The ROI of Interim CISO Services for Mid-Market Firms
See how Interim CISO Services pay off for your mid-market firm, cut tool sprawl, tighten incident readiness, and speed deals in 30 to 90 days.
Security pressure rarely comes from one place. You've got more vendor connections than you can count, more rules to answer to, and more AI-driven attack speed than your team can calmly absorb. At the same time, time for a Chief Information Security Officer is often the scarcest resource in the building.
That's where Interim CISO Services, such as a Virtual CISO, can earn a real return, fast, if you treat the role as outcome-driven leadership, not an expensive consultant.
ROI, in plain terms, is what you get back compared to what you spend. With an interim CISO leading your cybersecurity program, that "get back" usually shows up as money saved (less waste), loss avoided (less downtime and fewer surprises), growth enabled (fewer deals stuck in security review), and leadership confidence (clear decisions, clear owners, clear reporting). You'll leave with a practical way to estimate ROI, where value actually appears, and how to choose between interim, fractional, or full-time leadership.
Key takeaways you can use to judge ROI fast
In the first 30 days, you gain clarity on your top risks through risk assessment, owners, and next decisions.
Costs often drop when you cut duplicate tools, shrink vendor sprawl, and stop low-value work to ensure regulatory compliance.
Risk shrinks quickly when you tighten identity, access, backups, and incident roles.
Sales friction goes down when security questionnaires get consistent, fast answers.
Metrics should stay small (5 to 7) and tie to downtime risk, recovery readiness, and execution.
Before you sign, confirm decision rights (who can approve changes, spend, and risk acceptance).
Choose interim leadership for urgency, for example when you need an interim security executive for fast risk stabilization instead of waiting months for a permanent hire.
Where the ROI of Interim CISO Services actually comes from in a mid-market firm
Mid-market firms don't usually fail because they lack security tools. They fail because work gets fragmented. Priorities compete. Exceptions pile up. Then a regulator, customer, or attacker forces the business to answer questions it can't answer quickly.
Interim Chief Information Security Officer (CISO) services create ROI through a few reliable value streams, with information security leadership driving much of that value.
First, you replace guesswork with decisions. When security becomes "everyone's job," it often becomes nobody's call. An interim CISO sets decision rights, a weekly cadence, and a short list of priorities that match your business reality.
Second, you turn scattered activity into a focused Security strategy. That plan should name owners, timelines, and tradeoffs. It also should stop work that looks busy but doesn't lower risk.
Third, you reduce risk in ways that affect real loss. The fastest wins usually live in identity, access, backup recovery, and Incident response. Those aren't glamorous, but they directly change outage outcomes.
Finally, you gain risk-adjusted value, not just hard dollars. If you cut the chance of a three-day outage, you didn't "make money," but you changed your financial exposure. For a board or CFO, that's still value.
You reduce the cost of uncertainty, not just the cost of breaches
Uncertainty is expensive because it creates drag. Projects stall while teams debate "secure enough." Audits turn into fire drills. Vendors get onboarded with weak guardrails, then you pay for cleanup later. Insurance renewals bring surprise exclusions because nobody can show evidence fast.
Security by committee also breeds rework. One team ships. Another team later blocks it. Everyone loses time, and trust takes a hit.
An interim CISO reduces that cost by making the hard calls visible and repeatable through strong information security leadership:
Your top risks get ranked in plain language for Board reporting.
Each risk gets an owner and a due date.
"Good enough for now" gets defined, so teams can move without gambling.
Most importantly, you stop treating security as a parallel universe. You connect it to what the business is trying to do this quarter. If you want a clearer picture of that approach, read about aligning security to business goals. That alignment is where ROI becomes easier to defend, because you can explain why each decision matters.
If you can't name your top three cyber risks and who owns each one, you're paying an "uncertainty tax" every week.
You get fast incident readiness that lowers real loss
Mid-market incidents often turn into expensive chaos for a simple reason: nobody practiced, and nobody knows who decides what under pressure.
Interim leadership can tighten incident readiness quickly, even without rebuilding your whole program. The early focus is practical:
You assign incident roles (who leads, who approves shutdowns, who talks to counsel, who talks to customers). You create or refresh ransomware playbooks. You test backups and recovery steps, not just whether backups "exist." You run a tabletop exercise that forces real decisions about downtime, communications, and spending authority.
Those actions don't just strengthen Security posture. They change loss math. Less downtime means less revenue impact. Cleaner evidence handling reduces legal confusion. Faster containment lowers the spread. Better communications reduce customer churn.
If your leadership team needs a board-friendly way to frame these decisions, use guidance on ransomware readiness for leaders. When you pre-make a few key calls, you cut the hours lost to debate when the clock is running.
A simple ROI model you can explain to your CFO and board
You don't need perfect numbers. You need a defensible range that improves decisions and gets tracked over 90 days.
A simple model has two parts:
Baseline cost reduction (things you already spend every month)
Risk reduction (loss avoided via effective cyber risk management, expressed as scenarios with probability ranges)
Then you track results with a low, likely, and high estimate. This avoids fake precision and keeps the conversation honest.
Start with baseline costs you already feel every month
Start with costs your finance team will recognize. In many mid-market firms, the fastest baseline wins come from waste and friction, not from buying new tools.
Common baseline buckets include tooling overlap, duplicate vendors, audit and regulatory compliance overtime, gaps in legal and incident retainers, slow employee onboarding due to access confusion, delayed sales tied to questionnaires, and rising insurance premiums tied to weak evidence.
To gather numbers fast, ask four groups for what they already know:
Finance: security software, consulting, insurance, and unplanned overtime
IT and Engineering: time spent on patch fire drills, access cleanups, and vendor exceptions
Legal: outside counsel costs and incident-related readiness gaps
Sales Ops: cycle time impacts from security reviews and customer assurance requests
You're not building a dissertation. You're building a "directionally correct" baseline you can improve. An interim CISO should help you convert that into a short list of cost moves, with owners and dates.
Add risk reduction in plain English using scenarios
Next, use two or three scenarios tied to common cyber threats that your executives already worry about. Keep them concrete:
Ransomware outage that stops billing or operations
Vendor breach that exposes your customer data, undermining data protection
Misconfigured cloud security exposure that becomes a public incident
For each scenario, estimate four inputs:
Downtime hours
Revenue (or mission impact) per hour
Recovery and response cost (internal time plus outside support)
Probability range (low, likely, high over 12 months)
Then ask a simple question: "If interim leadership reduces downtime by 30 percent, what changes?" You'll quickly see how preparedness pays back.
During a real event, your board will also want calm, credible reporting. That's why it helps to adopt crisis metrics leaders can trust, such as time-to-decision, containment confidence, and business impact estimates that get updated on a steady cadence.
What you should expect in the first 30, 60, and 90 days
Interim CISO Services deliver ROI when the work stays time-boxed and outcome-based. You're buying traction, not theory.
A realistic timeline looks like this: stabilize first, then build a right-sized plan, then prove progress with a few metrics.
First 30 days: stabilize, get visibility, and stop the bleeding
In the first month, you should expect rapid triage, not a months-long assessment. The goal is to reduce obvious exposure and remove confusion.
You'll usually see a short risk review and gap analysis, a ranked top 10 risk list, and a snapshot of control health (identity, access, backups, logging, patching and vulnerability management, vendor access). Incident readiness gets checked quickly: roles, call tree, comms plan, and whether your "plan" would work at 2 a.m.
Quick wins matter here because they create confidence. That might include removing stale accounts, tightening admin access, expanding MFA in the right places, or proving restore steps for one critical system.
You also want a decision log to support security governance. When tradeoffs come up, you record what you decided and why. That prevents re-litigation and keeps the organization moving.
If you want an example of this kind of engagement posture, look at interim leadership that drives clarity. Clarity is the first return you feel, because it stops the organization from spinning.
Days 31 to 90: build a focused plan and prove progress with metrics
Once the bleeding stops, you need a plan your teams can actually execute. That means a right-sized roadmap for the cybersecurity program, budget recommendations with ranges, and vendor and contract clean-up where it saves money or lowers exposure.
In this window, you also establish the minimum set of Information security policy that unblock work. The best policies read like guardrails, not legal novels. You define how new vendors get approved, how exceptions work, and what "good" looks like for access, logging, and recovery testing.
Finally, you pick a small set of metrics tied to business outcomes. Think in terms of recovery readiness, identity coverage, exposure windows, and trend progress against the roadmap. If you struggle to choose metrics that executives will actually use, start with guidance on finding value in cyber metrics. The goal is decisions, not dashboard theater.
How to choose the right interim CISO so you actually get ROI
You don't get ROI from a resume. You get it from fit, authority, and an operating rhythm that survives busy weeks.
A strong interim leader should sound like an executive, act like an operator, and write like a human. You want clear tradeoffs, not fear-based selling.
Use a scorecard that tests business fit, not just security skills
Technical depth matters, but mid-market ROI depends on leadership behaviors. Use a simple scorecard in interviews. Listen for clarity, not jargon.
Here's what to test:
Board communication: Can they brief risks in plain language and recommend decisions?
Calm under pressure: Do they have real incident leadership experience?
Ability to simplify: Can they cut scope without losing the plot?
Framework comfort: Can they use the NIST framework or ISO for Governance Risk and Compliance without turning it into bureaucracy?
Vendor and team leadership (including third-party risk management): Can they drive outcomes through others, fast?
M&A readiness (if relevant): Can they assess risk quickly and support integration planning?
CEO trust: Can they partner with you, even when the news is bad?
If you want a stronger set of screening questions, use guidance on how to vet a CISO. The right hire will show you how they think in the first 15 minutes.
Avoid common ROI killers in interim engagements
Most interim failures are predictable. They happen when the leader has responsibility without authority, or when the engagement starts with tools instead of outcomes.
Watch for these ROI killers: unclear decision rights, no executive sponsor, tool-first thinking, too many metrics, no weekly operating cadence, and security strategy that never gets executed.
For a clean start, align on five basics up front:
Scope (what's in, what's out)
Outcomes (what changes in 30, 60, 90 days)
Stakeholders (who must show up, and when)
Meeting rhythm (weekly cadence plus escalation rules)
"Done" definition (what a successful handoff includes)
When those are set, your interim CISO can move like a field commander, focused, calm, and accountable.
FAQs: ROI, pricing, and when Interim CISO Services are the wrong fit
How do you measure ROI if you do not have a breach?
You measure leading indicators that change loss outcomes and execution speed. For example, restore testing results for critical systems, reduced audit findings, fewer duplicate vendors, faster approvals for high-value projects, and shorter cycle time for customer security reviews.
You can also measure decision speed. When security decisions stop stalling, you feel it across the business.
Interim vs fractional vs full-time CISO, what delivers the best ROI?
"Best" depends on urgency and load. This table helps you choose based on what you need now.
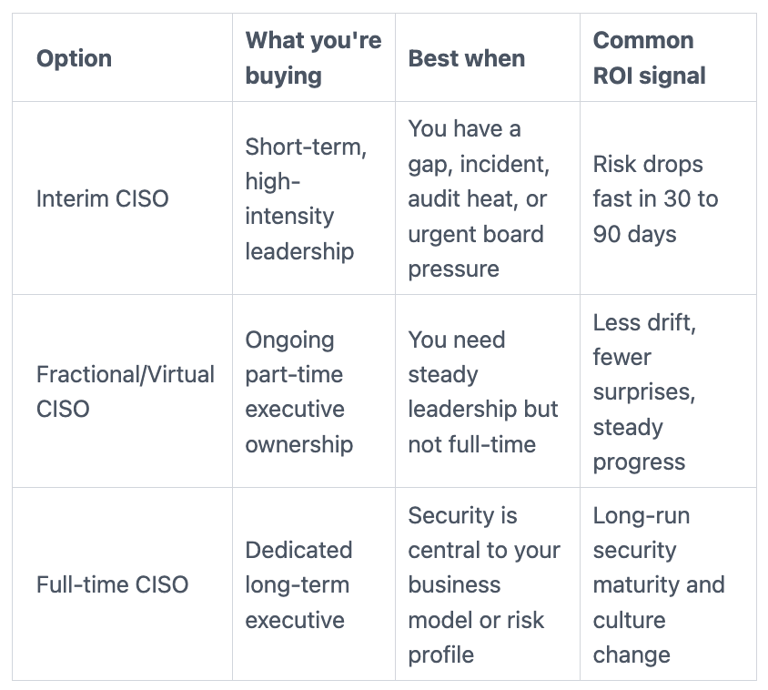
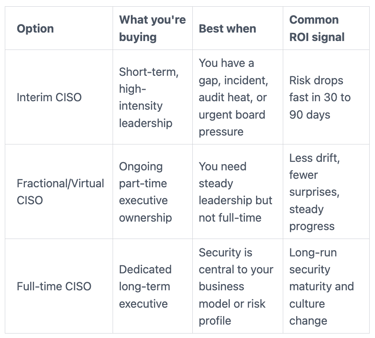
If fractional feels like the right fit, especially for mid-market firms facing specific regulatory needs like HIPAA compliance, consider fractional CISO support for mid-market firms when you need ongoing decision ownership without a full-time hire.
What does an interim CISO typically cost, and how do you budget it?
Pricing usually comes as a monthly retainer, a day rate, or a fixed-scope package. Cost drivers include complexity, travel, current incident risk, and how much hands-on execution you expect.
Budgeting works best when you compare it to total full-time cost (salary, benefits, recruiting fees, ramp time) plus the cost of waiting. Factor in a transition plan for the handoff to ensure continuity. If an interim CISO prevents even one extended outage, the math often gets simple.
When is hiring an interim CISO a bad idea?
It's a bad idea if you won't provide access or authority, or if you refuse to prioritize. It also won't work if you only want 24-7 alert handling with no leadership component.
If your real need is security operations coverage, consider managed detection and response, staff training, or targeted consulting. Interim leadership works when you're ready for decisions and change, not just a report for optics.
Conclusion
The ROI of Interim CISO Services doesn't come from a magic tool. It comes from faster decisions, lower loss exposure, and execution that keeps moving when the calendar gets ugly. You replace uncertainty with clear owners, a focused plan, and proof that risk is dropping to build business resilience.
To get started, take three steps this week: pick three cost buckets you want to shrink, pick two risk scenarios you want to improve, then define 90-day outcomes like security awareness training you can track in leadership meetings. If you're ready to move, explore hiring an experienced CISO for high-stakes change to deliver the information security leadership your team needs and set the mandate before day one.


