How Interim CISO Services Reduce Risk in 30 Days
Interim CISO Services cut cyber risk in 30 days, you stabilize access, email, and backups, set decision rights, and prove control gains.


If cyber risk feels like a dark cloud over your business, you're not imagining it. Risk is not just cyber threats such as hackers. It's downtime that stops operations, lost revenue from stalled deals, fines that hit cash flow, and trust damage that lingers long after systems recover. This underscores the need for a Chief Information Security Officer to lead cyber risk management.
Interim CISO Services give you information security leadership fast, usually for a set period, with one job: bring order to uncertainty and reduce avoidable exposure. You're not waiting months for a full-time hire. You're getting executive judgment now, plus a focused plan your team can actually follow.
In the next 30 days, you should expect three things to change: what you measure, what you decide, and what you can prove. This is a simple, board and CEO-friendly view of what happens week by week, without the usual noise.
Key takeaways you can use right away
Week 1: You stabilize the basics (admin access, email, backups) to shrink the blast radius.
By day 7: You complete a risk assessment to get a top-10 risk list tied to business impact, with named owners and first fixes.
By day 15: You lock decision rights (who can accept risk, approve emergency changes, and escalate).
By day 20: You have a simple risk register and a 30 to 90-day roadmap with priorities and dates.
By day 30: You can show evidence that your security posture improved through key controls (not just that work happened).
By day 30: Your incident response is practiced enough that leaders know who does what first.
Expectation check: Interim CISO Services can reduce real risk fast with a transition plan that includes a 30 to 90-day roadmap, but they won't rebuild every system, replace a weak culture overnight, or fix years of tech debt in 30 days.
What an interim CISO does in the first week to stop the bleeding
Week 1 is about stabilization and clarity. Think of it like patching the roof before you remodel the house. You're not trying to make everything perfect. You're trying to prevent a small problem from turning into a headline.
An interim CISO will start by confirming what matters most to your business. That might be customer-facing uptime, data protection for regulated data and payment systems, or a key product platform. Then they focus on vulnerability management for the most common paths attackers use because those paths tend to be the same ones that create ugly operational failures.
You'll usually see immediate attention on ransomware readiness, privileged access, backups, and third-party risk management. Not because those are trendy, but because they determine whether you can contain an incident or watch it spread.
Just as important, you get a clear cadence. Short daily touchpoints early on, then a steady weekly rhythm. That rhythm reduces "security whiplash," where everyone reacts to the latest alert instead of fixing what actually drives risk.
Run a rapid risk snapshot that leaders can actually understand
You don't need a long assessment to get traction. You need a fast snapshot that turns scattered facts into decisions.
A solid rapid snapshot often includes short interviews with leaders across IT, engineering, finance, legal, and operations. In parallel, the interim CISO conducts a gap analysis by pulling practical data: an asset list (even if imperfect), identity and admin account reports, endpoint coverage, email settings, and cloud security account structure. Recent incidents, audit findings, and open exceptions also matter because they show where the organization already knows it's exposed.
The key output is a simple risk map tied to business impact. You should expect a "top 10" list that reads like this:
what could happen (in plain language)
how likely it is (using a simple scale)
what the impact looks like (downtime, revenue, legal exposure, customer trust)
who owns the risk (a named leader)
the first fixes that reduce exposure quickly
If you can't name your top risks and owners in one page, you're managing activity, not risk.
This snapshot also prevents a common mistake: chasing the loudest problem. Your interim CISO should help you avoid spending week 2 fixing something that feels urgent but barely moves real exposure.
Put immediate guardrails around access, email, and backups
Most fast risk reduction comes from tightening a few control points. These are the places where one mistake can open the door wide.
First, privileged access gets cleaned up. Admin accounts get reduced, shared accounts get addressed, stale accounts get removed, and emergency access gets controlled and logged. Next, multi-factor authentication coverage gets confirmed where it matters most (email, remote access, cloud consoles, and admin tools). Then email defenses are hardened because email still drives many real-world breaches, including fraud and ransomware entry.
Backups are the other early focus. It's not enough to know backups exist. You need confidence you can restore. In week 1, you verify backup scope, isolation (so attackers can't wipe them), and whether restore testing is real or just assumed. Even one proven restore test can change the risk conversation overnight.
Finally, the interim CISO confirms incident contacts and escalation paths. If something happens tonight, your leaders should know who gets called, who can make the hard calls, and how quickly you can assemble the response team.
Days 8 to 20, you shift from guesses to a clear plan and stronger oversight
After week 1, the goal changes. You move from "stop the bleeding" to "run this like a cybersecurity program." That's where Interim CISO Services reduce risk in a way that lasts, even after the engagement ends.
During days 8 to 20, your interim CISO turns scattered work into a focused set of priorities. The best sign you're on track is that meetings get shorter but decisions get clearer. People stop arguing about tools and start aligning on outcomes.
You'll also see your security strategy tied back to business goals. If sales needs faster customer assurance answers, that becomes part of the plan. If regulatory compliance deadlines are looming, evidence collection gets organized. If customer trust is central to growth, you prioritize controls that reduce the chance of a public failure.
This period is also where security governance becomes practical. You set a decision cadence, define who owns what, and stop letting risk sit in the gaps between teams.
Create a simple risk register and a 30 to 90-day roadmap your team can execute
A risk register doesn't need to be fancy. It needs to be used. The interim CISO should create a short, living list of risks that includes owners, due dates, and status that changes based on proof.
Next comes the 30 to 90-day roadmap. This is where you prevent the "tool buying" trap. When fear rises, vendors get louder. A roadmap keeps you grounded. It forces sequencing and makes tradeoffs visible: what you do now, what you delay, and what risk you accept temporarily.
A good roadmap covers people, process, and tech. It names who will do the work, not just what the work is. It also uses frameworks like the NIST framework or ISO as organizing tools, not as paperwork exercises like drafting an information security policy. In other words, standards help you avoid blind spots, but you don't turn your first month into a compliance theater project.
Make Board Reporting that Shows Progress Without Noise
By this point, you should be able to brief leadership without a 40-slide deck. Strong reporting answers a few questions: what are the top risks, what changed, what decision is needed, and what proof supports the update.
You also want stable metrics, not a rotating set of numbers that hides the trend. The goal is confidence, not perfection. If you're building reporting that directors can actually use, this guide to board oversight and CISO performance metrics is a helpful reference for keeping the conversation decision-based.
Board reporting should stay tied to business impact. A control gap matters because it can stop revenue, create legal exposure, or break customer trust. When reporting keeps that link clear, you'll see faster approvals and fewer circular debates.
By day 30, you can prove risk went down and you know what comes next
Day 30 should not feel like "we learned a lot." It should feel like "we're safer, and we can show it."
Proof matters because security is often judged by belief. If you can't show evidence, confidence fades. By day 30, you should have documented decisions, tested readiness, and measurable improvements in a few high-impact areas. You also want a plan that survives leadership changes and advances security maturity. That's the real test of whether the work was structural or just personality-driven.
This is also the moment to choose the right leadership model going forward. Interim leadership is a sprint. The next step might be another sprint, a steady cadence, or a full-time build.
Deliver the day 30 package: controls improved, response ready, priorities locked
Your day 30 package should be practical. It should make your next 60 to 90 days easier, not harder.
Here are typical deliverables you can expect:
An updated incident response plan with named roles, escalation rules, and current contact lists
A tabletop exercise summary (or a ransomware readiness check) with lessons learned and next actions
Backup restore evidence for at least one critical system that strengthens business resilience, plus a plan to expand testing
An access cleanup report (admin accounts, stale accounts, MFA coverage) with before and after counts
A risk register ranked by business impact, with owners and target dates
A 30 to 90-day roadmap with sequencing, dependencies, and decision points
For directors and executives who want clarity on what "good oversight" looks like during readiness work, use this resource on board incident response oversight.
Decide the right next step: interim, fractional, or full-time CISO leadership
After 30 days, you have enough signal to choose the next leadership shape. The right choice depends on urgency, complexity, and how strong your internal team is.
This quick table helps you decide:
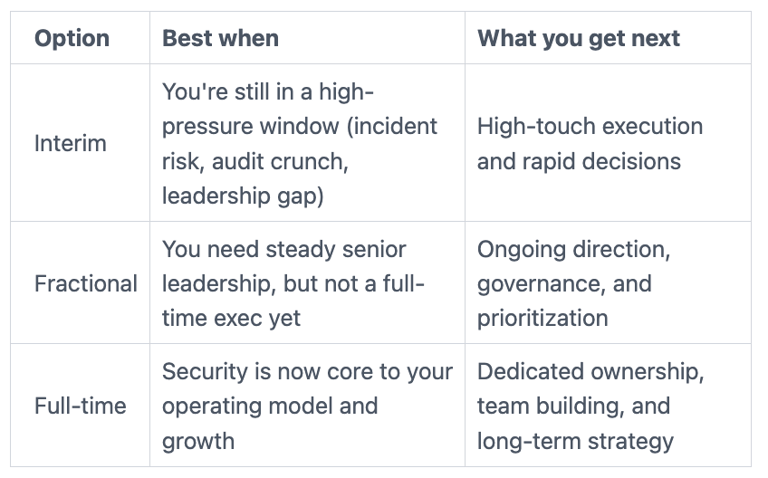
If you're continuing an intense stabilization period, consider an interim security executive model so you don't lose momentum mid-stream. If you're ready to shift to ongoing leadership and discipline, Fractional CISO can keep progress moving without forcing a rushed permanent hire.
FAQs leaders ask before they hire Interim CISO Services
How much do Interim CISO Services cost, and what drives the price?
Cost of Virtual CISO or Interim CISO Services depends on urgency, scope, and complexity. A multi-site environment, heavy regulatory needs such as HIPAA compliance, or active incident risk will require more time and deeper involvement. Clear priorities can lower cost because you avoid churn.
How fast can you start?
Virtual CISO engagements often start within days to a couple of weeks. Speed depends on availability and conflicts, but also on how quickly you can grant access to systems, key staff, and current documentation.
What do you need from your internal team in the first 30 days?
You need a small set of committed partners: IT, engineering, and someone who can speak for the business. You also need timely access to identity reports, endpoint and email controls, cloud accounts, and backup systems. Without access, you'll get opinions instead of proof.
How do you work with IT, legal, and HR without slowing everything down?
You set decision rights early and keep meetings short. IT and engineering drive security operations and technical changes, legal shapes incident and disclosure posture, and HR supports access changes and security awareness training needs. The interim CISO keeps everyone aligned on what reduces risk first.
What happens if there's an incident during the engagement?
You respond with a clear incident command structure, rapid containment, and executive communications. Just as important, you document decisions as they happen, so you can explain actions to customers, regulators, and the board later.
Can you help with compliance without turning this into a paperwork project?
Yes, if you focus on evidence and control outcomes. You map urgent regulatory compliance needs and Governance Risk and Compliance requirements to real controls (access, logging, backups, vendor oversight), then build a plan for the remaining gaps.
What does success look like in 30 days?
You can explain your top risks in plain language, name owners, show measured improvements in key controls, and demonstrate practiced incident readiness. You also have a roadmap that's realistic.
How should you vet a CISO-level leader before you commit?
You're looking for judgment, not just credentials. Ask how they've handled real incidents, how they brief boards, and what they deliver by day 30. This guide on how CEOs should vet a CISO can help you screen for practical leadership instead of polished talk.
Conclusion
In 30 days, Interim CISO Services should help you stabilize, then prioritize, then prove progress. Speed comes from focus and senior decision-making, not from buying more tools. When you tighten access, validate backups, practice response, and publish a clear roadmap, you reduce the odds of a business-stopping event.
If you want to explore what an engagement could look like in your situation, start with reaching out to engage a Virtual CISO or Chief Information Security Officer advisor and align on the security strategy outcomes you need by day 30.


