Hiring a Cyber Savvy Board Director Candidate. 9 Questions That Expose Real Judgment
Hire a Cyber Savvy Board Director Candidate with 9 interview questions that reveal judgment, tradeoffs, and incident leadership, plus a simple scorecard


A cybersecurity incident rarely fails because a board of directors lacked technical jargon. It fails because leadership made a bad call with incomplete facts, unclear roles, and fuzzy thresholds. As a director, you won't configure firewalls. You will shape risk appetite, funding discipline, and the tone of cybersecurity leadership when things go sideways.
A Cyber Savvy Board Director Candidate is someone who can oversee cyber risk in business terms, focusing on decisions and outcomes, not tools.
In this guide, you'll use nine interview questions that expose how a candidate thinks under uncertainty. You'll also get what strong answers sound like, what weak patterns reveal, and how to score candidates fairly. You'll leave with a simple way to reduce guesswork in your next director interview.
Key takeaways you can use in your next board director interview
Listen for tradeoffs in risk management, not certainty; good IT-savvy candidates explain what they'd protect first and why.
Ask for measurable outcomes; you want time-to-detect, time-to-recover, and decision speed.
Verify a governance mindset; look for clear decision rights and clear follow-up.
Test incident leadership; they should stay calm, protect facts, and coordinate legal and comms in response to cyber threats.
Confirm independence and ethics; watch how they handle conflicts, pressure, and executive pushback.
Look for learning habits; strong directors describe what they changed after being wrong.
What you are really hiring for in a Cyber Savvy Board Director Candidate
Cyber knowledge is knowing what controls exist. Cyber judgment is knowing what to do when you can't have everything, can't know everything, and can't wait. In board recruitment, boards hire judgment.
Your fiduciary duty sits at the center. Through executive search, you're hiring someone who can help you set risk appetite, challenge assumptions, and keep the company inside agreed guardrails. That includes privacy obligations, safety risks, customer trust, and enterprise risk. It also includes revenue, because growth depends on strategic assets you don't fully control, like SaaS platforms, cloud providers, and suppliers.
A cyber savvy director, beyond just it savvy, understands resilience as a business capability. Prevention matters, but recovery often decides the outcome. You want someone who asks, "How long can we be down?" and "What's our plan to keep serving customers?" They should also understand third-party and cloud realities, where your strongest control is often the contract, the architecture choice, and the monitoring, not ownership of the underlying tech.
Good oversight in a board meeting looks like this: clear questions, clear thresholds (what triggers escalation), and clear follow-up (who does what by when). If you want a deeper view on trust-driven oversight, see this perspective on being a digital trust expert.
The director you need isn't the one who "knows cyber." It's the one who can make risk decisions you can defend later.
Green flags and red flags that show up before you ask any questions
You can spot judgment early if you listen for how the candidate frames problems.
Green flags: speaks in scenarios, asks about decision rights, uses plain language, admits uncertainty, names tradeoffs, references lessons learned, focuses on recovery, respects legal and comms roles.
Red flags: starts "tool shopping," uses fear to sell, blames teams for incidents, talks about "zero risk," shares past confidential details too freely, treats compliance as paperwork, dismisses business constraints.
Those signals matter because board work is mostly judgment calls, not checklists.
The 9 questions that expose real judgment (with what strong answers sound like)
The goal is simple: you're testing how they think and real judgment, not just technology expertise or what they've memorized. You'll hear echoes of practical boardroom patterns in resources like these CISO and board-level insights, but your interview should stay grounded in your business.
Decision-making and governance questions that separate leaders from talkers
1) "Tell me about a time you changed your mind on cyber risk after new facts came in. What did you do next?"
Why: Boards need directors who update decisions without ego.
Listen for: what new data mattered, how they communicated the change, and what they did to prevent repeat confusion.
Probe: "What did you stop doing because of the new facts?"
Red flag pattern: they claim they rarely change their mind, or they blame others for "bad info."
2) "How do you decide what belongs in the board room vs management's job?"
Why: Many directors either micromanage or rubber-stamp. Both are dangerous.
Listen for: clear lines based on material risk, thresholds, and decision rights (not personal preference).
Probe: "Name one thing you'd never ask the CISO to bring to the board."
Red flag pattern: they want operational control, or they push everything to management with no guardrails.
3) "What metrics do you trust, and what metrics do you not trust, when cybersecurity professionals say a security program is improving?"
Why: Metrics can hide risk or create perverse incentives.
Listen for: a mix of outcome and capability metrics, plus skepticism about vanity numbers.
Probe: "What metric has fooled you before?"
Red flag pattern: they only cite counts (patches, training completion), or they treat maturity scores as proof of safety.
Resilience and incident questions that reveal cybersecurity leadership under pressure
4) "Walk me through the first 24 hours after a data breach. What should the board demand, and what should it avoid?"
Why: Early choices shape legal exposure, trust, and recovery time.
Listen for: fact discipline, clear roles (legal, comms, ops), and requests for decision-ready options.
Probe: "What would make you call an emergency meeting?"
Red flag pattern: they demand technical deep dives, or they push for public statements before verified facts.
5) "When would you support paying a ransom, and when would you refuse?"
Why: Ransom is a business decision with ethics, legal, and repeat-risk consequences.
Listen for: criteria like safety, service continuity, legal counsel input, and ability to restore without paying.
Probe: "What evidence would you require before any payment discussion?"
Red flag pattern: "Never pay, ever" with no nuance, or "Pay quickly to end it" with no guardrails.
6) "How do you test whether a response plan will work, not just exist?"
Why: Plans fail when people haven't practiced decision speed and coordination.
Listen for: tabletop exercises tied to business scenarios, measured outcomes (time-to-escalate, time-to-decide), and corrective actions.
Probe: "Who must be in the room for the hardest scenario, including the CISO?"
Red flag pattern: they equate a written plan with readiness, or they avoid involving executives.
Business strategy and third-party questions that show real-world practicality
7) "If growth depends on speed, what security decisions do you push to 'good enough' and what do you never compromise?"
Why: Every business makes tradeoffs, your director must make them explicit.
Listen for: non-negotiables (identity, backups, logging, data handling) and flexible areas (phased controls, risk acceptance with dates).
Probe: "Give an example of a time-boxed risk acceptance you'd approve."
Red flag pattern: they treat all controls as equal, or they use speed as an excuse to skip basics.
8) "How do you evaluate vendor and cloud risk without slowing the business to a crawl?"
Why: Third parties create real exposure, and boards must demand discipline that still moves.
Listen for: tiering vendors by impact and cyber vulnerabilities, contract and architecture controls, and proof of monitoring after onboarding.
Probe: "What would make you block a vendor even if a team loves them?"
Red flag pattern: they rely only on questionnaires, or they hand-wave risk because "everyone uses that vendor."
9) "What is one uncomfortable question you would ask the CEO about cyber, and how would you ask it?"
Why: The board's job includes hard conversations delivered with respect.
Listen for: direct but constructive phrasing, focus on accountability, and willingness to raise issues without drama.
Probe: "How do you handle it if the CEO gets defensive?"
Red flag pattern: they avoid discomfort, or they brag about "calling people out" as a power move.
How to score the interview, compare candidates fairly, and avoid common board hiring traps
A structured scorecard, essential for succession planning, keeps you from hiring the smoothest talker. It also helps the hiring manager explain your choice later, which matters in board settings.
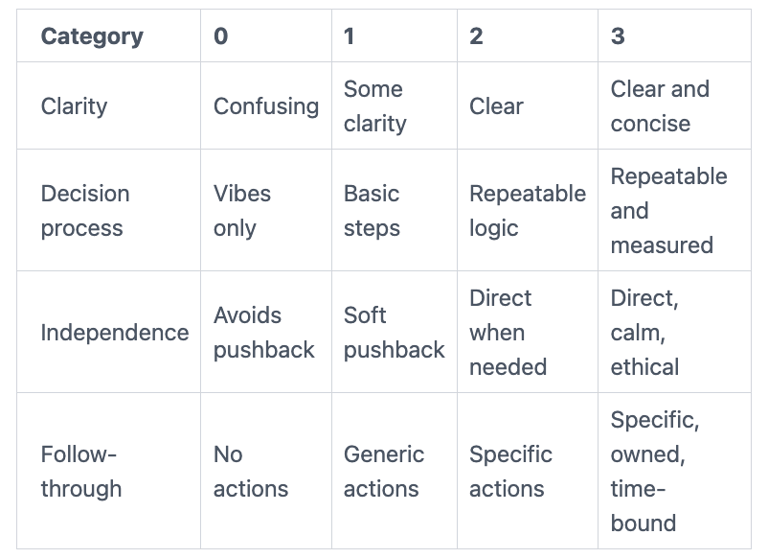
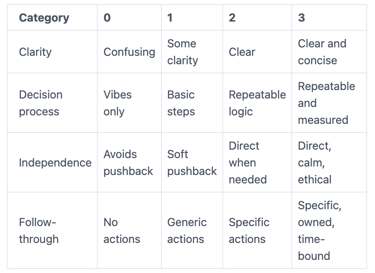
Use this simple 0 to 3 rubric:
Before you finalize talent acquisition, do reference checks with an evidence mindset. Ask for one incident, one hard tradeoff, and one example of changing course. Request outcomes and who was involved, not opinions like "great leader."
Watch for three common traps:
Hiring for buzzwords instead of decision quality.
Confusing compliance activity with real risk reduction.
Over-weighting former titles instead of patterns of judgment.
If you need seasoned help to calibrate the role, pressure-test expectations, or steady governance during a transition, consider outside experts like experienced security leadership when you need it most.
A simple 30-60-90 day expectation for your new director's cyber contribution
In the first 30 days, you want them learning your business model, key systems, and top trust risks. They should meet the CEO, CIO, CISO (or security lead), legal, and finance.
By 60 days, align on board oversight reporting. Agree on thresholds, what triggers escalation, and what "good" looks like. Also confirm committee placement and cadence.
By 90 days, have them pressure-test readiness. That can mean reviewing the last tabletop, sampling third-party risk decisions, and checking recovery assumptions. Keep it oversight-focused, they shouldn't run the security team.
FAQs about hiring a cyber savvy board director
Do they need to be technical?
No. They need business acumen to understand tradeoffs, material risk, and decision timing. Plain language beats jargon in the boardroom.
What committee should they sit on?
Often audit committee or risk, sometimes a dedicated technology committee. Match the seat to where cyber decisions and reporting already live.
How should you handle conflicts of interest?
Ask about advisory work, vendor ties, and investment positions early. Then document recusal rules and enforce them consistently.
How do you evaluate "former CISO" candidates?
Don't assume the title equals board judgment in the cybersecurity market. Test governance instincts, independence, and ability to stay out of operations.
What should you ask references?
Ask for one tough decision, one moment under pressure, and one example of earning trust with non-technical leaders. Push for outcomes, not adjectives.
How often should the board review cyber risk?
At least quarterly, plus event-driven updates when thresholds are crossed for cyber defenses. A governance survey identifies this as a best practice. If you want to strengthen governance quickly, consider engaging a CISO advisor to strengthen governance.
Conclusion
You're not hiring a technical superhero. You're hiring board-ready judgment, calm leadership, and business-first cybersecurity oversight that holds up under scrutiny. The nine questions above help you see how a candidate thinks when facts change, pressure rises, and tradeoffs get real.
Use the scorecard to compare candidates fairly, then validate stories through evidence-based references. After you choose, set clear 30-60-90 expectations so their contribution stays focused on oversight, not business operations.
Next step: review your board of directors' skills gap, run the structured interview, and lock in thresholds for reporting and escalation before the next incident forces the issue.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
