10 Signs Your IT Strategy Needs a New Roadmap
Spot 10 signs your IT roadmap is stale, fix priorities fast, and make third-party risk reporting to the board clear, steady, and actionable.


In today's fast-paced digital transformation, you can feel it when your IT strategy is off. The work never stops, budgets keep moving, and yet the outcomes stay fuzzy. Your teams might be talented and busy, but the business still asks, "Are we safer, faster, and more reliable than last quarter?"
An IT strategy and roadmap is just a plain plan that connects business goals to systems, people, money, and risk. It should help you decide what you'll do now, what you'll delay, and what you'll stop doing.
Below are 10 practical signs your roadmap is outdated, plus clear next steps to reset it without a year-long planning cycle. If you want one simple test, ask whether your roadmap produces answers a board can act on, for example third-party risk reporting to the board. When that breaks down, your roadmap usually is not doing its job.
Key takeaways you can use right away
If priorities change weekly, your IT roadmap isn't guiding work, it's reacting to noise.
If projects don't map to outcomes, you'll get debate, not strategic alignment.
If "done" doesn't include adoption and support from stakeholders, delivery won't stick.
Tool sprawl is often a symptom of unclear standards and weak decision rights.
If reporting needs a custom deck, IT governance is too manual to trust.
When risk updates only show up after bad events, you're managing surprises, not risk.
If vendors are treated like paperwork, you'll miss real exposure in day-to-day operations.
A good roadmap ties spend to business results and risk visibility, not activity.
First, check if IT is still tied to the business, or just reacting to noise
When your IT strategy and roadmap matches the business, it feels like momentum. When it doesn't, IT becomes a "service desk with projects," and leadership loses confidence.
Misalignment shows up fast during real business moments. A new product launch gets slowed by surprise integration work. An acquisition forces you to discover the current state of how many systems aren't documented. An audit finding turns into a scramble because evidence and ownership are unclear. A customer trust issue lands, and nobody can explain which cybersecurity controls matter most.
You don't fix this by "working harder." You fix it by making the roadmap a decision tool that reflects what the CEO and board are trying to accomplish. If you need help translating CEO priorities into a plan that holds up under pressure, this perspective on a business-aligned security and technology strategy can help: cybersecurity strategy advisor for CEOs.
Sign 3: Your roadmap ignores major business events until they become emergencies.
If launches, audits, acquisitions, or customer demands repeatedly trigger unplanned work, the roadmap is not built around business realities.
Sign 4: Your "strategy" is a list of projects, not a set of business tradeoffs.
If you can't explain what you're protecting (revenue, uptime, customer trust) and what you're choosing not to optimize for, representing strategic objectives, the plan will collapse under competing opinions.
Sign 1: You are always in firefighting mode, and the plan changes every week
Firefighting feels productive, but it's usually a sign of weak prioritization and thin guardrails. You see it in urgent tickets that preempt planned work, surprise outages that steal the best engineers, and last-minute vendor renewals that get approved without negotiation. Even "small" changes become risky because nobody trusts the environment.
A stable roadmap doesn't mean you never change priorities. It means you change them on purpose, with rules everyone respects. Think of it like air traffic control. Planes still land in storms, but the system doesn't improvise every minute.
Ask your team three quick questions:
What did we pause this month, and who approved the tradeoff?
What "run" work keeps interrupting "change" work, and why?
What would break if we stopped one major initiative tomorrow?
If those answers are vague, your roadmap is a calendar, not a guide.
Sign 2: Your projects do not map to clear outcomes, so leaders argue about what matters
You can run ten initiatives and still be stuck. Activity hides in plain sight when the roadmap measures effort instead of outcomes.
Business-readable outcomes are simple, for example: revenue enablement, shorter cycle time, better uptime, audit readiness, fewer high-risk exceptions, reduced incident impact. When projects don't map to outcomes, every leader brings their own definition of "important," and you get constant debate.
This is where the board question becomes painful: "What ROI did we get for the spend?" If you can't answer without a long story, the roadmap isn't doing its job. A healthy roadmap lets you say, in a few sentences, what improved and what risk dropped.
If you can't connect spend to outcomes and risk reduction that support business goals, you don't have an IT strategy, you have a queue.
Look for execution gaps that waste money, time, and trust
Even with a solid strategy, execution gaps can sink the roadmap. These gaps often feel like "delivery problems," but they're really operating model problems. Ownership is unclear. Standards drift. Reporting becomes a manual performance art.
One practical signal is how you measure progress. If you need heavy storytelling to prove improvement, you probably lack a small set of performance metrics that leaders can inspect. This is also where security and technology reporting can get sharper fast, using a few measures that show direction, not noise: the hidden value of cyber metrics.
Sign 5: Teams ship work, but nothing feels finished, adopted, or supported
Your teams may "deliver," yet the business doesn't change. Adoption stays low. Support calls increase. People invent workarounds. Six months later, you're replacing what you just launched.
This usually happens because "done" is defined as deployment, not operational ownership. You can tighten this with a simple definition of done for IT work:
Owner: a named person accountable after go-live
Budget: run costs, renewal costs, and resource allocation identified
Controls: access, logging, and basic risk checks completed
Monitoring: alerts, dashboards, and on-call path set
User adoption plan: training, comms, and feedback loop ready
If one of these is missing, you didn't finish. You just moved the work into the future.
Sign 6: Your tech stack keeps growing, but reliability and speed do not improve
Tool sprawl hampers operational efficiency, is expensive, but the bigger cost is complexity. Duplicate platforms create inconsistent data. Overlapping vendors, particularly in cloud computing, create unclear responsibility. Every new tool adds another failure point to your IT infrastructure, another renewal, another integration, another set of permissions.
Here's what that looks like during an incident. Your team has to check five consoles. Ownership isn't clear. Logs don't line up. Meanwhile, change approvals slow down because nobody is sure what dependencies exist.
A practical next step is boring and effective: inventory what you have, rationalize what overlaps, and set standards for what "good" looks like for your IT infrastructure. Standards reduce debate, speed decisions, and limit surprise costs.
Sign 7: You cannot measure progress without a custom slide deck and a lot of storytelling
When reporting is manual, decisions get emotional. Leaders argue based on anecdotes because the facts aren't stable month to month. You also end up rewarding teams that present well, not teams that reduce risk and improve service.
Your monthly reporting should be easy enough to produce without heroic effort. Metrics should be business-readable and consistent, not a new set each quarter. For example, you should be able to report:
Service availability for critical services
Time to patch critical issues on crown-jewel systems
Count of high-risk exceptions past due
Ransomware readiness items (backup restore test status, MFA coverage)
Major project milestones against forecast
Top third-party risks and status
If you can't produce these without a custom deck, governance and decision rights need tightening.
If risk and governance feel fuzzy, your roadmap is already behind
This is where roadmaps quietly fail. You can ship features and still lose trust if risk oversight is weak. Boards and executive teams don't need deep technical detail, but they do need steady, decision-oriented visibility. That includes how you frame top risks, what you're doing about them, and what choices you need leaders to make.
If you want a strong baseline for what leadership should be asking, this guide helps structure the conversation in plain language: audit committee cyber risk questions.
Sign 8: The board only hears about cyber risk after a bad event, not through steady reporting
Steady cybersecurity reporting means cadence, trends, and decisions needed. It's calm, repeatable, and comparable over time. You don't "surprise" the board, and the board doesn't "surprise" you with sudden demands.
A concrete dashboard item that often exposes roadmap weakness is third-party risk reporting to the board. If it's ad hoc, you're likely missing vendor tiering, ongoing monitoring, and clear ownership.
A good IT roadmap enables board-level decisions such as:
Funding: approve investment tied to measurable risk reduction
Risk acceptance: explicitly accept a defined risk for a defined time
Timeline tradeoffs: decide whether speed or risk reduction comes first for a major initiative
Without these, reporting becomes theater, and governance stays fuzzy.
Sign 9: Vendor and cloud risk is treated like paperwork, not an operating reality
Paperwork-heavy vendor risk management can still miss the real risk, like standing access, weak offboarding, unclear incident notice paths, and shadow SaaS bought on a credit card.
You can simplify this with a three-tier approach. Keep it practical, and tie it to business impact.
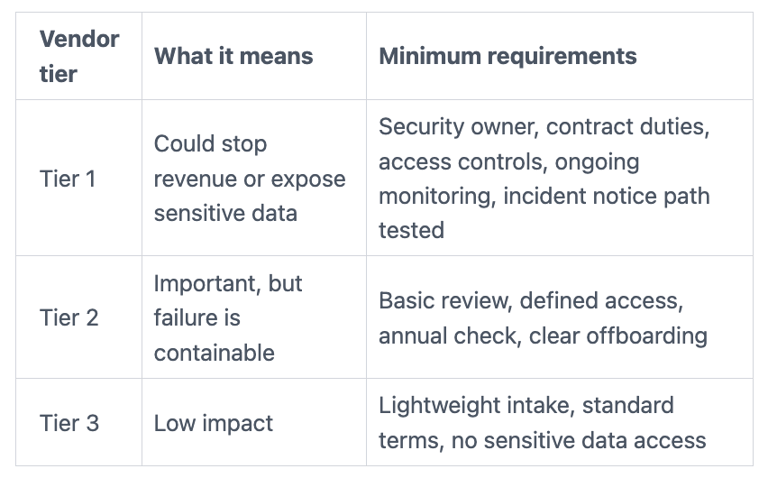
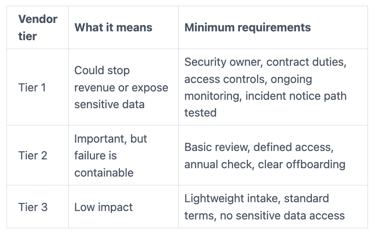
The takeaway is simple: spend time where the business impact is real, not where the paperwork is easy.
Sign 10: Incident readiness is unclear, so everyone hopes the plan will work in real life
A document is not readiness. Readiness is muscle memory, decision rights, and proof that recovery works.
You're "ready" when roles are named, escalation triggers are clear, backups are protected and tested, communications with stakeholders are rehearsed, and third-party contact paths work after hours. Tabletop exercises matter because they reveal the awkward gaps, like who can shut down a system, who calls counsel, and who speaks to customers.
Board oversight is part of readiness, not an afterthought. If you're tightening that oversight, this reference helps clarify what the board should expect and how it should stay involved: board incident response oversight.
What to do next: build a simpler roadmap you can explain in five minutes
You don't need a perfect IT roadmap. You need one that survives reality.
Over the next 30 to 60 days, aim for clarity, not volume. Start by naming outcomes, constraints, and decision rights. Then publish a short implementation roadmap that ties work to business impact, with owners and dates. Keep it small enough that you can repeat it consistently.
If you need hands-on senior help to reset priorities, stabilize risk, and improve board reporting without waiting for a full-time hire, fractional leadership can be a practical bridge: fractional CISO services.
Run a fast roadmap reset, starting with outcomes, constraints, and decision rights
Use a short sequence for strategic planning:
Confirm business goals for the next two quarters (growth, reliability, audit, customer trust).
Map the top risks that could block those goals (including third-party and identity risks).
Identify must-run services and crown-jewel systems, then protect them first.
Define standards (approved tools, architecture patterns, security minimums, automation).
Pick a small set of priorities, then publish what you're not doing.
Saying "no" works best when you offer a tradeoff. Name what you'll delay, explain why, and record who made the call. That removes drama and stops quiet resentment.
Set a monthly operating rhythm so progress toward your future vision is visible, not guessed
Keep the cadence lightweight:
Weekly delivery check: owners, blockers, next milestones
Monthly exec review: outcomes, risk changes, budget tradeoffs, decisions needed
Quarterly board-ready summary: trends, top risks, major commitments, where help is needed
Consistency is the point. When the format stays stable, leaders spot trends early, and small problems don't turn into big surprises.
FAQs leaders ask when they realize the roadmap is stale
How often should you refresh an IT strategy roadmap?
At least quarterly for priorities and forecasts, and annually for the bigger direction. Refresh sooner after an acquisition, a major incident, a major product shift, or the rise of artificial intelligence and other emerging technologies.
What's the fastest way to tell if your roadmap is working?
You can explain progress in five minutes, tied to outcomes and risk. If you need a custom story each time, the IT roadmap isn't inspectable.
What should the board see, without getting buried in detail?
Trends, top risks, and decisions needed. Boards don't need tool updates, but they do need clear thresholds, key performance indicators, and steady reporting.
How do you make third-party risk real without turning it into a compliance lecture?
Treat it like operational dependency management. Tier vendors, monitor Tier 1 partners, and make third-party risk reporting to the board a repeatable dashboard item.
Should you fix strategy first, or execution first?
Fix decision rights and outcomes first, then tighten execution. Without clear choices, better execution just ships the wrong work faster.
Conclusion
When your IT strategy roadmap is healthy and supports your digital strategy, you spend less time arguing over technology investments and more time delivering outcomes. You also reduce surprise risk in those technology investments because reporting is steady and decisions are recorded. Start with the signs that hurt most, then reset priorities around strategic objectives, standards, and ownership through SWOT analysis and gap analysis. Maintain the IT roadmap with strong project portfolio management. The goal is not perfection, it's clarity you can operate with strategic alignment to your IT vision, empowering leadership through effective strategic planning.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
