7 Signs You Need Interim CISO Services Now
See 7 signs you need Interim CISO Services now, unblock deals, calm the board, and get a 30-60-90 day plan to stabilize cyber risk fast.


You can feel it when cyber risk starts creeping into everyday business. Deals slow down because security answers aren't ready. Leaders hesitate before approving projects. The board asks tougher questions. Meanwhile, hiring a full-time Chief Information Security Officer can take months, and you may not need (or can't justify) a permanent executive yet.
Interim CISO Services (including Virtual CISO) offer experienced information security leadership on an interim leadership basis for a set time and scope. You bring someone in to create clarity, stabilize risk, and drive execution fast.
Below are seven signs you shouldn't ignore, what each one means in business terms (risk, uptime, trust, deal speed), and what you can do this month to get control without drama.
Key takeaways you can act on this week
You can spot a leadership gap when decisions stall, even though you already own plenty of tools.
You can unblock momentum quickly by setting decision rights, naming owners, and agreeing on risk tolerance in plain terms.
You should expect a clear, board-friendly top-risk summary for board reporting within the first 30 days, not a long assessment cycle.
You can reduce board uncertainty by reporting your security posture through trends and decisions, not activity counts and status colors.
You'll move faster when incident response becomes practiced behavior, not a document that lives in a folder.
You'll stop the "tool pile" pattern when spend ties to measurable risk reduction and protection of critical assets.
If you need fast stabilization without a permanent hire, an interim security executive who stabilizes risk quickly can compress months of confusion into weeks of direction.
The 7 signs you need Interim CISO Services now
These signs aren't really about buying more security products. They're about leadership, clarity, and follow-through in your information security policy. When those are missing, even good teams stay stuck. When those are present, you can make calm decisions under pressure and show progress without noise.
A simple test: if you can't name your top three cyber risks, who owns them, and what changes this quarter, you're running on hope.
You do not have clear ownership for cyber risk at the exec level
What it looks like: security "sits in IT," and hard calls bounce between leaders. Projects wait because nobody can confidently say yes or no. Exceptions pile up because rejecting them feels political.
Business impact: decisions slow down, risk hides in the gaps, and accountability gets fuzzy after an incident. You also lose time in budget cycles because you can't explain which spend changes which risk.
What to do next: name an executive risk owner (often the CEO, COO, or CIO) and define decision rights. Then bring in an interim leader to set the operating model for cyber risk management: who decides, who executes, and how progress gets reported.
Your board is asking sharper questions, and answers feel hand-wavy
What it looks like: board questions keep getting more specific, but your answers stay general. The deck gets longer, yet decisions don't get clearer. You hear, "We're working on it," too often.
Common questions you'll face include:
Are we ready for ransomware, and how do we know?
What are our top cyber threats right now, and what changed since last quarter?
Which third parties could hurt us the most?
What metrics show we're actually improving?
Business impact: board confidence drops, and leadership starts managing by anxiety. Directors may push for audits, outside reviews, or extra spend because they can't see a controlled plan.
What to do next: shift from "update reporting" to decision reporting. If you want a strong model for committee-level board reporting, use risk committee cybersecurity reporting guidance to tighten what you share, what you track, and what you ask the board to decide, or consider a virtual CISO for focused support.
You are one incident away from chaos, and you know it
What it looks like: you have an incident response plan, but it hasn't been tested with executives. Roles sound clear on paper, yet nobody knows who leads when facts are messy. Vendors aren't pre-selected, and communications are a scramble.
Business impact: downtime lasts longer, threatening business resilience, legal exposure grows, and trust erodes faster than you expect. In a serious event, your team spends precious hours negotiating authority instead of containing damage.
What to do next: run an executive tabletop in the next 30 days and lock in first-hour roles, decision rights, and outside support. For board-level clarity on oversight, review incident response oversight expectations for boards so you're aligned on what "ready" really means.
You are failing audits, missing deadlines, or living in constant compliance scramble
What it looks like: SOC 2, ISO 27001, HIPAA compliance, PCI, state privacy laws, or customer security reviews keep turning into late nights. Evidence lives in scattered folders. Control owners aren't sure what they own. Each audit feels like starting over.
Business impact: deals slow down, renewals get tense, and teams burn out. Worse, the scramble can hide real risk because everyone focuses on passing the next gate, not improving the program.
What to do next: stop treating regulatory compliance as a seasonal event. Build a simple control roadmap aligned to the NIST framework, assign owners, and create one source of truth for evidence. An interim CISO can sequence this so you stabilize fast, then mature steadily.
Security spend is rising, but you cannot show what you are getting
What it looks like: you keep adding tools, but the same problems return. Alerts stay noisy in security operations. Patch cycles lag in vulnerability management. Identity access sprawls. The budget conversation turns into, "We need more," without a clear tie to reduced exposure.
Business impact: finance loses patience, and leaders start questioning the entire security function. You may also underfund the basics because money is trapped in overlapping subscriptions.
What to do next: measure outcomes that executives understand, like risk reduction and recovery confidence. That can include time to detect and respond, patch latency on critical systems, backup recoverability, and protection of crown jewels. A strong starting point is measuring security's business impact, because it helps you connect spend to results without drowning in technical detail.
You are in a major change event, and security is not keeping up
What it looks like: growth is fast, but guardrails are slow. You're migrating to cloud with cloud security gaps, launching a new product, rolling out AI tools, consolidating vendors, or dealing with leadership turnover. Security reviews become a bottleneck, or worse, they get skipped.
Business impact: you ship risk into production and create expensive rework later. Teams also lose confidence because rules change midstream, and nobody can explain the "why."
What to do next: treat change events like risk multipliers. An interim CISO can set your security strategy, priorities, governance, and a decision cadence in weeks, so security supports delivery instead of blocking it. The goal is simple: fewer surprises while you move fast.
A deal, acquisition, or major customer is pressuring you on security fast
What it looks like: diligence requests hit, and the data room turns into chaos. Customer questionnaires get inconsistent answers. "Do we have a policy for that?" becomes a daily question. You aren't sure where the crown jewels live, or who can prove controls work.
Business impact: deal timelines slip, valuation pressure rises, and trust weakens at the worst moment. Insurers may also demand proof fast, which adds friction when you're already stretched.
What to do next: appoint a single owner for diligence answers, build a tight evidence pack with third-party risk management insights, and align your risk story through a gap analysis. If the pressure is tied to acquisition timing, an interim CISO for acquisition support can bring structure, consistency, and credible executive-level responses quickly.
What you should expect in the first 30, 60, and 90 days
A good interim CISO doesn't bury you in paperwork. You should feel more control and fewer unknowns each week. You also shouldn't wonder who's deciding what anymore.
Here's a simple roadmap you can use to set expectations upfront. For a broader view of how time-bound executive support works, see interim leadership for high-stakes moments.
One sentence of context before the table: this is the outcome-focused version, not the "deliverable theater" version.
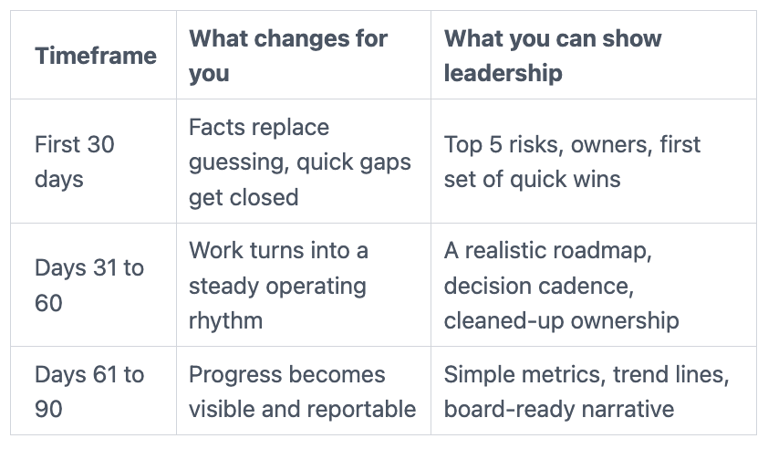
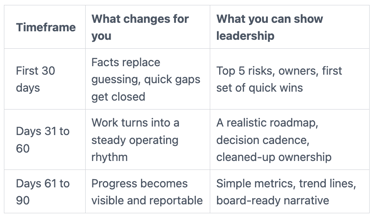
The takeaway: you're buying pace and clarity, not a longer list of tasks.
First 30 days: get the facts, stop the bleeding, pick the top 5 risks
In the first month, you should see fast discovery with tight scope. That includes a high-level map of critical assets and sensitive data, a snapshot of your current cybersecurity program, and a practical incident readiness check.
You also want third-party hot spots called out early, because vendor access often expands quietly. Finally, you should get quick wins that reduce obvious exposure, especially around privileged access, remote access, backups, and logging basics.
By day 30, you should be able to tell the CEO and board: "Here are the top five risks from our initial risk assessment, what they mean in business impact, what we're doing now, and what decisions we need."
Days 31 to 60: turn priorities into an operating rhythm
Now you shift from triage to execution. That means a predictable decision cadence, a small steering group, and a written ownership model that keeps work from bouncing around.
You'll also see policy cleanup where it removes friction, not because it looks nice. Vendor rationalization often starts here too, because duplicate tooling and unclear ownership drain money and attention.
Most importantly, you avoid boiling the ocean by sequencing work around what reduces risk fastest for your crown jewels.
Days 61 to 90: prove progress with simple metrics and board reporting
By this point, you should track a small set of metrics that matter to security maturity, then show trends over time. Think patch latency for critical assets, MFA coverage for privileged users, backup recovery test results, time to respond, and reduction of high-risk exceptions.
You also want a clear risk acceptance process, because "we'll fix it later" is not a plan. When reporting is honest and stable, you build confidence and trust without pretending you've reached perfection.
How to choose the right interim CISO, and avoid common mistakes
The wrong interim hire can create motion without progress. The right one creates calm, speed, and shared ownership.
If you want a CEO-friendly screen for fit, use how CEOs should vet a CISO as a practical baseline.
Look for business-first leadership, not just technical depth
You need someone who can translate risk into downtime, dollars, and trust. You also want a leader who can say what to do first, even when the inputs are messy.
Strong signals of information security leadership show up fast: they influence peers without authority, they brief the board clearly, and they don't default to "buy another tool" as the answer. On the other hand, a tool-driven approach often ignores security governance, the hard parts, decision rights, tradeoffs, and follow-through.
Get the scope and success measures in writing
You'll move faster when you define scope up front. At minimum, set expectations for authority, decision rights, time commitment, deliverables, stakeholder map, escalation path, and exit criteria.
Also protect your internal team. If IT and security staff feel blamed or sidelined, you'll lose the very people you need to execute. A good interim leader earns trust by making the team stronger, not smaller.
FAQs about Interim CISO Services
What is the difference between an interim CISO and a fractional CISO?
An interim CISO is usually higher intensity and tied to a change event, like an incident, regulatory compliance audit failure, leadership gap, or a deal. A fractional CISO, also known as a virtual CISO, is ongoing leadership with a steadier cadence over time. If you want that longer-term model, see fractional CISO services.
How fast can an interim CISO make a difference?
You can often see triage and stabilization in the first week, especially around access, backups, data protection, and decision paths. In the first 30 days, you should gain clarity on top risks and quick wins. By 90 days, you should see measurable progress, assuming you give access to the right people and data.
Do you need an interim CISO if you already have an IT director or security manager?
You might, because managers run operations, while a CISO (Chief Information Security Officer) sets strategy, governance, and board reporting. For example, your security manager can patch systems and tune tools. An interim CISO can decide what matters most, align leaders on tradeoffs, and create a plan the board will support.
How do you keep momentum after the interim engagement ends?
You develop a transition plan from day one. Common paths include hiring a permanent CISO, moving to fractional support, or handing off to a strengthened internal leader. The backbone is simple: documented decisions, a working operating rhythm, board-ready reporting, and training so the organization doesn't revert.
Conclusion: clarity beats guessing
If you recognized several of these seven signs, the real problem usually isn't effort. It's uncertainty about ownership, priorities, and what "good" looks like right now. Interim CISO Services give you a practical way to get clearer Governance Risk and Compliance insights, stronger oversight, and faster execution without waiting on a long hiring cycle.
When you're ready to confirm fit and next steps, you can start your interim CISO engagement conversation and turn this month's pressure into a stabilized plan that includes security awareness training and a security strategy you can stand behind.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
