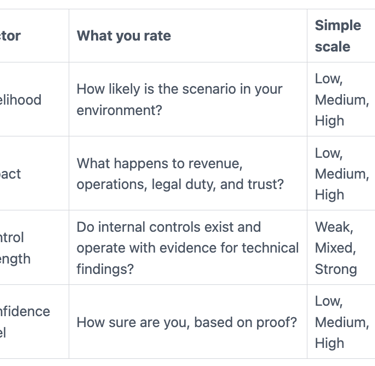
This scoring lens delivers a quick gap analysis. Then convert findings into a roadmap with owner, due date, proof of completion, and the decision required (if any). Delegate execution tasks to teams, but keep executive decisions at the top: governance risk and compliance items like risk acceptance, funding, policy exceptions, and downtime tradeoffs.
If you need rapid leadership capacity to drive this plan without waiting for a full-time hire, consider a fractional CISO model through https://tysonmartin.com/fractional-ciso.
Common questions leaders ask during a cybersecurity program assessment
How long should an assessment take?
You can get a solid first view in 2 to 4 weeks using an assessment tool if you focus on evidence and priorities. A deeper security assessment takes longer with an assessment tool, but you don't need that to start reducing risk.
What evidence is enough for executives?
Ask for reports, exports, tickets, vulnerability scanning results, and penetration testing outcomes, including FISMA compliance documentation. If the best proof is a verbal assurance, treat it as a gap.
What if you're mostly cloud?
Cloud changes the tooling, not the information security fundamentals or industry standards. Identity, logging, configuration control, and backup of SaaS still decide outcomes in information security.
What if you have no CISO?
Assign an executive owner for decisions, then use a short-term leader or advisor to build the first 90-day plan. If you're hiring, this guide helps you evaluate leadership fit: https://tysonmartin.com/how-ceos-should-vet-a-ciso.
How do you avoid boiling the ocean?
Start with crown jewels and loss scenarios, then validate identity and recovery. Let everything else queue behind the top risks.
What should the board see each quarter?
A short risk narrative aligned with industry standards, top changes since last quarter, a few stable metrics, and a decision list. If it doesn't drive decisions, it's not board reporting.
When should you bring in outside help?
Bring help in when speed matters, when you can't get evidence, after an incident, or during leadership transitions. Outside perspective also helps when internal teams are too close to the work to see weak assumptions.
Conclusion
A practical cybersecurity program security assessment follows a cybersecurity framework with a repeatable order of operations: define crown jewels and loss scenarios, validate identity security controls and hygiene security controls, test response and recovery, then perform a gap analysis to score findings into a 90-day roadmap.
Once you finish, write a short brief for leadership. Keep it tight: top risks, top fixes, and the decisions you need from executives or the board. That's how you turn a review into momentum.
If you need fast stabilization of your security posture during a transition or an urgent risk moment, interim support can help you move from uncertainty to risk management and control without delay: https://tysonmartin.com/interim-security-executive.


