How to Report Third-Party Risk to the Board (Without Drowning Them in Vendor Scores)
Get third-party risk reporting to the board right, show business impact, what changed, and the decisions you need, without drowning directors in scores.


In third-party risk management, you depend on third parties for cloud hosting, payroll, IT support, data tools, and customer-facing services. That's normal now. What's not normal is trying to explain that exposure to directors with a spreadsheet full of vendor scores that don't tell them what to do.
The board of directors wants a clear picture of business impact, what's changing, and what decisions need their input. They're thinking about revenue, operations, trust, and legal risk, not the fine print of security controls.
This guide gives you a simple structure for third-party risk reporting to the board within the broader cybersecurity landscape so you can speak plainly, stay consistent month to month, and strengthen oversight without turning meetings into technical debates.
Key takeaways you can use in your next board meeting
Frame vendor risk as business interruption, loss, or trust damage in vendor risk management, not control gaps.
Keep reporting tight by focusing on tier 1 vendors for critical activities and critical dependencies.
Show what changed since last time, and why it matters now.
Track a few metrics that show exposure and trend, not activity.
Make concentration risk obvious, especially where there's no quick substitute.
Separate "monitor" items from "approve" items so directors know when to act.
Bring decision requests with options and a date, not a status update.
These tips strengthen your TPRM efforts.
Start with the board's questions, then map vendor risk to business outcomes
Directors are already responsible for enterprise risk. Your job is to connect vendor issues to the outcomes they govern. Think of it like translating a weather report into travel decisions. "Storm probability" matters less than "your flight is likely canceled."
Start by anchoring third-party risk in a small set of board-level outcomes:
Service downtime: Your vendor goes down, your customers can't transact.
Data exposure: A data breach exposes customer data, employee data, or IP.
Fraud and financial loss: A vendor workflow enables payment diversion or account takeover.
Regulatory fines and legal exposure: A vendor failure triggers reporting, penalties, or lawsuits.
Contractual penalties: Missed SLAs, customer credits, termination rights, or loss of renewals.
Brand trust: Customers blame you, even when the vendor caused the issue.
Then map each vendor risk to the enterprise risk category the board already uses (financial, operational, legal and compliance, strategic, reputational). That mapping also helps you route oversight to the right committee:
A simple "board lens" looks like this:
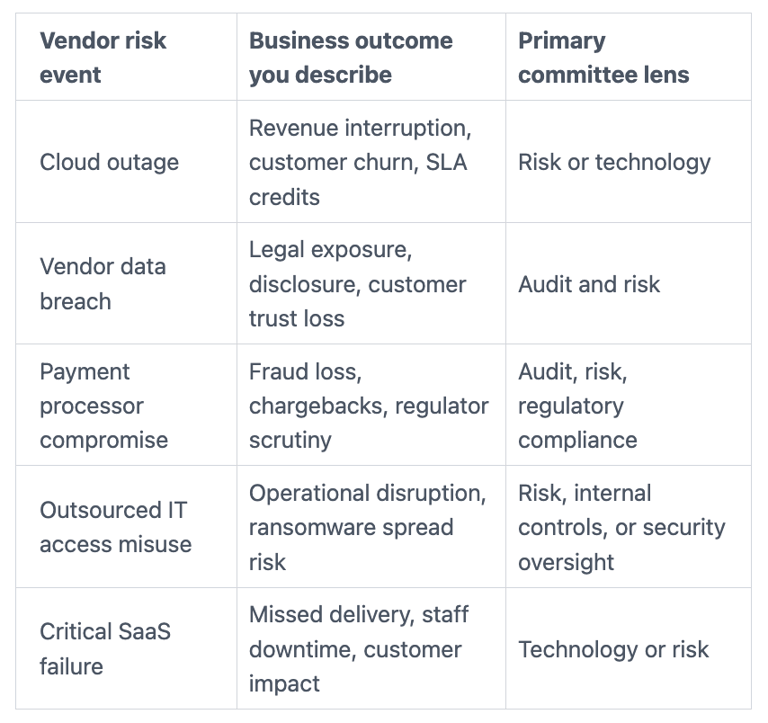
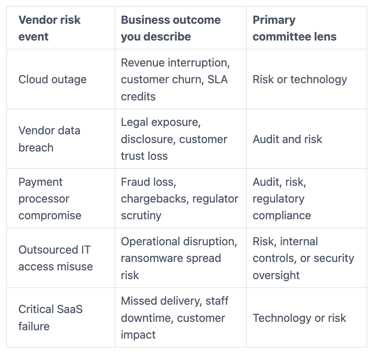
If your team struggles to brief this way, use a model for calm, board-ready phrasing, such as the guidance on leading cybersecurity conversations that inspire confidence. The tone matters as much as the facts.
Use a plain-language risk story: what could happen, how likely, how bad, what you are doing
You can use the same four-part risk assessment structure for any critical vendor. It keeps you out of jargon and forces a business "so what."
Use this repeatable sentence pattern:
What could happen (from our risk assessment): "If Vendor X is disrupted or breached…"
How likely: "We think likelihood is low, medium, or high because…"
How bad: "The impact would be… (revenue, operations, legal, trust)."
What you're doing: "We're reducing exposure by… (actions, dates, owners)."
Then add a one-line business hook: "So what: order taking stops, patient care slows, payroll fails, or product delivery slips."
Keep the supporting detail board-safe. Skip CVE counts. Skip SOC report deep dives. If directors want more, offer an appendix or a follow-up with the committee chair.
Name the few third parties that matter most, and explain why
Boards don't need perfection across hundreds of vendors. They need focus on the few that can move enterprise risk.
Define "tier 1" vendors using simple criteria you can defend in one minute:
They can access sensitive data (customer, employee, regulated, or proprietary).
They have production access (admin access, code paths, or privileged integrations).
You depend on them for critical uptime (core operations or revenue path).
They have transaction authority (payments, refunds, account changes, identity).
They can impact many systems (single sign-on provider, major cloud, key MSP).
Once you define tier 1, stick with it. The list should change slowly. When it changes, call it out and explain why.
Build a board-ready dashboard that shows exposure, trends, and decisions
A board dashboard should feel like an instrument panel for TPRM, not a lab report. If a director can't read it in two minutes, it's too busy.
Aim for a single page with five blocks. You're not describing how to build it, you're deciding what the board must see.
Portfolio view: How many tier 1 vendors you have, and overall security posture (direction, not noise) from TPRM ongoing monitoring.
Top third-party risks: The 3 to 5 risks with the highest business impact.
Trend arrows: What improved, what drifted, what stayed stuck via ongoing monitoring.
Exceptions and gaps: Time-bound exceptions, overdue items, evidence gaps.
Decisions needed: What you need the board to approve, accept, or prioritize.
Before you show any metric, make one promise: you'll use the same definitions next time. Directors lose trust when numbers shift because the measurement changed. If you need to change a definition, say so and show the impact.
If you want a strong mental model for picking metrics that hold up under pressure, the thinking behind the hidden value of cyber metrics applies well to third-party reporting. The point is signal, not comfort.
To make the dashboard concrete, you can structure it like this:
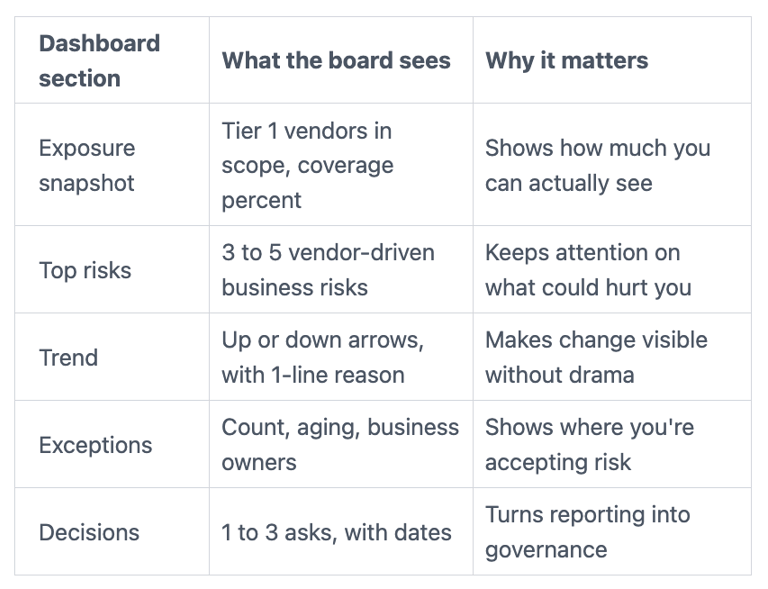
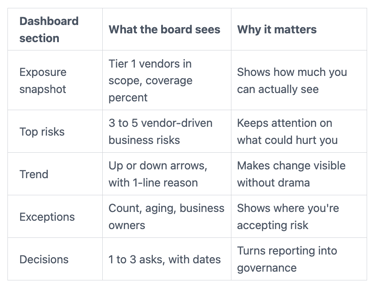
The takeaway: consistency beats complexity. A steady one-page view builds confidence over time.
Track a small set of metrics that signal real third-party risk
Pick metrics that answer, "Are we more exposed, less exposed, or the same?" Keep them limited, and show trends.
Percent of tier 1 vendors with a current security review: Shows basic coverage, not quality.
High-risk exceptions (count and age): Highlights where you knowingly accept exposure.
Time to close critical vendor findings: Shows whether remediation actually happens.
Incident notification SLA compliance: Did the vendor notify you within the contract window?
Vendor security ratings average score: Modern data point boards often inquire about.
Fourth-party visibility coverage: For tier 1 vendors, do you know their key sub-processors?
Concentration risk index: How many critical processes depend on a single vendor?
Access review completion for vendor accounts: Confirms privileged access stays controlled.
Joint exercise participation: Did key vendors join tabletop or recovery exercises?
Avoid vanity metrics like "questionnaires completed" or "vendors contacted." Activity can rise while risk stays flat. Focus on the few third-party relationships that matter most.
Show concentration risk and single points of failure in plain English
Concentration risk is usually the board's fastest path to "I get it." It's also where supply chain security, budget, and strategy decisions show up.
Use plain statements like:
"If Vendor X is down, these three business functions stop: online checkout, customer support ticketing, and invoicing."
Then add what directors really want to know:
Do you have a workaround (manual process, alternate provider, failover)?
How long until pain (hours, days, weeks)?
How hard is exit (contract limits, migration time, data portability)?
A simple heat map works, but don't over-design it. Even a short dependency list can be enough, as long as it's honest about where you have no viable substitute.
If you can't explain a vendor dependency without acronyms, you don't understand the dependency well enough yet.
Use a clear cadence for executive-level reporting, and ask the board for specific decisions
A predictable rhythm reduces panic and prevents surprise escalations. It also makes it easier to hold management accountable.
Use three layers for oversight and accountability:
Monthly highlights (10 minutes): what changed, top risks, exceptions, decisions.
Quarterly deep dive (30 to 45 minutes): rotate focus (cloud concentration, MSP access, payments, customer data vendors).
Incident-triggered updates: when an event crosses your escalation thresholds.
Separate items into two buckets so meetings stay clean:
Monitor: risks you're managing within approved risk appetite and budget.
Approve: decisions that change risk posture, spend, or strategy.
This aligns well with board oversight expectations and performance accountability. If you want a strong model for how boards evaluate leadership outcomes over time, the framing in board oversight and CISO performance metrics helps you keep reporting decision-shaped.
Bring decision requests, not just risk updates
Third-party risk reports fail when they end with, "We're working on it."
Instead, bring options directors can act on to drive strategic decision-making. For example, you might ask for: funding for vendor risk capacity, approval to exit a vendor, acceptance of a time-bound exception, or permission for contract negotiation (audit rights, breach notice windows, sub-processor limits). In some cases, the decision is resilience work, such as backups, alternate providers, or a faster migration plan.
Use a tight template:
"We recommend X because Y. If we don't, the risk is Z. Decision needed by date."
That one pattern keeps you out of debate and drives a clear vote or direction.
Be ready for the hard questions directors will ask
The board of directors will test whether the story holds. You'll earn trust by answering calmly, with facts, owners, and dates.
Here are common questions, plus what a good answer sounds like:
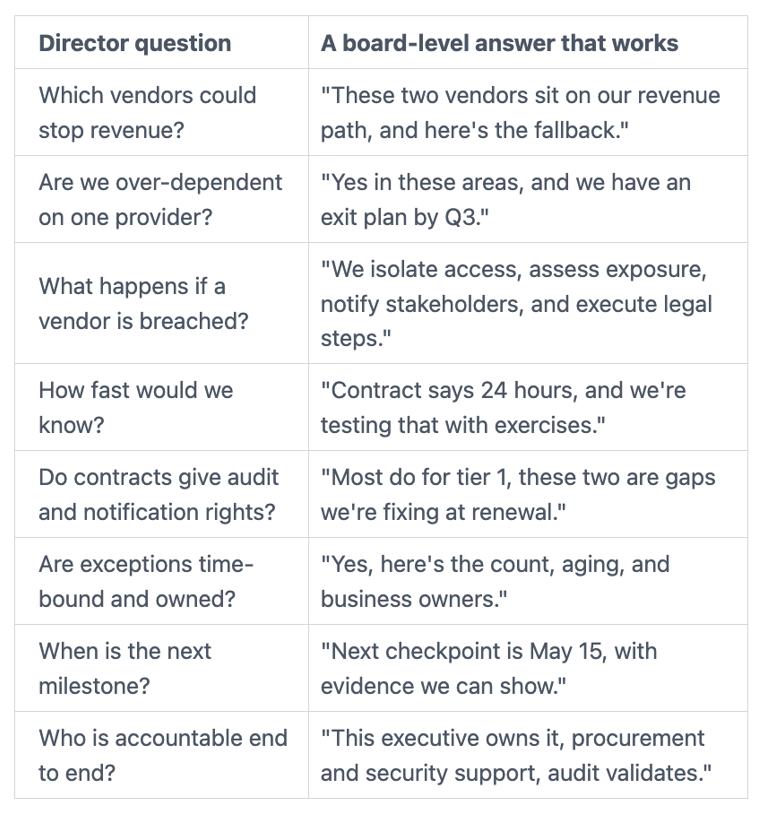
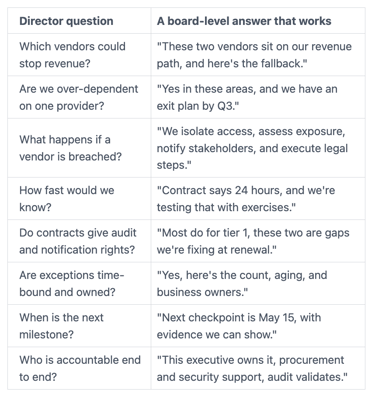
If you want a strong set of committee-ready prompts, point directors to audit committee cyber risk questions It helps keep the conversation sharp without becoming technical.
Handle incidents and bad news without losing trust
Vendor incidents, a critical operational risk, are where reporting discipline either pays off or collapses. When a third party has an outage, breach, or suspected compromise, directors don't expect certainty in the first hour. They do expect speed, clarity, and a plan.
Set expectations before anything happens. Define escalation thresholds, who contacts the board chair, and when the board gets an update. Then, when an incident hits, stick to the same format every time.
Board trust grows when you show three things fast: what you know, what you're doing, and when you'll know more. That's also the core of effective board incident response oversight.
Use a simple incident update format: facts, impact, actions, next update time
In the first 24 to 72 hours, keep updates short and timed. Avoid speculation, but don't hide uncertainty.
Use this checklist:
Facts: what happened, when you learned it, and who confirmed it.
Unknowns: what you don't know yet, such as technical vulnerabilities, and how you're finding out.
Customer impact: service disruption, data exposure risk, communications status.
Operational impact: which internal teams and processes are affected, including business continuity.
Legal and regulatory steps: counsel engaged, notification analysis underway.
Actions: risk mitigation through access changes, containment steps, monitoring, workaround activation.
Next update time: a specific time and owner for the next board update.
That structure keeps you steady, even when the news isn't good, while reinforcing your overall cybersecurity program.
Conclusion
When you report third-party risk well, you stop chasing vendor scores and start guiding oversight. Lead with business outcomes, focus on tier 1 vendors, and use a consistent one-page dashboard that shows exposure, trends, and decisions. Then keep the cadence predictable so directors see the story evolve over time, not just in a crisis.
If you want your reporting to feel calmer and more decision-ready next quarter, standardize the dashboard and decision template first, then refine the metrics. Over time, that's how third-party risk reporting to the board fits into the risk management lifecycle and becomes a governance strength instead of a recurring scramble.
If you need help pressure-testing your board reporting format and escalation thresholds, consider guidance from a cybersecurity board advisor.
FAQs
How often should you report third-party risk to the board?
Use monthly highlights for changes and exceptions in third-party relationships as part of third-party risk management, and a quarterly deep dive for one major theme. Also provide incident-triggered updates when thresholds are met. This keeps directors informed without turning every meeting into a vendor review.
What do you do when a vendor refuses to share controls evidence during due diligence (SOC report, pen test summary, or policy proof)?
Treat it as a risk decision, not a paperwork problem. You can escalate contract terms, add compensating controls (reduced access, segmentation, monitoring), or plan an exit. If the vendor is tier 1 and still refuses, you should assume higher residual risk and brief it that way.
How do you explain concentration risk without scary language?
State the dependency in plain terms: "If Vendor X is down, these functions stop." Then add timing and options: workaround exists or not, migration time, and contract constraints. Calm clarity beats dramatic warnings.
Should the board see every vendor and every score?
No. Keep the board view focused on tier 1 vendors and enterprise outcomes. You can keep a fuller inventory and detailed assessments for management and committees.
What's the fastest way to improve board confidence in vendor risk reporting?
Make the report consistent, show trends, and bring decisions with dates. Confidence grows when board members can see what changed in information security, why it matters, and what you're doing about it.


