Cybersecurity Governance for Boards: The Questions Directors Should Be Asking
Strengthen cybersecurity governance for boards with sharper questions on ownership, reporting, and readiness, so you can test real oversight.


Directors don't need to become security experts. You do need a clear way to test whether oversight is real, whether management has control, and whether the company can make sound decisions when pressure rises.
That is the heart of cybersecurity governance for boards. It is not a technical side topic. It affects uptime, customer trust, growth plans, legal exposure, and the quality of decisions made in the hardest moments.
If your board packet is thick but your answers are still fuzzy, governance is weak. The fix is usually not more data. It is clearer ownership, better reporting, and sharper questions from the board.
Key takeaways boards can use before the next meeting
Good governance is about accountability, not slide count.
The board owns oversight; management owns execution.
Reporting should show what changed, what matters now, and what needs a decision.
Escalation thresholds matter because surprise is usually a governance failure first.
You need proof of readiness, not reassurance from management.
A short standing set of board questions beats a once-a-year cyber presentation.
What strong cybersecurity governance for boards actually looks like
Strong governance is not the board trying to run security operations. It is the board making sure risk ownership is clear, reporting is useful, escalation works, and cyber decisions match business priorities. If you need a practical benchmark, Board Cyber Governance Best Practices 2026 offers a helpful reference point.
The board owns oversight, management owns execution
When roles blur, control weakens. The board should not decide which tools to buy or how to configure response teams. You should decide what levels of disruption, loss, and exposure are unacceptable, who is accountable for top risks, and when management must escalate.
This simple split helps:
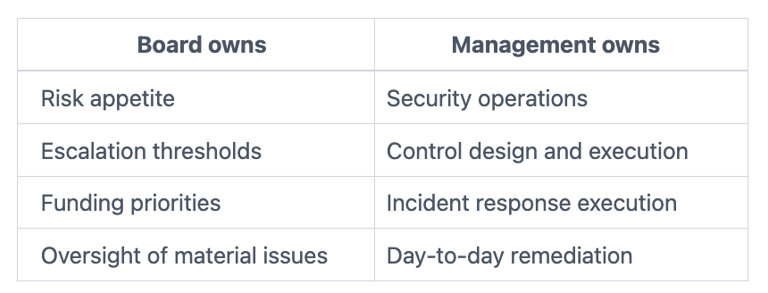
That sounds basic, but it often breaks down. The CEO may assume the CISO owns everything. The CISO may depend on the CIO. Legal may expect to be pulled in early, but operations may not know when. Meanwhile, business leaders may treat cyber as someone else's problem. Your job is to test whether accountability is clear across all of them.
Good reporting helps you make decisions, not just admire activity
Many board updates are full, but not useful. They show patches, alerts, training rates, and project status. They say little about business exposure.
Useful reporting is different. It shows trend lines, material changes, unresolved gaps, and the decisions that now belong at board level. It also explains business impact in plain language. If you want a model for that kind of reporting, these decision-ready cyber briefings show what better translation looks like.
If a report doesn't help you decide, it isn't governance material yet.
The questions directors should ask to test whether governance is real
A good board question is not a technical quiz. It is a pressure test. It tells you whether management can explain risk clearly, assign ownership, and act under stress.
Do we know which cyber risks matter most to the business right now?
Start with business exposure, not tools. Ask management to name the few risks most likely to disrupt revenue, operations, customer trust, or strategic plans. Ask which systems are true crown jewels. Ask which vendors could stop the business. Ask what changed since last quarter.
You are listening for prioritization. If everything is critical, nothing is. If every answer sounds high-level, management may not have a stable risk picture.
This is also where risk appetite matters. You need a shared view of what is acceptable and what is not. That includes downtime, data loss, vendor dependence, and the cost of delay. Work on defining cyber risk appetite and escalation thresholds can sharpen this discussion fast.
Most of all, connect cyber risk to business consequence. A weak identity control is not the board issue. The board issue is whether it could halt billing, expose customer data, or slow a major launch.
Who is accountable when risk crosses the line from acceptable to urgent?
Governance gets real when thresholds are crossed. Who decides that a cyber issue has become urgent? Who informs the CEO? When does the board chair get pulled in? Who can approve a major shutdown? Who can accept temporary risk, and for how long?
You want clear decision rights, not a polite story about teamwork.
Weak governance usually sounds like this: "We work closely together." Strong governance sounds different: "The COO owns recovery priorities. The GC owns legal posture. The CISO leads response. The CEO makes enterprise tradeoffs. The board is notified when these triggers are met."
Ask how management defines a material issue in your business terms. Then ask where those thresholds are documented. If the answer depends on who is in the room that day, the model will fail under pressure.
Are we seeing evidence of readiness, or just hearing reassuring updates?
Readiness leaves evidence. Promises do not.
Ask when the company last tested backup restore for critical systems. Ask what the last tabletop exercise exposed. Ask which lessons remain open. Ask how third-party incidents would be handled. Ask whether legal, communications, operations, and security have practiced together.
You are not asking for perfect readiness. You are asking for proof that the company can absorb a hit, recover, and communicate with discipline. The Board Incident Response Oversight guide is useful here because it focuses on decision rights and evidence, not theory.
A calm board question can reveal a lot: "What failed in the last exercise, and what changed because of it?" If management cannot answer that plainly, you are hearing comfort, not readiness.
Why boards still miss cyber risk even when updates are regular
Regular reporting can create false confidence. Frequency is not the same as quality. Some boards hear about cyber often and still miss the real story because the signal never gets clear.
The report is full, but the signal is weak
Dashboards often reward volume. You see activity, compliance status, and project motion. What you may not see is business exposure, risk drift, or hard tradeoffs that management is avoiding.
A polished report can even make things worse. It can hide uncertainty and push uncomfortable issues off the agenda. That is why you should challenge updates that look neat but don't answer simple questions: What changed? What got worse? What still lacks an owner? What decision do you need from us?
Ownership is fuzzy across technology, security, legal, and operations
Some governance failures begin long before an incident. They start when response, recovery, communications, and vendor coordination all sit in gray areas.
If no one clearly owns those functions, the board cannot trust the operating picture. During a fast-moving event, that confusion turns into delay. Delay becomes cost, reputational damage, and sometimes bad disclosure choices.
That is why sharp oversight is less about hearing more and more about requiring clear lines of authority. Busy meetings do not fix fuzzy ownership.
How to build a better board conversation on cyber risk
The goal is not a bigger cyber section in the board deck. The goal is a cleaner discussion that helps you decide faster and challenge more effectively.
Ask for a simple risk picture, clear ownership, and the decisions that need board input
Management should come into the room ready to answer five things:
What changed since the last meeting
What matters most now
What management is doing about it
Where support or funding is needed
What decisions belong at board level
That format cuts noise. It also makes it harder to hide behind process updates.
If you want a sharper question set for that discussion, these board questions exposing cyber blind spots can help you tighten the conversation.
Use a short standing question set every quarter
A repeatable cadence works better than a once-a-year deep dive. Use the same core questions each quarter so you can track movement over time. That helps you spot drift early, compare answers, and see whether management is learning or repeating itself.
Keep it short. Ask about top risks, ownership changes, recovery evidence, major vendor exposure, and board-level decisions needed. Over time, that rhythm gives you something more useful than comfort. It gives you a stable view of whether governance is improving.
FAQ: Practical questions board members often ask about cyber oversight
How often should the board review cyber risk?
You should review a short, stable update at each regular board meeting. In addition, a deeper quarterly discussion usually makes sense when the business is changing fast.
What should be in a board cyber report?
You need top risks in business terms, what changed, who owns each issue, open gaps, evidence of readiness, and the decisions management needs from you. Leave tool counts and low-value metrics out.
Does every board need a cyber expert?
Not every board needs a dedicated cyber director right away. However, many boards do need stronger independent judgment. This guide on adding cyber expertise to the boardroom can help you think through that choice.
When should a cyber issue come to the board?
It should come up when it crosses agreed thresholds for business impact, legal exposure, customer harm, or strategic disruption. If you only hear about it after the story is already formed, your escalation model is too late.
Cybersecurity governance for boards gets better when you stop asking for more activity and start asking for clearer decisions. You do not need to master the technical detail. You need to see risk clearly, know who owns it, and require proof that the company can act under pressure.
Before your next meeting, pressure-test the board packet. Check whether it shows what changed, who is accountable, what evidence exists, and what decisions now belong to the board. That simple discipline is often where stronger governance begins.
Tyson Martin advises boards and CEOs on cyber risk, technology governance, AI oversight, and decision-making under pressure. He helps leadership teams improve visibility, clarify ownership, and make more defensible decisions.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
