How to Hire an Interim CISO: A Step-by-Step Playbook
Hiring An Interim CISO? Use this step-by-step playbook to stabilize risk in 30 to 90 days, set decision rights, metrics, and a clean exit.


When cybersecurity leadership slips, the business feels it fast. Maybe you just had a breach. Maybe an audit report landed hard. Maybe your CISO (Chief Information Security Officer) resigned, or a merger turned your risk management picture into fog. Either way, you still have customers to serve, revenue to protect, and a board that wants clear answers.
That's what Hiring an Interim CISO is for. You're not buying a long strategy deck. You're buying time, clarity, and steady execution in the next 30 to 90 days. A strong interim CISO should reduce uncertainty, tighten the highest-risk exposures in information security, and leave you with a plan leaders can inspect.
This playbook helps you move quickly without wasting budget or trust. You'll decide if interim is the right model, write a one-page brief that attracts the right candidates, vet leadership under pressure, then onboard with measurable outcomes and a clean exit plan.
Key takeaways you can use today
Decide "interim" when you need fast risk stabilization via gap analysis and executive decision-making, not more security strategy.
Write a one-page, outcomes-based brief so candidates self-select for your real needs.
Screen for board-ready communication, your interim CISO must translate risk into business impact.
Ask every candidate for a plain-language 30-60-90 day plan, then test it against your constraints.
Pick a small set of metrics leaders can inspect weekly for security operations, and keep them stable.
Set governance decision rights on day 1, because unclear authority creates delays and "paper security."
Use references to confirm execution under pressure, not just technical depth.
Avoid common traps like tool-first thinking, vague "maturity" talk, and unclear ownership.
Step 1: Decide if interim CISO leadership is the right fit for your moment
In today's evolving threat landscape, interim leadership fits when you need an executive who can walk in, take control, and make decisions that stick. You usually choose an Interim CISO because the timeline is short and the risk is real. A permanent CISO search can take months, and your risk doesn't pause.
Interim is often the best option when:
You're recovering from an incident and need calm command and follow-through to bolster your security posture.
You have turnover, and security ownership is scattered across IT and compliance.
An audit or regulatory compliance finding needs remediation with clear accountability.
You're in the midst of digital transformation, and security is slowing delivery because priorities are unclear.
You're navigating M&A activity and need a single risk view across both environments.
An Interim CISO is also different from a consultant. A consultant may assess and recommend. An interim leader owns outcomes, leads people, and makes tradeoffs in real time. That means they run the security operating rhythm, drive cross-functional alignment, and put their name on the plan.
If you want a practical view of what "stabilize risk in 30 to 90 days" looks like, start with this guide on interim security executive help.
Fast self-check: what problem are you actually trying to solve?
Use these prompts to name your real objective:
Are you trying to restore board confidence after bad news?
Do you need ransomware readiness that goes beyond a document?
Are risk decisions stuck because no one can say "yes" or "no"?
Do you have tool sprawl, with no clear owners or outcomes?
Is incident response unclear, untested, or dependent on one person?
Are audit findings repeating because evidence and ownership are weak?
Are access controls messy (stale admins, weak offboarding, unclear MFA)?
Are vendor reviews blocking deals because triage is missing?
Do you lack a plain-language list of top risks and business impact?
If you can't name the outcome in one sentence, pause. You're not ready to hire yet.
Pick the right engagement model: interim vs fractional vs permanent
This quick comparison keeps you honest about urgency and bandwidth.
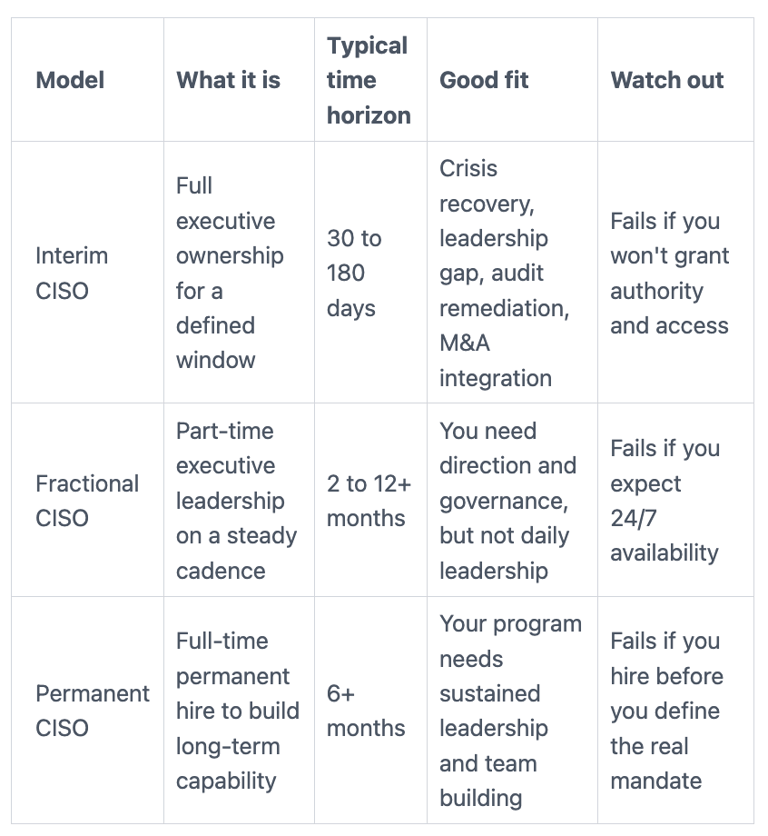
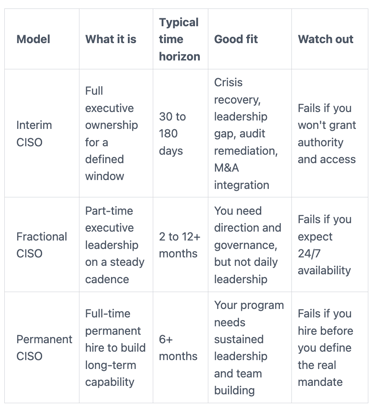
When you need ongoing senior guidance without a full-time hire, consider fractional CISO support as a longer, steadier model.
Step 2: Write a one-page interim CISO brief that drives the right candidates
When you're under pressure, it's tempting to post a generic role description. That attracts generic candidates. Your goal is a one-page brief that turns chaos into a clear target and secures executive buy-in, so the right Interim CISO candidates can say, "Yes, I've done this, and here's how."
Keep it tight, copyable, and business-first. Use headings like these:
Context: What changed, and why now?
Top risks (current state): Your best view from a risk assessment of what can hurt revenue, operations, or trust.
Outcomes (30 to 90 days): What must be measurably true after the engagement.
Decision rights: What the interim CISO can decide, what they co-decide, what they advise on.
Stakeholders: CEO, GC, CFO, CIO/CTO, audit, risk committee, key business owners.
Constraints: Budget reality, change freeze windows, limited staff, vendor contracts, deadlines.
Success measures: A small set of metrics and proof points leaders can inspect.
Write it in the language your CEO and board use, aligned with business objectives. Avoid tool lists. Tools are inputs, outcomes are what you're buying. If you want help aligning that one-pager to the business, this perspective on aligning security strategy to CEO goals is a useful reference.
Define outcomes for the first 30 to 90 days (not a list of tasks)
Here are outcome examples you can adapt:
Incident response works in practice, with roles, call tree, and one tabletop completed.
Your top 5 to 10 cyber risks are published in plain language, with owners and next decisions.
High-risk exposure is reduced (for example, privileged access tightened, stale accounts removed).
Backup recovery is proven for critical systems, with evidence you can show leaders.
Vendor risk triage exists, so you spend time on the suppliers that matter most.
Security priorities reset into a realistic roadmap with sequencing and cost ranges.
Board reporting shifts from noise to decisions, with clear asks and status.
Set decision rights so the interim leader can actually lead
Decision rights are a control. Without them, everything slows down, and you end up with "paper security" that looks busy but changes nothing.
Define three lanes:
Owns: Security policy guardrails, incident severity and escalation, security exceptions process, risk register management, security priorities.
Shared: Go-live approvals for high-risk systems, budget tradeoffs, vendor contract security terms, major architecture changes.
Advises: Risk acceptance (final sign-off by the accountable business leader), public statements (owned by execs and legal), cyber insurance claims steps.
Write down escalation paths. Also name who can approve downtime tradeoffs during a crisis. Speed without authority is just frustration.
Step 3: Source, vet, and hire your interim CISO with confidence
Move fast, but keep your standards. Interim hiring works best as a short, disciplined funnel.
Start with where to look: trusted executive networks, referrals from the board of directors, specialist interim firms, and advisors who routinely operate at CEO and board level. Then run a two-step screen: a 20-minute call to confirm fit and communication, followed by one deep interview focused on judgment and execution.
During screening, listen for "clean language." A strong interim Chief Information Security Officer explains tradeoffs without drama. They tie risk to downtime, revenue, legal exposure, and customer trust. They also describe how they'll work with IT, legal, and finance, because that's where decisions get real.
If you want a CEO-centered lens for your process, use this guide on how a CEO can vet a CISO. For a tighter interview structure, pull from these CISO interview questions.
What to look for in an interim CISO (signals, not buzzwords)
Strong signals for an Interim CISO:
They translate risk into dollars, downtime, and decision options.
They've led through real incidents (including as a virtual CISO) and can describe what mattered most.
They simplify priorities quickly and can name "stop-doing" work.
They partner well with GC, finance, and audit without hiding behind jargon.
They're comfortable briefing the board, including when the news is bad.
They can run governance without slowing delivery.
They coach your team and leave it stronger than they found it.
They can work within NIST or ISO, but stay practical.
They make hard tradeoffs and document risk acceptance clearly.
Red flags for an Interim CISO:
Tool-first answers, with little talk of outcomes.
Vague "maturity" language that never turns into decisions.
They avoid ownership (everything is "advisory").
They can't explain metrics in plain language.
They blame the organization instead of adapting to constraints.
If a candidate can't explain their first 30 days without acronyms, you'll struggle to get executive alignment.
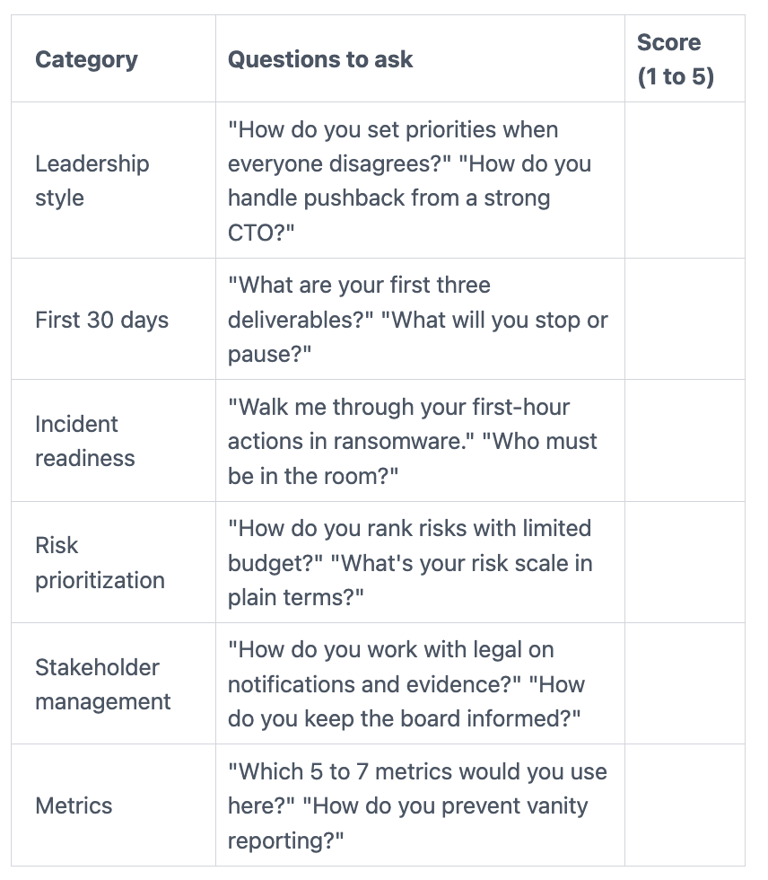
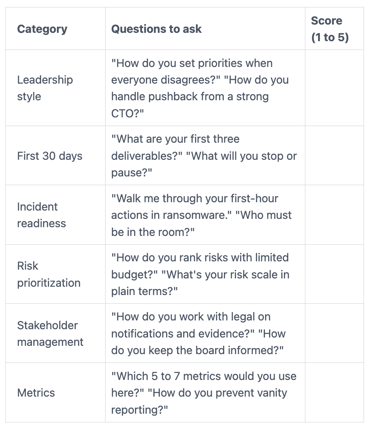
A simple interview scorecard you can use in one meeting
Use this scorecard in a single 60 to 75-minute interview, then score each area from 1 to 5. Compare scores to your one-page brief, not to charisma.
Step 4: Onboard fast, measure progress, and plan your exit from interim mode
Week one sets the tone. Treat onboarding like you would for any executive, because speed comes from access, context, and trust.
Set a simple cadence right away:
A short weekly exec check-in (30 minutes) for decisions and blockers.
A bi-weekly working session with IT and security leads for execution.
A monthly board or committee-ready update that highlights changes, risks, and decisions needed.
Your reporting should match oversight expectations to sustain program momentum. This guide on CISO performance metrics for board oversight can help you choose what leaders can inspect. For incident response, align early on board incident response oversight, including who communicates what, and when.
Also plan your exit up front with a clear transition plan. Decide what "done" means. Otherwise, you drift into a forever-interim pattern where nobody commits to the long-term model.
Your first-week onboarding checklist (access, people, and priorities)
Keep it practical:
Admin access paths (with logging), MFA status, and identity provider basics
Current incident response tools and contacts (including outside counsel if used)
Risk register (even if messy), audit reports, and open findings
Incident history and any post-incident reports
Cyber insurance policy info and notification requirements
List of critical apps, data stores, key data flows, and technical infrastructure
Top security projects in flight and who owns them
Key vendors with privileged access
Names of the people who can say "yes" on risk, downtime, and spend
A 30-60-90 day plan that leaders can inspect
Your interim CISO should publish a simple plan with proof points.
30 days: Triage and stabilize. Publish top risks in business terms, confirm decision rights, and close the easiest high-impact gaps.
60 days: Build operating rhythm. Run a tabletop, tighten access and backups for crown jewels to bolster cyber resilience, and implement vendor triage.
90 days: Deliver a board-ready roadmap. Show what changed, what's still exposed, and the cost and sequence to improve.
Proof points leaders can inspect:
One-page executive risk summary with owners
Tabletop completed, with follow-ups assigned
Backup restore test evidence for critical systems
Reduced privileged access sprawl (counts and approvals)
Third-party tiering and a decision path for exceptions
A prioritized roadmap with milestones and budget ranges
FAQs about Hiring An Interim CISO
How fast can you hire an interim CISO?
If you already have a one-page brief and decision rights ready, you can often identify Interim CISO candidates within days. The slow part is usually internal alignment, not sourcing.
How long does an interim engagement typically last?
Many engagements run 60 to 120 days, then transition to fractional CISO support. The right length depends on urgency, staffing, and deadlines like audits or M&A close.
What does an interim CISO cost?
Rates vary by scope, availability, and whether you need on-site presence. Cost also changes based on crisis conditions, travel, and how much execution you expect versus oversight. Focus on outcomes and authority first, then match the commercial model to that reality.
Can an interim CISO work with your MSP or MSSP?
Yes, and they should. Your Interim CISO sets priorities, clarifies roles, and holds providers accountable to measurable service outcomes.
What authority do you need to give them?
At minimum, they need access to the right data, the ability to set priorities, and a clear escalation path for urgent decisions. Without that, you'll pay for advice you can't act on.
How do you handle confidentiality and conflicts?
Use a strong NDA, confirm conflict checks, and limit sensitive access to what's required. You can also require that notes and artifacts remain your property.
When do you go permanent?
Go permanent when the program needs sustained leadership, team building, and long-term ownership of budgets and strategy. If you need an experienced Chief Information Security Officer for hire to bridge that transition to a permanent hire, make the handoff plan part of the engagement.
Conclusion
Hiring an Interim CISO works when you treat it like an executive decision, not a staff fill. First, decide if interim matches your urgency and internal capacity. Next, write a one-page outcomes brief that makes priorities clear. Then vet for judgment, communication, and real execution. Finally, onboard fast with visible proof points, stable metrics, and a defined exit.
You're buying time, clarity, and measurable progress in cybersecurity leadership, not security theater. This week, write your one-page brief and set decision rights in writing. After that, you'll interview better and move faster with fewer surprises while establishing effective governance.
If you want help shaping the brief, vetting candidates, or setting board-ready metrics for information security, consider engaging a CISO advisor to steady decisions while you stabilize risk management.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
