Application Rationalization Assessment Framework: What to Include
Use this application rationalization assessment framework to set scope, score apps, cut risk, and give leadership clear, defensible decisions.

If your company has too many apps, unclear ownership, rising spend, and patchy risk visibility, you already know the problem. The hard part is turning that mess into decisions.
An application rationalization assessment is a structured review of every business application. You use it to decide what to keep, retire, replace, consolidate, or modernize. The goal is not only cost control. It is also better governance, lower risk, simpler operations, and clearer choices for leadership.
This work matters most when your environment grew fast, changed through M&A, or became too hard to explain in a leadership meeting. If you can't say which apps matter, who owns them, what they cost, and what risk they carry, you need a stronger framework.
Start with scope, goals, and decision rules
A strong application rationalization assessment starts with boundaries. Without them, the effort turns into a vague inventory project that drags on and produces little.
Define which applications, business units, and environments you will review
Set scope early. Include the business units, regions, and app types you will review. That usually means production apps, legacy platforms, SaaS tools, custom-built systems, and shared services. Shadow IT should be included where you can find it.
Also separate core systems from niche tools. A payroll platform is not the same as a team-level file transfer app. In the same way, note whether you are reviewing only the current-state portfolio or also planned replacements and in-flight projects.
Set clear outcomes so every stakeholder knows what the assessment should deliver
State the business goals in plain terms. You may want to reduce overlap, lower support cost, cut vendor sprawl, improve security, or support modernization. Pick the few goals that matter most.
Then define the outputs. A useful assessment usually ends with a rationalized app portfolio, a heat map of risk and value, retirement candidates, consolidation options, modernization priorities, and a phased action plan. If the work must support executive or board review, say that up front.
If scope is fuzzy, every later decision becomes a debate.
Collect the right data for every application, not just the easy facts
Basic inventory data is not enough. Name, vendor, and renewal date won't tell you what to do. A useful application rationalization assessment depends on decision-ready data across business, technical, financial, and risk areas.
Capture business value, process fit, and who depends on the application
Start with business context. Record the app's purpose, the process it supports, the user groups it serves, and how critical it is to daily work. Add geographic use, transaction volume, and the likely impact if it fails.
Ownership matters just as much. Identify the executive owner, business owner, and technical owner. When ownership is vague, risk usually follows. So does delay.
Document technical health, integrations, and architecture constraints
Next, capture how the application actually works. Note the hosting model, tech stack, age, support status, and known performance issues. Record how much customization exists, because heavily tailored apps are harder to replace.
You also need dependency data. Map upstream and downstream links, APIs, identity integration, data flows, and recovery needs. Otherwise, you may retire one app and break five others.
Measure cost, contract exposure, and vendor dependence
Now get honest about cost. That means license cost, infrastructure cost, support cost, change cost, and internal labor. Hidden effort often keeps weak apps alive long after their value fades.
Contract terms matter too. Note renewal dates, exit limits, pricing traps, and vendor concentration risk. Many leaders think they have an app problem when they also have a contract problem.
Include risk, compliance, and control data from the start
Risk data should not be an afterthought. Capture data sensitivity, access model, known flaws, audit findings, control gaps, unsupported software, privacy duties, and regulatory impact.
That gives you a more defensible basis for action. It also makes reporting cleaner when leadership or the board asks why a low-use app is still in service. If your findings need to hold up under board scrutiny, the discipline described in this board cybersecurity advisor perspective is a useful benchmark.
Use a scoring model that helps you decide what to keep, retire, replace, consolidate, or modernize
Raw data alone does not create decisions. You need a scoring model that turns facts into a clear recommendation. Keep it simple, weighted, and easy to explain.
Score each application against a short list of criteria leadership can understand
Use five to seven criteria, not fifteen. For most portfolios, that is enough. Good choices include business criticality, user adoption, functional fit, total cost, cyber and compliance risk, technical health, and strategic fit.
Weight the criteria to match your goals. If risk reduction matters most, give that more weight. If post-M&A overlap is the issue, functional fit and duplicate capability may carry more weight. Fewer criteria usually work better because they are easier to defend and easier to review.
Create simple decision categories and define what each one means
Use a short set of categories and define the trigger for each one.
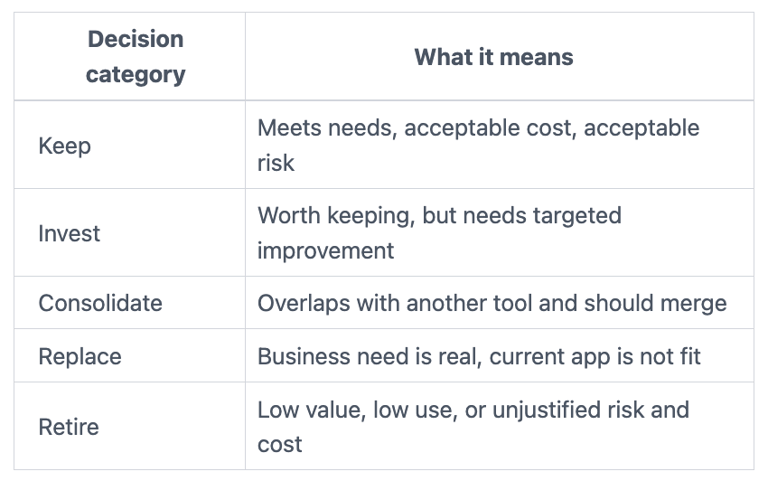

This keeps reviewers aligned. It also reduces late-stage arguments over labels.
Turn findings into a roadmap with owners, timing, and governance
An application rationalization assessment creates value only when it leads to action. So move from analysis to a sequenced roadmap based on risk, effort, business impact, and timing.
Prioritize quick wins, high-risk issues, and longer-term modernization work
Group actions into waves. Near-term work may include retiring unused tools, ending duplicate licenses, or assigning missing owners. Mid-term work may include consolidating platforms or fixing contract exposure.
Longer-term work often means replacing fragile legacy systems or modernizing shared services. Those moves take more planning, so don't bury them in the same queue as easy wins.
Assign decision rights, reporting cadence, and review checkpoints
Name the people who own the tradeoffs. That often includes an executive sponsor, business owners, enterprise architecture, finance, security, and procurement. When nobody owns the decision, nothing moves.
Set a review cadence as well. Monthly reviews help track actions, costs, and blocked decisions. Quarterly reviews help leadership test whether the portfolio is actually getting simpler, safer, and easier to explain. If your organization lacks that level of senior oversight today, fractional leadership for cyber priorities can help restore decision rhythm without waiting for a full-time hire.
In short, governance keeps the roadmap alive. Without it, rationalization becomes another slide deck.
A good framework gives you more than a cleaner app list. It gives you defensible decisions. Start with scope and goals, collect complete data, score apps with a simple model, define clear categories, and turn findings into a governed roadmap.
When you do that well, you get a cleaner portfolio, clearer ownership, lower risk, and a plan leadership can inspect. That is what a sound application rationalization assessment should deliver.


