How an Interim CISO Helps Reduce Cybersecurity Risk (Without Slowing the Business)
An Interim CISO steps in fast, clarifies top risks, tightens access and backups, and gives you board-ready reporting without slowing growth.


You usually notice the problem in a moment, not a meeting. A customer asks for proof you can't quickly produce. An audit turns into a scramble. A key security leader resigns. A near miss shakes your confidence. Or growth, turnover, and new vendors pile up until risk starts outpacing your team.
An Interim CISO is a short-term security executive who steps in to stabilize risk, set clear priorities, and drive measurable progress while you hire, recover, or scale.
The promise is simple: you get calmer decisions, fewer unknowns, and faster risk reduction than you'll get from tools, tickets, or good intentions alone. Instead of chasing every vulnerability and every framework at once, you focus on what can actually hurt the business, then you fix it in a way your leaders can inspect. Think of it like bringing in an experienced pilot during bad weather: not to fly forever, but to land the plane safely and hand the controls back in better shape.
Key takeaways you can act on this week
You should leave week 1 with clear decision rights for security and incidents.
You should leave week 2 with a top 10 risk list tied to business outcomes.
You should know which "crown jewels" matter most, and who owns them.
You should see 2 to 3 fast control improvements in identity, access, or backups.
You should be able to explain incident readiness in plain language to leaders.
You should have a 30 to 90-day plan with owners, dates, and tradeoffs.
What an Interim CISO does in the first 30 days to lower real risk
When you bring in an Interim CISO, the first month is about stabilization and clarity, not big rewrites. You reduce risk fastest when you stop guessing, name owners, and tighten a few high-impact controls.
A good Interim CISO also sets expectations early: some risks won't be eliminated in 30 days. Still, you can sharply reduce the odds of a preventable incident, and you can lower the blast radius if one happens.
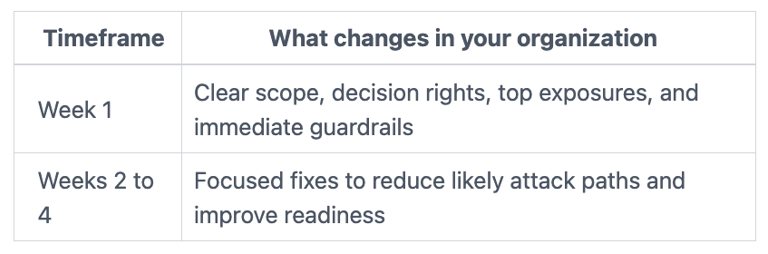
Here's what the pace often looks like:
If you want a practical view of how executive security leadership stabilizes risk fast, start with interim CISO for rapid risk stabilization. If you're evaluating candidates, it also helps to know the best practices for interim CISO selection so you can spot stabilizers early.
Start with a business-first risk snapshot you can defend
You don't need a months-long assessment to get to truth. Instead, you need a risk snapshot that holds up when the CFO, GC, and board ask, "How do you know?"
An Interim CISO typically starts by identifying your crown jewels (systems, data, revenue paths, safety-critical operations, and trust drivers). Next, you map the most likely threat paths to those assets. Then you look for control gaps that make the path easy, such as weak admin access, exposed remote access, or missing logs.
To move fast without false confidence, you'll usually see:
Short interviews with IT, product, operations, and finance leaders (what can't go down, what can't leak).
A lightweight evidence review (configs, access lists, backup status, incident artifacts), not a binder hunt.
A quick scan of top third-party risks (who has access, what's connected, what's inherited).
The output should be plain: what's most exposed, why it matters, and how confident you are in the assessment. That "confidence level" matters because it prevents optimism from pretending to be assurance.
Stabilize the basics: decision rights, priorities, and a short list of fixes
Risk stays high when nobody can answer three questions: who decides, who funds, and who runs. An Interim CISO fixes that first, because decision rights are a control.
From there, you should expect a short list of changes that reduce real risk quickly, often including:
Freezing risky change where it counts. You don't halt the business, but you put guardrails around critical systems so you don't "patch into an outage" or deploy into unknown exposure.
Patch and vulnerability triage. Instead of "patch everything," you prioritize internet-facing systems, identity services, and high-value servers. You also remove the noise so your team can finish.
Identity and access quick wins. You tighten privileged access, reduce stale accounts, expand MFA where it matters, and clean up admin sprawl. Attackers love messy access because it's quiet and effective.
Backup reality checks. Backups that haven't been tested are hope, not recovery. You confirm they're protected from tampering, and you prove a restore works.
Vendor access tightening. Third parties often keep standing access far longer than you think. You reduce that exposure and require better controls for the next onboarding.
By the end of 30 days, the best sign of progress is simple: fewer urgent surprises, faster answers, and a risk list that doesn't change every time someone new walks into the room.
How an Interim CISO strengthens governance so leaders can see and manage cyber risk
You can't manage what you can't see, and most leadership teams don't need more cybersecurity detail. You need clean decisions, clear accountability, and reporting that reduces surprises.
An Interim CISO strengthens governance by turning security into a repeatable leadership routine. That means risk is discussed the same way you discuss finance or operations: with definitions, owners, and follow-through.
If you want a board-level structure you can adopt quickly, use a cybersecurity governance framework for boards. To make oversight measurable, align reporting to board oversight CISO performance metrics so progress is visible and inspectable.
Turn cyber into a simple set of decisions, not a technical debate
Technical debates waste executive time because they skip the real question: what risk are you taking, and why?
An Interim CISO helps you define:
Your risk appetite (what you won't tolerate, what you can accept).
How risk acceptance works (who can sign, for how long, with what conditions).
What "good enough" looks like for your size, industry, and customer promises.
This gets practical fast. For example, if you're launching a new product, you decide what security checks must happen before release, and which can happen after launch with guardrails. If you're moving to the cloud, you define who owns identity, logging, and encryption decisions across teams. If you're opening a new region, you confirm data handling and access controls before you scale exposure.
In other words, governance becomes a decision system, not a slide deck.
Build reporting that helps the board ask better questions
Board reporting often fails in two ways: it's either too technical, or it's a comfort blanket of green charts.
An Interim CISO shifts reporting toward outcome signals, such as exposure trends, control coverage on crown jewels, time-to-fix for top risks, and incident readiness status. You still track technical metrics, but you translate them into business impact.
After that change, leaders should be able to answer questions like:
What are our top 5 risk scenarios, and how prepared are we?
Which critical assets have the weakest control coverage today?
What did we improve since last month, and what's stuck?
If ransomware hit tomorrow, what would we do in the first hour?
If your reporting doesn't lead to a decision, it's not reporting, it's noise.
Where an Interim CISO reduces risk that tools alone cannot
Buying another tool can feel productive, especially under pressure. However, tools don't set priorities. Tools don't resolve tradeoffs. Tools don't create calm leadership in a crisis.
An Interim CISO reduces risk through execution, standards, and people. You move from "we're compliant" to "we're confident," because you can explain what you've done, what's still exposed, and what you'll do next. The mindset shift is captured well in from compliance to confidence.
When things go wrong, leadership needs more than containment steps. You need shared facts and a steady cadence. That's why it helps to adopt cyber crisis command center metrics that keep decisions grounded.
Get incident-ready so a bad day does not become a business crisis
Even strong prevention fails sometimes. Readiness is how you control impact.
An Interim CISO typically makes incident readiness real by running a tabletop exercise, naming roles, and validating communications paths with legal and PR. You also define ransomware decision points early (shut down systems, negotiate, notify, restore), because you don't want to invent those rules mid-crisis.
Just as important, you prove the basics work under stress: backups restore, access can be cut quickly, and evidence can be preserved. The payoff is huge. When an incident hits, you spend less time arguing and more time acting.
Set standards and a roadmap your team can actually deliver
Frameworks like NIST or ISO help, but only if they reduce confusion. An Interim CISO uses them in plain terms: what outcomes you want, what controls support those outcomes, and what "done" means.
Then you build a 90-day plan that matches real capacity and budget. You avoid the trap of an over-ambitious roadmap that your team can't execute. As a result, effort concentrates on the few moves that change risk, not on the many tasks that only create activity.
How to tell if you need an Interim CISO, and how to choose the right one
Sometimes the clearest signal is how you feel. Decisions drag. Updates confuse. Everyone assumes someone else owns the risk.
Common triggers are straightforward:
Your CISO left, or you never had one, and the work outgrew ad hoc coverage.
Audit findings repeat, and evidence collection turns chaotic.
Cyber insurance and customer reviews demand faster, clearer answers.
You had a breach or near miss, and you don't want to rely on luck again.
M&A, integration, or rapid growth expanded your attack surface overnight.
Vendors now run critical parts of your environment, and oversight is thin.
Waiting adds hidden cost, because exceptions pile up and "temporary" becomes normal.
To hire well, use a CEO-friendly approach like this CEO guide to vetting a CISO. During interviews, bring a tight script, such as these CISO interview questions for CEOs, so you can test judgment, not jargon.
Clear signs you need short-term executive security leadership
If your top risks aren't written down, ranked, and owned, you're likely flying blind. If incident roles aren't clear, you're one surprise away from confusion. If teams debate priorities every week, nobody can finish the basics.
You don't need perfection to move forward. You do need a leader who can choose, commit, and deliver.
Questions that reveal whether an Interim CISO will reduce risk fast
Ask questions that force specifics, then listen for plain answers.
"Show me how you pick the first five priorities here." Good answers tie to crown jewels and likely threat paths.
"How will you report risk to my board?" Good answers describe decisions, trends, and what you need from leadership.
"What do you do in a ransomware scenario?" Good answers cover roles, comms, restore proof, and business decisions.
"How do you leave the team stronger when you exit?" Good answers include a handoff plan, routines, and named owners.
FAQs about hiring an Interim CISO to reduce cybersecurity risk
How fast can you start seeing risk reduction? You can see meaningful change in the first two weeks, especially in access, backups, and decision clarity. Bigger program shifts usually take 30 to 90 days.
Is an Interim CISO the same as a fractional CISO? Not always. Interim usually means high-intensity leadership for a short window. Fractional tends to be ongoing part-time coverage, which is explained clearly on fractional CISO services.
Will an Interim CISO replace your IT team's authority? A good interim leader won't. Instead, you'll get clearer ownership, fewer conflicts, and faster decisions across IT, legal, and the business.
Do you need to buy new security tools right away? Usually no. The first wins often come from tightening identity, reducing admin sprawl, validating backups, and improving response routines.
How do you measure success in 30 days? You should have a defensible top risk list, visible control improvements, and board-ready reporting. You should also have an incident readiness plan you've practiced, not just documented.
How long should an interim engagement last? Many run 3 to 9 months. The right length depends on whether you're stabilizing after an incident, bridging a hiring gap, or integrating change like M&A.
Conclusion
When risk is outpacing your team, speed matters, but so does judgment. An Interim CISO helps you reduce cybersecurity risk faster by bringing focus, governance, and execution you can inspect. You get clear priorities, tighter control of the basics, and better readiness for the incidents you can't fully prevent.
Your next step in the next 7 days is practical: request a one-page risk snapshot, confirm who decides in an incident, and validate whether backups actually restore. If you want help setting that plan in motion, start by engaging a CISO advisor and align on the outcomes you need most in the next 30 to 90 days.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
