The Clarity Audit: 5 signs your Board is getting "Technical Trivia" instead of risk data.
Use this clarity audit to see when board reporting turns into technical trivia, so you can spot risk, challenge ownership, and make decisions.


Your board can receive long cyber and technology updates and still lack a usable picture of risk. That happens more often than most leaders admit. The deck sounds serious, the charts look detailed, and the meeting feels active. Yet you still leave unsure what is exposed, what changed, and what decision matters now.
That gap is the issue. Your board does not need more technical output. It needs risk data that supports oversight. If reporting creates motion without judgment, you are getting technical trivia, not board-ready information.
Use this clarity audit before the next meeting. It will help you tell the difference fast.
Key takeaways from the clarity audit
Busy reporting can hide weak oversight.
Technical detail matters only when it changes a business decision.
A board update should show change, impact, ownership, and required action.
Raw counts rarely tell you how exposed the business is.
Weak board visibility slows decisions and creates false comfort.
Better reporting helps you challenge timing, funding, risk acceptance, and escalation.
If your board cannot tell what changed, why it matters, and what decision is needed, the reporting is failing.
Why technical trivia is a board problem, not just a reporting problem
When reporting misses the mark, the problem does not stay in the slide deck. It shows up in governance. You get slower decisions, softer challenge, and more surprise when pressure rises. That is why strong board cyber governance best practices start with clarity, not volume.
Boards often assume that detailed reporting means strong control. Sometimes it does. Often it means the opposite. A team can present dozens of metrics and still avoid the hard question, "What business risk remains, and who owns it?"
When reports sound busy, boards often assume control is stronger than it is
Volume creates comfort. A dashboard with blocked attacks, closed tickets, patch totals, and program updates can make the room feel informed. However, none of that proves material exposure is shrinking.
You can hear plenty of operational motion while ownership stays fuzzy. You can see lots of green while risk is drifting upward. You can get more data and less visibility at the same time.
That false comfort is expensive. It delays escalation, weakens scrutiny, and lets unresolved exposure sit in plain view.
If your board cannot tell what changed, what matters, and what needs a decision, the reporting is failing
Board reporting should support three outcomes.
First, you should see what changed since the last meeting. Second, you should understand what it means for the business. Third, you should know what decision or challenge belongs with the board.
That is a simple standard. It also aligns with better cyber risk board reporting, where the point is not to display technical depth. The point is to help you govern with a clear line of sight.
The 5 signs your board is getting technical trivia instead of risk data
You can usually spot the problem without a maturity review. It shows up in board packets, committee updates, and executive briefings. The signs are practical, visible, and hard to miss once you know what to look for.
Sign 1, the update is full of metrics, but none of them show business exposure
Patch counts, blocked attacks, tickets closed, scan volume, and tool uptime can show effort. They rarely show exposure on their own.
Your board needs a different view. What asset or process is at risk? How severe is the likely impact? What revenue stream, service, legal duty, or customer promise could break? Without that translation, the board sees work, not risk.
A useful update tells you what could be disrupted and how much that matters.
Sign 2, the reporting describes activity, but not trend or movement
Point-in-time updates create noise. You hear what happened this month, but you cannot tell if risk is rising, flat, or getting worse.
Trend changes the conversation. It tells you whether remediation is closing exposure, whether exceptions are piling up, and whether the business is moving outside its approved technology risk appetite. A static snapshot cannot do that.
Boards need movement, not moments. If the line is drifting the wrong way, you should see it early.
Sign 3, technical terms are doing the work that clear judgment should be doing
Acronyms, severity labels, product names, and architecture language often fill space where judgment should sit. That forces directors to guess.
When a report says "critical vulnerabilities remain in a segmented environment," you still need translation. How likely is harm? What kind of harm? How fast could it matter? Who owns the fix? If those answers are missing, jargon is carrying more weight than it should.
Clear reporting converts technical facts into business meaning. It does not ask the board to decode them.
Sign 4, every problem seems urgent, so nothing is clearly prioritized
Some board decks present a long list of issues, all flagged as serious. That creates heat, not clarity.
Prioritization is not cosmetic. It is a management signal. When the board cannot see why one issue matters more than another, you cannot judge tradeoffs, timing, or funding. You also cannot test whether management is making disciplined choices under constraint.
If every item is red, the report is unfinished. The board needs ranked exposure, materiality, and a reason for the order.
Sign 5, the board hears updates, but does not know what management needs from them
Information alone does not create oversight. Decision support does.
A strong update tells you whether management needs approval, challenge, escalation, funding, or formal risk acceptance. It may also tell you that management needs nothing from the board right now. That clarity matters too.
This is especially important in incident settings. Good board incident response oversight depends on clear decision rights before the pressure rises. If the board hears an update and still cannot tell its role, the briefing is incomplete.
What useful board risk reporting looks like instead
The better model is simpler than most teams expect. Start with the business risk. Then add only the technical detail needed to support judgment.
This quick comparison helps:
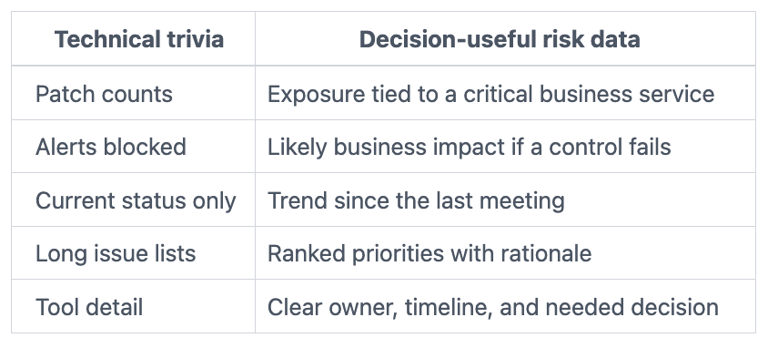
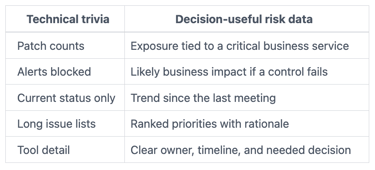
Start with business risk, then use technical detail only when it changes the decision
Lead with the business process, asset, dependency, or strategic exposure. Then explain the technical facts that change how you should judge that exposure.
That order matters. If you begin with tools, the board has to translate. If you begin with business risk, the board can assess impact, tradeoffs, and urgency in minutes.
Useful reporting is shorter because it is better structured. It helps you decide faster.
Make ownership, trend, and next decision impossible to miss
Every board-ready update should answer five things: what changed, why it matters, who owns it, where the trend is heading, and whether a board or committee decision is needed now.
If those fields are visible, your oversight gets stronger fast. If they are buried, the board spends meeting time searching for the basics.
A simple clarity audit you can use before the next board meeting
You do not need to blame the team to improve the reporting. Start by pressure-testing the deck.
Ask these five questions before you accept the next cyber or technology update
What business risk does this item show?
What changed since the last meeting?
Where is ownership clear, and where is it weak?
What is being prioritized, and why?
What decision, challenge, or approval is needed from the board?
Those questions work well in board and audit settings. They also align with sharper audit committee cyber questions when you need to test whether a plan or update is decision-ready.
Fix the reporting first, and your oversight usually gets better fast
Most boards do not need more slides. They need stronger reporting discipline.
When reporting improves, several things happen quickly. Ambiguity drops. Escalation gets cleaner. Management has to rank issues. The board can challenge with more precision. Trust improves because the conversation is grounded in evidence and decisions.
FAQ
Is technical detail ever appropriate for the board?
Yes, when it changes a decision. If a technical fact affects likelihood, impact, timing, or recovery, it belongs in the update. If it does not, it usually belongs in management reporting.
How often should cyber risk be reported to the board?
You should see a steady cadence, not a scramble after bad news. Most boards benefit from regular dashboard reviews and deeper quarterly discussions on major exposure, trend, and decisions.
What should management do if the board asks weak questions?
Management should still bring the clearer frame. Show business impact, trend, ownership, and the decision needed. Good reporting can raise the quality of board oversight even before the board asks better questions.
Who should own board-level cyber risk reporting?
Management owns the content, but one executive should own the final story. That person should be able to connect technical reality to business exposure, explain tradeoffs, and state what the board needs to decide.
Good board reporting does not prove how much the team knows. It helps you see risk clearly enough to govern. That is the standard that matters.
Before the next meeting, review the deck through this clarity audit. Remove anything that adds detail without improving judgment. Keep what shows change, impact, ownership, and decision.
When you do that, the room usually changes. The discussion gets shorter, sharper, and more useful. That is what board reporting should do.
About the author: Tyson Martin advises boards, CEOs, and executive teams on cyber risk, technology governance, AI oversight, and decision clarity during growth, incidents, and transition.
Sources referenced: Internal TysonMartin.com resources on board reporting, technology risk appetite, incident oversight, governance, and audit committee cyber questions.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
