Technology Risk Appetite Boards Must Define Before Crisis
Define technology risk appetite before crisis hits, so you can set board guardrails for downtime, data loss, vendor risk, and AI use.


Technology risk appetite is the level and type of technology risk you are willing to accept to pursue growth, speed, efficiency, and innovation. At the board level, that means deciding in advance what business impact is acceptable, what is not, and when management must escalate.
If you do not define that ahead of time, something else will define it for you. A cyber event will do it. A vendor failure will do it. A bad AI use case, a major outage, or a rushed launch will do it. And they will define it at the worst possible moment, when options are narrow and pressure is high.
This is not only a security issue. It is a governance issue and a decision issue. Your board, CEO, and executive team need clear boundaries before the next hard call arrives.
Key takeaways
A technology risk appetite tells management what tradeoffs you will accept, and which ones cross the line.
Vague language creates slow decisions, weak escalation, and false confidence.
Most boards discover their real appetite during a crisis, because they never defined it in calm conditions.
You need clear boundaries for downtime, data loss, vendor dependence, and AI use.
Appetite only works if decision rights, escalation triggers, and reporting thresholds are explicit.
Good board oversight links risk appetite to strategy, budget, and board conversation quality.
What technology risk appetite really means at the board level
At the board level, technology risk appetite is not about removing all risk. It is about setting boundaries, tradeoffs, and escalation thresholds in business terms.
Without an appetite statement, risk gets accepted by drift. Teams delay fixes. Exceptions stay open. Vendors become too important. AI tools get used before rules exist. Then leadership acts surprised when a problem lands in the boardroom.
A vague appetite statement is only slightly better. Phrases like "low risk" or "strong controls" sound polished, but they do not guide action. They do not tell management how much downtime is acceptable, what data exposure is intolerable, or when a vendor issue must come to the board.
A useful statement helps you make choices. It connects risk to uptime, customer trust, legal exposure, vendor dependence, AI use, and growth plans. If your company wants faster product delivery, more automation, or heavier use of third parties, your technology risk appetite should say what those choices can and cannot put at risk.
If you want a deeper view of boards setting tech risk thresholds, start there. The point is simple: you are not writing a slogan. You are defining guardrails.
Risk appetite is not the same as risk tolerance or risk capacity
Boards often mix up three terms, and that weakens oversight.
Risk appetite is what you choose to accept in pursuit of business goals. Risk tolerance is how much variation from that target you can live with. Risk capacity is the maximum hit the business could survive.
Those differences matter. If you confuse them, you may approve a growth strategy that assumes more downtime, data loss, or vendor concentration than the business can actually absorb. Or you may demand controls that slow the business without reducing the biggest exposures.
A useful appetite statement gives management clear guardrails
A practical appetite statement should do four things. It should guide investment. It should speed up routine decisions. It should define when issues come to the board. It should reduce case-by-case guessing.
That also means it must be measurable enough to shape reporting. If your appetite cannot show up in dashboards, escalation rules, and exception handling, it is not ready for real use.
Why boards often discover their real appetite in the middle of a crisis
Most boards do not enter a crisis blind because they ignored risk. They enter blind because reporting was weak, ownership was blurry, and growth pressure hid the drift.
You can look busy and still lack control. Board decks can be full of program updates, tool counts, and project lists while saying almost nothing about decision thresholds. Management may believe it has risk "covered," even as exceptions pile up, legacy systems stay fragile, vendors gain influence, and AI use expands faster than governance.
That is how false confidence forms. The business grows. The technology stack gets more tangled. The board hears activity, not exposure.
For a sharper lens on cyber risk board reporting, focus on business impact and decision use, not technical volume.
The warning signs are usually visible long before the event
The signs are rarely hidden. You usually see recurring exceptions, unresolved audit findings, single points of failure, poor incident escalation, and unclear data ownership.
You also see board materials that describe effort but not risk movement. When every slide says progress and nothing says threshold breach, you should assume visibility is weaker than it looks.
Under pressure, default decisions become your de facto risk appetite
When pressure rises, your defaults tell the truth. Delays, shortcuts, underfunding, and soft escalation reveal what the organization is willing to accept.
Silence is still a decision. So is "we'll fix it later."
If a critical vendor has no backup, if high-risk exceptions stay open for months, or if legal and reputational AI issues never reach the board, you already have an appetite. You just never chose it on purpose.
What boards need to define now, before they need it urgently
You do not need a long binder. You need a clear operating position.
Start with the exposures that can hurt the business fastest: downtime, data loss, third-party dependence, and AI use. Then define decision rights, escalation triggers, and reporting thresholds that match those exposures. That is where board cyber governance practices become real.
This simple framework helps separate drift from governance:
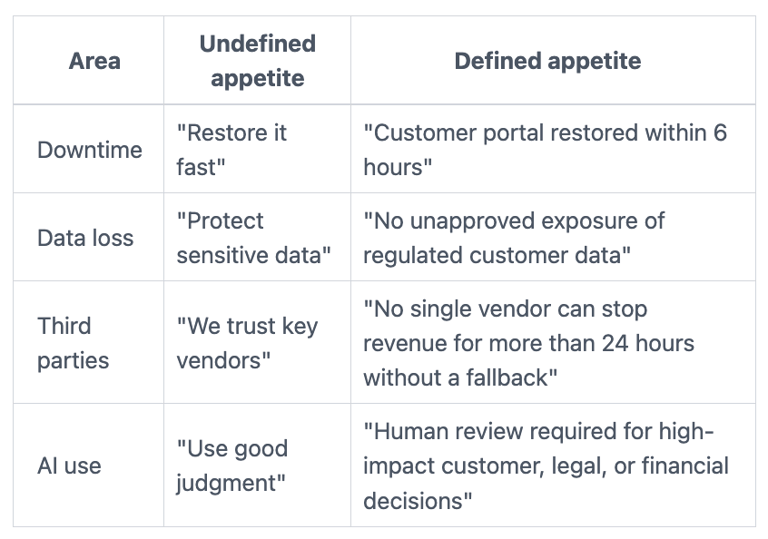
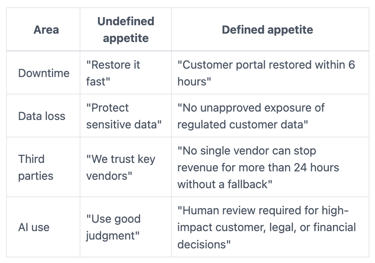
The board does not need to set technical controls. You do need to define acceptable business exposure.
Set boundaries for downtime, data loss, third-party dependence, and AI use
For downtime, decide how much disruption is acceptable for each critical service. Not in adjectives, in hours.
For data loss, define which data types need the strongest protection and what kinds of exposure are off-limits. Regulated data, customer identity data, payment data, and sensitive internal data should not sit in the same category.
For third parties, set limits on concentration risk. If one vendor failure can halt revenue, payroll, service delivery, or compliance, that is a board issue.
For AI, decide where human review is required, what data can be used, and which use cases carry legal, trust, or brand risk. Fast adoption without limits is not speed. It is deferred accountability.
Define decision rights, escalation triggers, and reporting thresholds
A risk appetite is only real if someone knows who decides what.
You need named decision rights for risk acceptance, exception approval, outage tradeoffs, and high-impact AI use. You also need escalation triggers that are pre-set, not improvised in a bad week.
Typical triggers include material incidents, critical system outages, major vendor failures, exceptions that exceed agreed limits, and AI use cases with legal or reputational impact.
That is also why board incident response oversight matters. If your escalation path is unclear before an event, it will break during one.
What good technology risk appetite looks like in practice
Good technology risk appetite is not policy theater. It is a working leadership tool.
You see it when the board and management make faster, cleaner, more defensible decisions. You see it when funding requests tie back to agreed business exposure. You see it when exception handling gets tighter, because no one has to guess where the line sits.
Good appetite statements are tied to strategy, not written as policy theater
Your statement should reflect where the company wants to grow and what it cannot afford to lose.
If your strategy depends on digital channels, uptime matters more. If growth depends on customer trust, data handling matters more. If M&A is likely, integration and vendor exposure matter more. If AI is becoming part of service delivery, oversight rules need to exist before reputational damage forces them into place.
A good statement should sound like strategy with boundaries, not compliance language.
The best test is whether it changes budget, priorities, and board conversations
You know appetite is working when it changes behavior.
Investment decisions get easier because tradeoffs are clearer. Dashboards improve because they track agreed thresholds. Board discussions get shorter and sharper because the guardrails are already approved.
If you want better challenge in committee settings, these audit committee cyber questions are useful because they force ownership, thresholds, and proof into the open.
Questions boards should ask now, plus a short FAQ
Use these questions to pressure-test whether your technology risk appetite is defined and usable:
Can management state our current technology risk appetite in plain business terms?
What downtime, data loss, or vendor dependence is outside appetite today?
Who can approve exceptions, and how long can they remain open?
What triggers require board escalation within 24 hours?
Where are AI use cases moving faster than governance?
Which board reports show drift against approved thresholds, not only activity?
A short test helps here. If answers are vague, your appetite is weak. If answers are measurable, ownership is clearer.
FAQ
How often should you review technology risk appetite? At least once a year, and sooner after major growth, M&A, incidents, platform changes, or new AI use cases.
Who should own the first draft? Management should draft it, often led by the CEO with technology, security, legal, and operations input. The board should challenge and approve it.
Does a mid-market company need a formal statement? Yes, if technology failure, vendor issues, cyber events, or AI misuse can create material business harm. Mid-market companies often have less margin for error, not more.
The next move before pressure takes it away
If you wait, a crisis will set your technology risk appetite for you. It will do it through delay, cost, confusion, and public consequence.
A better path is simpler. Review your current reporting. Identify missing thresholds. Ask management to bring a draft appetite statement, tied to business strategy, to the next board meeting.
That is not paperwork. It is a leadership tool. When pressure hits, clarity is what keeps your options open.
About the author
Tyson Martin advises boards, CEOs, and executive teams on technology, cyber, AI, and governance decisions when the stakes are high and visibility is weak.


