You Can't Govern What You Haven't Mapped.
Map your tech stack first so you can spot Shadow AI Threat risks, assign ownership, and govern with clear answers before gaps become crises.


You try to set policies and oversight without knowing your full tech stack. Hidden tools and processes create gaps. You miss shadow AI threats from teams using unapproved apps. This leads to data leaks, fines, regulatory scrutiny, lost trust, and stalled growth.
Growth adds strain. AI moves fast. Vendors multiply risks. Without a map, you govern guesses. Incidents surprise you. Costs rise. Boards face questions they can't answer.
Map assets, risks, processes, and people first. Then govern with clear sight. You spot issues early. Ownership sharpens. Decisions speed up. Start simple. Inventory critical tech and AI use. Assign owners. Update often. This turns blind spots into control.
Key Takeaways
Map before you govern to spot shadow AI threats early.
Unmapped risks turn small issues into crises.
Clear mapping sets ownership and decision rights.
Begin with high-impact areas like AI tools and vendors.
Regular updates build resilience against surprises.
Strong maps improve board reporting and trust.
Why Unmapped Technology Creates Leadership Blind Spots
You face growth strain and cyber incidents now. AI speeds past oversight. Vendors add hidden risks. Board accountability rises. Unmapped tech blurs reporting. Ownership fades. Surprises hit during audits or transitions.
Teams use tools outside view. A hidden AI app leaks data. Compliance gaps emerge. Costs climb. Trust erodes. Decisions slow. You react, not lead.
For example, finance runs an unapproved AI model on customer data. IT misses it. A breach exposes PII. Fines follow. You learn too late.
This matters because unmapped areas weaken your posture. Shadow AI threats grow unchecked. You need visibility to set real appetite. Check how boards set technology risk appetite for thresholds that work.
The Shadow AI Threat Hiding in Plain Sight
Shadow AI threats arise when teams grab AI tools without approval. Data flows to unknown clouds. Vulnerabilities hide.
You focus on approved tech. Rogue use escapes notice. IP leaks. Regulators probe. One sales team tool shares contracts. Competitors gain edge.
Spot signs fast. Watch cloud bills spike. Note productivity jumps without explanation. Ask about new apps in meetings.
Consequences hit hard. A shadow AI threat turns innovation into liability. Map it to govern.
Other Common Gaps Beyond AI
Legacy systems linger. Third-party vendors integrate deep. Supply chains use unvetted tech. Remote tools multiply.
Without a map, you chase shadows. Legacy code fails under load. A vendor outage stops revenue. Remote apps lack controls.
Compare it this way. No map means partial view. Full map shows dependencies. You control the picture. Governance strengthens.
How to Map Your Technology Landscape Effectively
You build a map with focus. Start critical assets like data, apps, AI. Name owners. Assess risks. Set baselines.
It's achievable. No massive project. Target high-impact spots first, including shadow AI threats. Outcomes include visibility and quick decisions.
Follow three steps. Use tools like spreadsheets at start.
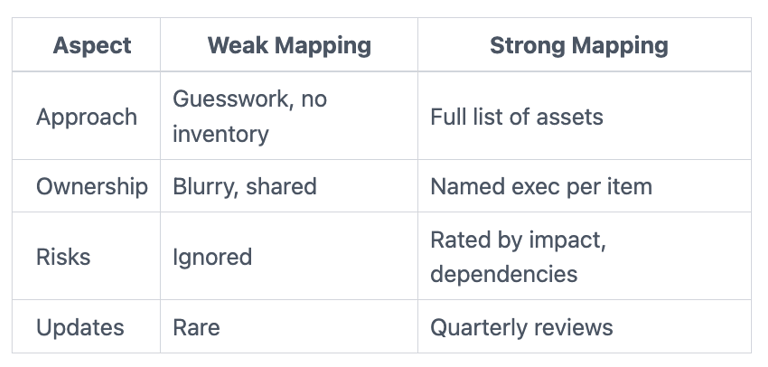
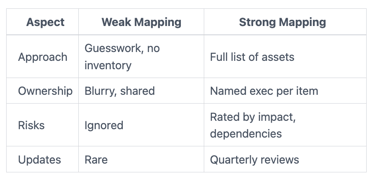
This table shows the shift. Strong mapping drives accountability. See a board cybersecurity advisor for oversight fit.
Step 1: Inventory What Counts Most
List core apps, data stores, AI experiments, vendor links. Prioritize by impact. Revenue systems first.
Use business lens. What stops if this fails? Spreadsheets work. Add columns for use, location, sensitivity.
You finish basics in days. High-impact areas reveal gaps fast.
Step 2: Assign Clear Ownership and Risks
Tag each item. Name owner. Rate risk low, medium, high. Note dependencies.
This uncovers shadow AI threats. Spot vendor reliance. Involve teams briefly. Keep it light.
Clear tags mean no more "someone handles it."
Step 3: Test and Update Regularly
Make it live. Review quarterly. Update after incidents or changes.
Test with walkthroughs. Does the map match reality? This builds trust. Resilience follows.
Questions to Ask for Stronger Oversight
Arm yourself with these. Ask management now. They spark action.
What shadow AI tools run today, and who owns them?
Does our map cover all critical assets and vendors?
Who accepts risk for unmapped items?
How do we spot new tech like AI experiments?
What changed in our stack last quarter?
When do we review the map next?
How does mapping tie to incident response?
Use them in meetings. Gaps surface. Decisions clarify. For more, see cyber risk questions audit committee should ask.
Frequently Asked Questions
How long does mapping take? Start with a high-impact inventory in one week. Full map builds over a month. Focus beats perfection.
What if teams resist sharing? Tie it to business goals. Show how it speeds approvals. Lead with exec buy-in.
How do you measure mapping success? Fewer surprises. Clear owners. Incident response uses the map. Track updates completed.
What about shadow AI threats specifically? Scan for AI use via bills, surveys. Ban unapproved tools. Map approved ones with rules.
Do you need software? Spreadsheets suffice first. Scale to tools later if needed.
How often update? Quarterly minimum. More with changes like new vendors.
You Govern Best with a Map in Hand
Mapping turns hope into control. You see risks. Ownership sticks. Surprises drop.
Take these steps now. Schedule a 30-minute kickoff. Review cyber reporting through mapping. Assign a map owner.
This builds trust and speed. You lead with clarity. Tyson Martin advises leaders like you on these moves.


