Interim CISO Contract: How to Set Clear Success Criteria
Set clear success criteria in your interim CISO contract, outcomes, proof, decision rights, and timelines, so boards agree and scope stays tight.


You don't hire an interim Chief Information Security Officer because things feel calm. You do it because something is urgent, a breach risk that won't wait, a bad audit report, a cybersecurity leadership gap, an acquisition, or insurer pressure that's turning into real business friction.
The most common failure mode is simple: the interim CISO contract says "improve security," but it never defines what success looks like for your information security strategy. As a result, scope creeps, executives disagree in side conversations, and board confidence gets weaker instead of stronger.
You can avoid that. In this guide, you'll set success criteria that are measurable, time-bound, and tied to business outcomes, whether you need help for 60 to 180 days or longer. If you're looking for a clear model of what fast stabilization should look like, start with this interim security executive approach.
Key takeaways you can use before you sign an interim CISO contract
These key takeaways apply whether you are signing an interim CISO contract or considering a fractional CISO as an alternative model.
Write outcomes first, not activities: "Reduce ransomware blast radius" beats "review our tools."
Name deliverables you can inspect: You should be able to open a document, see evidence, and confirm "done."
Choose a few decision metrics: Track what changes decisions (not what fills a dashboard). Use executive-friendly cyber metrics as your standard.
Define decision rights in plain language: If the interim CISO can't approve key actions, work stalls.
Put a clock on it: Tie each success item to a due date, an owner, and a checkpoint.
Avoid tool shopping as the "plan": New platforms rarely fix unclear ownership in information technology management, weak access control, or untested recovery.
Confirm board and exec expectations upfront: Align on risk appetite, compliance requirements, reporting cadence, and escalation thresholds before week one.
Start with alignment, what are you hiring an interim CISO to change right now?
Before you talk metrics, get clear on the mission. Otherwise, you'll measure the wrong things with great precision.
Start by aligning your core decision-makers, including the risk management executive: CEO, CFO, General Counsel, CIO, data protection officer, and the owners of the biggest operational risks (often product, operations, and customer support). They should not have to guess what matters most, or translate political signals into a plan.
A practical way to frame alignment is "if this, then that." For example:
If ransomware is the top concern, then success must include tested recovery, clear escalation steps, and realistic recovery time targets.
If your audit findings threaten revenue (customer questionnaires, renewals, or a regulator), then success must include evidence quality, control ownership, and a clean remediation timeline.
If you're in M&A, then success must include integration guardrails, access consolidation, and risk acceptance rules that match the deal timeline.
You also need a shared definition of "right now." In an interim window, you're not rebuilding everything. You're reducing uncertainty fast, closing the easiest paths to a bad day, and leaving behind a security roadmap your leaders can run. If you want CEO-level clarity on how to tie security to business priorities, use this framing from a cybersecurity strategy advisor for CEOs.
When everyone agrees on the problem you're solving this quarter, you stop paying for meetings that go nowhere.
Write a one paragraph mission statement that sets boundaries
A mission statement is your seatbelt. It protects you from drift, and it protects them from impossible expectations.
Use a fill-in-the-blank statement like this for strategic security planning, written as a single paragraph in the contract scope:
In the next X days, you will reduce Y risk for Z business priority by delivering A, B, C, while not changing D without approval.
Keep it blunt. "Reduce ransomware downtime risk for our order-to-cash systems" is better than "improve resilience." Also name what stays stable unless you approve it, such as core architecture, major vendor swaps, or broad rewrites of ISMS policies.
Boundaries also make tradeoffs easier. If a new "urgent" request appears, you can compare it to the mission and decide fast: is it in scope, or is it a change request?
Define decision rights so work does not stall
They can't be effective if every important move requires a new committee. Decision rights are part of success criteria because they determine speed.
At minimum, clarify who can decide, and how quickly, on these topics:
Policy exceptions (who grants them, for how long, and what evidence is required)
Risk acceptance (what thresholds require CEO, GC, or board awareness)
Incident escalation (who declares an incident, who notifies insurer and counsel, who speaks externally)
Budget tradeoffs (what they can reallocate without approvals)
Vendor renewals and security add-ons (who signs, who owns the relationship)
Your board does not need to approve daily actions, but it should govern the rules of the road through information security governance. When you anchor this in board oversight, it becomes easier to defend decisions later. This is where cybersecurity governance for boards helps, it turns "security updates" into accountable oversight.
Turn goals into clear success criteria, deliverables, metrics, and timelines
A strong engagement translates broad goals into outcomes you can verify. The test is simple: could a smart outsider look at the work and agree it happened?
Start with the goal, then write three parts:
Outcome (what changes for the business)
Proof (what you will see)
Time box (by when, and who owns it)
This works across common interim engagements, including security program development:
Stabilizing a drifting program (cybersecurity risk assessment, risk register, ownership, operating rhythm)
Preparing for an audit (evidence map for ISO 27001 or PCI DSS, remediation plan, control owners)
Building incident readiness (incident response plan: roles, call tree, tabletop, comms paths)
Improving third-party risk (vendor tiering, contract minimums, offboarding)
Leading security through leadership transition (handoff plan, roadmap, staffing plan)
If you want the board to evaluate progress without getting lost in jargon, align your success criteria to board oversight of CISO performance metrics. That keeps the conversation anchored in outcomes, not personality or noise.
Use a simple success scorecard, outcomes, proof, and due dates
A one-page scorecard beats a 30-slide deck. Keep it short enough that you can review it in ten minutes. Perfect for board reporting.
Here's the scorecard format to use. Each row names the outcome, the evidence you will see, and the due date plus owner.
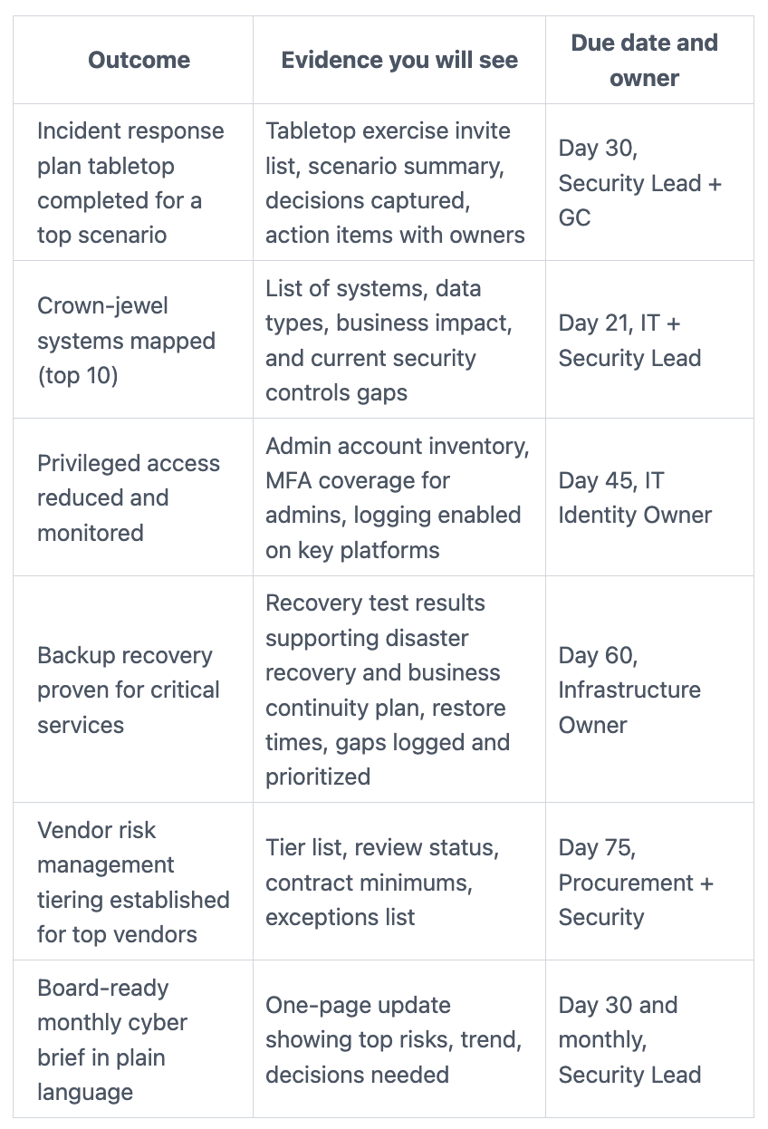
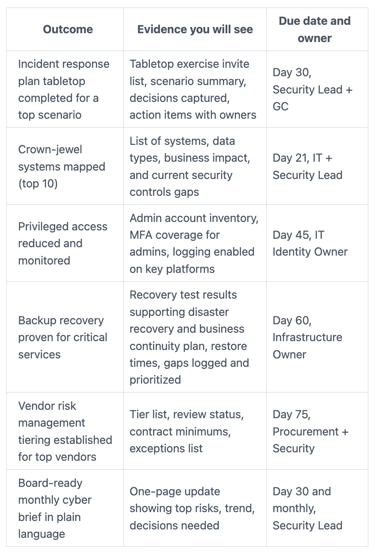
The takeaway: you're buying visible progress, including on the incident response plan. If the evidence isn't clear, success will turn into debate.
Pick metrics that drive decisions, not vanity numbers
Activity metrics are tempting because they're easy. "Tickets closed" or "vulnerabilities found" can look busy, but they don't always change risk.
Decision metrics are different. They tell you what to do next, and where you're exposed. For example: patch SLA compliance on critical assets, MFA coverage on admin accounts, time to contain high-severity incidents, backup recovery time for crown jewels, and number of high-risk vendor exceptions.
In the first two to three weeks, treat metrics as a baseline sprint. You can't improve what you haven't measured honestly. After you set baselines, pick a realistic improvement target by day 90. Don't promise miracles. Do promise movement you can prove.
Also, plan for the moment when things go wrong, because that's when leadership needs clarity most. Your security leader should be ready to report calm, credible signals under pressure, using ideas like these crisis command center metrics to keep executives aligned and decision-making steady.
Protect the engagement with contract terms that support success
Success criteria can still fail if the contract mechanics work against you. The contract should make access, cadence, and incident handling explicit, not implied.
Start with scope language that matches your mission statement. Then add the "how" terms that prevent confusion:
Access and authority: what systems, logs, people, and vendors the Virtual CISO or Remote CISO can reach, and by when
Cadence: weekly exec updates, monthly board sponsor update, and the format (one page beats ten)
Confidentiality and privilege: how you coordinate with counsel, especially during investigations
Independence: guardrails against vendor conflicts and tool sales pressure, including verification of qualifications like CISSP certification
Incident support: what happens if a real incident hits during the term, including availability and billing rules
If you want fewer surprises, set expectations early, before the contract gets "finalized" by habit. Engaging support up front often saves weeks later, which is why leaders sometimes engage a CISO advisor early to tighten scope, outcomes, and board-facing reporting.
Set a realistic 30, 60, 90 day plan with checkpoints
Checkpoints turn a time-boxed engagement into a controlled effort. They also give you clean moments to continue, expand, or transition.
By day 30, expect triage and clarity: top risks ranked, baseline metrics established, and the most dangerous exposure reduced (often identity, remote access, backups, and escalation paths). By day 60, you should see plans turning into routines, plus a few early wins with evidence. By day 90, you want repeatable governance that fosters digital trust, stable reporting, and measurable improvement you can defend.
These milestones should line up with your broader leadership needs, especially if you're bridging a gap in information technology management. This is the kind of structure you should expect from an Interim IT executive offering interim leadership support with 30, 60, 90-day outcomes.
Agree on what is out of scope and how change requests work
Scope traps are predictable. Full tool replacement, a full policy rewrite, or trying to fix every audit finding at once can consume the whole engagement while leaving risk unchanged.
Instead, add a simple change control rule to the contract: any new major work requires a written impact on timeline, cost, and success criteria, and you approve it before work starts. That protects you from surprise bills, and it protects the provider from a moving finish line.
FAQs about interim CISO contract success criteria
How many success criteria should you include in a CISO contract?
Aim for a short list you can review quickly, often 6 to 12 items; this works well even for a Fractional CISO. If you need 30 items to describe success, your scope is too broad. Keep the rest as a backlog, not contract promises.
Should success criteria focus on deliverables or risk reduction?
Use both. Deliverables create proof, while risk reduction explains why it matters to your information security strategy. A tabletop exercise is a deliverable, reduced time-to-decision in an incident is the business outcome.
What if you don't have baseline metrics yet?
Make baselining a deliverable in the first two to three weeks. Then set improvement targets for day 60 and day 90. You're buying honest measurement first, then movement.
Who should "own" success criteria, the CISO or your team?
Shared ownership works best. The risk management executive drives, but internal leaders must own key controls (identity, infrastructure, apps, procurement). Otherwise, improvements vanish after the engagement.
How do you prevent endless assessments?
Put a time box on discovery and require tangible outputs early. For example, "Top 10 risks, including ISMS policies gaps, and a one-page plan by day 10." If discovery keeps expanding, insist on a change request.
How do you hire the right interim leader for this kind of contract?
Look for week-one proof: a clear 30-day plan, fast risk triage, and board-ready communication for board reporting. This guide to best CISO traits helps you separate stabilizers from talkers.
Conclusion
A strong interim CISO contract doesn't just describe work, it defines success you can inspect. When you set outcomes like vendor risk management, evidence for security controls, and decision rights up front, you get faster progress and fewer surprises. Just as important, you give your board a clear way to oversee risk without guessing.
Your next step can be simple: review your one-paragraph mission statement, build a one-page success scorecard, and confirm cadence with your CEO and board sponsor. If you want a practical model for moving quickly without chaos, use this interim security executive engagement path, ideal for interim IT executives, to set expectations and lock in measurable results that build digital trust.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
