Third Party Risk Management Advisor. The 30-Day Reset Plan for Vendor Oversight
Get a 30-day reset with a Third Party Risk Management Advisor, build one vendor list, risk tiers, checks, contract fixes, and a board dashboard.


Vendor risk usually doesn't fail because you "ignored security." It fails because you can't see what you own, who touches it, and which partners can hurt you the fastest. Meanwhile, your vendor list keeps growing. A new SaaS tool shows up every week. Renewal dates sneak past. Then an audit, a customer questionnaire, or a board meeting forces the question you don't want to answer: "Which vendors are highest risk, and what are we doing about it?"
A Third Party Risk Management Advisor helps you get control without turning your business into a paperwork factory. In plain language, they help you set clear rules, choose the right checks, and keep vendors accountable over time. You stop guessing, and you start showing consistent proof.
This 30-day reset plan breaks the work into four weeks. In Week 1, you build one usable vendor inventory and risk tiers. In Week 2, you set baseline controls and evidence requirements. In Week 3, you fix contract gaps and create a simple intake gate. In Week 4, you install a cadence and dashboard that leadership can read. If you need experienced security leadership to drive this quickly, consider bringing in an experienced CISO for hire in vendor oversight to keep decisions moving.
Key takeaways
You can create a single vendor inventory in 7 days, even with messy data.
Three risk tiers stop your team from wasting time on low-impact tools.
Baseline controls by tier reduce audit friction and vendor arguments.
Contract basics (breach notice, audit rights, subcontractors) cut surprise costs.
A small dashboard and re-review triggers keep oversight consistent all year.
Days 1 to 7, get control of your vendor list and decide what matters
Perfection is the enemy this week. You're building clarity fast, so you can act. Think of this like cleaning a garage before you remodel. You don't need new shelves yet, you need everything in one place.
Your "third parties" are bigger than procurement's vendor file. They include SaaS apps, contractors, MSPs, data brokers, outsourced support, and any partner that touches your systems or data. The goal is one list that answers three business questions: what they do, what they can access, and what breaks if they fail.
A complete list is rare. A usable list is powerful.
Build a "one list" inventory in one week, even if your data is scattered
Start where money and access show up. Pull vendor names from accounts payable and corporate card spend. Export your SSO app catalog (Okta, Entra ID, Google). Ask procurement and legal for active contracts. Check IT tickets for recurring vendor support. Then scan each department's "must-have" tools, especially finance, HR, sales, and marketing.
When you find shadow IT, don't lead with blame. Lead with curiosity. People buy tools because they're trying to hit a goal. Your job is to make those tools safer, not to embarrass the buyer.
Capture a minimum set of fields in a spreadsheet or GRC tool. Keep it simple enough that business owners will cooperate:
Vendor name and service provided
Business owner (one accountable person)
Renewal date and contract status (signed, expired, click-through)
Annual spend (rough is fine)
Access type (none, user-level, admin, production, support)
Data types touched (customer, employee, payment, health, IP)
Integrations (SSO, API, data sync, agents)
Hosting region (US, EU, other, unknown)
Subcontractors (if known)
Last review date (or "never")
If you want practical ideas for driving this as an executive program (not a technical scavenger hunt), pull patterns from practical security leadership insights on how governance work actually sticks when time is tight.
Triage vendors into three risk tiers using plain questions
Tiering is your time machine. It keeps you from treating a social media scheduler like a payroll processor.
Use plain triggers that non-security leaders understand. Ask:
Do they have production access or admin rights?
Do they store customer or employee sensitive data?
Do they process payments or handle regulated data?
Do they support a business-critical operation?
Would an outage stop revenue, service delivery, or safety?
Would a failure create a compliance violation?
Here's a simple way to express tiers:
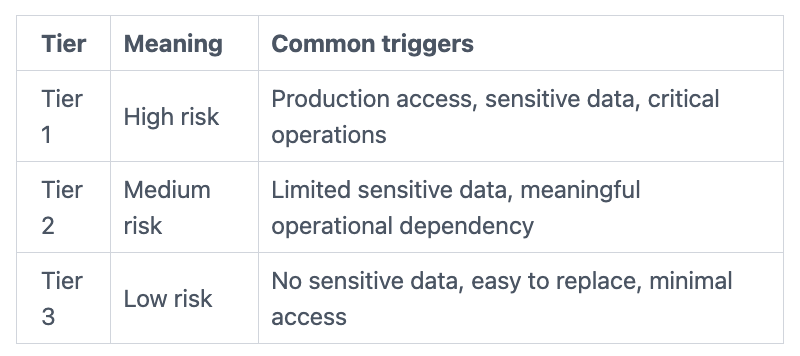
A quick example helps make it real. Your payroll provider is usually Tier 1 because it handles employee data and pay. Your customer support platform might be Tier 1 or Tier 2 depending on data access and integrations. A design tool used by one team is often Tier 3 if it has no sensitive exports.
Days 8 to 15, set your baseline controls so you stop guessing
Once you've tiered vendors, you can set "this is what good looks like" per tier. That's where executive sanity returns. Vendors stop negotiating every requirement from scratch, and internal teams stop improvising.
Keep controls measurable. You're not trying to quote NIST or ISO in meetings. You're trying to map to the same ideas: access control, change management, incident response, and recovery.
If your board or customers are focused on trust signals, align your vendor program to the bigger story of accountability. That's how you build confidence with buyers and regulators, and it's a core theme of being a digital trust expert and CISO advisor.
Define the minimum proof you need from vendors, and what you will accept
Ask for evidence that matches the tier. For mature vendors, you can accept SOC 2 Type II, ISO 27001 certification, SIG Lite, or a CAIQ. For higher risk, request a pen test summary, vulnerability management statement, incident response overview, and business continuity or disaster recovery test evidence.
Early-stage vendors often won't have SOC 2 yet. That doesn't mean you can't use them. It means you control exposure. Use compensating controls like limited access, no production data, shorter contract terms, and a written security roadmap with dates. Also keep a "right to audit later" clause for when the relationship grows.
Decide how you will assess, questionnaires, calls, or independent signals
Match the method to the risk. For Tier 3, a short questionnaire may be enough. For Tier 2, add document review. For Tier 1, run a focused review call with security and the business owner, then document decisions.
External security ratings can help, but treat them as a signal, not the decision. They're useful for spotting drift, not for replacing your judgment.
Set a timeline you can actually keep. A "good enough" rule: Tier 1 gets reviewed within 30 days (or before go-live), Tier 2 within 60 to 90 days, Tier 3 on renewal or when something changes.
Days 16 to 23, fix the contract gaps that create real business risk
Contracts are your control surface when you don't own the environment. If you wait until a breach to learn what a vendor "must" do, you're already paying extra.
This week, focus on the clauses that reduce loss and confusion. Keep them readable. You want leaders to approve them, and vendors to follow them.
When you're running governance under pressure, experience matters because decisions stack up quickly. If you need a leader who can keep risk, legal, and operations aligned, look for guidance that reflects leading risk and governance programs under pressure.
Add a short list of "must-have" clauses for your highest-risk vendors
For Tier 1 vendors, keep a short "must-have" set that procurement and legal can reuse:
Data ownership and use limits, including deletion on termination
Breach notification timeline that matches your obligations
Security requirements (MFA, encryption, least privilege, logging)
Subcontractor flow-down and approval for material changes
Audit rights (or at least evidence rights and cooperation language)
Vulnerability and patch expectations with time frames for critical fixes
Evidence retention for logs and investigation support
Right to terminate for cause if risk becomes unacceptable
Service levels for uptime, support, and recovery targets
Compliance obligations relevant to your business (privacy, payments)
Cyber insurance when it fits the exposure and vendor size
You don't need legal poetry. You need clear commitments that reduce surprise.
Make renewals and new purchases go through a simple gate, not a bottleneck
A gate is not a traffic jam. Keep it light for low-risk tools, and strict for Tier 1.
Define a short intake path: the requester submits the basic fields, security assigns a tier within two business days, then approvals follow the tier. A simple RACI often works: Business Owner owns the relationship, Procurement owns the purchase, Legal owns terms, Security owns risk controls, Privacy owns data use.
For urgent exceptions, allow a time-boxed approval with limits (reduced access, no sensitive data, short term), then require a full review after launch.
Days 24 to 30, put vendor oversight on autopilot with a clear cadence
Most vendor programs fail after the first push because no one owns the rhythm. Your goal this week is a repeatable cadence that takes less time than firefighting.
Pick a monthly operating meeting for Tier 1 and Tier 2 oversight. Keep it tight. Review what changed, what's overdue, and what needs executive help. Then create a quarterly board-ready view that highlights trends and exposure.
Create a vendor risk dashboard your board can read in two minutes
Before you build a fancy report, choose a few metrics that show control and movement:
Number of Tier 1 vendors, and top dependencies
Assessment completion rate by tier
Overdue findings (especially high-risk items)
Open high risks and target dates
Upcoming renewals in the next 90 days
Vendor incidents that affected your service
Business continuity test status for Tier 1 vendors
Concentration risk (top vendors by spend or operational dependency)
Report trends, not noise. If Tier 1 overdue findings drop each month, leadership sees progress. If a single vendor creates repeated incidents, leadership sees a decision point.
Set triggers for re-review so you catch risk when things change
Re-review doesn't need drama. It needs triggers. Reassess when there's a new integration, a data type change, a privilege increase, breach news, an acquisition, a major outage, a subcontractor change, a renewal, or a new regulation that touches the service.
Keep monitoring proportional. Tier 3 doesn't need constant attention. Tier 1 does.
A Third Party Risk Management Advisor helps you run these reviews without burning out your team. They keep owners accountable, keep evidence organized, and keep exceptions from becoming the new normal.
When you should bring in a Third Party Risk Management Advisor (and what to expect)
Outside help pays off when speed and credibility matter more than internal debate. That's often the case if you're scaling fast, responding to audit findings, recovering from an incident, or dealing with vendor sprawl that no one "owns." It also makes sense when regulated data is in play, or when procurement discipline is inconsistent across teams.
In the first 30 days, you should expect tangible deliverables, not vague recommendations. A solid advisor will help you produce: a single inventory, a tiering model, baseline requirements by tier, an evidence approach, a contract playbook, an intake workflow, and a board-ready dashboard.
Just as important, you should expect a plan that adjusts as your company changes. Vendor oversight can't stay frozen while your products, markets, and partners shift. That's why it helps to work with someone who shows how an experienced CISO learns and adapts programs over time, instead of forcing a one-time template onto your business.
Conclusion
In 30 days, you can go from vendor sprawl to a program you can explain in plain language. Week 1 gives you one list and three risk tiers. Week 2 sets baseline controls and proof, so you stop negotiating from scratch. Week 3 closes contract gaps and creates a fast intake gate. Week 4 installs a cadence, metrics, and triggers, so oversight stays consistent.
Vendor oversight isn't about paperwork. It's about business continuity, regulatory confidence, and trust you can defend when pressure hits.
Start the reset this week by building the inventory and assigning tiers. Then decide what "good enough" evidence looks like for each tier. If your team is stretched, bring in help to keep momentum and reduce rework.
FAQ
What counts as a third party for vendor risk?
A third party is any external company or person that touches your data, systems, or operations. That includes SaaS apps, contractors, MSPs, and data brokers.
How often should you reassess vendors?
Reassess Tier 1 vendors at least annually, and sooner when risk changes. For Tier 2, review on a set cycle or renewal. For Tier 3, reassess on renewal or major change.
SOC 2 vs ISO 27001, which is better for vendor oversight?
SOC 2 Type II shows how controls operated over time, based on the report scope. ISO 27001 shows a certified management system. Either can work, as long as scope matches your risk.
How do you handle small vendors without certifications?
Limit access, limit data, and use short contract terms. Ask for basic evidence like MFA use, encryption practices, patching approach, and an incident response plan summary.
What should you do after a vendor breach?
First, confirm whether your data or access was involved, and document facts. Next, trigger contract rights, require a root-cause summary, and update your tiering and controls based on what you learn.
Who should own vendor risk inside the company?
A business owner should own each vendor relationship and decisions. Security, privacy, legal, and procurement should set rules and review evidence, but they shouldn't "own" every vendor by default.


