IT Strategy vs. IT Roadmap: What’s the Difference?
Learn the difference between IT strategy and roadmap, spot weak plans, and tie priorities to cyber risk, governance, and board-ready metrics in 30 days.


You're in a leadership meeting in March 2026, and three things hit at once. A business unit wants a new platform "by summer." Someone else is pushing AI features "before competitors do." Meanwhile, your auditor, insurer, or a big customer asks tougher security questions, and your budget is flat.
So you ask for the plan. You get a deck titled "IT Strategy," plus a spreadsheet called "Roadmap." Both the IT strategy and roadmap look reasonable. Yet deadlines still slip, risks show up late, and teams stay busy without feeling ahead.
That confusion is costly. It creates hidden tradeoffs, surprise exposure, and constant re-planning. Most importantly, it makes it harder for you, as a CEO, founder, or board member, to approve spend with confidence.
This article gives you a plain-language difference between IT strategy and IT roadmap, how to spot weak versions of each, and how to connect both to cyber risk and governance while delivering the IT vision your leadership expects in a plan.
Key takeaways (read these first):
IT strategy sets direction through strategic planning, it explains why you're investing and what "good" looks like.
An IT roadmap sequences work, it shows what you'll do next, who owns it, and when it lands.
Strategy should change slowly, roadmaps should change often (with discipline).
Your board needs outcomes and risk movement, not tool counts.
You can tighten both in 30 days without rewriting everything.
IT strategy is your "why" and "where", the roadmap is your "what" and "when"
If you remember one thing, remember this: strategy is intent, and the IT roadmap is execution timing. Strategy tells you where you're going and why. The IT roadmap tells you what you'll build, in what order, with what constraints.
Here's a quick way to compare them.
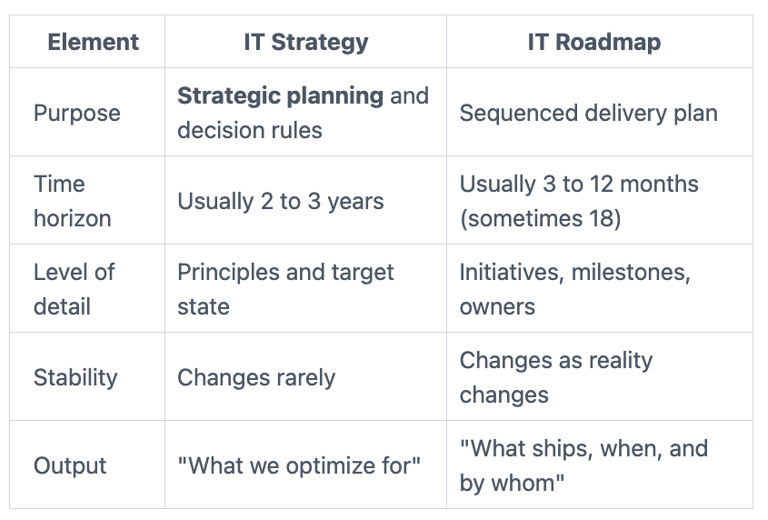
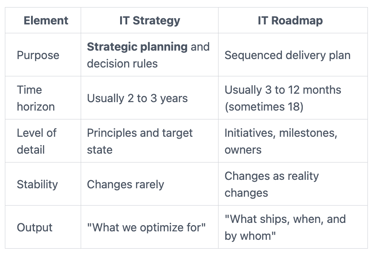
The takeaway from IT strategy and roadmap: when people argue about dates, you usually have a roadmap problem. When people argue about priorities, you usually have a strategy problem.
A simple example makes this real. Imagine you're modernizing identity and access as part of your digital transformation:
Strategy statement: "Standardize identity across all apps to reduce friction, reduce breach exposure, and speed partner onboarding."
Roadmap line items: "Consolidate SSO providers (Q2), enforce MFA for admins (Q2), migrate top 10 apps (Q3), retire legacy directory (Q4)."
If you want this to work in the real world, you need business strategic alignment, not security theater. That's where a strategic business-aligned CISO mindset helps, because it forces decisions to tie to growth, trust, and operational speed.
What an IT strategy should include so it is not just a slide deck
A useful IT strategy fits in your head and survives a hard budget meeting. It doesn't need 40 slides. It needs clear choices.
At minimum, make sure your IT strategy includes:
Business goals it supports: Growth targets, operating model shifts, M&A plans, customer experience goals.
Principles and decision rules: For example, "cloud computing-first unless regulated data requires otherwise," or "buy before build for commodity functions."
Target state: A plain description of what you're building toward (standard platforms and IT infrastructure, shared identity, clean data flows).
Risk posture: What risks you accept, and what you won't (especially around uptime, privacy, and fraud).
Investment themes: The 4 to 6 "buckets" for technology investments you'll fund repeatedly (modern apps, data, integration, security foundations, resilience, automation).
Success measures: A small set of metrics that show progress (cycle time, outage minutes, time to onboard, audit findings).
Cybersecurity and resilience belong inside the strategy as design constraints and trust outcomes, not as a separate plan that arrives late. When security is part of the "how we build," delivery gets faster, because you stop re-litigating basics.
What an IT roadmap should include so it is not just a wish list
A roadmap is a living plan you can inspect. It's also where optimism goes to die if you don't show constraints.
A usable roadmap includes:
Initiatives with clear outcomes (not vague tasks)
Dependencies (what must happen first)
Milestones and timing
Named owners (one throat to choke, with support roles around them)
Rough cost ranges, resource allocation, and capacity limits
Tradeoffs, including what you're not doing this cycle
Roadmaps should change more often than strategy. That's normal. What's not normal is changing dates without changing scope, staffing, or sequencing.
If your roadmap says everything happens in parallel, it's not a roadmap. It's a stress plan.
How to tell if you have a real strategy and a usable roadmap
You don't need a maturity model to diagnose this. You can run a 20-minute test in a leadership meeting. Put the strategy and the IT roadmap on screen, then ask a few yes or no questions.
Start with the strategy to question its effectiveness against the current state through a gap analysis:
Can your CIO, COO, and CFO repeat the strategy in one minute, using the same words?
Does it explain at least three "no" decisions you're willing to make, informed by a SWOT analysis?
Does it set principles that resolve arguments, for example build vs buy, or speed vs control?
Does it define what must not fail (critical IT infrastructure services, regulated data, revenue paths)?
Then check the IT roadmap:
Are the top 10 items connected to strategy themes, or are they pet projects?
Do dependencies look real, or are they missing because they're inconvenient?
Can you point to owners for each major milestone?
Do you see capacity (people and time), or only dates?
Reporting is where many teams break trust. If you want roadmaps that create confidence, you need performance metrics and key performance indicators that leaders can use. The framing in the hidden value of cyber metrics is a good reminder: outcome-linked measures beat technical noise every time.
If your strategy can't guide a tradeoff, and your roadmap can't survive a missed milestone, you don't have management tools. You have documents.
Green flags that your IT strategy is doing its job
You'll feel a good strategy at decision time.
Look for these signals:
It guides funding choices quickly, because priorities are explicit.
It explains tradeoffs in business terms (revenue, operational efficiency, customer trust, uptime, regulatory exposure).
Teams can repeat it without jargon, and they make consistent choices when you're not in the room.
It ties to growth and risk, so you can defend it to investors, regulators, and customers.
It uses a small set of measures, and you review them on a steady cadence.
Most importantly, a working strategy helps you say "no" with confidence. That "no" protects capacity for what matters.
Red flags that your roadmap is setting you up for surprises
Roadmap failure has a pattern. It starts with good intent, then collapses under too many simultaneous commitments.
Watch for these red flags:
Too many parallel projects, with no sequencing discipline
Dependencies that "aren't tracked," which really means "aren't managed"
No capacity view, so every plan assumes perfect execution
"Everything is priority one," which means nothing is
Dates without owners, or owners without authority
Security and compliance bolted on late, right before launch
Those gaps don't just cause delays. They compromise risk management, creating audit findings, outages, and incident exposure because foundational controls (identity, logging, backups) never get scheduled early.
How to connect IT strategy and roadmap to cyber risk and board oversight
When you connect IT strategy and roadmap well, governance becomes calmer. You stop getting surprised by risk, and you stop approving spend that doesn't deliver ROI.
At the board level, IT governance means you're not trying to run projects. You're trying to ensure three things:
Key stakeholders know what the organization is building toward, including its strategic objectives and future vision.
Execution is realistic and inspectable.
Risk moves down in a measurable way.
That's why good oversight ties strategy, roadmap, and cyber risk into one picture. If you want a practical framework for that level of oversight, cybersecurity governance for boards is a strong reference point for decision rights, accountability, and what "good" looks like without turning directors into technologists.
Turn strategy into a few "guardrails" that keep delivery and security aligned
Guardrails are where strategy becomes usable day to day, supporting strategic alignment between delivery and security within your broader digital strategy. They prevent each project from re-arguing basic safety and trust expectations.
Here are sample guardrails you can adopt in plain language:
Standard identity: All key apps use one identity standard (SSO plus MFA), no exceptions without approval.
Encrypt sensitive data: Customer and regulated data stays encrypted in transit and at rest.
Vendor risk thresholds: Critical vendors must meet minimum controls, or you don't sign.
Logging requirements: Important systems generate security logs that you can retain and search.
Recovery expectations: Critical services have tested backups and clear recovery time targets.
Admin control: Privileged access is limited, monitored, and reviewed on a schedule. These cybersecurity measures make roadmaps faster because teams stop debating basics on every project. They also reduce rework, since "secure enough" is defined up front.
Make the roadmap inspectable with metrics leaders can actually use
To govern well, you need a reporting set that is simple and consistent. Aim for four buckets, each tied to outcomes:
Delivery health: Are the top initiatives on track, and what changed since last month?
Risk burn-down: Which top risks decreased, stayed flat, or increased, and why?
Resilience readiness: Backup test success, recovery exercise results, and major outage lessons learned.
Decision points: Items that require leadership calls (scope changes, accepted risk, funding shifts for technology investments).
Use a monthly cadence for the exec team and a quarterly cadence for the board. Keep the metrics stable for long enough to show trend. Also, avoid tool counts as your headline story. Tools don't equal control, and activity doesn't equal reduced exposure.
If your dashboard can't answer "Are we safer, and can we ship faster?", it's not a leadership dashboard.
A simple 30-day approach to tighten your IT strategy and roadmap (without a big rewrite)
You don't need a big transformation program to get clarity on your implementation roadmap. You need focused decisions, tight language, and a roadmap that respects capacity.
If you're missing senior ownership for cyber risk decisions, or you need a fast reset without waiting for a full-time hire, a fractional CISO model can help you set priorities, translate risk into business choices for your IT strategy and roadmap, and create reporting that a board can inspect.
Week 1: Get clear on outcomes, risk appetite, and what must not fail
Run a short workshop with your key stakeholders (CEO, COO, CFO, CIO, and security lead). Keep it tight.
In one page, write:
Your top 3 business goals for the next 12 months
The critical services that must not fail
Your risk appetite in plain terms (what you won't tolerate)
Who decides when tradeoffs appear (and who escalates)
This step reduces debate later, because you agree on stakes first.
Weeks 2 to 4: Re-sequence the roadmap around dependencies and trust outcomes
Next, take your current roadmap and do a reset around reality.
Map dependencies, then pull foundational items earlier, especially identity, logging, backups, and segmentation. Pause low-value work that consumes scarce staff. Confirm each milestone has a named owner and an estimated capacity ask through project portfolio management.
Before you lock dates, validate with finance and operations. If staffing or vendor lead times don't match the plan, the dates are fiction. Adjust scope, sequence, or both, then publish the updated IT roadmap with explicit tradeoffs.
Conclusion: Keep direction stable, keep plans honest
Key takeaways (quick recap):
IT strategy and roadmap work as a pair, direction plus sequenced execution.
Strategy should make tradeoffs easier, and roadmaps should make work inspectable.
Board confidence rises when you report outcomes, risk movement, and decision points.
Once you separate "why" from "when," your meetings get cleaner. Your teams stop thrashing. Your risk reductions become predictable, not accidental, aligning your IT roadmap with business goals.
FAQs
Who owns the IT strategy? You want a clear owner, often the CIO, with shared accountability across the executive team.
How often should each change? Strategy usually refreshes annually. Roadmaps often update monthly, with a formal quarterly reset.
Can you have multiple roadmaps? Yes, as long as they roll up to one set of priorities and one capacity reality.
Where does cybersecurity fit? It belongs inside strategy as guardrails and trust outcomes, including emerging technologies, and inside the roadmap as scheduled, owned work.
What does the board need to see? Top risks, trend over time, major decisions, and proof that resilience is improving, with cybersecurity integrated to support strategic objectives.
Next step: review your current artifacts against the green and red flags, then schedule a decision meeting with owners to lock priorities, sequencing, and the "not doing" list.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
