Do I Need a CISO? 9 Signs It's Time to Hire One
Do I Need a CISO? Use 9 signs to spot when risk hits revenue, uptime, or sales, then choose full-time, fractional, or interim leadership.


A few years ago, security could sit inside IT and still feel "good enough." Now information security shows up as trust, deal friction, regulatory exposure, and business continuity risk. If you're C-suite, such as a CEO, founder, or member of the board of directors, you're not trying to become a security expert. You're trying to keep the business moving without ugly surprises.
A CISO (Chief Information Security Officer) sets direction, reduces risk, builds readiness for incidents, and makes tradeoffs clear. They translate security work into business decisions you can approve, defer, or fund. When you have a strategic, business-aligned CISO, security stops being a pile of tasks and becomes a cybersecurity strategy you can inspect.
Use the self-check below. These are nine real-world signs, not fear tactics.
Key takeaways you can use today
You need a CISO when cyber risk management starts affecting revenue, uptime, or board confidence.
Hiring a CISO should change decision speed, ownership, and reporting quality.
If you're not ready for full-time, start with a fractional CISO or interim leadership.
Ask for a 30 to 90-day plan with owners, milestones, and proof risk is dropping.
Don't buy more tools until you can explain what risk they reduce.
Move from compliance to confidence to strengthen your cybersecurity posture by focusing on outcomes, not checklists.
In the first conversation, test how they explain risk in plain language.
If you want fewer surprises, you need clear decision rights and a plan you can inspect
Surprises happen when nobody knows who decides. A CISO establishes clear decision rights: who owns what, who can accept risk including regulatory compliance, and who can approve spend. Without that clarity, work stalls, exceptions stack up, and the loudest voice wins.
A CISO helps you define risk acceptance in simple terms that align with business objectives, then creates an operating rhythm. Think monthly risk reviews, a visible cybersecurity strategy roadmap, and short executive updates that end with a decision, not a debate. You stop guessing where the exposure is, because the same top risks show up until they move.
This is also where board of directors oversight improves. Instead of "security updates," you get governance: what changed, what you're accepting, and what you need to fund next. If you want a practical GRC model for that, start with cybersecurity governance for boards.
If you can't point to who decides and what the plan is, you're not managing risk, you're hoping.
The 9 signs it's time to hire a Chief Information Security Officer (CISO) (or bring in interim help)
You don't need all nine signs. Seeing two or three at once is usually enough to act for your SMB. The patterns below show up most when security has outgrown ad hoc ownership.
Signs tied to business risk, growth, and trust
You cannot explain your top cyber threats in plain language.
What it looks like: risk conversations turn into tool names, charts, or technical arguments. Why it matters: if leaders can't describe risk, they can't accept it or fund it. What good looks like: a one-page list of top risks tied to money, downtime, and customer impact, with owners and next steps.You are growing fast, and security is lagging.
What it looks like: new markets, new apps with cloud security needs, and new data appear faster than your controls. Why it matters: growth expands your attack surface and threat landscape, and the blast radius grows with it. What good looks like: security guardrails built into launches, clear priorities, and a roadmap that matches the business calendar.Customers or partners are asking tougher questions about information security, and sales is stalling.
What it looks like: security questionnaires bounce between IT, legal, and sales, and nobody "owns" the answer. Why it matters: enterprise buyers read confusion as risk. What good looks like: fast, consistent responses, a simple control narrative, and evidence that matches what you claim.You've had a near miss, and fixes are still ad hoc.
What it looks like: phishing fraud, a data breach, an outage, or a ransomware alert, followed by a burst of activity, then drift. Why it matters: near misses are tuition. If you don't learn, you'll pay again. What good looks like: a clear after-action review, assigned owners, and a short list of fixes that actually reduce repeat risk.Compliance is becoming a treadmill, and you still don't feel safe.
What it looks like: SOC 2 or ISO 27001 work consumes the team, yet leadership still can't answer "Are we safer?" Why it matters: passing an audit doesn't guarantee resilience. What good looks like: compliance mapped to real cyber threats and controls that improve recovery via the NIST Cybersecurity Framework, with fewer exceptions. When you're ready, use how CEOs should vet a CISO to avoid hiring someone who only knows the paperwork.
Signs tied to governance, leadership gaps, and readiness
The board wants better oversight, but reporting is shallow or too technical.
What it looks like: everything is green, yet directors still feel uneasy. Why it matters: boards need decisions, not status theater. What good looks like: trends, thresholds, and explicit tradeoffs, plus a record of what risk you accepted and why. A CISO can deliver this clarity.You have too many tools, not enough outcomes.
What it looks like: spend rises, alerts rise, and confidence stays flat, even with vulnerability assessments piling up. Why it matters: tools don't create accountability. They can also create noise that hides real issues. What good looks like: a smaller set of well-owned controls, tied to measurable outcomes. If you need senior leadership that can reset direction quickly, consider an experienced CISO for hire.Incident response is unclear (who leads, who decides, who talks).
What it looks like: there's an incident response plan somewhere, but you haven't practiced it, and roles blur under pressure. Why it matters: the first hour drives cost, downtime, and reputational damage. What good looks like: named roles, a call tree, pre-approved outside help, and a tabletop exercise schedule. In urgent windows, an interim security executive can stabilize this fast, much like a CISO would.Security ownership is fragmented, and priorities clash.
What it looks like: IT, product, legal, and risk all touch security, but nobody can break ties. Why it matters: gaps live in the seams between teams. What good looks like: one accountable leader, written decision rights, and a shared backlog including security awareness training. If you're not ready for a permanent hire, a fractional CISO can create structure without waiting months. For the board's role during a crisis, align expectations with board incident response oversight.
If you see the signs, choose the right CISO model and avoid common hiring mistakes
Not every organization needs a full-time Chief Information Security Officer right away. The right CISO model depends on urgency, complexity, and how much internal execution muscle you already have.
Here's a simple way to decide:
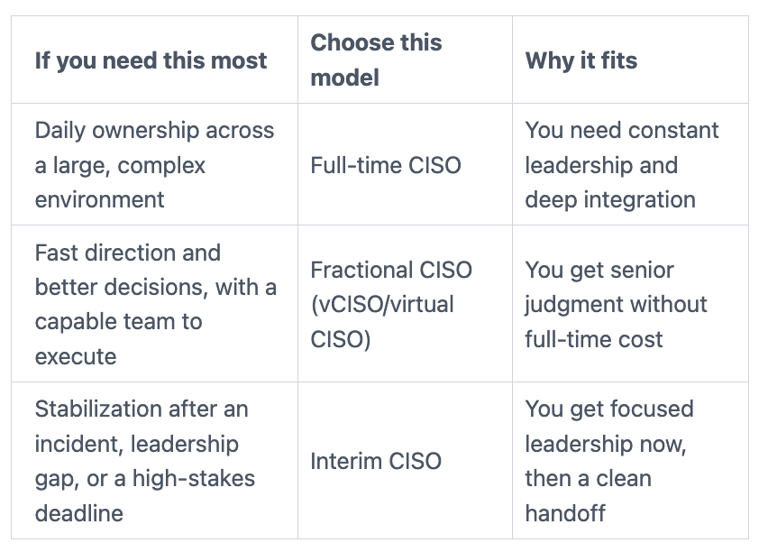
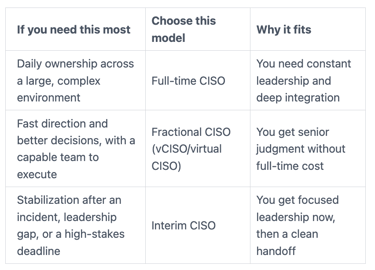
No matter the model, full-time, fractional, interim, or outsourced CISO, avoid the mistakes that cause "security motion" without results:
Hiring for tools, not outcomes: you need risk reduction to improve cybersecurity posture, not a shopping list.
Unclear mandate: if the CISO role can't set priorities for information security, it can't lead.
No access to the CEO or board: security becomes a middle-management struggle.
Expecting one person to do everything: strategy, operations, and engineering are different jobs.
Underinvesting in fundamentals: identity, backups, logging, and patch discipline still matter most.
If you want a practical screen for leadership thinking, use these CISO interview questions for CEOs and CHROs to keep the process grounded in real outcomes.
What to ask in the first conversation so you know you're hiring a leader, not a firefighter
The first conversation should reveal how they think, not how much jargon they know. Use questions like these, and listen for calm tradeoffs.
What are the first three things you'll do in your first 30 days here?
How do you rank risks when every team says their issue is urgent?
What do you need from me (CEO) to be effective?
How do you brief a board in five minutes when the news isn't good?
Which metrics do you use to show progress without creating reporting overhead?
How do you work with product and engineering so releases don't turn into battles?
What would make you recommend a fractional CISO or interim approach instead of full-time?
If you want to align those answers with oversight expectations, review board oversight and CISO performance metrics so you can measure leadership, not just activity.
FAQs about hiring a CISO
Do I need a full-time CISO?
Not always. If risk is rising but your environment is still manageable, fractional leadership can be the right first step.
How much does a CISO cost?
Costs vary widely by market, scope, and seniority. What matters is whether you need full-time ownership from a CISO, or targeted leadership to set direction and governance.
Can my CIO be the CISO?
Sometimes, but it can create conflicts between the Chief Information Officer and Chief Information Security Officer roles. A Chief Information Officer often gets rewarded for speed and delivery, while a CISO must slow things down at times and challenge assumptions.
When should I hire fractional first?
Choose a fractional CISO when you need executive decisions and a plan, but you don't need a full-time leader in the building every day.
What does a good CISO deliver in 90 days?
You should expect a plain-language risk view, tightened decision rights, a realistic roadmap, and improved incident readiness through a tested exercise.
How do I know if my security program is working?
Look for fewer unknowns, faster detection and response, and steady progress on the top risks. Also measure trends that leadership can act on, not vanity counts. For a useful framing, see the hidden value of cyber metrics.
Conclusion
When you ask, Do I Need a CISO, you're really asking if your current setup can keep trust intact during your digital transformation. If you saw multiple signs, you don't need more tools first. You need clearer leadership, clearer decision rights, and governance that holds up under pressure, including disaster recovery paths.
Start small this week: write your top five cyber risks in plain language, name who decides for each, and set a board-ready update cadence you can keep. If you want help choosing the right CISO model or pressure-testing your situation, you can engage a CISO advisor and get a clear, practical path forward.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
