Third-Party Risk Reporting: Turn Vendor Data Into Board Decisions
Fix third-party risk reporting to the board, tie vendors to business services, show trend and confidence, then ask for accept, reduce, transfer, or replace.


In third-party risk management, your vendors don't just support the business, they often run it. They host customer data, process payments, manage payroll, ship products, and keep core apps alive. So when a third party fails, it doesn't feel like a cybersecurity issue. It shows up as downtime, missed revenue, legal exposure, and a trust problem you can't quickly unwind.
Still, most organizations report vendor risk the same way they conduct vendor risk management: questionnaires, SOC reports, security ratings, and sprawling spreadsheets. The result is predictable. The board gets noise instead of clarity, and leaders start tuning it out until something breaks.
You can fix that by reshaping third-party risk reporting to the board of directors into something directors can use. Instead of a vendor catalog, you bring a decision tool. You connect vendor risk to business services, show exposure and trend (not one-off scores), and ask for a clear choice: accept, reduce, transfer, or replace. That's when vendor data turns into board decisions that protect revenue, uptime, trust, and disclosure readiness.
Key takeaways you can use in your next board update
These TPRM takeaways streamline board reporting:
Lead with business services, not vendor names, so directors see what could stop revenue or operations.
Report a short "critical vendor" tier, and keep the rest in management reporting to reduce distraction for board members.
Show trend and exposure, not single scores, because one rating rarely explains real business risk.
Pair every top vendor risk with a decision path, accept, reduce, transfer, or replace, with an owner.
Separate "risk level" from "confidence", so the board knows when the data is thin or stale.
Make exceptions visible until closed, with dates, owners, and what happens if deadlines slip.
Use reporting to strengthen governance, oversight and accountability, and confidence, because boards trust what they can inspect over time (including finding hidden value in cyber metrics).
Start with what the board actually decides, then work backwards to the vendor data
If your board packet reads like a vendor audit file from your third-party risk management process, you're asking directors to do the wrong job. The board doesn't exist to interpret SOC 2 language, debate questionnaire scores, or sift through raw risk assessments. Directors exist to make high-stakes calls with incomplete information, and to make those calls consistently.
So begin by naming the decisions your board or a committee actually owns. Then shape vendor reporting around those decision points:
Approve risk appetite and thresholds (what "in tolerance" means for critical vendors).
Fund risk reduction when exposure is real and time-bound.
Approve exceptions when the business accepts risk for speed or cost.
Set accountability, including who owns remediation of internal controls and who can grant extensions.
Decide when to exit a vendor or pause a rollout because risk stays out of bounds.
Oversee incident readiness, especially dependencies you don't control directly.
Once decisions are clear, scope gets easier. Third-party risk reporting to the board should focus on critical vendors, meaning vendors that support critical activities and can (1) stop a business service, (2) expose sensitive data, or (3) trigger regulatory compliance or contractual impact. Everyone else still matters, but they belong in management dashboards, not board time.
This is also where governance pays off. When decision rights and reporting expectations are explicit, your vendor program stops feeling personal or political. It becomes part of the operating system of oversight, which is the core idea behind cybersecurity governance for boards.
Define "critical vendor" in one sentence your leaders will repeat
Use a definition that fits in one breath:
A critical vendor is any third party whose failure could materially disrupt a core business service, expose sensitive data, or create a major compliance or financial impact.
Then anchor it to three repeatable criteria as part of your due diligence:
Service criticality: If the vendor goes down, do you lose sales, operations, or patient care?
Data sensitivity: Do they store, process, or transmit regulated or high-value data?
Concentration risk: Are they a single point of failure (or the only realistic option)?
Keep the top tier small so reporting stays sharp. In many organizations, 10 to 30 vendors is enough for board visibility. For example, your payroll provider, EHR, cloud hosting platform, payment processor, or managed service provider often lands in this tier. If your "critical" list is 120 vendors, it isn't a tier, it's a catalog.
Translate vendor risk into the same language as enterprise risk
Vendor risk gets traction when it lines up with how leadership already talks about risk. That means you map third-party exposure into the same buckets your ERM program uses, such as financial, operational, legal, reputational, and safety.
Next, tie the vendor back to the company's objectives. A cloud provider issue isn't "vendor risk," it's a threat to uptime, customer experience, and revenue recognition. A marketing SaaS breach isn't "security posture," it's brand damage plus disclosure risk.
Use consistent scales across vendors and time, such as low to critical. Also state your assumptions in plain language. When directors can see assumptions, they can challenge them, which improves decisions instead of turning meetings into debates about scoring math.
Build a board-ready third-party risk report that is clear, comparable, and decision-driven
A strong third-party risk reporting to the board fits in 1 to 2 pages or 2 to 4 slides. It stays consistent month to month, so the board can spot drift. It also makes deep dives possible without dragging everyone into detail.
Think in three layers for executive-level reporting:
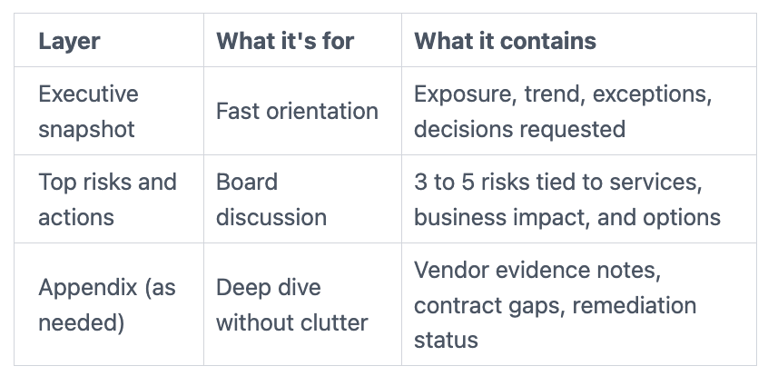
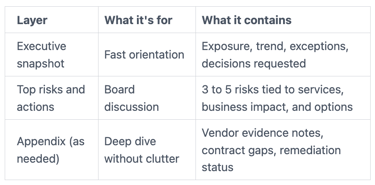
Before you build anything fancy, set a rule: the board view is not the evidence repository. It's the decision lens.
Avoid common traps that create more heat than light:
Long vendor narratives that read like account summaries.
Raw questionnaire totals without context.
Security ratings presented as truth, without validation.
Green dashboards with no exceptions, no uncertainty, and no tradeoffs.
Instead, aim for reporting that makes it hard to hide. If you want a model for making reporting honest enough to act on, use the framing from reporting cyber risk to the risk committee. The same discipline applies to third-party oversight.
If the board can't tell what changed, what matters, and what you want them to decide, you don't have reporting yet. You have documentation.
Use a one-page dashboard: exposure, trend, and where you need a decision
Your TPRM dashboard should read like flight instruments, not a novel. Keep sections stable each quarter:
Start with coverage and exposure:
Total critical vendors in scope.
How many are out of tolerance (and how that changed since last quarter).
Concentration risk, such as top five vendors by business impact.
Then show change:
New critical vendors added (and why).
Vendors that improved or degraded, with the driver.
Major open actions, with owners and due dates.
Finally, include a "Decisions requested" box with one to three items. Each item should offer options, cost ranges, and a recommended path. For example, approve a time-bound exception, fund a control, or authorize an exit plan. When you limit decision asks, directors can focus and follow through.
Make scores meaningful by pairing them with impact and confidence
A single vendor risk score can mislead because it hides the "why." It also tempts leaders into false precision, like a 7.2 versus a 7.6 matters. What matters is impact, likelihood, and how confident you are in the data.
Use a simple view, either a 2x2 (likelihood vs impact) or a three-factor summary:
Likelihood: How plausible is a negative event in the next 12 months?
Impact: What happens to revenue, operations, trust, or legal exposure?
Confidence: How good is your evidence?
Confidence is the missing piece in most third-party risk reporting to the board. Label it clearly when data is thin, outdated, or self-reported.
Call out evidence sources in plain terms, such as SOC 2, ISO certificates, pen test summaries, SLA history, incident history, or recovery test results. Then connect those inputs to outcomes using the same logic you use for executive metrics, including guidance on measuring security's business impact.
Close the loop: turn the report into action, contracts, and resilience
Board reporting is only useful if it changes what happens next week. That means you turn "risk noted" into risk mitigation through a plan with owners, deadlines, and proof.
Start by converting each out-of-tolerance vendor into one of four paths: accept, reduce, transfer, or replace. Then make the path visible until it closes. A vendor shouldn't disappear from reporting because it became awkward.
Next, connect actions to the levers that actually move vendor risk:
Remediation plans with measurable outcomes (not just "work in progress").
Contract changes and enforceable SLAs, especially around incident notice and recovery.
Segmentation (what access they have, what data they can touch, what environments they enter).
Offboarding plans so "replace" is real, not theoretical.
Incident path testing so you don't discover gaps during a crisis.
Vendor risk also shows up during incidents as confusion and delay. Boards reduce that risk when they set expectations for how dependencies behave under pressure, which ties directly to board oversight of incident response.
What you do when a vendor is out of tolerance (without creating panic)
When a critical vendor lands out of tolerance, you don't need drama. You need a controlled choice with a time limit.
Use four options and write down who can approve each one:
Accept: Approve a time-bound exception with an expiry date and named owner.
Reduce: Require internal controls and deadlines, then track completion with evidence.
Transfer: Shift exposure using insurance, indemnity, or stronger contractual terms.
Replace: Start an exit plan, including data return, cutover steps, and timeline.
Keep exceptions visible until they close. Otherwise, "temporary" becomes permanent, and reporting turns into wishful thinking.
Bake risk into vendor management, not just security reviews
You'll get better results when third-party risk becomes a shared workflow, not a security side quest. Procurement, legal, IT, privacy, and security should follow the same simple flow: intake, tiering, due diligence, onboarding controls, ongoing monitoring, and renewal gates.
Plain contract terms do a lot of heavy lifting, especially when shaped by smart contract negotiation. Focus on clauses leaders can understand:
Breach notice windows (hours, not "reasonable time").
Audit rights and access to evidence.
Subprocessor transparency (who else touches your data).
Recovery objectives that match your business continuity tolerance.
When you put those expectations into the normal purchasing cycle, board reporting gets easier. You're no longer chasing vendors after the fact.
FAQs directors and executives ask about third-party risk reporting to the board
How often should you report third-party risk to the board?
Use a simple cadence. Report to the full board or a committee quarterly with trends, exceptions, and decisions on cybersecurity risks. Run monthly management reporting with ongoing monitoring to keep actions moving. Escalate immediately for defined triggers, such as a critical vendor outage, a major incident like a data breach, or a material control failure.
Should you rely on security ratings scores?
Treat ratings as a signal, not a decision. They can highlight unknown vendors, drift, or basic hygiene issues. Still, they miss context, shared responsibility boundaries, and compensating controls. Pair ratings with validated evidence in information security and a confidence label to avoid false precision.
What is the minimum a board needs to see to make a decision?
Keep it tight: the business service at risk, the operational risk impact, the timeframe, options with cost and tradeoffs, and who owns the plan. Directors shouldn't have to ask ten questions to get those basics. If you want stronger prompts to pressure-test the story, pull from these audit committee cyber risk questions.
How do you handle fourth-party risk without boiling the ocean?
Focus on critical vendors' key subprocessors, not every dependency in third-party relationships. Require transparency for the vendors that matter most, especially where they create concentration risk. Then tie that visibility back to critical business services, not abstract supply chain maps.
How do you prove progress over time?
Track a small set of trends: critical vendors out of tolerance, exception aging, remediation cycle time, and cybersecurity incident or outage performance tied to vendors. Trend beats snapshots because it shows whether your system works. For a board-ready way to keep this measurable, align to CISO performance metrics the board can oversee.
Conclusion
You don't need more vendor data. You need a method that turns vendor inputs into strategic decision-making for the board. Start with decisions, tier vendors, report exposure with trend and confidence, and close the loop with risk assessment, owners, and deadlines. Then use the next board cycle to replace long vendor lists with a short dashboard and a tight decision box.
When third-party risk reporting to the board becomes decision-driven, you reduce surprises, speed up action, and strengthen your security posture. You also make trust easier to defend in supply chain security when something goes wrong. If you want help tightening that reporting and risk management lifecycle, consider working with a cybersecurity board advisor who can keep the conversation business-first, outcome-based, and focused on third-party relationships rather than technical vulnerabilities.


