Why Cybersecurity Governance for Boards Breaks Down Despite Reporting
Learn why cybersecurity governance for boards breaks down despite regular reporting, and how you can spot weak ownership, thresholds, and escalation.


Cybersecurity governance for boards breaks down when reporting creates motion, not judgment. You may receive dashboards, scorecards, and incident updates every quarter and still lack a clear picture of what the business is exposed to, who owns the risk, and what decisions belong to you.
That gap is more common than many leaders admit. Reporting can make you feel informed while leaving the company poorly governed. You see activity, but not consequence. You hear updates, but not thresholds. You get status, but not accountability.
If you lead under pressure, that is a dangerous mix. It delays decisions, blurs ownership, and makes escalation messy when time matters most. The sections below show what is actually failing, why leaders miss it, and what to fix first.
Key takeaways boards should keep in view
Reporting is not the same as governance. A board packet can be full and still be weak.
Polished dashboards often hide blurry ownership, vague risk decisions, and silent drift.
Many boards get status updates when they need decision-ready insight.
If escalation thresholds are unclear, bad news arrives late or arrives in a panic.
Good governance gives the board clearer decisions and management clearer accountability.
Better oversight starts when you ask what changed, what exceeds tolerance, and who owns the next move.
Why boards can get regular cyber reporting and still miss what matters
The central problem is not lack of data. It is lack of decision-useful reporting.
Many teams report what they can count. That usually means patch totals, training rates, control coverage, or open tickets. Those items may matter to management. Still, they rarely tell you whether business exposure is rising, whether recovery is credible, or whether a risk now sits outside tolerance.
This is why frequent reporting can create false confidence. A board sees color-coded charts and assumes the basics are covered. Meanwhile, the real issues sit off the page, vendor concentration, unresolved exceptions, weak recovery, or a risk that no one has formally accepted.
A short comparison makes the problem plain:
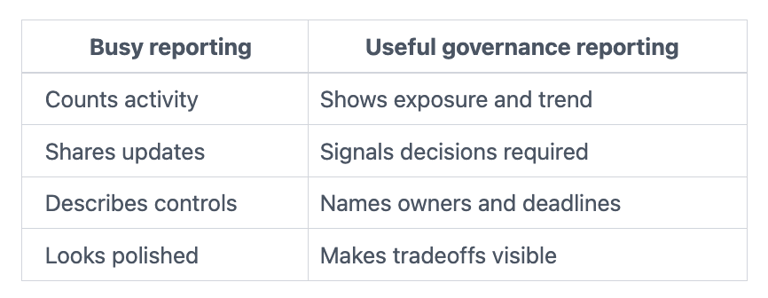

If you want a stronger model for cyber risk board reporting, start by testing whether your current materials explain business impact, movement over time, and the cost of delay.
The board sees metrics, but not the real business story
Raw security metrics often miss the point. Patch counts do not tell you whether crown-jewel systems remain exposed. Training completion does not tell you whether your people report threats faster. Tool coverage does not tell you whether a major outage would stop revenue.
You need the business story behind the number. What changed since the last meeting? Which gaps still matter? Where is concentration risk building? What would happen if the current plan slips by 90 days?
Without that translation, the board sees heat but not shape. That makes oversight shallow, even when the deck is long.
Updates are shared, but decisions are still unclear
Governance also breaks when reporting does not separate information from decision support. You may hear that a risk is "high," yet no one states whether it exceeds appetite, who approved that position, or what the board must decide now.
That is the hidden failure. Information tells you something happened. Decision support tells you what it means, who owns it, and what needs approval or escalation.
When that distinction is missing, meetings drift. Directors ask for more data, management offers more detail, and nobody leaves with a sharper decision record.
The real reasons cybersecurity governance for boards breaks down
Most failures in cybersecurity governance for boards are structural, not technical. They come from the way work is organized, framed, and pushed upward.
Ownership is blurry across the board, management, and vendors
Cyber risk often sits across the CIO, CISO, COO, legal, finance, audit, and outside providers. Because of that, responsibility can look shared while accountability is missing. One leader owns tools. Another owns operations. A third owns disclosure. Meanwhile, no one clearly owns the business decision when risk remains open.
In that setting, reporting becomes performative. Everyone can point to activity. Few can point to a named risk owner with decision authority.
Vendor-heavy environments make this worse. Outsourcing a function does not outsource accountability. If a critical supplier fails, customers and regulators still look to you.
Risk appetite is vague, so reports cannot show what is off track
If your board has not defined what "not acceptable" looks like, reporting cannot tell you much. Management can show movement without showing whether the company is inside or outside its boundaries.
That leaves you unable to tell the difference between normal fluctuation and a real governance issue. A delayed remediation plan may be tolerable, or it may cross a line. A third-party gap may be manageable, or it may sit well beyond what the business should accept.
That is why clear thresholds matter. When you set cyber risk thresholds, reporting becomes easier to read and harder to soften.
Board reporting is built for reassurance, not challenge
Many reports are designed to reduce friction. They smooth complexity, compress uncertainty, and present a calm story. Usually, that is not dishonesty. It is a design flaw.
Management often wants to avoid confusion. Security leaders may also fear overwhelming the board with technical detail. So the packet gets polished, simplified, and drained of tension. The result looks clean, but it no longer helps directors probe weak spots.
Good governance needs challenge built into the format. You need to see unresolved exposure, exceptions nearing expiry, dependencies that could fail together, and areas where management needs board air cover or board pressure.
For broader board cyber governance best practices, the pattern is consistent, clear ownership, clear thresholds, clear review cadence.
What good board cyber governance looks like when reporting actually works
When reporting works, it reduces ambiguity. It does not make cyber risk disappear. It makes decisions cleaner, ownership sharper, and escalation calmer.
Good reporting shows change, consequence, and who owns the next move
A useful board report starts with change. What is worse, what is better, and why? Then it connects that movement to business effect, revenue, downtime, customer harm, legal exposure, or missed strategy.
After that, it shows ownership. Who is accountable for the open issue? What action is underway? What remains unresolved? What support or approval is needed from the board?
This is where good reporting earns trust. It highlights exceptions, trend lines, and decision points. It does not drown you in tool detail. If you need a sharper model for management and board roles, board-ready cyber governance insights can help frame that boundary.
The board and management know exactly where oversight starts and ends
The board does not need to run security operations. It does need a clear view of material risk, readiness, and escalation triggers. That means management owns execution, while you own oversight of thresholds, funding tradeoffs, and risk acceptance at the right level.
In practice, that looks simple. Management can explain what sits outside tolerance, what decision rights are delegated, and what would trigger immediate escalation. You can challenge the reasoning without drifting into operations.
Incident readiness is a good test. If the company cannot explain when the board is informed, what facts arrive first, and who can make high-impact calls, governance is still weak. Strong board incident response oversight removes that uncertainty before a high-pressure moment does it for you.
What you should ask before the next board meeting
Before the next meeting, press for answers that clarify ownership and exposure fast. Keep the questions short. Require plain answers.
What changed since the last board update, and why does it matter to the business now?
Which risks currently sit outside our tolerance, even if only temporarily?
Who owns each top cyber risk, by name and role, not by function?
What would trigger escalation to the CEO, committee chair, or full board?
Where does vendor dependence create single-point failure or hidden concentration risk?
Which open issues have been accepted, deferred, or left unresolved without a formal decision?
What does management need from the board right now, funding, direction, risk acceptance, or escalation support?
Those questions do something important. They cut through activity and force a governance answer. They also reveal whether your reporting system supports real oversight or only creates the appearance of it.
FAQ: Short answers to the questions leaders usually ask next
Is more reporting the answer?
No. More reporting usually adds noise. Better reporting gives you clearer choices, ownership, and thresholds.
How often should the board review cyber risk?
You should review a short, stable cyber view at each regular board or committee cadence. Then go deeper quarterly on major shifts, open exposures, and readiness.
What should be in a board-level cyber report?
It should show what changed, business impact, risks outside tolerance, accountable owners, unresolved exposure, trend lines, and any decisions needed from you.
Who should own cybersecurity governance for boards?
The board owns oversight. Management owns execution. Within management, named executives should own business risk outcomes, not only the security team.
Cybersecurity governance for boards does not fail because you lacked reports. It fails because the reports did not improve judgment, accountability, or escalation.
If you want a practical next move, review your next board packet before the meeting and ask three things. Does it help you make a clearer decision? Does it show rising exposure early enough to act? Does it make ownership unmistakable?
If the answer is no, fix the reporting design before the next high-pressure moment. That is usually where governance breaks, and where you still have time to correct it.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
