M&A Due Diligence Checklist: How to spot digital "Technical Debt" and hidden liabilities before the deal closes
Use this M&A Due Diligence Checklist to spot hidden technical debt before close, test management claims, and protect value, timing, and trust.


Your M&A Due Diligence Checklist should treat digital technical debt as a financial issue, an execution issue, and a trust issue. It includes old code, but it also includes weak architecture, thin documentation, unsupported systems, shaky vendors, security gaps, poor data controls, and unclear ownership.
Those liabilities matter before close because you inherit them. They can change valuation, delay integration, increase holdbacks, and weaken the basic case for the deal. If you want a sharper view of identifying digital liabilities in mergers, start with evidence, not confidence.
Key takeaways leaders should know before diligence starts
Technical debt hides in systems, data, contracts, security, and operating habits.
In a deal, hidden debt shows up later as cost, delay, outage risk, and leadership drag.
Fast timelines often reward smooth storytelling and weak proof.
You should test management claims with documents, metrics, walkthroughs, demos, and samples.
Some findings belong in valuation, holdbacks, covenants, or integration timing, not in a post-close wish list.
Your goal is a defensible picture of what you are buying, what must change first, and what can wait.
What digital technical debt really means in an M&A deal
In M&A, digital technical debt is the pile of shortcuts, weak controls, aging systems, and fragile workarounds that the target used to keep moving. Some of it is visible. Much of it sits behind stable revenue, loyal customers, and management confidence.
You should care about the business effect, not the engineering label. A brittle integration layer can slow synergy plans. Weak identity controls can turn day one into a cyber event. Poor data definitions can corrupt reporting after two systems merge. A sole-source vendor can control your timeline without your consent.
Some modernization work is normal. Every company has a backlog. The question is whether the backlog is manageable, or whether it hides liabilities that could disrupt growth, compliance posture, customer trust, or recovery after an incident. That is why leaders often need cybersecurity governance questions for boards that cut through reassurance.
The difference between fixable backlog and value-eroding liability
A fixable backlog item has a clear owner, a known cost, and a realistic plan. It may be annoying, but it does not threaten the deal thesis.
A value-eroding liability is different. It lacks ownership. It depends on one person. It has no real timeline. It creates outage risk, blocks integration, or raises regulatory and customer exposure. If a problem will consume executive attention for six months after close, it is no longer a minor technology issue.
Why technical debt stays hidden until late in the process
Seller optimism is one reason. Weak reporting is another. Also, many targets rely on outside providers or a few long-tenured insiders who keep things running through memory and habit.
Finance work usually dominates diligence. That makes sense, but it leaves room for shallow technical review, weak security testing, and unchallenged assumptions. By the time the truth surfaces, momentum is high and leverage is low.
The M&A due diligence checklist, where hidden digital liabilities usually show up
The biggest misses tend to appear in the same places. You should ask for proof, named ownership, and trend data in each one.
Core systems and architecture, what is old, fragile, or hard to integrate
Review ERP, CRM, custom apps, legacy servers, cloud sprawl, and the integrations between them. Look for unsupported software, manual file transfers, single points of failure, and systems that only one person understands.
Warning signs are simple. No current architecture map. No asset inventory you trust. No clear modernization path. No answer to what breaks if one service goes down.
Cybersecurity and resilience, what could become an immediate post-close surprise
Ask whether the target can detect, contain, and recover. Policies do not answer that. You need to see patching discipline, identity controls, endpoint visibility, incident logs, backup test results, and third-party exposure.
Prior events matter too. If the company had incidents, ask what changed after each one. A useful frame for this part of diligence is board incident response oversight, because post-close surprises often come from assumptions that were never tested.
Data quality and governance, what will undermine reporting, AI, and integration
Bad data slows almost everything after close. Look for duplicate records, weak lineage, inconsistent definitions, shadow spreadsheets, missing retention rules, and poor master data discipline.
If customer, product, and revenue data cannot be reconciled cleanly, integration will take longer and cost more. In addition, poor data governance can create privacy exposure you do not see in the first management deck.
Vendors, contracts, and hidden dependence you may be buying without realizing it
Review critical vendors, managed service providers, software licenses, and support agreements. Check for change-of-control clauses, auto-renewals, weak service levels, expensive renewals, and sole-source reliance.
This is not only a procurement issue. It is a control issue. If a vendor holds admin access, architecture knowledge, or recovery capability, then part of your operating model sits outside your control.
Team, operating model, and key-person risk that slides rarely reveal
Look past the org chart. You need to know who owns platforms, products, security decisions, and service recovery. Thin benches, low documentation, and burnout often hide under a stable-looking environment.
If the business runs because a few people remember how it works, you are buying dependence, not capability.
How to separate normal complexity from a real deal warning sign
No target is perfect. Your job is not to demand perfection. Your job is to judge severity well enough to price risk, sequence integration, and avoid preventable surprises.
Ask for evidence in five forms, documents, metrics, walkthroughs, demos, and samples
Each form of proof tells you something different. Documents show whether governance exists on paper. Metrics show trend and discipline. Walkthroughs reveal how work actually gets done. Demos expose hidden manual steps. Samples prove whether the stated process holds up in real artifacts.
Ask for architecture diagrams, asset lists, uptime trends, backlog aging, access reviews, incident logs, backup test reports, runbooks, and contract excerpts. Also ask for a live walkthrough of one critical workflow, such as order-to-cash or identity provisioning. Strong board-ready cybersecurity metrics work here because they translate technical detail into business impact.
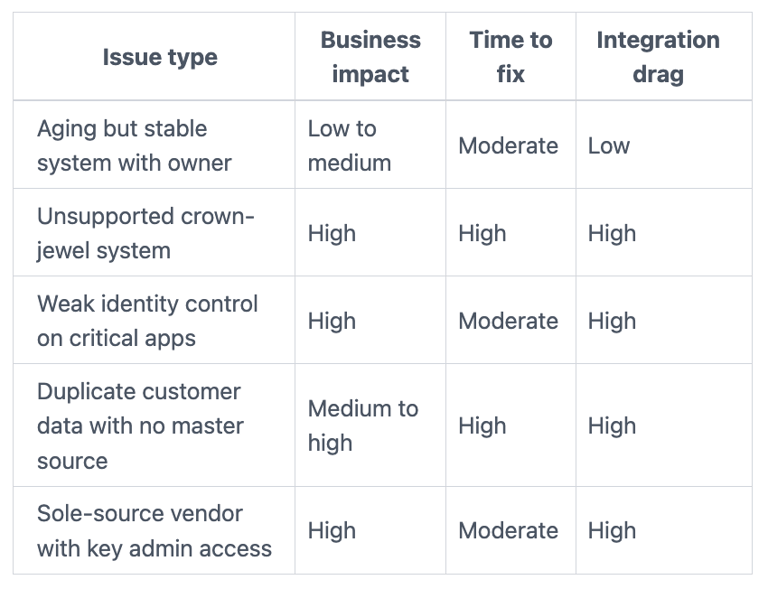
Rate each issue by business impact, time to fix, and integration drag
A simple screen helps you avoid overreacting to noise and underreacting to real risk.
The takeaway is simple. Issues get more serious when they affect revenue, trust, compliance, recovery, or the speed of integration. If you need a governance lens for those thresholds, audit committee cyber risk questions help sharpen challenge quality.
Questions leaders should ask before the deal closes
Good diligence questions should surface risk fast. They should also improve the quality of challenge in the room.
Questions to ask management when the target says the platform is stable
Use direct questions that force specificity:
What fails most often, and what is the business effect when it does?
What critical system depends on one person or one undocumented process?
What major upgrade has been delayed, and why?
What security issue would worry you most in the first 90 days after close?
What cannot scale without rework if growth accelerates?
Which manual workaround would you remove first if you had funding today?
If the answers stay broad, ask for proof. Stable businesses can still sit on fragile platforms.
Questions to ask when vendors seem to run too much of the business
Use a second set of questions when external providers appear to hold too much power:
Who owns the architecture, your team or the vendor?
Who controls admin access, logging, and backup settings today?
What happens if the vendor misses service levels for a week?
Where does system knowledge live if the vendor team changes?
Which contracts could limit pricing power or transition flexibility after close?
Those questions often reveal that vendor dependence is really an ownership problem.
What good looks like before you sign, and the next move if you find real technical debt
A strong diligence outcome is clear and calm. You have a risk register with ranked issues, named owners, costed remediation themes, known dependencies, and a realistic day-one and first-100-day plan. You also know which risks belong in price, which belong in holdbacks, and which should change integration order.
Good governance matters here because appetite and thresholds should be explicit before you inherit the problem. That is the logic behind board cyber governance practices. You want decision rights to be visible before pressure rises.
If you find real liabilities, act proportionately. Reprice if the cost is material. Use holdbacks if facts are still uncertain. Stage integration if the environment is fragile. Add remediation covenants if the seller must fix specific items before or after close. Replace or add leadership if ownership is missing. And if the deal logic no longer holds, walk away while you still can.
FAQs about M&A due diligence and technical debt
Is technical debt a reason to walk away?
Sometimes, yes. Most debt is manageable if cost, ownership, and timing are clear. You should walk when the liabilities are structural, the evidence is weak, and the remediation burden breaks the deal thesis.
How much technical diligence is enough for a mid-market deal?
Enough to understand crown-jewel systems, cyber readiness, data quality, vendor dependence, and key-person risk. You do not need a perfect catalog of every issue. You do need a clear view of what could hurt value in year one.
Who should own digital diligence?
The answer should be shared, but not vague. Deal leadership should own the decision. Technology, security, legal, finance, and operations should each test part of the operating truth. Boards and CEOs should push for clarity when the reporting feels too smooth.
Can you quantify technical debt before close?
You can estimate it in ranges. Start with remediation cost, integration delay, added staffing, vendor lock-in, and outage or exposure risk. Exact precision is rare. Decision-grade ranges are usually enough to change terms or sequence.
A clean deal is rare. A defensible view of the risk is possible.
Your next move is to use this M&A Due Diligence Checklist to separate normal complexity from inherited liability. Before close, you still have leverage. After close, you own the surprise.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
