How to know if your cybersecurity is good enough
How to know if your cybersecurity is good enough, use a 4-part leader test, outcomes, top risks, proof, and a simple, board-ready monthly dashboard.


You don't need "perfect" cybersecurity. To know if your cybersecurity is good enough, you need security that's good enough for your size as a small to medium-sized business, your data, and the kind of attention your business attracts. Otherwise, you end up spending on tools and still feeling uneasy, like locking the front door while a window stays open.
In simple terms, "good enough" means four things stay true most of the time: you can prevent common attacks, detect problems fast, recover without chaos, and explain risk clearly to leaders. That's what protects revenue, operations, and trust.
If you're trying to decide whether you're there, anchor your thinking in digital trust, the confidence customers and partners have that you can protect what you handle (https://tysonmartin.com/digital-trust-expert). To assess your cybersecurity posture, run a four-part test: outcomes (prevent, detect, respond, recover), coverage of the biggest risks, proof through testing, and leadership visibility.
Key takeaways: how to know if your cybersecurity is good enough
You're "good enough" when your security measures can prevent common attacks across all critical systems, not just a few.
You detect and contain suspicious activity fast, with clear on-call coverage and roles.
You protect your crown jewels first, based on how your business makes money and serves customers.
You can recover quickly because backups are isolated and restores are tested.
Access from third-party vendors and SaaS sprawl are controlled, including shadow AI and data sharing.
You rely on evidence from repeatable tests, not confidence based on tools.
Leadership gets a simple dashboard that drives decisions, not a pile of status updates.
You know when to bring in outside leadership, before a surprise forces your hand.
Start with outcomes: can you prevent, detect, respond, and recover fast enough?
Cybersecurity maturity sounds reassuring, but outcomes are what matter when something goes wrong. Think of "good enough" like a seatbelt and brakes test, you don't grade the car on how shiny it is. You ask whether it stops in time, every time.
A practical way to judge outcomes is to use a simple scorecard your CEO or board can understand:
Prevent: Do common attacks fail most of the time?
Detect: If something slips through, do you notice quickly?
Respond: Can you contain damage without confusion?
Recover: Can you restore operations and data on purpose, not by luck?
"Good enough" does not mean "nothing bad will happen." It means your team can keep a routine incident from becoming an existential one.
If your plan depends on one hero who "knows the systems," your cybersecurity isn't good enough yet.
Prevention: are the basics really locked down across your most important systems?
Most breaches don't start with movie-level hacking. They start with inconsistent basics. One business unit uses MFA, another doesn't. One admin account is protected, five aren't. One legacy server never gets patched, leaving vulnerabilities exposed, because "it might break something."
Focus on consistency across your critical apps and environments (email, identity, finance systems, cloud consoles, customer databases). The basics that most organizations still miss are plain:
multi-factor authentication where it matters (email, remote access, admin consoles), patch management with clear deadlines, least privilege for admins, cybersecurity awareness training for staff, secure backups that attackers can't erase, hardened email controls to reduce phishing, endpoint protection that's owned and tuned, and tight vendor access controls.
This is also where you move from checkbox work to confidence. If you want that framing, it helps to think in terms of shifting from compliance to confidence, because passing a requirement doesn't always mean you reduced real exposure.
Detection and response: would you know quickly, and would people know what to do?
Two time measures tell you a lot:
Mean time to detect (MTTD): how long it takes you to notice something bad.
Mean time to contain (MTTC): how long it takes you to stop it from spreading.
You don't need perfect numbers. You need a trend that improves, plus a process that works outside business hours. That means logging that's actually turned on for critical systems, alerts that someone reviews, an on-call plan (even if it's small), and a triage routine that separates "noise" from "this could hurt us."
Response is also people and roles. Who is the incident lead, who talks to legal, who handles customer messaging, who can approve shutting down a system? If those answers feel fuzzy, use board-level expectations as your baseline, including what oversight c-suite executives should have in the first hours of an incident response (https://tysonmartin.com/board-incident-response-oversight).
Check whether you are protecting what matters most, not everything equally
A common failure pattern is spreading security effort like peanut butter. It feels fair, but it doesn't protect what would truly hurt if it failed. "Good enough" is a prioritization decision, not a promise to protect everything at the same level.
Your threat level depends on the cyber threats you face based on who you are and what you do. A SaaS company might face account takeover and API abuse. A healthcare nonprofit might worry about ransomware and sensitive records. A manufacturer might face downtime risk and supplier access. Financial services will carry heavier fraud and regulatory exposure.
So the goal is alignment: your controls should match your crown jewels and the most likely failure paths.
Do you know your crown jewels and the few ways you could lose them?
Start simple. Name three to five business processes or datasets you cannot afford to lose. Examples: sensitive data such as customer identity data, payment flows, patient records, payroll, production scheduling, donor databases, or proprietary designs.
Next, map the few ways those could fail in the real world. Keep it concrete:
Phishing attacks lead to payroll fraud.
Stolen credentials lead to admin access in the cloud.
Ransomware attacks lead to downtime and missed shipments.
A vendor compromise leads to data exposure through an integration.
You don't need a heavy threat modeling program to do this. You need a short cybersecurity risk assessment workshop that links assets to impact and likely attack paths. That connection also makes budget conversations sane, because you can measure outcomes in business terms, not tool counts. If you want a practical bridge between security work and business value, this perspective helps (https://tysonmartin.com/measuring-securitys-business-impact).
Are third parties and AI tools creating quiet risk you are not seeing?
Your risk surface now includes vendors, SaaS apps, cloud services, and integrations that can move data without much friction. In 2026, you also have AI risk that rarely shows up on an asset list: shadow AI, employees pasting sensitive data into public tools, long-lived model access keys, and "helpful" copilots connected to internal systems.
You don't need to ban AI to be safe. You do need guardrails, policy plus technical controls, and vendor discipline. When you assess vendors, keep a few leadership questions ready:
What access do you need, and can you operate with least privilege?
How do you isolate customer data, and how do you prevent training on it?
How fast do you notify us after an incident, in writing?
Can we log and review admin activity tied to our environment?
How do you offboard access, and how do we verify it's gone?
These questions belong in risk reporting, not buried in procurement emails. Strong governance and clear reporting paths help you keep third-party and AI risk visible without creating drama (https://tysonmartin.com/risk-committee-cybersecurity-reporting).
Look for proof, not promises: the tests that show if your security is real
Anyone can say, "We have EDR," or "We're ISO-aligned." Proof looks different. Proof is repeatable testing that creates learning loops for proactive security, with results you can explain in a few sentences.
If you can't show evidence, you're forced to rely on confidence and good intentions. That's not fair to your team, and it's not defensible for leadership.
What to test, how often, and what "passing" should mean
You don't need a massive program to get real signal. A practical testing set usually includes vulnerability scans (with clear deadlines to remediate vulnerabilities), backup restore tests, access reviews for privileged accounts, incident tabletop exercises, and targeted penetration test for high-risk areas. For cloud-heavy teams, configuration reviews matter because small mistakes can scale fast.
"Passing" should mean you hit simple targets and you improve over time. For example, you might aim to patch critical internet-facing issues in days, not months, prove quarterly restores for key systems, and run at least one executive tabletop per year. The exact targets depend on your business, but the direction should always be visible.
Good metrics keep this honest. Bad metrics create noise. If you want a clean way to think about that difference, this is a useful reference (https://tysonmartin.com/the-hidden-value-of-cyber-metrics).
Red flags that say you are guessing, even if your team is working hard
Hard-working teams can still be stuck in a guessing loop. Watch for these signals:
Unknown asset inventory, so you can't prioritize patching. No restore testing, so backups are just hope. Alerts piling up with no owner. Admin sprawl and shared accounts. Old user accounts that never get removed. Unclear incident roles, especially after hours. Projects not tied to top risks, so you can't explain why work matters. "We bought a tool" as the plan, with no process change. No independent validation, so issues like a malware infection stay hidden until an audit or incident.
If you want a fast leadership move for the next 30 days, sponsor three things: an admin access cleanup, a backup restore test for one critical system, and a tabletop with named roles and a call tree.
Tools help, but they don't equal outcomes by themselves. If you've felt that gap, this framing will sound familiar (https://tysonmartin.com/security-roi-isnt-in-your-tech-stack).
Make it board-ready: the simplest way to report "good enough" without hiding risk
Leadership confidence comes from clarity, not from green status lights. The simplest approach is to report a small set of measures that stay stable, with short notes on what changed and what decisions you need.
This is the "inspect what you expect" idea. If you don't inspect it, it drifts.
A simple monthly dashboard you can actually use
Here's a compact dashboard structure that fits in one page and supports decision-making in your cybersecurity strategy. You can tune targets later, but keep the categories stable.

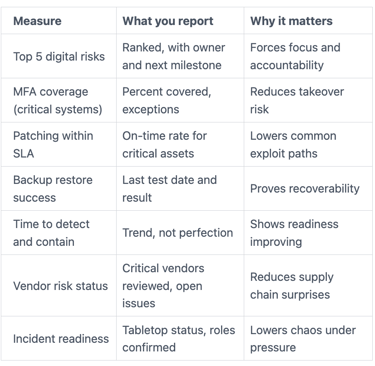
For deeper guidance on board-level measures and oversight, this is a solid reference (https://tysonmartin.com/board-oversight-and-ciso-performance-metrics).
When "good enough" means you should bring in outside leadership
Sometimes your controls are fine, but leadership bandwidth isn't. You should consider outside help when you hit triggers like fast growth, a merger, a new regulatory bar or compliance issues, repeated incidents, insurance pressure, a missing security leader, or a major cloud transformation.
You also have options that don't require an immediate full-time hire. A fractional CISO can give you steady senior ownership part-time. An interim security executive can stabilize risk quickly when you need intense short-term leadership.
The right choice depends on urgency and whether you need a long-term operator or a short-term stabilizer.
FAQs leaders ask when they are trying to judge cybersecurity
Is passing an audit the same as being secure?
No. A cybersecurity audit helps you confirm control coverage, but it doesn't prove you can detect, contain, and recover from real attacks. Evidence from restore tests, tabletops, and operational metrics matters more than a passed checklist.
How much should you spend on cybersecurity to be "good enough"?
Tie spend to business risk, not a benchmark alone. Start with crown jewels, downtime tolerance, and the cost of a serious incident like a data breach. Then fund the few improvements that reduce likely loss from cyber threats and speed recovery.
What are the fastest improvements that reduce risk this quarter?
Start with MFA on critical access, isolate backups and run a restore test, tighten patch deadlines for exposed systems, clean up admin access, run an incident tabletop, and review vendor access paths. Those moves reduce common failure modes quickly.
How do you know if your security team is understaffed?
You'll see constant firefighting, a backlog of critical fixes, and testing that keeps slipping. Alerts pile up from visibility gaps like remote workers and IoT devices, owners aren't clear, and nobody has time to validate basics like restores and access reviews. Understaffing shows up as missed follow-through, not just tired people.
Do you need cyber insurance to be "good enough"?
Insurance is a financial backstop, not a security control. Insurers also expect proof, often MFA, backups, response plans, and testing evidence. If you treat insurance as your plan, you'll be disappointed when a claim turns into a documentation debate.
Conclusion
You know your cybersecurity is good enough when you can show outcomes, focus protection on what matters, prove it through testing, and report it clearly to leadership. That's the difference between feeling busy and feeling in control.
Pick one step you can schedule this month: a network visibility assessment, a dark web scan, a backup restore test, an MFA coverage check on critical systems, or a 90-minute incident tabletop with named roles. Then repeat the cycle, measure progress, and tighten what's weak as part of your cybersecurity strategy.
If you want help validating your "good enough" baseline and turning it into a simple plan leaders can inspect, you can engage a fractional CISO advisor. The goal is straightforward, fewer surprises and more confidence in your information security when the pressure hits.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
