An IT Roadmap Template to Align Tech and Business Goals
Use this IT strategy and roadmap template to tie tech work to business goals, budgets, risk, and timelines, so leaders decide faster and trust grows.

If your leadership team feels like digital transformation work is nonstop but business goals aren't advancing, you're not alone. You may have projects, tickets, and "initiatives" everywhere, yet growth still feels harder than it should. Costs creep up, delivery slows, and risk conversations get tense.
An IT roadmap is a simple, repeatable document that shows what you're building, why it matters to the business, when it will land, what it will cost, and defines your IT vision.
In this post, you'll walk away with a practical IT strategy and roadmap that connects goals, risk, budgets, and delivery. Just as important, you'll see how to use the roadmap as a communication tool, so your CEO, board, and committees can provide oversight without getting pulled into tool debates. When your roadmap is clear, trust rises, and decisions get faster.
Key takeaways you can use right away
Start with 3 business goals, then map each tech bet to one goal for strategic alignment and one measurable outcome.
Assign an executive owner per goal, so priorities don't drift when delivery gets hard.
Write down decision rights early (what leaders must decide, what IT can design).
Use a simple 1 to 5 scoring model to rank initiatives in a cross-functional meeting.
Build cybersecurity and resilience into every IT infrastructure workstream, not a separate "security plan."
Track board-inspectable performance metrics (trend, target, scope), such as key performance indicators, not tool activity or vanity counts.
Update on a steady cadence (monthly ops review, quarterly steering), then re-plan only on triggers.
Start with business goals and decision rights, or your roadmap will not stick
A roadmap fails for one main reason; without strategic alignment, it tries to solve technology before you agree on business outcomes. When leaders don't share the "why," every project becomes a debate. Teams then optimize for local wins, not enterprise results.
Start by using a SWOT analysis to choose three to five business goals that matter over the next 12 to 18 months. Keep them plain. Think growth, cost control, trust, speed, and compliance. These business goals represent your strategic objectives as long-term targets. Next, name an executive owner for each goal (not "IT" as a group). Then define the few decisions the business must make up front:
Priority order when goals conflict
Risk tolerance as part of risk management (downtime, data exposure, vendor dependency)
Funding model (run, grow, transform)
What must ship this quarter, and what can wait
After that, IT can conduct a gap analysis to design options that fit those decisions and move from the current state to the desired outcomes. This is where your IT strategy and roadmap becomes a decision tool, not a status artifact.
A quick goal-to-outcome mapping can look like this:
Grow enterprise revenue: reduce security questionnaire cycle time from 15 days to 5.
Reduce operating cost: cut duplicate SaaS spend by 12 percent through consolidation.
Improve delivery speed: reduce release rollback rate from 8 percent to 3 percent.
Strengthen trust: meet defined recovery targets for your top three critical services.
Tighten compliance: reduce high-severity audit findings from 10 to 3 by next audit.
When you align technology choices to CEO priorities, it helps to frame the tradeoffs in business language, not architecture diagrams. A useful reference point is a cybersecurity strategy advisor for CEOs perspective, because it ties priorities, risk limits, and reporting into one operating approach.
Turn strategy into measurable outcomes (not vague "modernization")
"Modernize the stack" is a slogan, not an outcome. Your roadmap needs testable statements you can check within a quarter or two.
Use outcome language like:
Reduce customer onboarding time from X days to Y days
Increase uptime to Z percent for the revenue-critical platform
Reduce time to remove access for leavers from X days to Y hours
Pass audits with fewer high-severity findings, and close them within X days
Restore critical systems within X hours during a test, not a real crisis
If you can't test it soon, it's probably too big, or too vague.
Set risk tolerance and escalation paths before you pick tools
Risk tolerance is how much pain you're willing to accept before you spend or slow down. It shows up in cloud choices, third-party use, data access, and how tightly you control change.
For example, if you can't tolerate downtime during peak revenue weeks, you'll fund redundancy and recovery testing. If you can't tolerate sensitive data leaving your environment, you'll set stricter vendor and access rules.
Also, decide escalation paths now. A simple rule works: operational issues stay with management, material risk choices go to the CEO and risk committee, and board-level escalation happens when customer trust, financial impact, or disclosure thresholds are in play. If you want a board-ready model for governance and decision rights, anchor it in cybersecurity governance for boards.
Use this IT roadmap template structure to connect work, money, and timelines
A roadmap earns its keep when it connects four things in one view: outcomes, work, time, and capacity. You can copy the structure below into a slide deck or a short document. Keep it tight. Most leaders will read what fits on one page, then ask for details only on the top items.
Here's the implementation roadmap template structure to use.
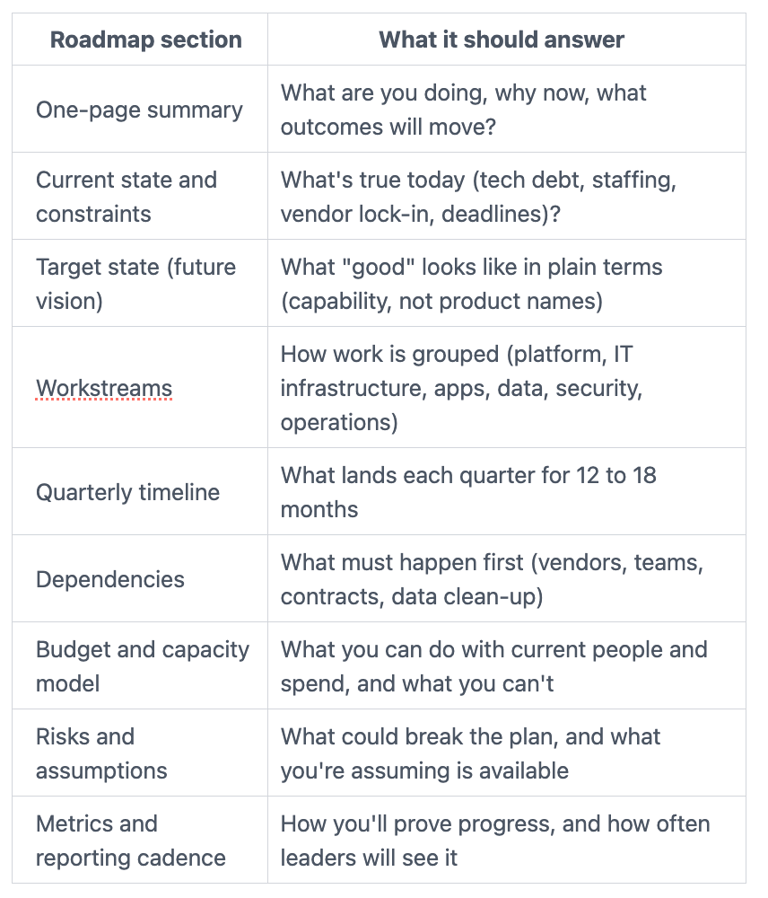
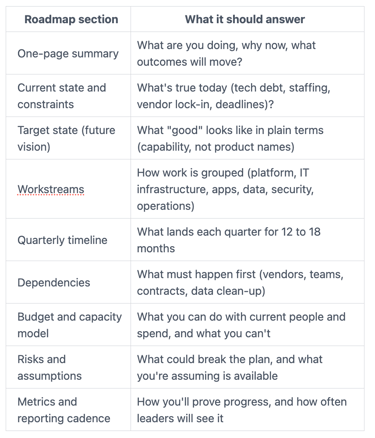
A practical time horizon for your IT roadmap is 12 to 18 months with quarterly detail, then a lighter view out to 24 months. The farther you go, the more you should speak in outcomes and capability, not committed delivery dates.
A few rules keep the template usable:
First, describe work as "capabilities delivered," not "tools installed." Second, show capacity honestly. If you only have bandwidth for three major efforts, say so. Third, treat security like a built-in requirement, similar to finance controls, not an optional add-on.
When you introduce reporting, don't default to technical dashboards. Use metrics leaders can understand and inspect. The approach in the hidden value of cyber metrics is a helpful north star, because it focuses on exposure, readiness, and trend lines that connect to business outcomes.
Finally, match reporting to how governance actually works in your organization. Your roadmap update should fit the rhythm of executive staff meetings, risk committee agendas, and board packets. If your committees want decision-ready reporting instead of "all green" comfort, align your format to risk committee cybersecurity reporting expectations.
A simple scoring model for prioritizing initiatives (value, risk, effort)
Prioritization breaks when the loudest voice wins. This scoring model, as a form of project portfolio management, won't solve politics, but it forces a cleaner conversation around technology investments.
Score each initiative from 1 to 5:
Business value (consider ROI)
Risk reduction
Customer impact
Effort (higher score means harder)
Time-to-value (higher score means faster)
Then rank using a simple rule: prioritize high value, high risk reduction, high customer impact, with low effort and fast time-to-value. Do the scoring in a cross-functional meeting, with finance, product, ops, and security in the room. That's how you improve resource allocation and reduce "pet projects."
A quick example: phishing-resistant MFA for admins can score high even if it's not flashy. It protects revenue, reduces outage risk, and lowers the chance of a public incident that damages trust.
Build security and resilience into every workstream, not as a separate lane
Security work fails when it lives in a side plan. Instead, embed baseline controls into platform and app projects as "definition of done."
In practice, that means:
Identity belongs in platform and workforce enablement, not just "security." Backups and recovery belong in operations and data work, not just "infra." Logging belongs in every service build, not an end-of-year project. Vendor risk belongs in procurement flow, not a once-a-year questionnaire scramble.
Also, treat incident readiness as part of delivery. If you ship a new system, you should know how you'll detect issues, who gets paged, and how you'll restore service. Boards increasingly expect evidence of this discipline. If you need a clear view of what oversight looks like without running the response, use incident response oversight as a guide for roles, proof, and cadence.
If your roadmap can't answer "what happens when this fails," you don't have a plan yet, you have a wish.
Make the roadmap governable: clear updates, simple metrics, and a plan for surprises
An IT roadmap is only useful if it stays alive. That takes a governance rhythm that fits how leaders work.
Set three layers of IT governance:
Monthly operating review: you and stakeholders check delivery, capacity, budget burn, and top risks. Quarterly steering: you confirm priorities, approve tradeoffs, and adjust scope. Board-level oversight: you focus on top enterprise risks, readiness, and material changes.
Then decide what triggers a re-plan. Keep the list short, or you'll constantly churn. Common triggers include a major incident, an acquisition, a funding shift, a regulatory change, or a strategic pivot in strategic planning that changes the "critical path" systems.
When change hits, communicate tradeoffs in plain language. Say what you will stop, what you will delay, and what you will accelerate. Avoid the trap of promising everything will still happen "just a bit later." Your team hears that as "work weekends."
For oversight, pick a stable set of metrics leaders can inspect over time. If you want a board-friendly way to define and evaluate those measures, anchor on oversight metrics that leaders can inspect.
What to report each month so leaders trust the IT roadmap
Use the same short format every month. Consistency builds confidence faster than extra detail.
Include:
Delivery status by quarter (on track, at risk, off track)
Budget burn versus plan, plus forecast
Top five risks, with owners and due dates
Key incidents and lessons learned (including near misses)
Control coverage on critical assets (identity, backup restore tests, logging)
Vendor issues that affect uptime, data, or delivery dates
Outcomes achieved, like gains in operational efficiency and automation (the measurable statements you committed to)
Keep slides short, and keep labels stable. Changing definitions breaks trust.
When you should bring in interim or fractional leadership
Sometimes the roadmap stalls because nobody can make the hard calls across teams. Other times, you have a gap in CISO or CIO leadership, and execution drifts.
Common triggers include a stalled program, new compliance pressure, a ransomware wake-up call, M&A integration, or leadership turnover. In those moments, fractional support can help you build a defensible plan quickly, then hand it off cleanly. If that's your situation, consider fractional CISO support for building a defensible IT roadmap, especially when security, governance, and board reporting need to tighten at the same time.
FAQs about building an IT strategy and roadmap template
How long should an IT roadmap be?
Aim for 12 to 18 months with quarterly detail. Keep a lighter view out to 24 months for direction.
Who owns the IT roadmap?
You do, as a leadership team. IT owns the draft and delivery plan, but business leaders must own priorities and risk choices.
How often should you update it?
Review it monthly, and steer it quarterly. Re-plan only when a clear trigger hits, like an acquisition or major incident.
How do you balance quick wins versus big bets?
Ship quick wins that remove friction or reduce exposure fast, but don't crowd out foundational work. Use scoring to protect the "unsexy" items that prevent outages.
How do you incorporate emerging technologies like artificial intelligence?
Scan for fits with business goals each quarter, run low-risk pilots, and map longer-term adoption to stay ahead without overcommitting resources.
What if your data is messy (inventory, costs, or dependencies)?
Don't wait for perfect data, especially in complex areas like cloud computing. Start with what you know, label assumptions, then improve data quality as a workstream.
How do you include cybersecurity without fear-driven language?
Tie security to outcomes like uptime, recovery time, customer trust, and audit stability. Speak in dollars, hours, and decisions, not attacker headlines.
Conclusion
When you use an IT strategy and roadmap template the right way, you stop managing a pile of projects. Instead, you create alignment with your digital strategy, simpler decisions, clearer risk ownership, and faster delivery that leaders can see and trust. The roadmap becomes a shared map, not an IT artifact.
Your next steps are straightforward: draft the one-page summary, score the top initiatives with your stakeholders, then set the reporting cadence and stick to it. After that, improve the plan through steady strategic planning, not constant churn.
If you want a senior, business-first review of your roadmap and the metrics you plan to report, consider engaging a CISO advisor to review your roadmap and metrics. That outside clarity often saves you a quarter of rework while optimizing technology investments to meet strategic objectives.


