Hiring an Interim Cybersecurity Executive. Stop Buying Tools. Fix Ownership and DecisionsYour blog post
Hiring an Interim Cybersecurity Executive helps you pause tool sprawl, assign risk owners, and speed decisions with a simple weekly cadence.
Your security spend keeps rising, yet the risk story still feels fuzzy. One quarter you buy an EDR add-on, the next you expand SIEM, then you bolt on another cloud scanner. It feels like progress because something ships, a dashboard lights up, and a vendor promises fewer headaches. That's the trap an Interim CISO is hired to escape.
Still, your team argues about priorities, alerts pile up, and key decisions drag on for weeks. Meanwhile, the business wants speed, not more friction.
An interim cybersecurity executive, serving as your Chief Information Security Officer for a defined period, is a time-bound, Leadership-as-a-Service, outcomes-driven leader you bring in to restore control. Not by adding more tools, but by clarifying who owns the risks, how decisions get made, and what "good" looks like in plain terms. When ownership and decisions work, tools finally start working for you too.
Key takeaways you can act on this quarter
Conduct a cybersecurity risk assessment to name your top 5 risks in business terms (for example, "ransomware outage," "fraud," "customer data exposure"), not tool gaps.
Assign one executive risk owner per top risk, with one technical owner supporting them.
Set a weekly 30-minute decision cadence to accept, fund, transfer, or stop risk work.
Freeze net-new tool purchases for 60 days, unless tied to a named risk with an owner and due date.
Define what the Board of directors needs to see (trend, exposure, decisions made, and what's stuck).
Perform a gap analysis to retire or reduce overlapping controls before you expand the stack.
Hire an interim cybersecurity executive to deliver a strategic roadmap when decisions stay stuck and nobody can break the logjam.
Why buying more security tools keeps failing (even when the tools are good)
Most tool programs fail for boring reasons. Not because the products are bad, but because your organization can't decide what matters, who owns it, and what "done" means.
When decision rights are unclear, every tool becomes a debate magnet. Security wants coverage. IT wants stability. Legal wants safe language. Finance wants predictability. Business leaders want fewer delays. If nobody can make the call, the default choice is often, "Buy something."
That creates a familiar pattern:
You add a new platform, then spend months integrating it. Alerts increase because detection improves faster than response capacity. People tune rules instead of fixing root causes. Teams argue about which dashboard is "true." In the end, you have more data and the same uncertainty.
The business impact shows up fast. Costs climb because you pay for overlapping tools and extra storage, undermining operational efficiency. Projects slow because security reviews stretch out. Outages last longer because incident roles aren't clear. Trust erodes because C-suite leadership can't answer simple questions like, "What are we exposed to this month, and what did we decide about it?"
Good tools can support a plan. They can't replace ownership.
The hidden costs leaders do not see on the invoice
You don't just buy software. You buy work, and that work often lands on the same people you already need for risk reduction.
Here are costs that rarely show up in the pitch deck:
Integration time that pulls engineers off patching, identity fixes, and hardening.
Duplicate effort when two tools detect the same thing, but neither team trusts the other feed.
Shelfware when licenses renew while adoption stalls, because nobody owns outcomes.
New dashboards nobody checks after the first executive review, because they don't answer business questions.
Opportunity cost is the quiet killer. For example, a team might spend six weeks tuning SIEM rules while critical servers stay unpatched. Or you might roll out a third-party risk tool while procurement still can't enforce basic vendor requirements. You can't buy your way out of indecision.
The core gap is governance, not features
Governance sounds formal, but it's simple: who decides, who pays, who operates, and who accepts organizational risk.
When governance is weak, your security program becomes tool-led. Vendors shape your roadmap. Loud stakeholders win priority. Risk acceptance turns into silence, which is not the same as approval. As a result, every meeting becomes a negotiation, and every tool becomes a substitute for a hard choice.
Use this line in your next leadership meeting:
If nobody owns the risk, everybody buys tools.
Once you assign ownership and set decision rules, the politics drop. People stop arguing about features and start deciding on outcomes. That's when the stack becomes an asset instead of a cluttered closet. Interim executive placement offers a strategic bridge to establish this clarity quickly.
What an interim cybersecurity executive actually fixes in the first 30 to 90 days
You don't bring in interim leadership to "do security." You bring them in to make security decidable. The first wins are usually about rhythm, ownership, and follow-through, because those are the things that unblock everything else.
In practice, the Interim CISO becomes your bridge between board expectations and the teams doing the work, providing a strategic vision that translates risk into business impact, then turns business priorities into actions that stick. This transitional leadership in the first 30 to 90 days often starts with triage. What risks could stop revenue or operations in the next 90 days? What control failures keep repeating? Where are you one mistake away from a reportable incident? Then they set a clear operating system: a short list of risks, named owners, a decision cadence, and reporting that drives action.
This is why hiring an Interim CISO can change outcomes quickly. You stop waiting for perfect org design and start making real decisions with the structure you have today. If you want a sense of what that executive leadership looks like in practice, review what an experienced CISO for hire focuses on when stakes are high and time is tight.
Reset ownership with a simple map: decisions, risks, and names
You can picture this as a one-page map, not a big committee.
Start with a ranked list of your top risks. Each risk gets:
an executive owner (accountable for the outcome),
a technical owner (accountable for delivery through their technical expertise),
a due date (when you will reduce exposure or formally accept it).
The key shift is what you "own." You don't own a tool. You own a risk outcome (for example, "reduce ransomware blast radius," not "deploy backup software").
A capable Interim CISO will quickly define six basics aligned with ISMS policies, so decisions stop bouncing:
Decision rights (who can approve spend, exceptions, and acceptance)
Escalation path (what rises to execs within 24 hours, including for incident handling)
Risk acceptance rules (who can accept which level in line with regulatory requirements, and for how long)
Budget guardrails (what's pre-approved, what needs review)
Control owners (who runs identity, patching, backups, vendor risk)
Reporting cadence (weekly ops, monthly exec summary)
Once names are attached, progress stops being optional.
Create a decision cadence that stops the endless debate
A common fix is a weekly, 30-minute risk decision meeting. It's short on purpose. You bring the smallest group that can decide: the security lead, IT ops, product or business owner, and a finance voice when money is on the table.
The agenda stays stable:
What changed in exposure this week?
What decisions are needed?
What's blocked, and who will unblock it by when?
Decisions should land in one of four buckets: accept, mitigate, transfer (insurance or contract), or stop (de-scope risky behavior). Fast decisions include patching deadlines, MFA enforcement, and vendor access rules. Slower decisions include architecture changes, platform migrations, and major contract shifts.
Documentation matters more than the format. A simple decision log (date, risk, decision, owner, review date) keeps choices alive through staff changes. It also stops re-litigating the same argument every quarter.
Turn the tool stack into a plan, not a shopping cart
Once risks and owners are clear, your tool stack can finally be judged against needs. The Interim CISO typically maps tools to required controls in plain language (identify, protect, detect, respond, recover). Whether you align to NIST CSF or ISO 27001, the idea is the same: tools support controls, and controls support risks.
Then the stack gets rationalized with four choices: keep, integrate, replace, or retire.
A "60-day tool pause" often helps. During that pause, you allow exceptions only for urgent gaps tied to a named risk (for example, no viable backups, no MFA, no incident logging). Everything else waits until you can prove it reduces exposure.
A useful test: if you can't name the risk owner and the expected outcome, it's not a tool purchase, it's a hope purchase.
You measure outcomes that executives understand: fewer critical alerts that nobody can act on, faster patch cycles, stronger identity controls, and incident readiness that doesn't rely on heroics.
How you know it is time to bring in interim leadership (and how to hire well)
Interim leadership makes sense when you need movement, not another strategy deck. You might be growing fast through digital transformation, dealing with an incident, staring at an audit deadline, or absorbing an acquisition. Sometimes you simply have too many opinions and not enough decisions. Unlike a permanent hire that requires extensive onboarding, interim leaders deliver quick results with defined scope.
The hiring trick is to avoid vague scope. You don't need "someone to improve security." You need someone who can establish ownership, create a decision cadence, and deliver a board-ready view of risk in weeks, not quarters. An executive search firm can be a valuable resource for organizations seeking high-level interim talent in cybersecurity leadership.
If you want a clear starting point for a conversation and scope, use this page to engage a CISO advisor and align on outcomes, authority, and timeline before the work begins.
Signals you are stuck in tool buying mode
If several of these feel familiar, it signals gaps in cybersecurity leadership, and you're probably paying for confusion:
Your security roadmap changes every quarter.
Nobody can name the top 5 risks without opening a spreadsheet.
Gap analysis uncovers two or more tools that overlap, yet gaps still exist.
Incidents get handled ad hoc, with different roles each time.
Audits drive most work, even when risks point elsewhere.
Risk is reported as red-yellow-green with no business context.
Budget rises, but incident frequency, impact, and security posture don't improve.
Business units pick their own security tools or bypass standards.
Decisions take months, even when risk is obvious.
These aren't "security team problems." They're ownership and governance problems.
A simple hiring scorecard for an interim cybersecurity executive
Use a scorecard so you can move fast without guessing. This table works well in executive interviews and helps differentiate from a permanent hire.
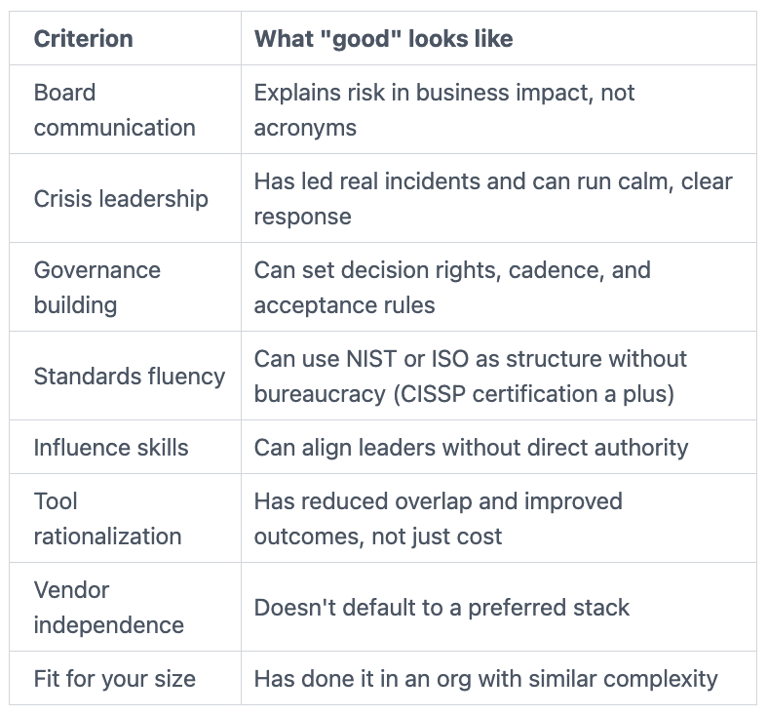
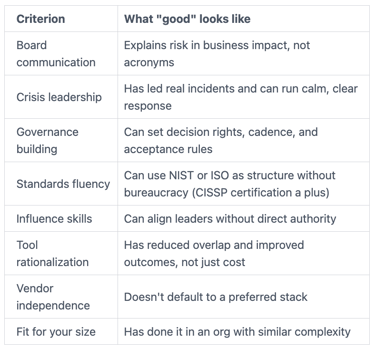
In interviews, ask for specifics. "Tell me about a time you stopped tool sprawl." "How do you set risk acceptance rules?" "What does your first 30 days look like?" Also ask what they will deliver in 30, 60, and 90 days. You should hear tangible outputs: a top risks list with owners, a decision log, an incident readiness check, and a prioritized plan tied to budget. An executive search firm excels at sourcing interim cybersecurity leadership talent matching this profile.
FAQs leaders ask before they stop buying tools and start owning decisions
Interim vs fractional Chief Information Security Officer vs full-time CISO, what's the difference?
Interim usually means full-force help for a fixed window, often during change or crisis. Fractional CISO is part-time leadership over a longer period, offering flexibility for ongoing needs. A Virtual CISO provides similar remote oversight, but a Fractional CISO often delivers more tailored, hands-on guidance. Full-time is the long-term hire who owns the function. Leaders weighing a Fractional CISO against a Virtual CISO or full-time role find interim best for rapid decisions, clean ownership, and stabilization.
How fast do you see value from interim cybersecurity leadership?
You can see value in weeks if authority is clear. Early wins include a top risks list, named owners, and a weekly decision cadence. You also get faster incident handling because roles and escalation become explicit. Tool spend gets more disciplined once purchases must map to owned risks.
How do you avoid stepping on IT or the CIO?
You align on boundaries up front with strong stakeholder management. Security sets risk requirements and decision structure. IT owns operations and delivery. The interim leader should partner with the CIO, not compete with them. A shared decision meeting and a single decision log remove surprises and reduce friction.
What should you do with existing tool contracts?
Start by mapping each contract to a control and a risk outcome, including those tied to business continuity planning or disaster recovery. If a tool is redundant, decide whether to retire at renewal or reduce scope now. Avoid ripping out platforms during an incident-heavy period. Instead, stabilize first, then rationalize with timing that protects operations and negotiating power.
How do you report cyber risk to the board without panic?
Keep it consistent and decision-focused. Share your top risks, the trend (better, worse, flat), success metrics, and what decisions you made this month. Highlight what's blocked and what you need from leadership. Boards respond well to clear ownership, deadlines, and tradeoffs, not long lists of vulnerabilities.
Conclusion
Tools aren't the enemy. The problem is buying tools as a substitute for ownership and decisions. Fixing ownership unlocks a clear strategic vision for tackling organizational risk.
If you want control back, start with what you can do this week: conduct a cybersecurity risk assessment to name your top risks in business terms, assign one owner per risk, and set a short weekly cadence to decide. Then pause net-new tools long enough to sort signal from noise.
When you can't get those decisions made, transitional leadership is the cleanest reset. Bring in an Interim CISO through interim executive placement who can set the rules, build the rhythm, and make progress visible. This Leadership-as-a-Service model delivers the structure you need. Use this line in your next exec meeting: "No new tools until we can name the risk owner and the decision."
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
