The 5 Questions Every Director Should Ask the CISO: Move beyond technical metrics and start measuring strategic resilience.
Use these board questions for CISO talks to see real cyber resilience, weak ownership, and recovery risk before the next board meeting.


Most board conversations with the CISO still get stuck in activity. You hear alert counts, patch rates, training completion, and tool updates. Yet those numbers rarely tell you whether the business can prevent disruption, absorb a hit, and recover without losing trust.
That is the real job of board questions for CISO discussions. You need a clearer view of exposure, ownership, readiness, and recovery. When you ask the right five questions, you learn far more than a dashboard usually shows.
Key takeaways: the five questions that change the board conversation
Ask which few cyber risks could disrupt the business this year, so management must rank exposure by business consequence.
Ask where ownership is weak or shared, so accountability gaps surface before an incident does.
Ask what breaks first in a serious incident, so you can judge operational readiness instead of hearing generic confidence.
Ask how risk is improving over time, so reporting shows movement and not team activity.
Ask what would make the CISO seek board help now, so you get early warning on pressure points, tradeoffs, and stalled decisions.
Why technical metrics can hide real risk from the board
Security dashboards often create comfort without clarity. A board packet may show thousands of blocked attacks, high training completion, and solid patch progress. However, those numbers can still leave you blind to what matters most.
You need to know what could stop revenue, interrupt operations, trigger legal exposure, or damage customer trust. You also need to know who owns those risks and what happens if controls fail. That is the difference between information and governance.
If your board still gets dense updates, CISO board reporting best practices can help reset the format around business impact and decisions.
Busy security reporting is not the same as decision-useful reporting
Decision-grade reporting is concise. It shows trend, business impact, ownership, and thresholds for escalation. It also states what changed since the last meeting and what decision management needs from you.
By contrast, activity metrics can stay green while exposure grows. You can patch thousands of issues and still leave a critical service fragile. You can block attacks all day and still have weak recovery.
If a report cannot tell you what decision is needed, it is not board-ready.
Resilience is about business continuity, not just cyber defense
Strategic resilience means your company can keep serving customers, protect key processes, and recover with control when something goes wrong. That includes cyber defense, but it also includes decision rights, third-party dependencies, communications, and tested recovery.
Boards often miss this because security updates focus on protection. The larger question is whether the business can take a punch and keep operating. That is why these five questions matter.
The five questions every director should ask the CISO
These are not technical review questions. They are governance questions. Used well, they help you judge management credibility and the company's ability to operate under pressure.
For broader context on board-ready cyber risk questions, this same discipline applies across governance, reporting, and incident oversight.
What are the few cyber risks most likely to disrupt the business this year?
This question forces prioritization. A strong answer names a small number of risks and ties each one to business effect, such as lost revenue, downtime, customer harm, compliance exposure, or delayed growth.
You should hear plain language. For example, a fragile identity system could lock out critical staff. A key vendor failure could stop order flow. Weak recovery for a major platform could turn a short outage into a multi-day event.
Be cautious if you get a long list with vague labels like "high" or "critical." You should also worry when the answer has no link to business processes. If everything is a top risk, nothing is.
Where are we most exposed because ownership is weak, unclear, or shared?
Many failures start with blurry authority. Security may spot the risk, but IT owns the system, legal owns part of the response, operations owns continuity, and a vendor owns part of the stack. Shared responsibility without clear accountability is where drift begins.
A strong CISO answer names the accountable executive, the current gap, and the plan to close it. You should hear where decision rights break down and how management is fixing them.
This question also connects to boards setting technology risk appetite. If your board has not defined tolerances and escalation thresholds, ownership will stay fuzzy when pressure rises.
If a serious incident hits tomorrow, what breaks first and how ready are we to respond?
This is the readiness question. You are asking which business services are most fragile, what dependencies matter, and who would make the hard calls in the first hours.
A strong answer identifies the most vulnerable services, the likely failure points, the decision makers, and the evidence from realistic exercises. You want to hear that leadership has practiced shutdown decisions, communication paths, outside counsel triggers, and recovery steps.
Warning signs are easy to spot. Overconfidence is one. No recent tabletop exercise is another. A weak escalation path is worse, because it means the company may lose time while authority gets negotiated.
If you want a model for board incident response oversight, focus on proof, not comfort.
How will you show us that risk is improving, not just that the team is busy?
This question tests reporting quality. Good reporting should show trend over time, movement against agreed priorities, reduced exposure around critical services, and whether controls are working where they matter most.
You should expect a small set of indicators that management can explain in plain English. For example, you might see improved recovery test results for a crown-jewel system, fewer expired risk exceptions, or stronger privileged access coverage tied to critical assets.
Weak answers lean on volume. More tickets closed, more alerts handled, more scans run. Activity matters to management, but the board needs evidence that the company is getting safer in ways that matter.
What would make you ask the board for help right now?
This question reveals candor. Good CISOs do not wait until the problem is polished. They tell you where tradeoffs, constraints, or conflicts are starting to strain the program.
A strong answer may include funding choices, leadership gaps, vendor concentration, policy exceptions, M&A pressure, rapid AI adoption, or unresolved conflicts between speed and control. Those are board-level issues because they shape the company's risk posture.
Be concerned if the answer is, "Nothing right now." Every serious company has tensions. You want early warning, not smooth reassurance.
What good answers sound like, and what should raise concern
You do not need deep technical skill to tell the difference between real oversight and technical theater. You need to listen for clarity, ownership, and evidence.
Signs the CISO understands the business and can support the board
A capable CISO prioritizes. You hear a short list of risks, not a flood of issues. You also hear tradeoffs stated plainly, with business impact attached.
Strong answers sound calm and specific. Ownership is visible. Recovery has been tested. Escalation thresholds are clear. That kind of reporting builds trust because it helps you decide.
Signs you are hearing confidence without real resilience
This quick comparison helps you judge the quality of the discussion.
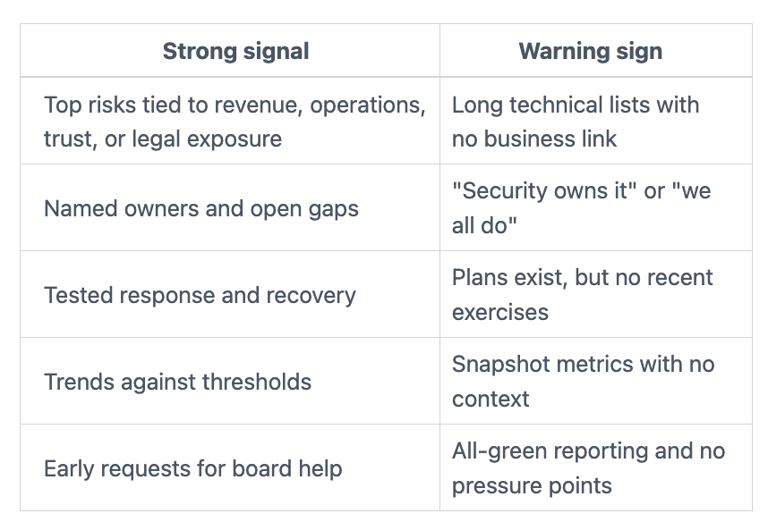
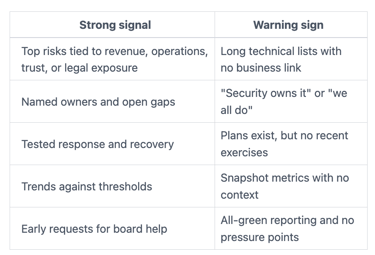
When the board keeps hearing only green status, you should assume the picture is incomplete.
How to turn these questions into better board oversight
These questions work best as a repeatable governance tool. Use them every quarter, and you create a steady frame for trend, accountability, and escalation.
If you need clarify risk appetite and escalation paths, make that part of the board cadence and not a one-time workshop.
Use the same five questions each quarter so trends become visible
Consistency matters because it helps you spot drift. You can see when the same ownership gap remains open, when recovery keeps slipping, or when new business initiatives increase exposure.
A stable set of questions also improves management reporting. Teams stop rebuilding the story each quarter. Instead, they show what changed, what improved, and what still needs action.
Ask for one-page answers tied to business impact and next actions
Keep the format simple. Ask for top risks, what changed, where ownership sits, what needs a decision, and what could strain resilience next quarter.
That one-page discipline does two things. First, it forces management to prioritize. Second, it helps you stay in governance rather than drifting into operations.
Frequently asked questions about board questions for CISO discussions
How often should the board meet with the CISO?
Quarterly is a sound baseline for most boards. If the company is in transition, dealing with an incident, preparing for a transaction, or moving fast with AI, you may need more frequent touchpoints.
Should the CISO present directly to the board?
Yes, in most cases. Direct access improves clarity and reduces translation loss through layers of management. The CEO and other executives still matter, but the board should hear from the CISO in their own voice.
What metrics belong in a board deck?
Use metrics that show business exposure, trend, ownership, and recovery strength. Keep out raw alert volume, tool status, and other measures that do not support a decision.
How can a non-technical director challenge weak answers?
Ask for plain language, named owners, thresholds, and evidence. If the answer stays vague, ask what business process is exposed, what the likely consequence is, and what management needs from the board.
Strong oversight starts with better questions, not more technical detail. When you ask about exposure, ownership, readiness, reporting quality, and calls for help, you learn whether the company can operate through disruption.
Use these five questions in your next CISO discussion. Then judge the answers by clarity, ownership, readiness, and business consequence. If those four elements are weak, the reporting needs work before the next board cycle.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
