Top 10 Mistakes To Avoid When Hiring an Interim CISO
Hiring An Interim CISO under pressure? Avoid 10 common mistakes, set 90-day outcomes, decision rights, and a clean handoff for real risk drop fast.


You don't bring in an Interim CISO when things are calm. You hire an Interim CISO when risk management is critical, time is short, and confidence is low. Maybe you just had a breach, a ransomware scare, or an ugly audit finding. Maybe cyber insurance renewal is coming up, a merger is on the table, or your CISO just exited and left a leadership vacuum.
In those moments, Hiring an Interim CISO can feel like calling in a fire chief while smoke still hangs in the air. The good news is you can get control fast. The bad news is it's easy to hire the wrong way and end up with more activity, more spend, and the same anxiety.
This guide gives you the most common hiring mistakes to avoid, plus what to do instead, so you get real risk reduction in weeks, not excuses in quarters. If you need a fast path to stabilize cybersecurity leadership, start with an interim security executive engagement.
Key takeaways (use these right away):
Write a 90-day mission with measurable outcomes before you interview anyone.
Give the interim clear decision rights, budget boundaries, and a weekly briefing path.
Protect executive time, don't bury the interim under tickets and tool admin.
Prove readiness early with a tabletop exercise and validated backups.
Plan the handoff on day one, or you'll lose momentum when they leave.
Start by getting clear on what you are really hiring an interim CISO to do
An interim Chief Information Security Officer (CISO) is not a substitute teacher watching the class until "the permanent hire" shows up. You're bringing in a short-term executive with a specific mission, real authority, and outcomes you can inspect. When you treat the role like executive leadership, it moves quickly. When you treat it like extra hands, it turns into expensive busyness.
Speed comes from clarity. You want alignment on three things before you start: the business trigger, the top risks tied to that trigger, and the decisions you need made in the next 30 to 90 days. Your CEO and board of directors (or audit committee) should agree on business objectives and what "better" looks like. Otherwise, every conversation becomes a debate about tools, priorities, and who owns the call.
It also helps to name the few constraints that can't be ignored, like a major product launch, a seasonal revenue peak, or a fragile legacy system. A strong Interim CISO will work within reality, but only if you surface it early.
If you can't say what you need done in 90 days, you'll hire a personality. Not a result.
Mistake: Treating the role like a stopgap instead of a mission with outcomes
When you hire "to fill the gap" without a gap analysis, you usually get busywork. The interim joins meetings, reviews alerts, and debates vendors. Meanwhile, no one is sure what must change first. That's how you end up with tool churn, shifting priorities, and no traction.
Do this instead: write a 90-day mission with 3 to 5 outcomes. For example, stabilize incident response, reduce your top risks, set board reporting, create a security roadmap, and triage vendor spend. Measure completion by whether each outcome has an owner, a due date, and evidence it's working (not just a slide).
Mistake: Not matching the interim CISO to your situation
A great Interim CISO in a regulated bank can struggle in a product-led SaaS company. A leader built for global operations may feel heavy in a small, fast team. Fit matters because you're buying judgment under pressure, not generic security knowledge.
Do this instead: screen for situational match. Ask yourself: Are you regulated or not? Are you cloud-native or IT-led? Is your risk mostly availability, privacy, or fraud? Do you need breach recovery, program reset, M&A integration, or board confidence? Then pick someone with proof in similar conditions, not just a strong resume. A good reference point is an experienced CISO for hire profile that shows board-level work and real outcomes.
The 10 hiring mistakes that create confusion, wasted spend, and weak risk control
Most interim CISO failures don't come from lack of effort. They come from fuzzy expectations, weak authority, and too many stakeholders pulling in different directions. Fix those, and you'll feel the temperature drop quickly.
Below are the 10 mistakes that cost you the most, along with tight fixes that keep the work practical and business-first.
Mistake: Hiring for a resume instead of proof you can trust
A resume tells you where someone worked, not what changed because they were there. Without proof, you're betting on storytelling.
Why it hurts: you get confidence theater instead of results.
Do this instead: ask for two short case studies tied to your mission, plus two references who saw that work up close. Also request artifacts, for example a board deck, a sample risk register, or an incident playbook outline.
Mistake: Skipping decision rights, budget authority, and reporting lines
Interims fail when they can't make calls. They may see the risk clearly, but they can't move the organization.
Why it hurts: work stalls, exceptions pile up, and accountability blurs.
Do this instead: write down who approves risk assessment and risk acceptance, who owns IT operations, what the interim can spend without escalation, and who they brief weekly (CEO, GC, CIO, or committee chair).
Mistake: Letting the interim be buried under IT tickets and tool admin
If your interim spends their week in ticket queues, you're paying executive rates for operational throughput.
Why it hurts: priorities drift, and leadership routines never form.
Do this instead: pair the interim with an ops lead (internal manager, MSP, or security manager for technical infrastructure and security operations). Keep the interim focused on risk decisions, stakeholder alignment, and the weekly cadence that drives follow-through.
Mistake: Confusing compliance checklists with real security outcomes
You can pass an audit and still be one click away from a bad day. Compliance is evidence, not safety.
Why it hurts: you spend money to look organized while attackers target your gaps.
Do this instead: map regulatory compliance work to top business risks, then prioritize controls that reduce likely loss and improve security posture (identity, backups, segmentation, logging, vendor risk). For board-ready governance questions that expose real gaps, use a cybersecurity governance advisor for boards perspective.
Mistake: Not testing incident readiness before the next crisis
Many teams "have a plan," but nobody has practiced it with executives. Under stress, confusion wins.
Why it hurts: downtime grows, ransom pressure increases, and legal exposure expands.
Do this instead: within 30 days, run an executive tabletop for incident response. Confirm roles (CEO, GC, comms, IT), validate backup restores, and test isolation steps on the systems that matter most.
Mistake: Expecting a strategy deck when you need execution, or the reverse
Sometimes you need hands-on stabilization. Other times you need a clean plan and governance reset. Mixing them creates disappointment.
Why it hurts: you get a beautiful roadmap during a crisis, or frantic changes when you needed calm structure.
Do this instead: match deliverables to the trigger. Breach response needs an incident operating rhythm and containment priorities. A program reset needs a risk register, operating model, and 6 to 12-month roadmap. M&A needs integration risk triage and Day 1 controls.
Mistake: Ignoring culture and change management
Information security work breaks when people feel blamed, surprised, or blocked. Tools can't fix that.
Why it hurts: teams avoid security, hide problems, and route around controls.
Do this instead: require a simple engagement plan. The interim should show how they'll partner with product, IT, HR, and finance, and how they'll build trust without fear tactics.
Mistake: Failing to plan the handoff on day one
An interim can create a surge of momentum, but it evaporates if nothing sticks.
Why it hurts: you revert to old habits the moment they leave.
Do this instead: require a transition plan from the start. It should include documented decisions, a 6 to 12-month roadmap, and named owners for every workstream.
Mistake: Using the wrong time horizon and pay model
Vague hourly arrangements often turn into endless extensions and unclear value.
Why it hurts: you pay for time, not outcomes, and you lose urgency.
Do this instead: set a 30/60/90 plan with review points. Use a scoped retainer or milestone-based structure when possible, and agree on what "done" means before you renew.
Mistake: Waiting too long to bring the board into the plan
Board oversight isn't about panic. It's about clear thresholds and steady reporting.
Why it hurts: leadership hesitates, risk acceptance happens informally, and surprise escalations land badly.
Do this instead: agree on a simple cadence and 3 to 5 measures the board can inspect, for example risk trends, incident readiness, and critical remediation progress.
A simple hiring and onboarding playbook you can run in two weeks
When you're under pressure, you don't need a perfect process. You need a short one that prevents obvious mistakes and gets you to traction fast. If board confidence is part of the trigger, a cybersecurity board advisor view or virtual CISO can help you keep governance tight while the interim executes.
Here's a two-week flow that works in real life for rapid cyber resilience:
Define the 90-day mission: 3 to 5 outcomes, decision rights, and who owns what.
Screen for mission fit: pick candidates with proof in similar situations.
Run two interviews: one on crisis judgment, one on operating cadence and stakeholder alignment.
Do references fast: two calls tied to your mission, not generic character checks.
Contract for outcomes: time horizon, deliverables, access, authority, confidentiality, exit plan.
Kick off like an executive: Day 1 access, weekly briefing rhythm for executive buy-in, and a published first-30-day plan.
Your short scorecard for interviews and reference checks
You'll make better choices if you score candidates on a few traits that predict outcomes. Focus on mission fit, calm decision-making, board communication, prioritization skill, vendor independence, and artifact quality.
Three must-ask questions help you separate operators from talkers: (1) Outline your 30-60-90 day plan here; what do you deliver by Day 30? (2) Tell me about a high-pressure incident you led, what decision mattered most? (3) What do you stop doing in week one, and why? Watch for red flags like tool-first thinking, vague answers on authority, or blaming past teams for lack of progress.
What great looks like in the first 30 days
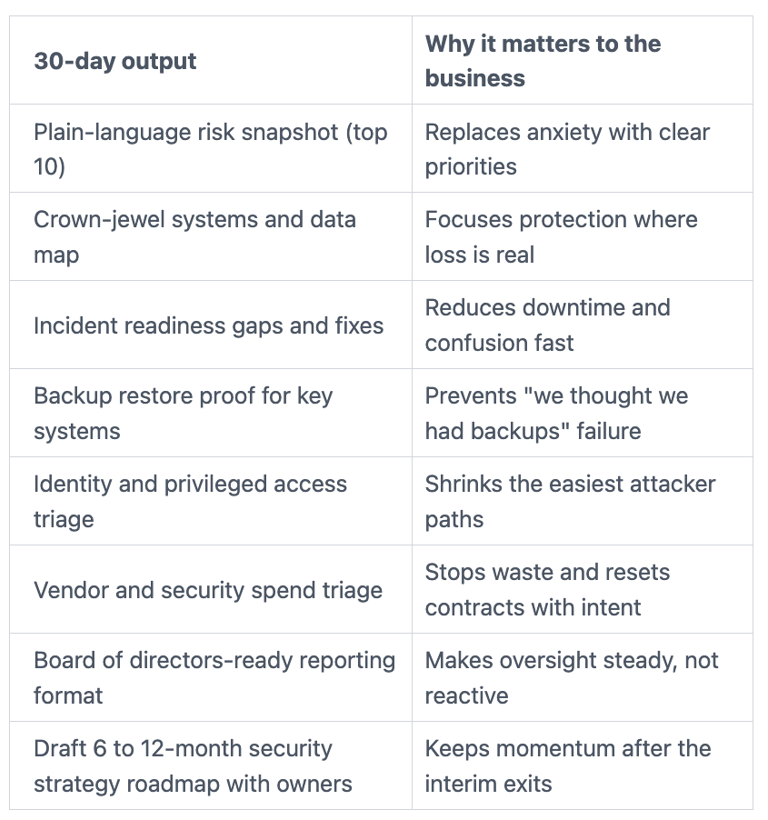
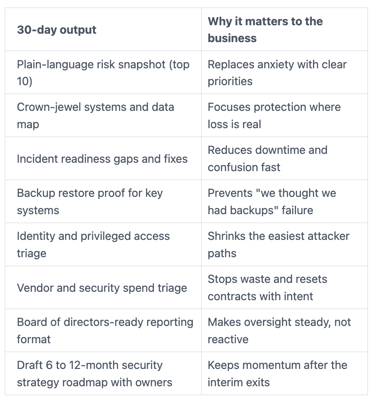
In the first month, you should see tangible outputs, not just meetings. If you want a benchmark for board-level communication and execution style, a board cybersecurity advisor perspective aligns well with what you should expect an interim leader to produce.
Here are practical outputs you can ask to see:
FAQs senior leaders ask when hiring an interim CISO
How long should an interim CISO engagement last?
Plan for 90 days when you need stabilization and clarity. Expect 6 months when you're working through an audit cycle, rebuilding a program, or hiring a permanent hire. M&A activity and integration can also stretch the timeline, especially when systems and identity need consolidation.
What should you expect to pay for an interim CISO?
Rates vary widely by scope and market. Cost usually depends on days per week, crisis intensity, travel, and the deliverables you expect. Instead of fixating on a number, tie value to reduced loss, fewer surprises, and faster decisions that prevent downtime, fines, and customer churn.
Should the interim Chief Information Security Officer report to the CEO, CIO, or General Counsel?
Match reporting to the problem you're solving. If it's enterprise risk and trust, CEO visibility often helps. If it's heavily operational and IT-led, such as digital transformation, a CIO line can speed execution, as long as escalation stays clear. For incidents and disclosure pressure, close alignment with the GC matters, plus board visibility when stakes are high.
How do you measure success without drowning in metrics?
Keep measures small and decision-friendly. Track progress on the top risks in the threat landscape, incident readiness improvements, critical remediation on crown jewels, privileged access reduction, and stakeholder confidence (can leaders explain what changed and what's next). Stability and trend matter more than perfect numbers.
Conclusion
Most Interim CISO hiring problems come from three gaps: an unclear mission, weak authority, and no transition plan. When you fix those up front, you stop paying for motion and start paying for outcomes. Write the 90-day results you expect, score candidates against real proof, and set a weekly cadence that forces decisions and follow-through to maintain program momentum after the engagement ends.
If you want a clean next step, consider whether you need short-term stabilization, ongoing part-time leadership, or a bridge to a permanent hire. For many organizations, a fractional CISO model provides the right mix of speed, accountability, and continuity, without waiting months for a full-time executive.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
