Pre-Acquisition Cybersecurity Assessment: Costs, Timeline, and Deliverables
See what a pre-acquisition cybersecurity assessment should cost, how long it takes, and which deliverables help you price risk before close.


An acquisition can transfer hidden cyber risk faster than it transfers value. If you don't see the target's weak controls, old incidents, or cleanup burden before close, you inherit them after close.
That's why a pre-acquisition cybersecurity assessment matters. It gives you plain-English clarity on exposure, likely remediation work, and whether cyber issues could affect price, timing, insurance, integration, or trust with customers and regulators. If your deal team or board needs stronger pre-M&A risk visibility, this work belongs early, not at the end.
What a pre-acquisition cybersecurity assessment should actually cover
A pre-acquisition cybersecurity assessment is not a quick scan and not a stack of screenshots. You are trying to answer a business question: what cyber risk are you buying, how hard will it be to fix, and what could go wrong soon after close?
That means the assessment should test three things at once. First, it should show you the target's current exposure. Second, it should show you the maturity of the controls that are supposed to manage that exposure. Third, it should give you a grounded view of the work, cost, and executive attention you will likely need after close.
The right scope depends on the deal. A small tuck-in acquisition with limited sensitive data needs less depth than a healthcare, fintech, or critical infrastructure target. Still, the core objective stays the same, clarity for decision-makers.
The core areas you need reviewed before closing
At minimum, you should review security governance, identity and access management, endpoint and network security, cloud setup, backup and recovery, incident history, third-party risk, ransomware readiness, legal and compliance issues, and sensitive data handling.
You also need to know who owns security. Weak ownership often matters as much as weak tools. If decision rights are fuzzy, problems stay open longer and get worse during integration.
Identity deserves special attention because many serious incidents start there. You want to know how the target manages privileged access, remote access, multi-factor authentication, and joiner-mover-leaver processes. Meanwhile, cloud review should focus on exposure that can change loss quickly, public storage, weak admin paths, poor logging, and fragile configurations.
Incident history matters too. A target that says it has had "no incidents" but can't show records, logs, or response notes is giving you uncertainty, not comfort.
Red flags that can change price, terms, or timing
Some findings change the deal faster than others. No asset inventory is one. Weak MFA coverage is another. Add unmanaged privileged accounts, unsupported systems, open critical findings, poor logging, missing incident records, unresolved compliance issues, or unclear data ownership, and you have a different transaction than the one described in the pitch deck.
These aren't only technical flaws. They can change valuation, representations and warranties, indemnities, remediation commitments, and the amount of cash you may want held back.
If the assessment can't tell you what risk may cost after close, it's not doing enough for the deal.
For example, unsupported systems may force urgent replacement spending. Weak backups may mean higher ransomware exposure during integration. Missing incident records may expand legal review and cyber insurance questions. In some cases, the right move is to pause, narrow scope, or set explicit closing conditions.
The practical takeaway is simple. You are not looking for perfection. You are looking for enough truth to price risk and act with discipline.
What drives the cost of a pre-acquisition cybersecurity assessment
Cost depends on scope, speed, and complexity. A small target with one environment, one geography, and basic evidence will cost far less than a global carve-out with cloud sprawl, regulated data, and a rushed signing date.
You should expect price to move based on target size, number of locations, business units, cloud footprint, data sensitivity, timeline pressure, and whether the work includes interviews, technical validation, or limited testing. Legal constraints can raise cost too, because they often force more manual review and tighter coordination.
The table below gives a practical planning range.
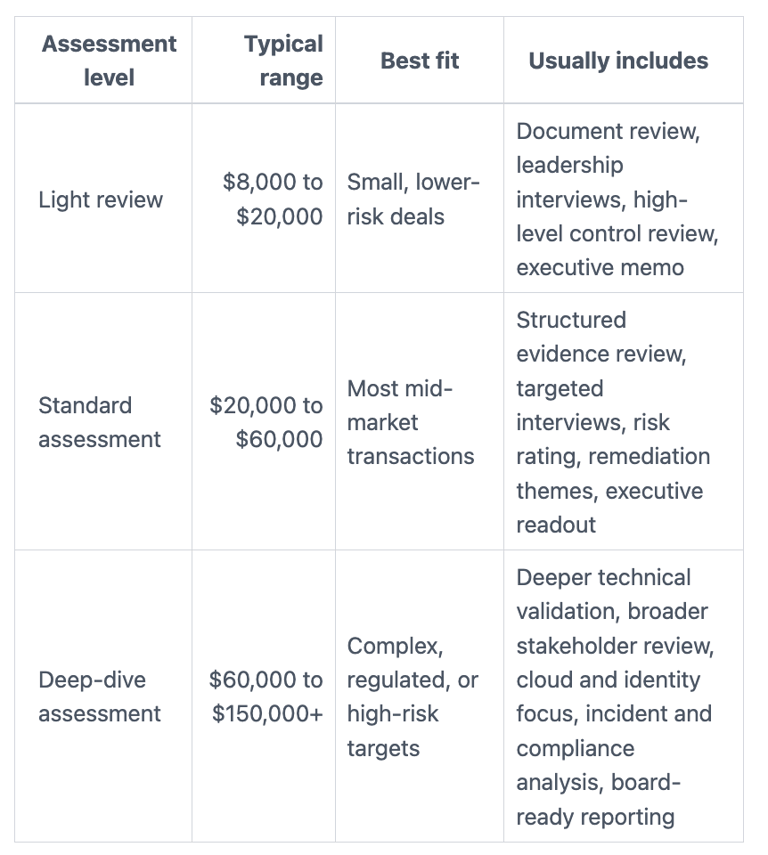
The key point is not the fee alone. The key point is whether the work is decision-ready. A cheaper review can miss the issues that later drive the most cost.
Typical cost ranges for light, standard, and deep-dive assessments
A light review works when the target is small, the data risk is limited, and you need a fast read on obvious concerns. It usually won't tell you everything, but it can help you spot whether the deal needs deeper work.
A standard assessment fits most mid-market acquisitions. It should give you a useful view of control maturity, major gaps, likely first-year remediation work, and issues worth raising in negotiation.
A deep-dive review makes sense when the target operates in a regulated sector, has international operations, has had recent incidents, or plays a core role in your future platform. In those cases, a surface read can create false comfort.
Hidden cost factors buyers often miss
Rushed timelines drive up effort. So do weak records, scattered evidence, multiple business units, and defensive target teams. Carve-outs are especially costly because control ownership often sits in awkward shared services.
Another hidden factor is reporting. Executive briefings, counsel summaries, and board-ready outputs take real judgment and time. Still, they are often the most useful part of the engagement because that's where technical facts become deal decisions.
Keep one point in view. The assessment fee is usually small compared with post-close cleanup. If you expect urgent leadership help after close, it can help to compare that separately with interim CISO service costs in 2026, not as part of diligence fees, but as follow-on support planning.
How long the assessment takes, and how to keep the deal moving
Most assessments take days or a few weeks, not months. If the target responds quickly and scope is tight, you can get a usable answer fast. Speed helps, but blind speed hurts. A rushed review that skips the wrong evidence can give you false confidence.
In practice, the work usually moves in phases. You define scope, issue a document request, review evidence, interview key people, do technical validation if needed, then prepare findings and an executive summary.
A practical timeline from kickoff to final findings
For a light review, you may finish in 3 to 7 business days. For a standard assessment, 2 to 4 weeks is common. A deep-dive can take 4 to 6 weeks, sometimes longer if there are carve-outs, legal limits, or major evidence gaps.
A simple cadence often looks like this:
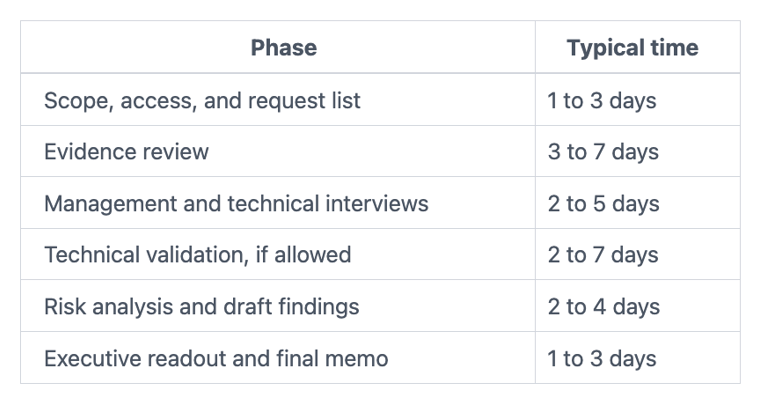
Compressed deals often run these steps in parallel. That can work, but only if you decide early which issues must go straight to leadership.
What slows the work down, and how you can avoid delays
The usual blockers are predictable. Missing documentation slows review. Unclear points of contact create churn. Weak inventories force guesswork. Legal limits on testing narrow what you can confirm. Some target teams also become defensive, which wastes time and lowers signal.
You can avoid much of this by setting a focused scope early. Keep the request list tight. Name one point person on each side. Also decide in advance what gets escalated, what stays in working sessions, and what evidence counts as enough.
If urgent findings show up before close, your next issue is usually stabilization. In that situation, short-term leadership support during acquisitions can help you move from discovery to managed action without losing deal momentum.
The deliverables you should expect, and how to use them in the deal
A good assessment does not end with technical detail. It ends with outputs you can use in valuation, negotiation, and transition planning. If the report is long but not clear, it has missed the mark.
The strongest deliverables separate confirmed facts from assumptions. They also distinguish current exposure from likely post-close work. That matters because your legal team, deal team, and board may need different views of the same issue.
The must-have outputs for executives, counsel, and the board
You should expect these core outputs:
Executive summary: Plain-English findings, top risks, and the decision points that matter now.
Prioritized risk register: Ranked issues, with severity, business impact, and likely owner.
Severity-rated findings: A clear split between critical, high, moderate, and low concerns.
Business impact notes: Why each issue matters to operations, revenue, legal exposure, or trust.
Remediation cost estimates: Rough order-of-magnitude cleanup cost, not false precision.
First-100-day action plan: The steps you should take after close, in sequence.
Open questions and evidence gaps: What could not be verified, and why that matters.
The best versions of these outputs help leadership act without inflating certainty. That is what lets you defend the decision later.
How assessment findings should shape negotiation and post-close planning
You should use the findings to adjust price, set holdbacks, require remediation commitments, refine reps and warranties, and shape cyber insurance discussions. The same findings should also feed your integration roadmap, because control gaps rarely stay isolated after close.
For example, weak identity controls may raise urgent day-one access concerns. Poor backups may change business continuity planning. Missing incident records may expand legal review and customer communication prep. Each of those issues belongs in your deal model, not in an appendix nobody uses.
If the target's weaknesses are manageable but leadership bandwidth is thin, short-term interim CISO services for acquisitions or fractional CISO support during deal timelines can give you executive capacity to run remediation and integration without waiting for a full-time hire.
A pre-acquisition cybersecurity assessment is not about finding every flaw. It is about getting enough clarity to price risk, protect the deal, and plan your first moves after close.
That means you should ask for decision-ready findings, realistic cost estimates, and a usable timeline, not only technical detail. Start early, because the earlier you start, the more options you keep.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
