Do You Need a Security Leader? Costs vs Risk Explained for Executives
Do We Need a Security Leader? You'll weigh fractional, interim, or full-time cost against breach risk, with a 90-day exec plan plus a path you can defend.


If you're in senior management weighing a security leadership hire, you're really choosing when you want to pay. You can fund prevention and readiness now, or you can fund downtime, legal response, and reputation repair later.
This decision usually shows up at predictable moments. A new enterprise customer sends a security questionnaire. Your company grows fast and adds more vendors. You move to cloud services and lose track of cloud security exposures. An incident rattles the team. An audit gets tense, or the board starts asking sharper questions.
At that point, the question becomes simple and direct: Do We Need a Security Leader? You don't need a buzzword answer. You need a business answer.
Here's what you'll get: a clear look at real costs versus real risk, plus a decision path that aligns with business goals you can take into your next exec meeting.
Key takeaways you can use in your next executive meeting
A security leader reduces surprise by turning scattered technical issues into a ranked risk management plan you can fund and track.
You need leadership sooner than you think if customers, regulators, or insurers expect proof, not promises.
Cost comes in tiers, from fractional leadership (part-time) to interim (time-boxed) to full-time, plus security program spend for basics.
The most expensive risks are predictable, like weak identity controls, untested backups, and unclear incident management roles.
"Good enough" security is measurable: you know what you own, who can access it, how fast you patch, and how you recover.
If you're unsure, start with clarity: define your top risks, decision rights, and a 90-day plan with owners.
What a security leader really does (and what they should stop doing)
A security leader's real job isn't picking tools. It's developing a security strategy, creating accountability, and driving effective risk management. You're not paying for someone to worry. You're paying for someone to help you make better decisions with fewer blind spots.
When security leadership works, you can answer basic questions without a scramble: What could take the business down? What would it cost? What are you doing about it this quarter? Who owns each fix? When do you accept risk, and when do you stop the line?
This is how security achieves business alignment and protects revenue. Uptime stays steadier. Sales cycles move faster because you can show controls and governance. Your legal and regulatory posture improves because you can prove you manage risk, not just react to it.
The common failure mode is painful and familiar. The security leader becomes the "ticket closer" and tool admin. They spend days tuning alerts, resetting accounts, and handling vulnerability management. Meanwhile, leadership still can't get a straight risk story. As a result, security turns into noise, and funding becomes guesswork.
If you can't explain risk in business risk terminology, you can't manage it, and you can't defend it later.
Your security leader owns the risk story, the priorities, and the tradeoffs
You need someone who can translate technical findings into business impact. That includes setting a clear risk tolerance with you and the board, then using it to rank work. The output should be a short list you can act on, not a 70-page report no one reads.
For example, imagine you're choosing between three projects:
Patching a set of critical servers
Rolling out MFA company-wide
Tightening vendor access and contract controls
A strong security leader won't say "do all of it" and walk away. Instead, they'll map each option to likely loss, speed of improvement, and operational friction. If ransomware risk is high and identity controls are weak, MFA might come first because it blocks common attack paths quickly. If you already have MFA but your patch cycle is chaotic, patching might move up. If customer contracts hinge on vendor controls, vendor risk may jump to the top. You get tradeoffs you can defend, not opinions.
They build the system around security, not a hero culture
You don't want a single person saving the day. You want a repeatable system built through cross-functional collaboration where security holds up under stress.
That system includes security governance (who decides, who funds, who is accountable), a few durable processes (access, patching, vendor intake, incident response), and metrics you can inspect. It also includes incident readiness, because plans that aren't tested tend to fail at the worst time.
If you're exploring outside leadership, it helps to see what an experienced CISO for hire looks like in practice, especially when you need fast clarity and steady execution.
Costs you can budget for vs losses you cannot schedule
Security leadership has visible costs you can plan. Incidents create costs you usually can't control, because they stack up fast and hit multiple teams at once.
On the budget side, think in two buckets: leadership capacity and the security program work that follows. Leadership might be fractional (a few days a month), interim (a time-boxed push through a transition), or full-time. Program costs often include basics like endpoint protection, logging, training, audits, and meeting insurance requirements. The right mix depends on how complex your business is and how much risk you carry.
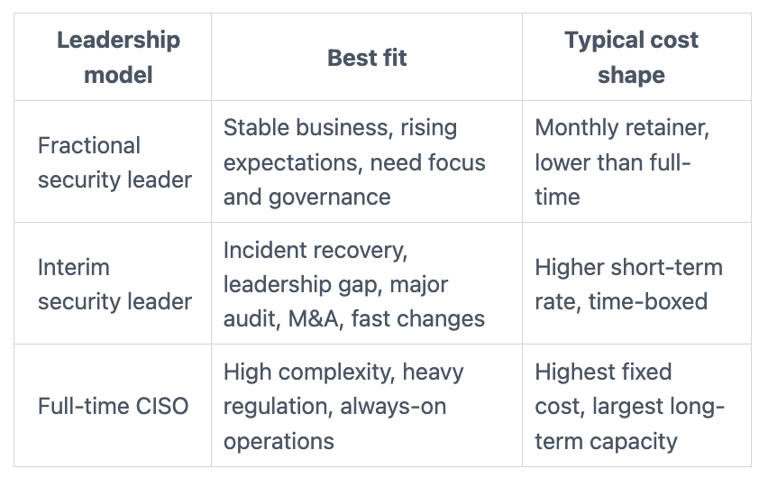
Here's a simple way to compare leadership models. These are rough ranges, because rates vary by market and scope.

Now compare that to losses from technical risk you can't schedule. The bill rarely stays inside the security team, affecting enterprise risk management as downtime hits revenue. Forensics pulls IT and engineering away from delivery. Legal counsel ramps up quickly. Regulators or customers ask for proof and timelines. Sales slows because your buyers lose confidence. Insurance premiums rise after claims, and renewals get harder.
The hidden cost many teams miss is burnout. A serious incident can flatten your best operators. Then you pay again through attrition and slower execution.
The true cost of security leadership is not just salary, it is focus and follow-through
Even with fractional leadership, you'll spend executive time. You'll change processes. You'll say no to shortcuts that feel efficient but create future loss. That "friction" is part of the price, and it's also the point.
In return, you get fewer repeat cleanups and a clearer path to trust. When you treat trust as a business enabler, you start managing it like one. That's the core idea behind working with a digital trust expert and CISO who ties controls to confidence, uptime, and customer expectations.
You're not buying security. You're buying fewer bad surprises, and faster recovery when they happen.
The biggest risk costs come from a few predictable failure points
Most expensive incidents don't require exotic hacking. They exploit basic gaps that stay open too long.
Here are common high-cost drivers:
No MFA on email, admin, or remote access
Backups that exist but aren't restore-tested
Unclear incident roles (people freeze or duplicate work)
Unmanaged endpoints (stale laptops, missing patches)
Shadow IT (unknown apps storing customer data)
Weak vendor controls (too much access, not enough oversight)
Poor joiner-mover-leaver practices (access doesn't match job reality)
A few "if you have this, expect that" examples help clarify the stakes:
If you don't have MFA, expect account takeover attempts to turn into real outages.
If you don't test restores, expect backups to fail when you need them most.
If incident roles are unclear, expect longer downtime and higher legal costs.
A simple decision framework: when you need a security leader, and what kind
You don't need the "perfect" answer. You need a defensible one for your board of directors that matches your risk and complexity.
Start with three ratings for your organization: low, medium, high.
Complexity: How many systems, vendors, locations, and integrations do you run?
Exposure: How attractive are you as a target, and how much sensitive data do you hold?
Pressure: How hard are customer demands, audits, regulators, or insurance requirements pushing?
Then choose the next move:
If most scores are low, appoint clear ownership (even part-time), set basic controls, and build reporting.
If you see a mix of medium, bring in fractional leadership to create a roadmap and drive execution.
If any score is high, treat security leadership as a risk control, not an optional role. Consider interim or full-time.
Your goal is steady decision-making, not a pile of policies. A good security leader also keeps learning through ongoing professional development, because threats, tech, and regulations change. That mindset matters, and you can see what it looks like in an evolving CISO continuous education path that stays grounded in real leadership demands.
You likely need dedicated leadership if any of these are true
Use these as fast triggers. If you recognize several, you're past the "someone will handle it" stage.
If you handle sensitive personal data (customer, patient, student, donor), you need clear oversight.
If you're in a regulated space, you need consistent evidence and controls.
If you run 24-7 operations, outages become headline problems fast.
If you're in rapid growth, your controls won't scale on hope.
If you depend on many vendors, third-party risk becomes your risk.
If you're doing M&A, you need visibility before and after integration.
If customers demand security reviews or SOC reports, you need a repeatable response.
If audits show repeat findings, you need someone driving closure, not explaining delays.
If you had a recent incident or near miss, you need leadership to prevent reruns.
If security work always loses to delivery deadlines, you need decision rights, not wishful planning.
Choose the right model: fractional, interim, or full-time (and what success looks like in 90 days)
Fractional works when you need direction, governance, and momentum without a full-time hire. Interim fits when you're in transition or under intense pressure. Full-time makes sense when security is a constant business constraint and the scope is large.
In the first 90 days, success should look practical:
A short risk assessment you can explain to the board
A target-state roadmap demonstrating strategic thinking with dates, owners, and funding needs
Top controls delivered (often MFA, backup testing, and patch cadence)
An incident plan with roles, tested in a tabletop exercise
A reporting cadence that shows trends, not trivia
Decision rights clarified (who approves risk, who funds fixes)
Credibility matters in these moments, especially when you're aligning teams under pressure. You can also look for leadership readiness signals, including strong leadership skills and being certified to lead, such as CISM, in cybersecurity frameworks and governance that boards recognize.
FAQs leaders ask before they hire security leadership
"Can our IT leader just own security too?"
Sometimes, yes. It can work when your scope is small, regulation is light, and your IT leader has time. It fails when delivery pressure conflicts with risk decisions, or when security becomes a part-time afterthought. Separation of duties also matters, because you need an independent security department for risk visibility, not self-reporting. A technical expert in IT cannot always provide the strategic oversight that a dedicated security department requires.
"What is the minimum security program we need right now?"
Start with basics you can measure. Know your assets, require MFA, and set a patch cadence. Add backups with restore tests, logging for key systems, a simple vendor intake step, and a security awareness program. Build security awareness into your corporate culture with this program. Finally, write an incident plan with names and roles, then practice it once.
"How do we measure if the security leader is doing a good job?"
Look for fewer critical exposures over time, not perfect numbers. You should see faster patching on high-risk systems and growing confidence in restore tests for the security department. Incident drills should improve decision speed and role clarity. Most importantly, reporting should drive decisions that improve business outcomes, not create panic.
"Won't security leadership slow the business down?"
Bad security slows you down with last-minute scramble and failed deals. Good leadership speeds you up by setting clear rules and enabling executive decision-making, removing uncertainty. When product and sales know what "approved" looks like, they move faster.
"Where can we get practical board-level guidance as we decide?"
If you want examples and executive-focused thinking, review the business side of cybersecurity to see how oversight, reporting, and decision rights can work without noise.
Conclusion
You're choosing between the known cost of leadership and the unknown cost of unmanaged risk in your security program. Paying for a security leader can feel optional until a customer blocks a deal, an insurer tightens requirements, or an incident forces you to spend fast with limited choices.
A defensible approach is staged. First, get clarity on your top risks and who owns each decision. Next, fund the few controls that block common failure paths. Then scale governance and reporting so the board can see progress and trends.
If you want a fast, practical start, engage an advisor with technical credibility and leadership skills to assess your needs and set a 90-day security strategy you can execute. The simplest next step is to engage a fractional CISO advisor and turn uncertainty into a plan your leadership team can stand behind.


