Do I Need a CISO? The Checklist to Decide in 15 Minutes
Do I Need a CISO? Use this 15-minute checklist to score risk, pick full-time, fractional, or interim help, and give your board proof, fast.


Information security has a way of outgrowing "IT stuff" without anyone noticing. One month you're answering a customer questionnaire about cyber threats, the next you're debating cyber insurance terms, and suddenly the board wants to know who owns the risk.
A CISO (Chief Information Security Officer) is the executive who owns cyber risk decisions. They set priorities, assign accountability, test readiness, and report progress in plain business terms. They're the person you look to when you need a defensible answer, not a technical debate.
This is a fast checklist, not a full assessment. In about 15 minutes, you'll land in one of three outcomes: hire a full-time CISO, bring in fractional or interim help, or strengthen your current model. If you want a CEO-focused view on cybersecurity strategy and aligning security to business priorities, start with this guidance on aligning security to business strategy.
Key takeaways (fast):
You need clear ownership, not more tools.
Score the checklist, then match it to the right leadership model.
Board confidence comes from proof, not promises.
The best time to add CISO-level leadership is before urgency turns into chaos.
Before the checklist, get clear on what you want a CISO to own
If you're asking "Do I Need a Chief Information Security Officer," you're really asking a sharper question: who owns cyber risk outcomes here?
A CISO isn't a tool buyer, and they shouldn't be your most expensive ticket-closer. They're an executive owner of decisions, tradeoffs, risk management, and proof. That includes setting a risk appetite (what you will and won't accept), translating business priorities into a security roadmap, and making sure incident response works in real life, not just in a binder.
Here are examples of decisions that should have one clear owner:
How much downtime you can tolerate for critical operations, and what you'll fund to reduce it.
Which third parties get deeper access, and what evidence you require before you trust them.
What "ready" means for your cybersecurity posture against ransomware, and whether your backups and recovery steps are tested.
Which security work gets done this quarter, and what gets deferred, with eyes open.
Confusion usually shows up in three places.
First, people blur IT operations with security leadership. Your Chief Information Officer may run systems well, but security is a different job. It's about adversaries, uncertainty, and business risk choices.
Second, teams confuse compliance with resilience. A clean audit can still leave you exposed to account takeover, ransomware, and vendor incidents.
Third, organizations mistake policy writing for execution. A policy is a promise. Execution is the proof that promise holds under stress.
If nobody can clearly answer who owns cyber risk outcomes, you likely need CISO-level leadership. If you want a reference point for what strong alignment looks like, this description of what a business-aligned CISO looks like is a useful yardstick.
The simplest definition: a CISO turns cyber risk into decisions you can defend
You don't need your leadership team debating encryption settings in a board meeting. You need someone translating information security into decisions you can stand behind, even after an incident.
A CISO frames risk in business terms, like revenue impact, downtime, legal exposure, customer trust, and operational drag. Then they set priorities you can inspect: what happens now, what happens next, and what can wait.
They also create measurable outcomes. "More controls" sounds busy, but clear decisions and measurable outcomes are what reduce surprises.
Think of it like a pilot's checklist. You can't fly on hope. You fly on clear steps, verified readiness, and disciplined habits.
When "the IT lead handles security" is fine, and when it is not
Sometimes it's fine, especially when your footprint is small and your exposure is limited. For example, it can work when you have a simple environment, low data sensitivity, and a short, stable vendor list.
It's also fine when customer expectations are light, and you rarely face security reviews. In that case, your biggest need may be clean basics, not an executive security function.
On the other hand, it stops being fine when your risk profile changes faster than your governance. Regulated data (payments, health, education, sensitive employee data) pushes you toward formal ownership. Rapid growth expands the attack surface, even if your team stays the same size.
Customer trust pressure matters too. If enterprise buyers ask for proof, or your cyber insurer keeps raising requirements, the "IT lead covers it" model often breaks. At that point, you're not missing effort, you're missing executive decision-making and accountability.
The 15 minute "Do I Need a CISO?" checklist
Use this as a quick scoring exercise. Answer Yes or No. Count your Yes answers.
Scoring guide:
0 to 3 Yes: tighten the basics, clarify ownership, and improve proof.
4 to 7 Yes: a virtual CISO (vCISO) or fractional leadership is likely your fastest path.
8+ Yes: you need dedicated CISO-level leadership, even if you start with interim.
You'll see two buckets below. The first is about business exposure and trust. The second is about execution, governance, and risk management, which is where good intentions go to die.
Risk and trust signals you cannot ignore
Do you store or process regulated or highly sensitive data subject to regulatory compliance? If yes, you need clearer accountability and stronger evidence.
Do enterprise customers ask for security reviews, SOC 2 evidence, NIST Cybersecurity Framework alignment, ISO 27001 certification, or detailed questionnaires? If yes, security directly affects sales velocity and trust.
Has cyber insurance renewal become harder, slower, or more expensive? If yes, external pressure is telling you your controls and proof aren't strong enough.
Do critical systems need high availability (revenue stops if they stop)? If yes, resilience planning becomes a leadership problem, not an IT chore.
Do you rely on key third parties that can touch sensitive data or production systems? If yes, vendor risk becomes your risk, even when it's "their issue."
Is your IP or product roadmap a competitive advantage that would hurt if leaked? If yes, you need clear protection priorities and access discipline.
Have you had a real incident like a data breach or a near miss in the last 18 months? If yes, treat it like a smoke alarm, not a one-time nuisance.
Are you in an acquisition, merger, IPO path, major migration, or AI-driven transformation? If yes, change will outrun controls unless someone owns the tradeoffs.
Execution and GRC red flags that point to CISO-level ownership
Can't you clearly name who can accept cyber risk, approve exceptions, and fund fixes? If decision rights are fuzzy, work stalls and risk grows.
Do you lack a prioritized security roadmap that maps to business goals? Without a roadmap, you'll fund noise, not risk reduction.
Don't you have a reliable inventory of your key systems and "crown jewel" data? You can't protect what you can't name.
Do you have an incident response plan that you haven't practiced with leaders in the last year? A plan you haven't rehearsed won't hold under pressure.
Is access control inconsistent (stale accounts, too many admins, messy offboarding, unclear MFA coverage, as shown in vulnerability assessments)? Identity is the front door, and attackers try doors first.
Do audit findings or recurring issues keep coming back quarter after quarter? Repeats usually mean leadership and follow-through problems, not tool gaps.
Do you struggle to produce simple, board-ready metrics that show progress and exposure? If you can't show it, you can't govern it.
If your score points to part-time executive support, this explainer on what a fractional CISO does can help you picture the outcome. If your score is driven by a major change or a sudden leadership gap, consider interim leadership during change to stabilize risk fast.
Match the result to the right CISO model: full-time, fractional, interim, or advisor
Your score gives you a direction, but the right model depends on speed, complexity, and how much execution muscle you already have.
If you scored 0 to 3 Yes, your job is to tighten basics and clarify ownership. You may not need a CISO title yet, but you do need one executive accountable for outcomes, plus a simple plan and reporting rhythm.
If you scored 4 to 7 Yes, you're in the danger zone for "busy, but not safer." A fractional CISO often fits here because you can get senior decision-making from a vCISO or virtual CISO without a long hiring cycle. An outsourced CISO can also fit if the pressure comes from a transition, like growth, audit strain, or a leadership gap.
If you scored 8+ Yes, treat this as a signal that cyber risk is already a C-suite problem. You can start with an interim CISO leader, but the destination is usually a dedicated CISO who owns the program end to end. If you want to explore options for bringing in an experienced CISO, focus on outcomes you can verify in 30 to 60 days, not a glossy strategy deck. A fractional CISO can bridge the gap if you need targeted expertise alongside your team.
Sometimes you don't need someone to run the whole function. You need an outside executive who can pressure-test decisions, sharpen reporting, and coach your current leaders. That's where engaging a CISO advisor can make sense, especially if you have strong operators but weak governance.
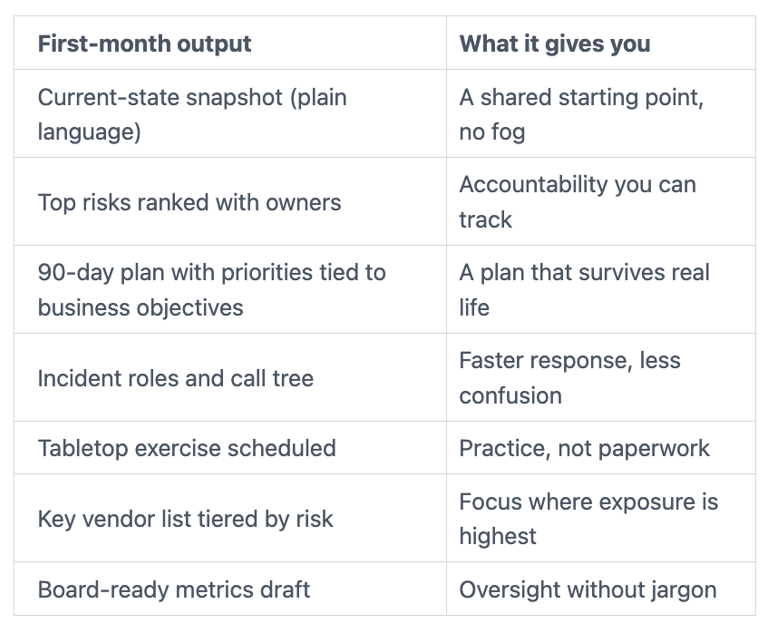
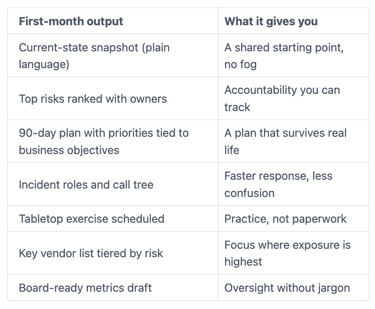
What to expect in the first month, so you know it is working
Here's what "good" looks like early, in tangible outputs:
Board ready proof: what you should be able to show, say, and measure
The board of directors doesn't need technical detail to do good oversight. They need a short set of artifacts that turn security into governance.
You should be able to show a simple risk register that names your top risks, the business impact, the owner, and what's changing. Keep it tight. If it's 50 pages, it won't get used.
You should be able to say, in one minute, what you're protecting most. That usually means naming your crown jewels, such as key cloud security assets, your highest-risk third parties, and your incident readiness status.
You should be able to measure progress with a handful of metrics tied to outcomes, not tool activity. Examples that tend to work:
Time to patch critical systems (trend, not perfection)
MFA coverage for key systems and admins
Disaster recovery backup test results (can you restore, how fast)
Third-party reviews completed for high-risk vendors
Time to assemble the incident team and make first decisions
Completion rates for security awareness training (human-centric progress)
If you want a strong board framing for measurement, review this guidance on board oversight and Chief Information Security Officer performance metrics. For a practical reminder of why a few good measures beat a noisy dashboard, see the hidden value of cyber metrics.
If you sit on a board or committee, use these questions to raise the bar fast
You don't need trick questions. You need questions that force clarity.
Ask the CISO who owns cyber risk outcomes, and how that ownership shows up in decisions. Ask the CISO for the top five risks in plain language, with one sentence on impact. Ask whether incident response has been practiced with executives, and what changed after the last exercise. Ask how third parties are tiered and monitored, especially those with sensitive access. Ask the CISO what tradeoffs the team is making with budget and staffing, and what risk they're accepting because of it, particularly around the overall cybersecurity posture.
If you want a committee-ready set, start with these audit committee cyber risk questions.
Conclusion
You don't need a Chief Information Security Officer because security feels scary. You need CISO-level leadership in information security when you need clarity, accountability, and speed in decisions you can defend. Use the checklist score to pick a model, then judge success by what you can show and measure in the first month.
If you want to validate your result with a quick conversation, focus it on decision rights, top risks, and proof. That's how you start building trust with CEOs through clear cyber decisions in the evolving threat landscape.
FAQ
Do I need a CISO if I outsource IT?
Yes, even for SMBs, if risk decisions still lack an owner. An MSP can run operations, but you still need a CISO accountable for tradeoffs, readiness, and reporting.
What is the difference between a CISO and an IT director?
An IT director usually owns service delivery and uptime. A CISO owns security risk outcomes, including incident readiness, third-party risk, and board-level reporting.
When does fractional stop making sense?
It stops making sense when security work demands daily executive presence during digital transformation, or when the risk profile stays consistently high. At that point, fractional should transition to a dedicated CISO.
How fast can you get value from an interim CISO?
You can see value in weeks if they have authority and access. The first wins are clearer priorities, tighter access, and a tested incident path.
What should the board see each quarter?
A short risk update on cybersecurity strategy, readiness status against cyber threats, third-party posture, and a few stable metrics tied to outcomes. The goal is decisions and confidence, not a flood of technical charts.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
