How CISOs Can Translate Cyber Risk Into Business Impact for the Board
You improve board reporting for cybersecurity program decisions by showing how cyber risk affects revenue, operations, legal exposure, and trust.


You may understand cyber risk in detail, but your board needs something else. It needs to know what that risk means for revenue, operations, legal exposure, customer trust, and strategic goals. If you can't make that connection clearly, the board can't govern well.
That is the core tension in every cyber briefing. The issue is rarely a lack of data. More often, it is a lack of translation. Strong board reporting for cybersecurity program maturity depends less on technical depth and more on business clarity.
Your job is not to impress directors with threat terms. Your job is to help them see material exposure, understand what changed, and make sound decisions under pressure.
Start with the business, not the threat list
Board conversations should begin with what the business is trying to protect or achieve. Start with growth targets, uptime commitments, margin pressure, compliance duties, customer retention, or a pending deal. Then connect cyber risk to those priorities.
If you begin with tool gaps, vulnerabilities, or alert volume, you force directors to do the translation themselves. Most won't, and they shouldn't have to. The board's role is oversight, not decoding security language.
This shift matters because boards compare cyber risk with every other enterprise risk. They already think in terms of business interruption, financial loss, legal exposure, and strategic drag. Meet them there first, and your briefing gets sharper fast.
Map cyber risks to the outcomes the board already tracks
You don't need a long catalog of scenarios. You need a short set of business-relevant ones. For each major cyber risk, show the likely operational and financial effect.
A ransomware event is not just a malware issue. It may mean five days of billing disruption, delayed shipments, contract penalties, and missed quarterly targets. Weak third-party controls are not just a vendor problem. They may mean customer churn, regulatory review, or slowed integration after an acquisition.
That is why you should map risks to outcomes the board already knows how to evaluate. A simple frame works well: revenue loss, downtime, legal cost, delivery delay, and trust erosion. If you want a broader model for tying security choices to executive priorities, this perspective on a cybersecurity strategy advisor for CEOs is useful.
When cyber risk looks like business risk, the board can compare it, rank it, and act on it.
Translate technical findings into likely business disruption
Technical findings matter, but only after you convert them into plain language. A critical vulnerability is not the message. The message is what that weakness could stop, slow, or cost.
For example, don't say, "Identity controls are weak in the cloud admin layer." Say, "A compromised admin account could disrupt core systems, delay customer orders, and increase legal exposure if sensitive data is touched." That phrasing is clear, repeatable, and decision-ready.
Focus on three things, probability, scale, and timing. How likely is the event, how big is the effect, and how quickly could it hurt the business? That keeps the discussion grounded.
If a director can't repeat the risk in plain English, the board doesn't understand it yet.
Fear is not the goal. Clarity is.
Give the board a simple model for business impact
The board needs a stable way to compare risk over time. Without that, every meeting starts from scratch. A repeatable model keeps discussion focused on what changed, what matters now, and what management recommends next.
This is where board reporting for cybersecurity program maturity often rises or falls. Not on slide count, not on technical detail, but on consistency. When you use the same impact model each quarter, directors can challenge assumptions without getting lost in format changes.
Use a few impact lenses the board can understand fast
Keep your impact lenses limited and stable. Five are usually enough: financial loss, operational disruption, legal and regulatory exposure, strategic delay, and reputation harm.
Too many categories create noise. Directors stop comparing risks and start debating labels. You want the opposite. A stable model helps the board test tradeoffs, ask better questions, and spot drift early.
For example, a cloud concentration issue may not look urgent from a control view. But through a business lens, it may create severe operational disruption and strategic delay if a key platform fails during a product launch. That is a board issue.
These same lenses also help management. They force you to explain why a risk matters, not just why a control is missing.
Show risk in ranges, not false precision
Exact dollar estimates often create false comfort. Most cyber scenarios carry uncertainty, especially before an incident occurs. Therefore, use directional ranges that support decisions instead of pretending you can predict exact losses.
A simple range-based view works well:
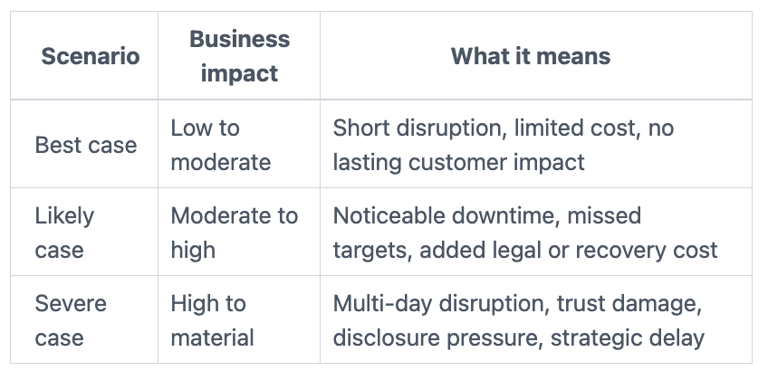
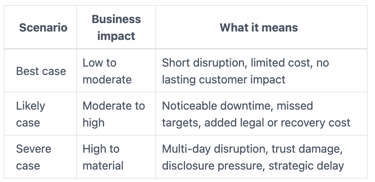
This format gives directors something they can use. It shows uncertainty honestly, while still helping them judge severity.
The takeaway is simple. Precision is less useful than a decision-grade range tied to business consequences.
Build board reporting that shows what changed and what needs a decision
Useful reporting does not try to tell the board everything. It tells the board what changed, what remains exposed, what management is doing, and where a decision is required.
That sounds obvious, but many updates still miss the mark. They offer status without movement, activity without effect, or reassurance without evidence. A board packet should make trend, posture, and action clear in minutes.
Lead with trend, exposure, and decision points
A strong update starts with change since the last meeting. Which risks increased, which decreased, and why? Then show what management did, what still needs work, and where delay would raise exposure.
That structure creates a clean board conversation. Directors can focus on oversight instead of pulling basic facts out of the room. It also supports better challenge, because they can see movement over time instead of a one-time snapshot.
If you want a board-level view of what good oversight looks like, this guide to cybersecurity governance for boards aligns well with that discipline.
A useful board update usually answers five things in order: what changed, what it means, what management is doing, what support is needed, and what happens if action slips.
Cut vanity metrics that hide the real story
Some metrics create motion but not insight. Blocked attack counts, patch totals, and alert volume usually tell you more about system activity than business exposure. They can make a board packet look busy while hiding what matters.
Instead, show measures tied to critical assets and business effect. For example, track unresolved control gaps around crown-jewel systems. Track time to contain high-impact incidents. Track third-party concentration risk where one supplier failure would stop revenue. Track overdue fixes tied to regulated data or business-critical processes.
These measures are not flashy, but they are useful. They help the board see where exposure sits and whether it is shrinking.
Good reporting is not dense. Good reporting is honest.
Help directors act on cyber risk without turning them into operators
The board should challenge, approve, and guide. It should not run your response plan or manage your backlog. When you translate cyber risk well, you help directors stay in their lane while doing their job better.
That distinction matters. Weak reporting often causes one of two failures. Either the board stays too high-level and passive, or it drops into technical detail because the business issue never became clear.
Ask for decisions, not just attention
End your board discussion with a clear ask. If you don't, the meeting produces awareness but not action. You may need approval for funding, confirmation of risk acceptance, support for a policy position, or agreement on the order of major priorities.
Make management's recommendation plain. Then show the tradeoffs. If the board delays funding for identity improvements, what stays exposed? If it accepts a third-party risk temporarily, what trigger would require re-review?
This is where strong governance takes shape. Directors do not need every technical detail. They need a clear choice, a rationale, and the cost of waiting. A seasoned board cyber risk advisor can help sharpen that boundary between oversight and management action.
When the board knows what decision is being requested, the quality of the discussion improves.
Create a steady reporting rhythm the board can trust
Trust grows from consistency. Use the same format, the same definitions, and the same impact model each quarter. Over time, that rhythm lets the board see whether the program is reducing risk or just producing activity.
Plain-English commentary matters here. Numbers alone rarely explain whether a trend reflects real improvement, delayed remediation, a business change, or rising concentration risk. Your commentary should do that work, briefly and directly.
A steady cadence also lowers drama. Directors stop feeling surprised. Management stops rebuilding the story every meeting. The conversation becomes more disciplined, because everyone can see progress, slippage, and unresolved choices in the same frame. For ongoing business-first perspective, these CISO insights for leaders can help keep reporting grounded in decisions, not noise.
Consistency is not cosmetic. It is what makes oversight credible.
In the end, your role is not to showcase technical depth. It is to help the board understand business exposure, trend, choices, and consequences. When you translate cyber risk into business impact, directors govern with more confidence, management gets clearer direction, and the business is better prepared to act when pressure rises.


