Cybersecurity Governance for Boards: A Practical Framework That Holds Up Under Pressure
Cybersecurity governance for boards gives you clear oversight, decision rights, and escalation triggers, so you're ready before pressure hits.


Cybersecurity governance for boards is not about turning directors into security experts. It is about giving you clear visibility, defined decision rights, a repeatable oversight rhythm, and confidence that management is handling material cyber risk well.
That matters because weak oversight carries real business cost. You can see it in operational disruption, legal exposure, damaged trust, slower growth, failed diligence, and poor executive calls made with thin facts.
If you sit on a board or support one, the goal is simple. You need a governance model that helps you see what matters, decide what you own, and avoid being surprised late.
Key takeaways boards can use before the next meeting
You should see cyber risk in business terms, not tool terms.
You own oversight, thresholds, and challenge; management owns execution.
You need a small set of board-ready metrics that show change and exposure.
You should define escalation triggers before an incident forces the issue.
You should revisit risk appetite, ownership, and reporting on a steady cadence.
If your board packet can't show what changed, who owns the gap, and what decision is needed, it isn't governance yet.
What cybersecurity governance for boards actually means
Cybersecurity governance for boards is the system you use to direct, oversee, and hold management accountable for material cyber risk. It is not the security program itself. It is also not the same as compliance.
Compliance asks whether you met a rule. Governance asks whether leadership can see risk clearly, make sound tradeoffs, and respond well when pressure rises.
Many boards struggle because the material they get is busy but not useful. Reports often contain technical detail, maturity language, and dashboards with no clear decision path. Ownership can also blur across the CEO, CIO, CISO, legal, operations, and committee structure. When that happens, everyone works, but few people decide.
If you want a clearer benchmark for board cyber governance practices, start with the basic test: can the board explain top cyber risks, their business effect, and who owns them?
The board governs risk, management runs the program
Your board should approve risk appetite, oversight structure, escalation thresholds, and major funding tradeoffs. You should review trend reporting, unresolved gaps, major incidents, and material exceptions.
Management should own control design, staffing, vendor management, incident execution, and day-to-day risk reduction. That line matters. If the board stays too passive, risk drifts. If the board dives into tactics, accountability blurs.
Good oversight is neither distant nor hands-on. It is disciplined.
Why cyber becomes a board issue before a crisis
Cyber becomes a board issue well before a breach. It affects uptime, customer trust, product delivery, vendor dependence, AI use, acquisitions, and disclosure readiness.
A company can miss revenue targets because a core system fails. A deal can stall because diligence reveals weak control and poor recovery confidence. A major vendor can become a single point of failure. By the time a serious incident lands, your governance model has already been tested.
The five-part framework for stronger board oversight
A practical framework does not need to be large. It needs to be clear enough to use every quarter.
The table below shows the difference between weak and strong governance.
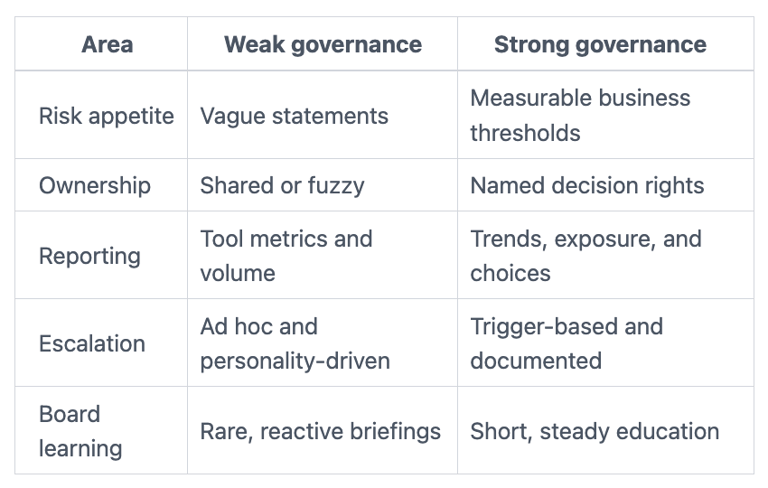

The takeaway is simple. Strong governance is easier to repeat because it is easier to understand.
Set risk appetite in business terms, not security jargon
Risk appetite should describe what level of harm you will tolerate, and what you will not. That means talking about downtime, critical systems, vendor dependence, data exposure, and recovery expectations.
For example, you can define how long a customer-facing system can be down before the issue becomes board-level. You can define which data exposures are never acceptable. You can define how much third-party concentration risk you will accept.
That is far more useful than broad statements about having a "low" cyber appetite. If you need help setting technology risk appetite in business terms, start with the business services you cannot afford to lose.
Define who decides, who reports, and who escalates
Most governance failures are ownership failures. If no one knows who decides, then decisions get delayed, defaulted, or made in the wrong place.
You need clear roles across the board, the audit committee where relevant, the CEO, CIO, CISO, legal, and operations. During normal operations, management should know who owns each top unresolved risk. During an incident, leaders should know who can declare severity, shut systems down, approve outside counsel, and notify the board.
Blurry ownership creates comfort right up until it creates surprise.
Use board reporting that shows change, exposure, and decisions needed
A board-ready cyber report should answer a short set of questions. What changed this quarter? What remains exposed? What is improving? What is slipping? What decision or support is needed from leadership?
That means showing top risks, trend lines, material gaps, control progress, incident activity, third-party exposure, and current recovery posture. It does not mean dumping alert counts or long lists of vulnerabilities into a deck.
If you want a model for board reporting that translates cyber risk into business impact, keep the report short enough to read in minutes.
Make escalation and incident oversight predictable before something breaks
A serious incident is a bad time to debate who calls the board, what "material" means, or who owns external communications.
You should define notification triggers in advance. You should also know what the board will receive in the first 24 to 72 hours of a serious event: confirmed facts, business impact, actions underway, decisions needed, and next update time.
That is governance readiness. It is different from the operational playbook, and it matters just as much. Strong board incident response oversight removes guesswork before pressure spikes.
Build board fluency so oversight improves over time
You do not need every director to be technical. You do need enough shared understanding to challenge weak reporting and weak assumptions.
Short briefings help. Tabletop exercises help more. So does a steady rhythm of plain-English updates on new exposure from business changes, key vendors, cloud concentration, and AI use.
Board fluency is not about mastering cyber detail. It is about making better judgments with less noise.
Where cybersecurity governance usually breaks down
Most boards do not fail because they do not care. They fail because the structure makes weak oversight feel adequate.
Too much reporting, not enough decision support
Volume creates false comfort. A thick deck can hide the fact that no one can answer what changed, what matters now, or what support management needs.
Maturity scores, tool counts, and patched-ticket totals often bury the real story. Meanwhile, the board misses rising vendor dependence, repeated exceptions, stale recovery assumptions, or a growing backlog around critical systems.
You need signal, not noise.
Good people, weak structure, unclear accountability
Capable teams can still produce weak outcomes when ownership is split, vendors shape decisions, or no executive is clearly accountable for enterprise cyber risk.
That creates governance drift. The board hears that work is moving. Management believes someone owns the hard calls. Then a high-pressure moment exposes that nobody had the full mandate.
Good people are not enough. Good structure matters.
Questions boards should ask to pressure-test the framework
The right questions expose whether your governance model is real or only well-presented. If you want a sharper set of audit committee cyber questions, use them to test visibility, ownership, and readiness.
Questions that test visibility, ownership, and readiness
What changed in our cyber risk picture this quarter, and why?
Who owns our top unresolved cyber risks, by name and role?
What would trigger immediate board escalation?
Where are we most dependent on key vendors, and what is the fallback?
Can management show recovery confidence in business terms, not only technical terms?
Which current risks are we accepting, and when do those exceptions expire?
Strong answers are short, direct, and evidence-backed. Weak answers sound broad, shared, or delayed.
How to put this framework in place without slowing the business down
You do not need a perfect model on day one. You need a usable starting point that gets better through repetition.
Start by clarifying oversight scope. Then set expectations for reporting. Next, define escalation triggers and decision rights. After that, review the framework every quarter and adjust it as the business changes.
This kind of structure does not slow the business down. It supports speed because leaders waste less time guessing. It also builds trust because everyone knows what matters, who decides, and when the board gets pulled in. If you want an outside view on where blind spots often hide, a cybersecurity governance advisor for boards can help pressure-test the model fast.
FAQ: common questions leaders ask about board cyber oversight
Does every board need a cyber expert?
Not every board needs a full-time cyber specialist. Every board does need access to credible cyber judgment, whether through a director, advisor, or committee support.
How often should the board review cyber risk?
You should review a concise update at each regular meeting, or at least quarterly. Material incidents, major business shifts, and large technology changes should trigger extra review.
What belongs with the audit committee versus the full board?
The audit committee often handles deeper review of reporting, controls, and follow-up. The full board should handle material risk appetite, major incidents, large tradeoffs, and overall accountability.
How technical should board reporting be?
Only technical enough to support a business decision. If directors cannot explain the issue in plain English, the reporting needs work.
A clearer board packet starts here
Cybersecurity governance for boards works when oversight is clear, reporting is decision-useful, and escalation is defined before pressure hits. That is what gives you calmer decisions when facts are incomplete and stakes are high.
Before your next meeting, review the board packet against the five-part framework. Then ask management to clarify ownership, risk thresholds, and escalation triggers where the material is still fuzzy. That one step can move your board from informed-looking to actually ready.
Author bio: Tyson Martin advises boards, CEOs, and executive teams on cyber risk, technology governance, AI oversight, and operational resilience. He helps leaders make clearer, faster, and more defensible decisions when visibility, ownership, and trust start to break down.
Sources referenced:
U.S. Securities and Exchange Commission, Cybersecurity Risk Management, Strategy, Governance, and Incident Disclosure
NIST Cybersecurity Framework 2.0
CISA guidance on cyber incident preparedness and response
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
