Is an Interim CISO the Smartest Security Move for Your Company?
Need security control fast? An Interim CISO gives you decision rights, a 30 to 90-day risk plan, and audit-ready progress you can show to your board.


You can feel it when security starts to drift. Customer questions get sharper. Auditors ask for proof, not promises. Your team is busy, but you can't clearly say you're safer. Meanwhile, hiring a full-time Chief Information Security Officer can take months, and the risk doesn't wait.
That's where an Interim CISO can be the cleanest move. Not as a bandage, but as a short, focused leadership assignment with real authority. You get someone who can make decisions, set priorities, and steady the program fast, especially when the business is in motion.
If you're trying to regain control quickly, a good starting point is understanding what it means to bring experienced cybersecurity leadership in fast, like this guidance on bringing in an interim security executive for rapid stabilization. The real question is simple: will an Interim CISO create clarity and execution now, or will it just delay the hard work of a traditional executive search?
Key takeaways to decide if an Interim CISO fits your situation
It's a great fit when time matters: You need accountable leadership in weeks, not quarters.
It's not a fit when you only want advice: If you won't give decision rights, you'll pay for motion, not outcomes.
Expect traction in 30 to 90 days: A risk snapshot, priority plan, and visible fixes to the biggest gaps in your Information Security Program.
You should see fewer "unknowns" fast: Clear top risks, clear owners, and fewer surprises in audits and customer reviews.
Don't confuse interim with fractional: Interim is often higher-intensity and time-bound, while Fractional CISO support tends to be ongoing and part-time.
Avoid the most common hiring mistake: Picking a tool-first leader instead of a decision-first leader.
Set success metrics before day one: If you can't measure progress, you can't govern it.
If you want calm outcomes, you need calm authority. Interim works when you treat it like executive leadership, not a "security project."
What an Interim CISO actually does, and why it is different from consultants or IT leadership
An Interim CISO is a temporary security executive who takes real accountability for outcomes. That accountability is the difference. You're not buying a report, a slide deck, or a set of best practices. You're assigning decision-making power to someone who can run a prioritized security program under business constraints.
In practical terms, an Interim CISO:
Owns a short list of top risks and turns them into a funded cybersecurity strategy with scheduled work.
Makes tradeoffs visible, so leaders can decide without guessing.
Tightens incident readiness to strengthen your security posture, so your response is a capability, not a document.
Creates reporting that leads to decisions, not noise.
Consultants can be helpful, but they usually operate outside your governance chain. They recommend, then leave you to negotiate priorities across teams. A strong Interim CISO does the opposite. They walk into the messy middle, align leaders, and drive execution.
A Virtual CISO (vCISO) can also work, especially for lighter oversight. However, many vCISO models stay advisory and part-time. When you're in a gap or a crisis, "advisory" can feel like watching the house fill with smoke while everyone debates which extinguisher to buy.
IT leadership can't carry this alone either. Your CIO or IT manager has a full plate: uptime, delivery, budgets, and service levels. Security needs cross-functional authority that spans IT, legal, HR, finance, and the business. When you try to bolt security onto an already overloaded IT leader, you often get activity without closure.
If you want hands-on executive ownership, not just guidance, look at what hands-on, board-capable CISO leadership for hire looks like in practice. The value is simple: you stop hoping security will improve "when things slow down," because it rarely does.
The difference between interim, fractional, and full-time CISO leadership
Here's a plain-language comparison you can use to self-sort.
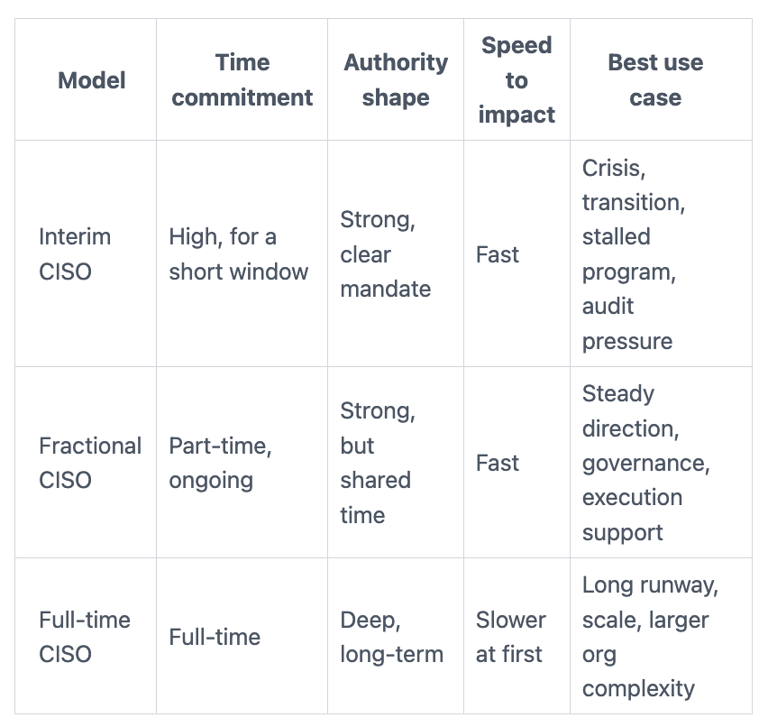
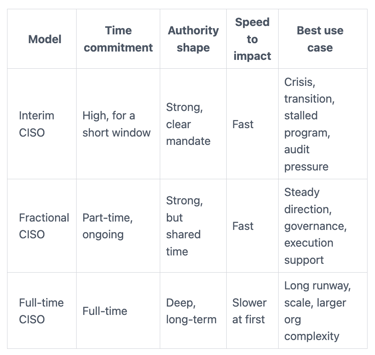
Cost is not just salary math. It's also time-to-impact, avoided losses, and avoided rework. If you make the wrong "quick hire," you can lose a year cleaning it up.
A simple rule of thumb helps: if you need stabilization and tough decisions now, go interim. If you need sustained part-time strategic guidance, go fractional. If you have a mature program and a long roadmap, hire full-time.
What good looks like in the first 30, 60, and 90 days
Good interim work is inspectable. You should be able to point to what changed.
First 30 days should feel like triage plus clarity:
A listening tour with IT, legal, finance, and the most exposed business owners.
A Cyber Maturity Assessment as a current-state risk snapshot in plain language (not a 70-page assessment).
Quick wins that reduce blast radius, for example tightening admin access, expanding MFA where it matters, and validating backup recovery.
By 60 days, you should see an operating rhythm:
Vulnerability management for patching and vulnerabilities focused on what's exposed and important.
Vendor risk triage that matches business impact, not paperwork volume.
A simple incident playbook, with a call tree that works after hours.
By 90 days, you should have confidence-building outputs:
A prioritized roadmap with owners, milestones, and realistic sequencing.
Board-ready reporting that highlights decisions, progress, and exceptions.
Signs an Interim CISO is the smartest security move right now
Some moments demand a leader, not another project. If several of these sound familiar, interim leadership often beats waiting for a perfect full-time hire.
You're under pressure to show control. That pressure might come from audits, cyber liability insurance providers, customers, or your own board. At the same time, the team can't name the top risks without debating dashboards. That's a leadership gap in risk management, not a tooling gap.
You also might be living with hidden fragility. Access is messy. Backups exist, but restores haven't been proven. Vendor connections, without proper third-party risk management, have grown quietly for years. Each of these issues is survivable until the day it isn't.
A practical test is this: can you explain your top three cyber risks in two minutes, including what you're doing next month to reduce them? If not, you're probably running on assumptions.
This is where board expectations matter. If you need stronger governance around incident response readiness and decision rights, this guidance on board-level incident oversight and readiness fits the kind of pressure directors face now. The goal is fewer surprises, not prettier decks.
You are in a high-stakes transition, and you need leadership before you can hire full-time
Transitions create openings attackers love, and auditors notice, too. You might be dealing with a CISO departure, M&A activity, rapid growth, a new regulatory demand, or a major audit finding. Cloud migrations without solid cloud security architecture and new product launches also widen exposure fast.
In these moments, your company needs someone who can:
Stabilize decisions, so teams stop improvising.
Set a plan the business can fund and execute.
Leave clean documentation and routines a future CISO can inherit.
Interim leadership works because it's time-bound and outcome-driven. You get a leader who can hold the pen on priorities, then hand off without drama.
You have tools and reports, but you do not have clear risk decisions or accountability
It's easy to confuse activity with progress. Tickets close. Scans run. Dashboards update. Yet the same risks keep coming back.
Outcomes look different:
Fewer privileged accounts through better identity and access management, and tighter controls over new ones.
Faster containment through improved threat detection when something goes wrong.
Shorter exposure windows on critical vulnerabilities.
Cleaner vendor access, with contracts that match your expectations.
These outcomes align with a zero trust framework. Decision rights sit at the center. Who can accept risk? Who can force a fix? Who can approve downtime for a security change? If those answers aren't clear, your security program becomes a negotiation.
Metrics can help, but only if they lead to decisions. This perspective on cyber metrics that build executive confidence is useful when you want reporting that shows value, not just volume.
How to hire an Interim CISO without wasting time, money, or credibility
An interim hire fails for predictable reasons. You bring someone in, but you don't give them authority. Or you ask for a strategy, yet you really need execution. Sometimes you let IT "own" the relationship, then wonder why board reporting never improves.
Start by defining the mandate in business terms with Governance Risk and Compliance in mind:
What must be true in 30 days?
What must be measurably better in 90 days?
Which Risk Management priorities could hurt revenue, trust, or uptime this quarter?
Next, decide how you'll govern the work. Weekly leadership checkpoints beat monthly steering committees. You want a steady cadence, clear owners, and fast escalation when tradeoffs get hard.
Finally, vet for judgment, not just credentials. A strong guide for that is how you vet a CISO in business terms. You're looking for someone who can make hard calls calmly, and explain them clearly.
A simple scorecard you can use to evaluate candidates
Use this as a quick filter in interviews:
Executive presence: You trust them in front of your board and customers.
Incident leadership: They've led real incidents, not just tabletop exercises.
Program discipline: They can run a NIST or ISO-aligned program without drowning teams in process.
Prioritization skill: They can cut scope and still reduce real risk.
Tradeoff comfort: They don't pretend everything is "critical."
Board communication: They can explain risk, trends, and decisions without jargon.
Team-building mindset: They strengthen your people instead of creating dependency.
Vendor independence: Strong Security Vendor Management skills mean they don't sound like a reseller.
Red flags are usually obvious. Watch for vague outcomes, tool-first pitches, and no references for high-pressure work.
How you set them up for success: mandate, reporting, and decision rights
Give your Interim CISO access to leaders and real data early. Limit gatekeeping. Make it clear who they report to, and what they can decide.
Also, set a lightweight reporting format that fits executives. You want top risks, what changed, what's stuck, and which decisions you need to make. If you want a board-friendly approach to Board Reporting, use guidance like CISO performance metrics that boards can actually use to keep oversight grounded in outcomes.
If you don't define decision rights, you'll replay the same debate every week, just with new slides.
What to do next: choose interim, fractional, or advisory support based on your gap
Choose interim when you need hands-on execution and accountability now. Choose fractional when you need steady leadership but not a full-time presence. Choose advisory support when the biggest gap is governance, decision-making, Strategic Guidance, or board communication.
If you need help sorting that quickly, consider engaging a CISO advisor for clear decisions and momentum. The goal is fit, not a trendy staffing model.
FAQs: Interim CISO questions leaders ask before they commit
How long do you typically need an Interim CISO?
Most interim roles run long enough to stabilize and set direction, often a few months. Your timeline depends on urgency such as regulatory compliance deadlines, team maturity, and whether you're also recruiting full-time.
How will an Interim CISO work with your CIO or IT leader?
They should operate as partners, not rivals. You'll want clear lines: IT owns operations, while the Interim CISO owns security risk decisions and the security program.
What deliverables should you expect?
Expect a ranked risk view, a 30 to 90-day plan, and evidence of executed improvements like business continuity enhancements. You should also get board-ready reporting and a clean handoff package.
How do you handle confidentiality and sensitive findings?
Set confidentiality expectations in writing. A professional Interim CISO limits access to need-to-know data for data protection and uses clear escalation paths for material issues.
How do you avoid dependence on one person?
Require documented decisions, repeatable routines like a security awareness program, and ownership assigned to internal leaders. Interim leadership should build capability, not create a single point of failure.
Can an Interim CISO improve board and committee reporting quickly?
Yes, if you agree on format and cadence early. For committees, it helps to align to risk committee cybersecurity reporting that includes penetration testing validation and specific needs like HIPAA compliance, so updates drive decisions instead of debates.
Conclusion
An Interim CISO is the smartest move when you need speed, accountability, and a plan your leadership team can defend. You're not trying to buy comfort. You're trying to reduce uncertainty and stop preventable failures, while keeping the business moving.
Write down your top three business risks tied to cyber, then decide what must change in 30 days. From there, choose the cybersecurity leadership model that matches the gap, not your org chart.
When the moment is high-stakes, having the right support matters. If you need a clear path for interim leadership support for high-stakes moments from a seasoned Chief Information Security Officer, start with a focused mandate and the decision rights to match.


