Third-Party Risk Reporting to the Board: 7 Ways to Make Reports Board-Friendly
Make third-party risk reporting to the board clear and action-ready, use 7 tips, scorecards, trends, thresholds, and next steps leaders can decide on.

You can do solid vendor risk work within your Risk Management efforts and still lose the board. It happens when your report reads like an Information Security audit file, not a decision tool. It's too long, too technical, or it never says what the business should do next.
Picture a critical SaaS vendor that runs your customer support, or a payment processor that touches revenue every minute. If that vendor fails, your ops stall, customers notice, and regulators may care. In that moment, the board won't ask about your Cybersecurity Program Assessment or how many controls you reviewed. They'll ask, "How bad can this get, how fast, and what are you doing about it?"
That's the point of third-party risk reporting to the board. You're not trying to prove you worked hard. You're trying to make risk easy to see, easy to compare, and easy to act on.
Below are seven practical ways to make your reporting clearer, faster to scan, and more decision-ready.
Key takeaways you can use in your next board pack
Write in plain language, because directors need choices, not security controls IDs.
Translate vendor gaps into business impact, such as downtime, data exposure, or regulatory compliance fines.
Use a simple heat map or scorecard for risk assessment so risk is scannable in three minutes.
Show trends and concentration risk, because movement matters more than snapshots.
Set decision thresholds so you don't debate every red flag in real time.
Separate "must fix" from "good to improve" so priorities are obvious.
End with actions, owners, and a steady oversight rhythm the board can inspect.
Start with what the board needs to decide, then work backward
A board-friendly third-party risk report starts with one question: What decision do you need from the board or a board committee? If you can't answer that in one sentence, you'll drift into compliance storytelling.
So, define decision rights upfront. For example, the board (or risk committee) might own key Risk Management decisions like risk appetite for critical vendors, approval of high-risk exceptions, and tolerance for downtime in core services. Management owns the day-to-day vendor process, but you should still surface the moments where escalation is required due to impacts on Security Posture.
This is where governance expectations matter. If you want a clean model for what "good" looks like at the board level, align your reporting to a clear Governance Risk and Compliance framework like cybersecurity governance for boards. When governance is clear, your report stops being a debate about details and becomes a review of choices.
To work backward, start your report with:
The top vendor risks that could change business outcomes this quarter.
The specific decision you're asking for (approve, fund, accept, pause, or exit).
The consequences of doing nothing.
Then, and only then, include supporting evidence. Your goal is not to hide complexity. Your goal is to keep complexity out of the decision path.
If a board can't tell what you want them to decide, your report becomes background noise.
Turn vendor findings into business impact, not control language
Most vendor assessments produce "findings," but boards hear "noise." You fix that by using Gap Analysis to translate control gaps into outcomes.
Instead of "Vendor lacks MFA for admin access," say, "A compromised admin account could expose customer data and disrupt operations." The finding is still true, but now it's decision-ready.
Use a simple mapping template so every issue lands the same way. One short table keeps you consistent and helps directors compare risks, including Operational Risk.
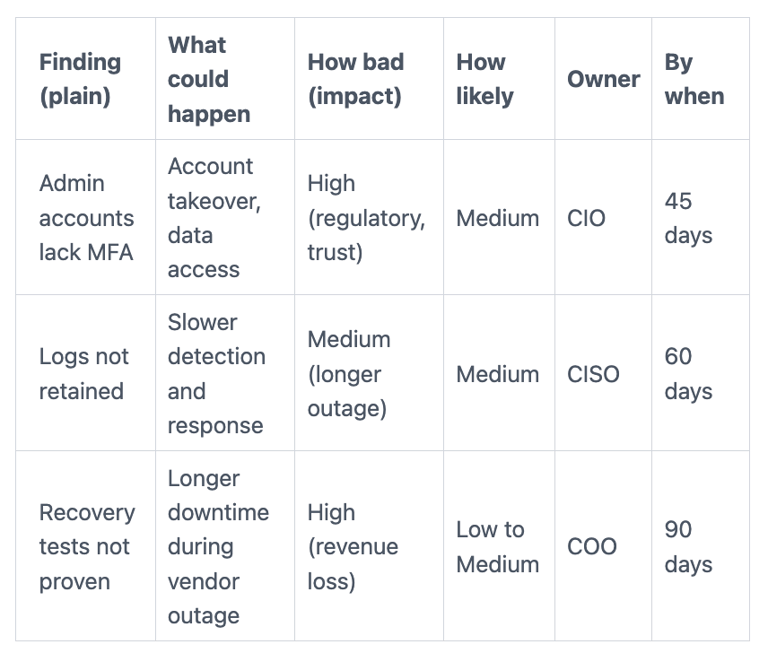
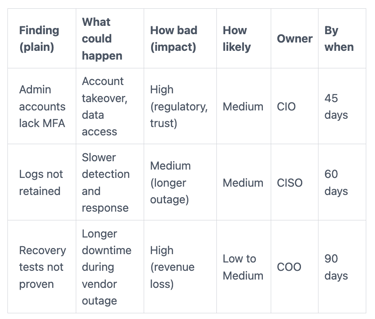
The takeaway: you're not changing the facts, you're changing the language. Boards fund outcomes. They don't fund control checklists.
Define decision thresholds so you are not debating every red flag
Without thresholds, every red issue becomes a meeting. That slows down onboarding, renewals, and remediation. It also trains your team to argue instead of decide.
Set clear thresholds that trigger escalation. Tie them to business criticality, not to how scary the security wording sounds. Good threshold inputs include: critical service dependency, sensitive data types, production access, use of sub-processors, and concentration risk (too much dependence on one provider).
Here's a simple way to structure it:
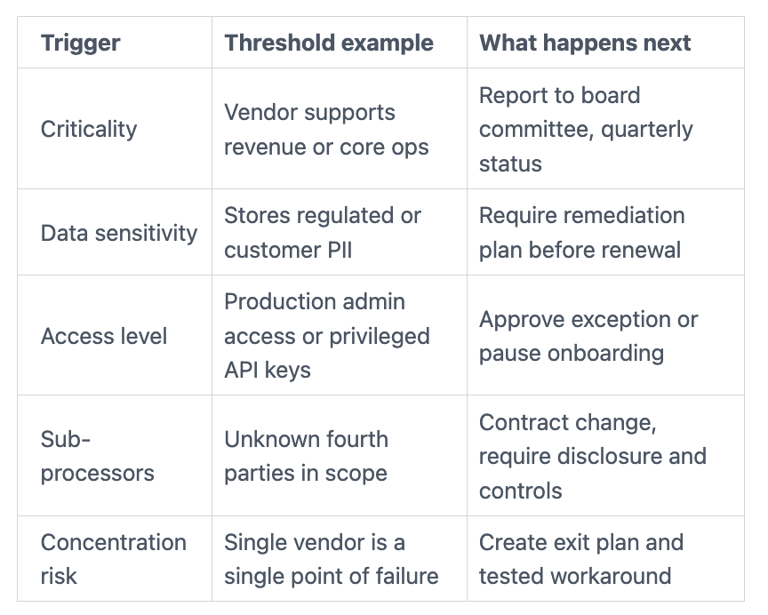
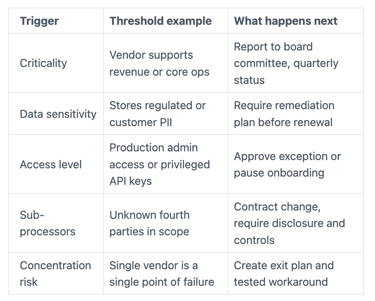
When thresholds are defined, your board moves faster because the rules are pre-agreed. You also reduce "surprise escalations," which is where trust tends to break.
Make the risk easy to scan in 3 minutes, then give depth for follow-up
Boards read your report the way people scan a weather forecast. They want the headline first, then the details only if the storm is real.
So, build your report in layers:
A one-page summary for decisions and changes since last time.
A visual snapshot using an Assessment Tool (heat map or scorecard) that shows where attention is needed.
A short appendix for those who want depth, including control details like Vulnerability Scanning.
Also, assume directors will ask sharper questions when the report is clear. It helps to come prepared with a small set of prompts, like the audit committee questions on third-party cyber risks, so your meeting ends with actions, not vague comfort.
Use a one-page scorecard for your top vendors, with consistent ratings
A scorecard works because it's familiar. It feels like finance reporting. It also forces you to standardize how you rate vendors.
Keep the rating scale simple, ideally 3 to 5 levels (for example: Low, Moderate, High, Critical). Don't mix frameworks like the NIST Cybersecurity Framework or ISO 27001 without explaining the mapping. Otherwise, you'll spend the meeting debating definitions.
A strong one-page layout includes:
Vendor name and service provided
Service criticality (to revenue, ops, or customer promise)
Data type (PII, financial, health, IP for Data Security)
Access level (none, limited, privileged)
Inherent Risk (before controls)
Residual Risk (after controls and compensating steps)
Top 1 to 3 gaps (plain language)
Open actions (owner, due date, status)
Renewal date (so timing is visible)
The board doesn't need every vendor. Start with the top 10 to 20 by business impact. If your list is longer, you're not ranking risk, you're counting it.
Show trends and concentration risk, not just point-in-time scores
A snapshot can look fine while risk quietly grows. Boards think in movement, because that's how business works. Are you getting safer, or just staying busy?
Add two or three trends that show whether exposure is rising:
Open critical vendor issues over time (three to four quarters is enough)
Vendors past due on remediation commitments
Critical vendor renewals in the next 90 days (renewal pressure drives bad decisions)
Exceptions granted and still open (especially if they never expire)
Then add concentration risk. If one cloud, one identity provider, or one managed service partner can stop the business, say that plainly. You don't need drama. You need visibility, plus a mitigation plan the board can inspect.
A simple way to phrase it: "We rely on Vendor X for Y percent of customer-facing uptime. Our fallback plan is Z. It is tested (or not tested)."
Separate "must fix" from "good to improve" so priorities are obvious
Many vendor reports fail because everything is a finding. When everything matters, nothing stands out.
Use a rule of thumb that's easy to defend:
Must fix before go-live: blocks onboarding
Must fix before renewal: blocks contract extension
Fix in planned cycle: scheduled remediation with proof milestones
Monitor: track, but don't burn time in the board meeting
This reduces noise and makes your stance clear. It also protects relationships with procurement and business owners, because you're not "failing" vendors over minor gaps.
Keep detailed control lists in the appendix. The main deck should show decisions, exposure, and dates.
Show your plan, your owners, and your oversight rhythm
A board-friendly report doesn't end with risk. It ends with execution.
That means you show the Roadmap to reduce exposure, who owns it, and how you will track progress. It also means you report on a cadence that matches how the business changes, guided by Policies and Procedures, not how audits schedule work.
If you want a model for a steady committee rhythm that avoids all-green dashboards, use a structure like risk committee reporting on third-party cyber exposures. The goal is simple: keep reporting honest, consistent, and tied to decisions.
Make every board report end with clear actions, dates, and who owns them
Every board pack should close with a short action list. Not a long backlog, just the actions that change risk.
Focus on "board-level" actions, such as:
Contract changes (incident notice timelines, audit rights, sub-processor disclosure)
Added monitoring of Security Capabilities (access reviews, log access, assurance updates)
Exit plans for critical vendors (with realistic timelines)
Recovery testing (prove you can operate through a vendor outage)
Segmentation or access gating (reduce blast radius)
Onboarding gates (no go-live until must-fix items close)
Define what "done" means. "Vendor committed to fix" is not done. "Evidence received and validated" is done.
Assign accountability to an executive who can move things. If ownership sits in a shared inbox, it won't close.
Report like a program, not a pile of vendors
Boards trust programs because programs have rhythm, scope, and measurable progress that reflect Security Program Maturity. A pile of vendor reviews feels endless and random.
Use a cadence that fits how third-party risk actually behaves:
Quarterly board view: top vendor risks, trends, decisions needed
Monthly executive view: Information Security remediation progress, renewals, exceptions
Event-driven updates: vendor incident, major renewal, new critical vendor, acquisition
Track a small set of program metrics over time, including Internal Controls effectiveness:
Count of critical vendors (and what changed)
Percent assessed by criticality tier
Percent with open high issues
Remediation timeliness (SLA performance)
Exceptions granted, with expiration dates
When you report this way, you're showing control of the system, not just activity inside it.
FAQs boards and CEOs ask about third-party risk reporting
How many vendors should be in the board report?
Only the ones that can change business outcomes, such as those affecting FISMA compliance or your Authorization to Operate, usually your top 10 to 20.
What if a vendor refuses to remediate a major gap?
You either negotiate contract terms, add compensating controls, or plan an exit. Put the choice on the page, especially for gaps uncovered by Penetration Testing.
Should you show a heat map even if it looks "worse" this quarter?
Yes, because honest trends build trust. Also, "worse" can mean visibility into Risk Exposure improved.
How do you handle vendor incidents in board reporting?
Treat vendor breaches from Cyber Threats as your incident until proven otherwise, and follow a clear model for board questions on third-party incident response.
What does "good" look like for remediation timing?
It looks like predictable SLAs by severity to ensure Cybersecurity Preparedness, with exceptions that expire and get re-approved.
Conclusion
When you make third-party risk reports board-friendly, you turn vendor noise into decision-ready oversight. Start with the decision, translate findings into business impact, and set thresholds that speed up escalation. Then make it scannable, show trends, separate must-fix from nice-to-have, and end with owners and dates.
Your next board pack can feel lighter and still be more honest. That's the real win: clearer decisions, fewer surprises, and stronger trust when a vendor becomes the headline; practices that align with the FFIEC IT Examination Handbook and whose success you can measure using CMMI.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
