Cyber Risk and Fiduciary Duty: A Plain-English Guide for Directors
Use this directors guide to cyber risk to improve your board oversight, ask better questions, and judge business impact clearly.


Cyber risk is a business risk. It can cut revenue, stall operations, create legal pressure, damage trust, and distract leadership at the worst possible time.
As a director, you do not need to become a security expert. Your job is to exercise informed oversight, ask clear questions, and make sure the company can identify, report, manage, and escalate material risk in time. This directors guide to cyber risk is built for that job.
Key takeaways for busy directors
Cyber risk is a governance issue, because technology now touches core business operations.
Fiduciary duty requires informed oversight, not technical mastery.
Weak reporting creates false confidence, especially when updates show activity but hide exposure.
Management owns execution, while the board owns oversight, challenge, and escalation expectations.
Your goal is better decisions under pressure, not more jargon in the board packet.
Perfect security is unrealistic. Your duty is informed oversight and timely challenge.
Why cyber risk belongs in the boardroom, not just in the server room
Years ago, many boards treated cyber as an IT matter. That view no longer fits how companies operate. Revenue depends on systems. Operations depend on software. Customer trust depends on how data is handled. Vendor outages can become your outage in a day.
A ransomware event can halt fulfillment. A vendor failure can block payroll or billing. Data exposure can trigger legal review, customer churn, and regulator attention. Prolonged downtime can hurt deal readiness and financing conversations. Because the business depends on technology, the board has to oversee whether leadership knows what matters most and whether the company is prepared.
The business harms that matter most to directors
You do not need a technical breakdown of malware families or control frameworks. You need to understand business harm. The main harms are usually cash flow disruption, stalled operations, legal and disclosure pressure, damaged trust, customer loss, and leadership distraction. When cyber conversations stay at the tool level, those harms get buried. When they shift into business terms, you can govern them.
What fiduciary duty looks like in a digital business
In simple terms, duty of care means you stay informed, ask reasonable questions, and challenge weak assumptions. It also means material risk should reach the board early enough for action. This is a practical governance point, not legal advice. You are trying to build a record of thoughtful oversight, clear decisions, and follow-through. That is the core of strong board cyber governance practices.
What directors need to understand, even if they are not technical
Cyber risk is the chance that technology, data, systems, vendors, or digital processes fail, are attacked, or are misused in ways that hurt the business. That includes hostile acts, but it also includes weak recovery, bad access control, poor vendor dependence, and fragile operations.
You should also separate a cyber event from cyber risk posture. An event is one incident. Risk posture is the broader picture, how exposed the company is, how prepared it is, and how fast it can recover. A company can avoid a major incident for years and still carry a weak posture. Another company may suffer an incident and still show strong governance because it detected, escalated, and recovered well.
The plain-English building blocks of cyber risk
This simple framework keeps the discussion grounded:
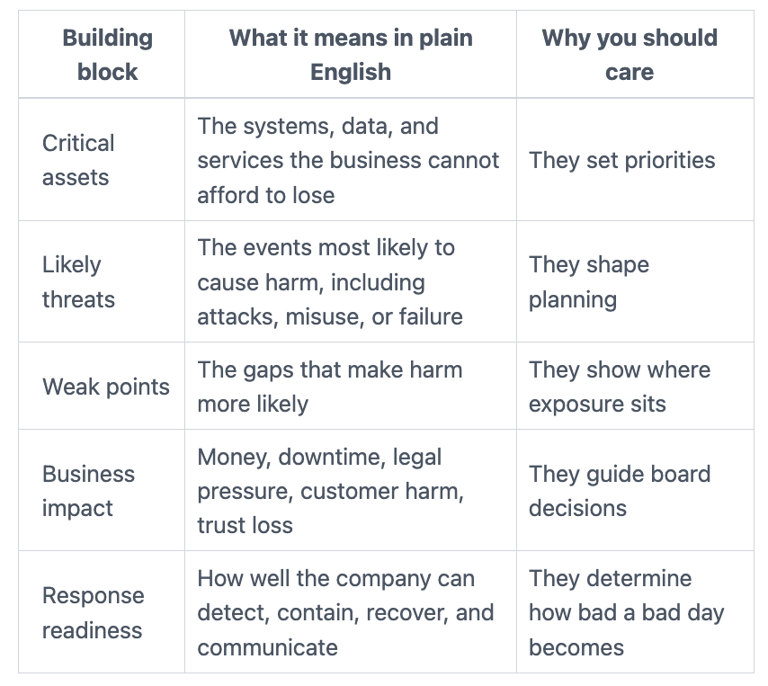
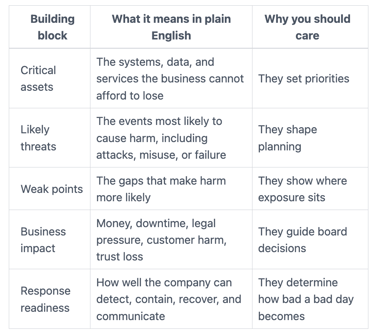
The standard is not perfection. The standard is disciplined oversight around these few moving parts.
How to tell the difference between noise and a real board issue
Most boards do not suffer from too little data. They suffer from too much data and too little translation. Patch counts, tool names, and long control lists rarely help on their own. What matters is trend, business exposure, accountability, and whether management can explain what changed.
A useful board update should tell you the top risks, why they matter, who owns them, what is getting worse or better, and where a decision is needed. That is the discipline behind translating cyber risk into business impact for the board. If the update cannot help you decide, it is not board-ready.
Where oversight usually breaks down, and how you can spot it early
Boards usually get exposed through ordinary failure, not dramatic failure. Reporting is vague. Ownership is blurry. Risk appetite is implied rather than defined. Vendor dependence is treated as procurement, not business risk. Incident plans exist, but nobody knows what the board would actually see in the first day of a real event.
These breakdowns are easy to miss because they often look organized. You may get a thick deck, a clean dashboard, and calm language. Yet the real gaps sit underneath: no thresholds, no named owner, no tested escalation path, no link between cyber updates and business decisions.
Warning signs that management reporting is giving you false comfort
Watch for these red flags:
The update is heavy on technical detail and light on business effect.
You see snapshots, but no trend over time.
Top risks are missing, or every item is labeled "high."
No threshold tells you when management must escalate to the board.
Major exposures have no clear owner.
The update does not connect to funding, tradeoffs, or decisions.
If several of these show up together, your reporting model needs work.
Why third parties and SaaS vendors can raise your risk
Your company may rely on outside providers for identity, payroll, payments, customer platforms, cloud hosting, or core operations. That means a vendor weakness can become your weakness, even if your internal team performs well.
You should ask where the business is too dependent on one vendor, one contract, one region, or one access path. You should also ask how fast a critical vendor must notify you of an incident, who validates their controls, and what fallback exists if they fail. Vendor oversight belongs in the same conversation as continuity and accountability.
What good board oversight looks like in practice
Strong oversight is simple enough to repeat. You have clear ownership. You have regular, board-ready reporting. You have defined escalation thresholds. You have tested incident roles. You also have a shared view of what risks the company is willing to accept.
That model creates calmer decisions because the rules are clearer before pressure rises. It also keeps the board out of day-to-day operations. You are seeking clarity, not volume. For example, a strong board incident response oversight guide focuses on decision rights, proof of readiness, and what the board must know early.
The few things you should expect to see in every board update
Every update should cover the same basics: top risks, what changed since the last meeting, likely business impact, progress on priority fixes, unresolved decisions, and any item that may need escalation. Consistency matters because it helps you spot drift early.
How risk appetite helps you govern without micromanaging
Risk appetite is the agreed level of risk the business is willing to live with in order to operate and grow. In practice, it means defining what levels of downtime, data loss, fraud, or vendor dependence are acceptable, and what levels are not.
Once those guardrails exist, management can execute within them and escalate when exposure moves outside them. That is how you govern without running the program. If your board has never defined those guardrails clearly, this guidance on how boards set technology risk appetite is a practical next step.
The questions you should ask before the next board meeting ends
Good questions matter more than technical vocabulary. You are testing visibility, ownership, readiness, and judgment.
Questions that test visibility and ownership
What are our top cyber risks right now, in business terms?
What changed since last quarter, and why?
Who owns each major risk, by name and role?
What decision or support does management need from the board now?
Questions that test readiness before an incident happens
Which business processes would hurt most if disrupted?
How quickly could we recover those processes in reality?
When did we last test incident roles, communications, and recovery?
Where are we too dependent on one vendor, one person, or one system?
If you want a fuller set of prompts for committee use, these audit committee cyber risk questions help keep the discussion sharp and useful.
Frequently asked questions from non-technical directors
Am I expected to be a cyber expert?
No. You are expected to be informed enough to oversee, challenge, and document decisions responsibly.
How often should the board review cyber risk?
A short, decision-useful update should appear regularly, often each quarter. Higher-risk periods may call for more frequent review.
What makes a cyber issue material?
Materiality depends on business impact. Revenue disruption, major downtime, legal exposure, customer harm, or trust damage can all make an issue material.
What should I do if reporting feels unclear or overly technical?
Ask for a rewrite in business terms. If management cannot explain the risk plainly, the board does not yet have a usable view.
Your next move is simple. Pressure-test the quality of reporting, ownership, escalation paths, and incident readiness at the next board or committee meeting.
You do not improve oversight by acting like the security team. You improve it by demanding a clearer view of what could materially hurt the business, who owns it, and when the board must act. Better governance starts with clearer questions, clearer reporting, and calmer decisions under pressure.
Tyson Martin advises boards and CEOs on cyber risk, technology governance, AI oversight, and operational resilience.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
