How to Set Technology Risk Appetite at the Board Level
Set technology risk appetite at the board level, so you give management clear limits, better escalation rules, and fewer costly surprises.


Tyson Martin advises boards and CEOs on technology, cyber risk, AI oversight, and decision clarity when stakes rise.
Your board-level technology risk appetite is the clear statement of how much technology risk you are willing to accept in pursuit of growth, speed, efficiency, and innovation. It is not a technical document. It is a leadership position.
If you do not define it, you still have one. It shows up by default in budgets, vendor choices, AI pilots, cloud changes, delayed fixes, and weak escalation. In other words, your company starts making risk decisions without ever saying so out loud.
That is why this belongs in the boardroom. You are not choosing tools. You are setting boundaries for acceptable business exposure, so management can move faster without guessing where the line is.
Key takeaways leaders should keep in view
Technology risk appetite is a leadership decision, not an IT artifact.
It should connect directly to growth plans, trust, downtime tolerance, and downside you can absorb.
A usable appetite needs thresholds, ownership, escalation rules, and reporting.
Your appetite should differ by category, including cyber, AI, vendors, major change, and operational recovery.
One broad statement is rarely enough, because different risks need different limits.
You should revisit it when strategy, scale, regulation, or dependency changes.
Why technology risk appetite belongs at the board level
Technology risk now touches capital allocation, growth plans, customer trust, and operating stability. That makes it a governance issue. The board is not there to set controls. You are there to decide how much exposure the business will accept while pursuing its goals.
That boundary-setting role sits at the center of board cyber governance best practices. It affects how management funds recovery, approves AI use, handles vendor concentration, and decides when bad news must rise quickly.
Without a defined appetite, you get uneven choices. One team accepts major vendor concentration to move faster. Another delays security work because the budget is tight. A third launches AI with weak review because no one said what was off-limits. Each decision may look reasonable on its own. Together, they create drift.
What technology risk appetite actually means in plain English
In plain English, technology risk appetite is your board-approved position on acceptable exposure. It says what you are willing to live with, and what you are not.
It is broader than a threshold. Appetite is the direction. Tolerance is the amount of variation you can handle. Capacity is the outer limit the business could survive. Thresholds are the trigger lines that make the whole thing usable. For example, you may have low appetite for customer data exposure, moderate appetite for short internal system outages, and almost no appetite for untested AI touching regulated decisions.
What goes wrong when the board leaves this undefined
When you leave this vague, management fills the gap with assumptions. Risk acceptance gets buried in project choices. Security teams report technical facts instead of business exposure. Directors receive activity, not clarity.
Then the real appetite only becomes visible after a failure. You learn it through a missed recovery target, a vendor outage, a weak escalation path, or a public AI mistake. By then, the company has already made the decision. It just made it the hard way.
Build your board-level technology risk appetite in five practical steps
You do not need perfect precision. You need a practical frame that improves decisions.
The goal is not a flawless statement. The goal is fewer surprises and better tradeoffs.
Start with business priorities, not a list of threats
Begin with what the business is trying to achieve. Are you scaling fast, integrating acquisitions, protecting trust, reducing concentration risk, or pushing AI into core work? Your appetite should reflect those choices.
Anchor the conversation in mission-critical processes, revenue exposure, customer expectations, and regulatory stakes. A company with aggressive growth goals may accept more change risk. A company built on trust and uptime may accept far less.
Choose the risk areas that need clear board boundaries
One enterprise statement is too thin on its own. You need a small set of categories where board limits matter. For most companies, that includes cybersecurity, data and privacy, AI use, third-party dependence, operational recovery, and major systems change.
Not every category deserves the same caution. You may accept moderate risk in internal experimentation, while keeping low appetite for outages in customer-facing operations. That is the point. A category-based view makes tradeoffs visible.
Turn broad intent into usable limits and triggers
Words like "low" and "moderate" help only if you translate them into triggers. Otherwise, they become comfort language.
Set a few limits management can report against. Examples include maximum downtime for critical services, acceptable recovery time after a major disruption, the share of critical vendors without backup options, or the number of high-risk issues allowed to remain open past deadline. You should also define trigger points for immediate board notice.
This is where board incident response oversight and risk appetite meet. If your limits are clear, escalation becomes calmer and faster. If they are fuzzy, every event becomes an argument about severity.
Assign ownership so decisions do not drift
The board approves the appetite. A committee, often audit or risk, challenges it and tracks it. The CEO aligns it to strategy. The CIO, CISO, legal team, and operating leaders help draft, test, and monitor it.
Weak ownership is one of the main reasons appetite statements fail. If no one owns reporting, updates drift. If no one owns escalation, bad news arrives late. Strong board reporting for cybersecurity program decisions makes the appetite visible in trend lines, exceptions, and decision points.
Review it when the business changes
Annual review is fine for a stable business. Many companies are not stable. Growth, M&A, leadership change, a large AI rollout, or a new vendor dependency can change your risk posture fast.
Therefore, treat technology risk appetite as a living governance tool. If the strategy changes, the appetite should change with it.
What a strong technology risk appetite looks like in practice
A strong statement is short, business-linked, category-based, and measurable where possible. It gives management room to operate, but it also gives the board a clear basis for challenge, reporting, and escalation.
Signs your current statement is too vague to guide decisions
You likely have a weak statement if everything is labeled high priority, nothing ties back to strategy, thresholds are missing, reporting never shows "in appetite" versus "out of appetite," and no one can say when the board must be informed. That is not governance. That is broad concern without usable direction.
A simple example boards can adapt without overcomplicating it
This comparison shows the difference between vague language and decision-useful language.
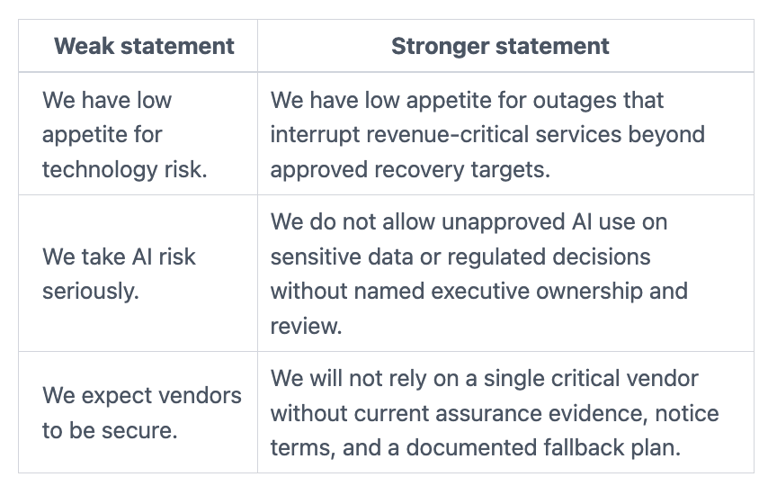
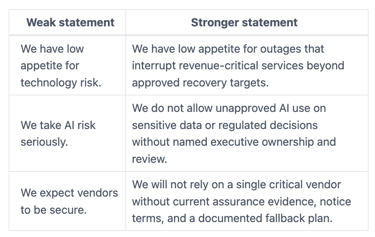
A simple structure works well: one short enterprise statement, followed by category statements for cyber, recovery, AI, and third-party risk. The wording matters less than whether it changes decisions.
Questions the board should ask before approving technology risk appetite
A strong approval discussion depends on better questions, not longer decks. If you need a sharper meeting frame, these audit committee cyber risk questions align well with technology oversight.
Board questions that test whether the appetite is real
What business outcomes are you protecting most?
Where are you choosing to accept more risk to move faster?
Which risks are you carrying because of cost, talent, or time limits?
What would trigger immediate board escalation?
How will you show that the company is operating outside appetite?
Those questions expose assumptions, tradeoffs, and ownership fast.
When to revisit your risk appetite, not just file it away
Revisit it after major growth, M&A, material incidents, leadership turnover, new AI use cases, major cloud or vendor concentration, or a shift in regulatory pressure. If the business is changing quickly, annual review alone is not enough. Risk appetite should move when operating reality moves.
FAQ: common board-level questions about technology risk appetite
Is technology risk appetite the same as cyber risk appetite?
No. Cyber risk appetite is one part of it. Technology risk appetite is broader. It also covers change failure, outages, data quality, concentration risk, and poor recovery.
How detailed should the board get?
Stay at the business boundary level. You should approve category limits, trigger points, and escalation rules. Management should map those choices to controls and execution.
Who should draft the first version?
Management should draft it, usually with input from the CEO, CIO, CISO, legal, and operating leaders. The board should challenge the draft, tighten the language, and approve the final position.
What if management and the board disagree on acceptable risk?
Treat that as a governance discussion, not a personality issue. The disagreement usually points to a real tradeoff around cost, speed, trust, or recovery. Record the decision, the reason, and the review date.
Technology risk appetite is not about sounding disciplined. It is about giving management clear boundaries, better escalation rules, and decision support when pressure rises. If you do this well, you reduce drift before it turns into surprise.
Your next move is simple. Ask management to bring a short draft to the next board or committee meeting, with category limits, trigger points, owners, and proposed reporting changes. A technology risk appetite becomes useful the moment it starts shaping real decisions.


