Fractional CISO Services for SMBs: A Practical Buyer's Guide
Fractional CISO Services for SMBs, learn what you should get in 30 to 90 days, how pricing works, and the questions that prevent costly misfires.


In 2026, you don't just face "more threats." You face more questions. Customers send security questionnaires before they sign. Insurers ask about backups and MFA like they're underwriting a building. Vendors connect into your systems, which expands risk you don't fully control. Meanwhile, ransomware pressure hasn't eased, it's just gotten more targeted.
If you're an SMB leader, you may feel the squeeze: you need cybersecurity leadership, but a full-time CISO can be out of reach. That's where Fractional CISO Services fit. In plain terms, a part time CISO is an experienced security leader you bring in part-time, focused on outcomes, not busywork. This delivers cost effective security for smaller organizations.
This guide helps you buy smart. You'll learn what you should get in the first 30 to 90 days, what pricing usually depends on, what to ask in interviews, and how to avoid the common traps. If you want a baseline on what this support can look like, start with fractional CISO support for SMB security control.
Key takeaways to choose the right fractional CISO without wasting months (or money)
Look for decision-making, not advice-only, from your fractional or Virtual CISO: You need someone who sets priorities and drives follow-through.
Expect real outputs by day 30: A Risk Assessment with top risks, an incident "first hour" plan, and a short roadmap for your Information Security Program with owners.
Scope should match your reality: If you're mid-incident or failing audits, you'll need more time and cadence.
Price follows complexity: More regulated data, more locations, or more vendors usually means higher cost.
Ask how they'll work with your IT lead and MSP: If that relationship is fuzzy, execution will stall.
Demand board-ready reporting: You should get short updates that lead to clear decisions.
Measure progress in business terms through Business Objective Alignment: Tie security work to uptime, sales friction, and risk reduction, using guidance like tying security to business goals.
Do you need a fractional CISO right now, or something else?
You don't need a fancy title, you need the right kind of help. The fastest way to self-qualify is to ask, "What's missing today, leadership, execution, or both?"
A fractional CISO is part-time Executive Level Guidance. You hire them to set direction, prioritize risks, and create a security operating rhythm through cyber risk management. They're usually best when you have people who can implement, but nobody senior enough to make the hard tradeoffs.
An interim CISO or interim security executive is different. Interim usually means you need a strong push right now, often because something is on fire (or close). Think incident recovery, a sudden leadership gap, a failed audit, or major deadlines. If you need fast change with clear authority, interim security leadership when you need fast change is often the better fit.
A Virtual CISO can mean fractional leadership, or it can mean a more templated Virtual CISO service package. The label varies. So you have to inspect what you're actually buying.
A security consultant might do assessments, policies, or a specific project, much like a cybersecurity expert. That's useful, but it can fail if nobody owns the decisions afterward.
An MSP security add-on often improves tooling and monitoring. That's helpful, but it's not the same as executive leadership. Your MSP can run tools. Your CISO sets priorities, resolves conflicts, and speaks to executives and the board in plain terms.
The decision criteria are usually straightforward:
Urgency: Are you reacting to an incident, or preventing one?
Deadlines: Are regulatory compliance dates, renewals, or customer demands hitting soon?
Leadership gap: Does security have an owner with authority?
Change events: Are you doing M&A, launching a new product, or entering enterprise sales?
Clear signs you have a leadership gap (even if you have good tools)
Use this quick checklist to spot "busy but stuck" security:
You don't have a living risk register with owners and dates.
Incident response exists on paper, but you haven't practiced it.
Security priorities change weekly, based on whoever shouts loudest.
Budget decisions feel random, not tied to top risks.
Vendor risk reviews happen informally, if at all.
Audits turn into a scavenger hunt for evidence without compliance gap analysis.
Customer questionnaires slow deals because answers aren't ready.
Admin access is messy, and nobody owns cleanup.
Backups exist, but restore tests aren't routine.
The CEO still gets surprised by security issues.
When to pause and hire full-time, or bring in an interim CISO first
Fractional isn't always the right move, depending on your security maturity level. You should pause if:
You need 24/7 security operations, and you don't have a team.
You're in heavy regulation with constant evidence work (and you're behind).
You have a funded, enterprise-scale transformation already approved.
You're in active incident recovery, with legal and insurer pressure.
You're about to close a major acquisition and need deep diligence fast.
Rule of thumb: if you need a leader "in the building" most days for the next quarter, fractional may be too thin. In that case, consider engaging an experienced CISO for high stakes needs or interim support, then transition to fractional once the surge work ends.
What good Fractional CISO Services look like for an SMB (deliverables, cadence, and outcomes)
Good fractional leadership feels less like a report, and more like a simple operating system. You should see clarity, then momentum in your Cybersecurity Program.
First, your fractional CISO runs a focused Risk Assessment. That means understanding your "crown jewels" (systems, data, and processes you can't afford to lose), your current controls, and your biggest exposure paths. They won't boil the ocean. They'll identify what changes decisions fast.
Next, they align risk to the business with a Security Strategy. If enterprise sales is your growth engine, customer assurance becomes a priority. If uptime drives revenue, resilience and recovery take the lead. If you handle sensitive data, access control, monitoring, and paths to SOC 2 or ISO 27001 compliance rise quickly.
Then you get a Strategic Security Roadmap you can execute. It should be staged, realistic, and matched to your team's bandwidth. A strong plan also includes quick wins, because early traction builds trust across leadership.
Governance is part of the package, forming the Information Security Program. That doesn't mean heavy process. It means you know who owns what, how risk decisions get made, and how progress gets reported. If you've lived in checkbox land, the goal is to shift toward outcomes, using a mindset like moving beyond checklists to real confidence.
Finally, a good fractional CISO coaches your internal leaders. Your IT lead, engineering manager, and ops leaders should get clearer expectations, not extra meetings that go nowhere.
If all you get is a slide deck, you bought explanation, not leadership. Decks are fine, but only when they come with decisions, owners, and execution support.
Your first 30 to 90 days, what you should actually receive
You should ask for tangible outputs, not vague "strategy work":
A short current-state Risk Assessment summary (what's solid, what's risky, what's unknown).
A prioritized risk list in plain language, tied to business impact.
A 12-month roadmap with milestones, owners, sequencing, Data Protection Strategies, and Security Awareness Training.
Minimum security standards (MFA rules, patch targets, backup requirements).
Incident Response Planning with a runbook and a tabletop exercise plan.
A board-ready reporting template (one page, decision-focused).
A simple budget plan with ranges and a few options.
"Slide decks only" is a red flag unless they're paired with action and follow-through.
How a fractional CISO should work with your MSP, IT lead, and vendors
Execution depends on clean collaboration. So you want decision rights spelled out early.
In most SMBs, the model works like this: your fractional CISO sets priorities and approves security standards; your IT lead and MSP implement; your CEO (or a delegated exec) accepts risk when tradeoffs get hard. Without that structure, security turns into tool sprawl and half-finished projects.
A strong fractional CISO will also reduce noise. Instead of chasing every alert, you focus on operational basics that prevent common failures: identity and access, patching, backups with restore tests, and logging you can actually use.
If you want a clearer view of how this leadership model should run day to day, use a business-aligned CISO operating model as your benchmark.
How to evaluate, price, and contract a fractional CISO (questions you can use today)
Buying fractional CISO support is like hiring a pilot, not buying a map. The resume matters, but the operating style matters more. You need someone who can fly in bad weather, stay calm, and explain the route to non-pilots.
Start with shortlist criteria you can defend:
Has led security at a level similar to your risk, not just your industry.
Can communicate cybersecurity leadership with your exec team and board without jargon.
Has incident leadership experience, not only prevention.
Can work with your existing IT model (internal team, MSP, or hybrid).
Stays vendor-neutral and doesn't push tools as the answer.
Then run interviews that test judgment, not trivia. If you want a CEO-friendly approach to screening, use how to vet a CISO as a guide for what "good" sounds like from a cybersecurity expert.
Contracting matters too. Your statement of work should define outcomes like cyber risk management, deliverables, meeting rhythm, and how decisions get documented. If any of that is vague, expect drift.
Interview questions that reveal real leadership, not just technical depth
Use these questions to surface how they think and how they lead. For a longer bank, see CISO interview questions for CEOs and CHROs.
Business alignment
How do you rank risks when sales, product, and IT all disagree?
What do you ask the CEO in week one to set priorities?
Incident leadership
3. Tell me about a serious incident you led, what decisions mattered most?
4. What do you want in place before you'll say we're "ransomware-ready enough"?
Board communication
5. How do you brief a board in five minutes when the news is bad, including board of directors reporting?
6. What does a good monthly exec update include, and what does it avoid?
Budget and tradeoffs
7. If you had to cut security spend by 20%, what would you protect, including security policies and procedures?
8. What "basic controls" do you fund before buying anything new, such as vulnerability management?
Vendors and third parties
9. How do you handle vendor claims that their tool is "required"?
10. What does a right-sized third party risk management process look like for an SMB?
Culture and execution
11. How do you create follow-through without slowing teams down?
12. What do you expect from my IT lead each week?
Pricing and scope, what drives cost, and how to avoid surprise fees
Most fractional CISO engagements price in one of three ways: monthly retainer, hourly, or fixed-scope. The right model depends on how predictable your needs are, delivering cost effective security for SMBs.
Here's a simple comparison to set expectations:
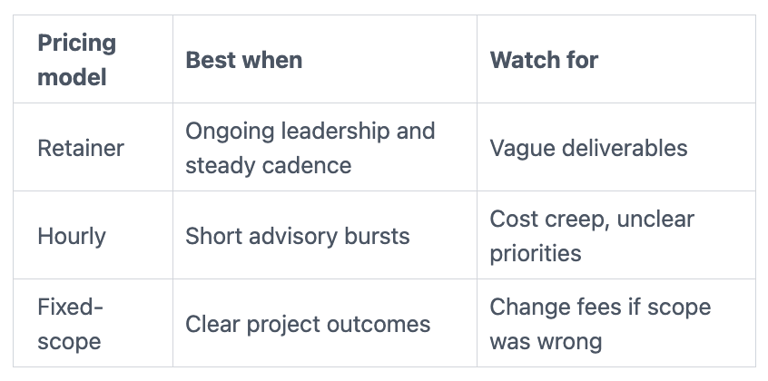
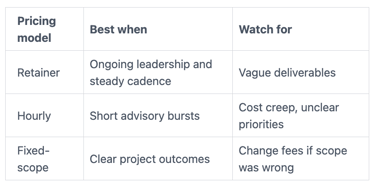
Cost usually changes with your size, risk profile, compliance load, vendor sprawl, incident recovery needs, M&A activity, and meeting cadence. Travel can also matter, but many SMBs stay remote-first.
Your SOW should include: outcomes, deliverables, meeting rhythm, decision rights, and "not included." That last part prevents resentment later.
Red flags to avoid:
Vague scope with no early deliverables
Tool kickbacks or hidden reseller incentives
No measurement plan
No executive updates or board-ready reporting
If you want a useful lens for avoiding tool-first spending, read measuring security value beyond tools.
How you know it is working: simple metrics, board updates, and FAQs
If fractional support is working, your cybersecurity program starts to feel less like a pile of tasks, and more like a steady drumbeat. You should see fewer surprises, faster decisions, and clearer ownership.
Set a simple reporting cadence: a short weekly working session with IT and ops owners, then a monthly executive update for Board of Directors Reporting that shows what changed, what's blocked, and what decisions you need. Quarterly, you can do one deep dive on a major risk area.
Before-and-after examples you should expect:
MFA coverage goes from partial to near-complete for high-risk access.
Restore tests become routine, not a once-a-year scramble.
Vendor reviews move from informal to triaged and documented.
Customer questionnaires get answered faster because evidence exists.
Metrics help when they show trends and drive decisions. For a strong perspective on why this works, see the hidden value of cyber metrics.
A lightweight scorecard you can review monthly
Track a few indicators that your team can update without pain to support your GRC program, including internal security audits. Trends matter more than perfection. If you want board-friendly framing, use CISO performance metrics for board oversight.
Critical patch SLA performance for key systems
MFA coverage for email, remote access, and admin accounts
Backup restore tests completed (and time to restore)
Endpoint protection coverage on all company devices
Phishing reporting rate (not just training completion)
High-risk vendor reviews completed and refreshed
Incident response exercise completed (and lessons closed)
Time to close top risks identified in your risk assessment on the priority list
Number of privileged accounts (should usually trend down)
Log coverage for critical systems (enough to investigate)
Aim for steady improvement in your information security program you can explain, not perfect scores you can't defend.
FAQs: quick answers SMB buyers need
How many hours per week do you usually need?
It depends on urgency. Many SMBs start higher for 30 to 60 days, then taper.
Can a fractional CISO work with our MSP?
Yes, if roles are clear. A virtual CISO sets direction, the MSP implements and operates.
Will this help with customer security questionnaires?
It should. You're building evidence like SOC 2 and ISO 27001 artifacts and repeatable answers, not reinventing each time.
Do you need NIST or ISO to start?
No. A good fractional CISO uses the NIST Cybersecurity Framework or HIPAA compliance lightly as a structure, then keeps it practical.
What if you've had a recent incident?
You may need interim-style intensity from cybersecurity leadership first. Then a virtual CISO or part time CISO can maintain progress.
How soon should you expect results?
You should see clarity and early risk reduction within the first 30 days, making your cybersecurity program more effective.
How do you avoid getting buried in policies?
You focus on minimum security policies and procedures and proof they work, then expand only as needed.
Conclusion
You don't hire Fractional CISO Services to "do security." You hire them to create ownership, make smart tradeoffs in your Security Strategy, and build a Cybersecurity Program your team can actually run.
Your buyer's plan is simple: confirm you need Executive Level Guidance (not just more tools), define outcomes in business terms, demand tangible deliverables like a Strategic Security Roadmap in the first 30 to 90 days, and measure progress with a lightweight scorecard for your Cybersecurity Program. Keep the tone calm and practical, because panic creates waste.
If you're ready to explore fit, start with engaging a CISO advisor, a Part Time CISO option, and focus the first conversation on your goals, constraints, top risks, and Cyber Risk Management. The right Cybersecurity Expert partner won't just inform you, they'll help you decide what matters, and get it done with less drama and fewer surprises, providing the Cybersecurity Leadership you need.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
