Cybersecurity Governance for Boards: What Good Oversight Actually Looks Like
Learn what strong cybersecurity governance for boards looks like, so you can clarify ownership, improve reporting, and reduce avoidable surprises.


Good board oversight does not mean you run the security program. It means you make sure cyber risk is visible, owned, discussed in business terms, and tied to decisions. If that sounds obvious, look at how many companies still learn the hard way that vague ownership and weak escalation create blind spots.
When cybersecurity governance for boards is weak, surprises build quietly. Management reports activity, but not exposure. Leaders assume someone else owns key decisions. Then an outage, breach, vendor failure, or disclosure issue forces the board to react without a shared picture of what matters most.
That is the difference between checking a box and governing well. Strong oversight gives you clear thresholds, better reporting, and fewer "how did we miss this?" moments. It helps your CEO and executive team lead with less guesswork, especially when pressure rises.
Key takeaways boards can use right away
Your board owns oversight, risk tolerance, and escalation expectations. Management owns execution.
Good reporting should show top risks, trend lines, business impact, and decisions needed, not only technical activity.
If no one can name who owns a material cyber risk, you have a governance problem.
Passing audits may reduce noise, but it doesn't prove you understand operating exposure.
Incident oversight starts before the crisis, with agreed triggers, roles, and briefing rules.
If your board packet can't show what changed since last quarter, you're not seeing governance clearly.
Why cybersecurity governance for boards has become a leadership issue, not just an IT issue
Cyber risk now reaches into revenue, operations, trust, legal exposure, and deal readiness. It also touches AI use, cloud dependence, and critical vendors. Because of that, cybersecurity governance for boards is no longer a side topic for the technology team.
You are not expected to be a technical expert. You are expected to oversee whether the company can operate safely, recover quickly, and make sound decisions when facts are incomplete. That is a leadership duty, not an IT specialty.
As companies scale, the stakes rise. A weak identity model can slow growth. A fragile vendor can stall integration. Poor recovery planning can turn a contained incident into a business crisis. If you want clearer structure for board-level oversight, board cyber governance practices offer a useful companion view.
What changes when cyber risk starts affecting growth, trust, and resilience
A cyber issue becomes a board issue when it can stop the business from doing what it promised. That may mean missed revenue, customer churn, delayed product launches, regulatory attention, or a weaker position in diligence.
This shift matters because boards govern tradeoffs. You decide how much disruption is tolerable, what risks require escalation, and where management needs support or challenge. In other words, you don't need to know every control. You need to know whether leadership is steering with a clear map.
Why many boards still feel under-informed even when they get regular updates
Most boards aren't starved for data. They're starved for useful meaning. Reports often include too much technical detail, no clear trend view, and no line between what management can handle and what needs board attention.
You may also see dashboards with no thresholds, no context, and no business impact. That leaves you hearing about patch counts, training rates, or tool rollouts without knowing whether the company is getting safer. If your reporting still sounds busy but not decision-ready, this guidance on effective cyber briefings for directors helps sharpen what the board should ask for.
What good board oversight actually looks like in practice
Good governance is a working system. It is not a policy binder, an annual slide deck, or a once-a-year tabletop. You know it is working when ownership is clear, risk moves visibly, and escalation happens before confusion takes over.
This quick comparison makes the difference easier to see:
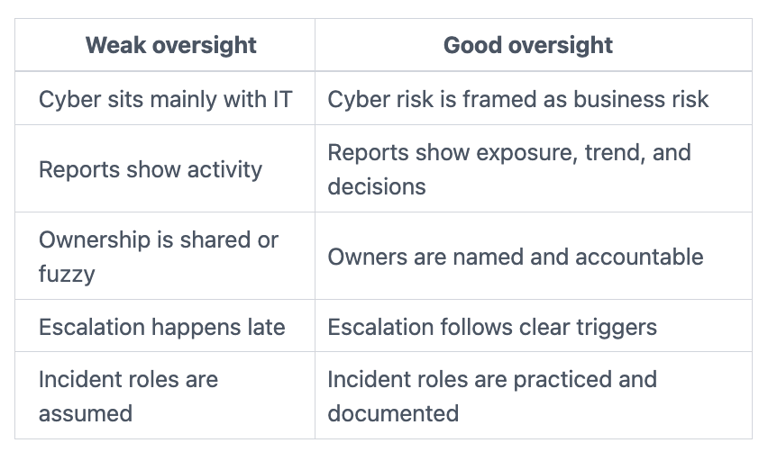
The goal is not perfection. The goal is a board that can see what matters and act in time.
Clear roles, clear decisions, and no confusion about ownership
The board governs. Management executes. Legal, operations, security, communications, and business leaders each own part of the outcome. When that sounds simple but feels blurry in practice, trouble usually follows.
Blurred ownership slows decisions. It also creates false comfort. During calm periods, people assume alignment. During pressure, those assumptions break fast.
You want visible accountability across the chain. Who owns the top cyber risks? Who can accept temporary risk? Who decides whether to shut down a critical system? Who briefs the board? If those answers change by meeting, your governance model is unstable.
If you need a sharper structure for risk appetite and thresholds, technology risk appetite is where many boards find clarity first.
Board reporting that shows risk, movement, and decisions needed
Useful reporting answers four things quickly: what matters most, what changed, what remains exposed, and what decisions are needed now. Dashboards can help, but only if they support judgment.
A good board packet should show top risks in business terms, movement over time, material incidents or near misses, key control gaps, third-party exposure, and the current state of recovery readiness. It should also say what management recommends and what happens if action slips.
If a report can't tell you what judgment is needed, it is not board-ready.
That is why trend matters more than volume. You need movement, not noise.
Escalation rules and incident oversight before a crisis hits
A mature board does not wait for a breach to define escalation. You set the rules in advance. What gets escalated, when, by whom, and in what format should be settled before pressure hits.
This is strategic work. It is about decision rights, not technical playbooks. The board should know what it expects to see during a serious incident, including current impact, actions underway, key uncertainties, and next update time.
If you want a practical model, board incident response oversight shows how to remove assumptions before they become expensive.
Where oversight usually breaks down, even in well-run companies
Governance failures often appear in companies that look disciplined from the outside. People are working hard. Reports arrive on time. Audits get completed. Still, the board lacks a defensible picture of risk.
That gap usually comes from design problems, not bad intent. The system rewards motion, not clarity. It produces updates, not decisions. It treats cyber as a specialist subject instead of an enterprise risk that needs ownership, thresholds, and follow-through.
Compliance gets reported, but real exposure stays blurry
Compliance can be useful. It creates structure and proof. Still, it does not automatically tell you whether the company understands its true operating risk.
You can pass an audit and still have weak recovery. You can meet a requirement and still depend too heavily on one vendor. You can complete training and still have poor escalation. Compliance may tell you the company met a standard. It may not tell you what would hurt the business next.
The board hears activity, but not whether the company is getting safer
This is one of the most common failure patterns. Management reports how many tickets were closed, how many systems were patched, or how many people completed training. Those things may matter. Still, they don't answer the board's real question: are you reducing business exposure?
You want to hear about risk reduction, recovery strength, and where the company is drifting out of bounds. If not, the board may confuse effort with progress.
The questions you should ask to test whether oversight is strong
You do not need more abstract discussion. You need sharper questions before the next board or audit committee meeting. Strong questions expose whether governance is real or only described well.
Questions about ownership, reporting, and decision rights
Start with ownership. Who owns each material cyber risk, by name and role? Then ask what changed since last quarter, not what the team worked on. That shift matters because it forces management to show movement.
Next, ask which risk decisions need leadership input now. You are looking for tradeoffs, deferred work, accepted risks, and areas where accountability is weak. If every answer points back to "the security team," the governance model is still too narrow.
For committees that want a tighter agenda, these audit committee cyber questions are useful because they keep the focus on business consequence.
Questions about readiness, resilience, and third-party exposure
Readiness starts with assumptions. What are your recovery assumptions, and when were they last tested? Which vendors could stop critical operations? What concentration risk sits outside your walls? Has leadership practiced its response with legal, operations, and communications in the room?
You should also ask whether reporting reflects dependency risk from cloud, software providers, and outside service firms. Many boards think they are reviewing internal risk when the biggest exposure sits in a contract, a vendor login, or a recovery gap.
Shared responsibility does not mean shared accountability. If the business suffers, you still own the oversight problem.
FAQ: short answers to the board questions that come up most
Does your board need a cyber expert?
Not every board needs a full-time specialist, but every board needs access to credible cyber judgment. If oversight remains fuzzy, an independent Board Cyber Risk Advisor can help clarify thresholds, ownership, and escalation fast.
How often should cyber be on the board agenda?
Cyber should appear often enough to show movement, not only after incidents. In many companies, that means regular dashboard review with deeper quarterly discussion.
What should you do if reporting is weak?
Ask management to redesign the packet around business impact, top risks, trend lines, and decisions needed. Do not accept more slides as the fix.
Should the full board or the audit committee own this?
Either can work. The key is clarity. Committee review can go deeper, but the full board still needs visibility into material risk and major decisions.
Good cybersecurity governance for boards is not about becoming more technical. It is about becoming more disciplined. You want visibility, ownership, escalation, and reporting that helps you decide.
Before your next meeting, do three things. Clarify the thresholds for escalation. Tighten the board packet so it shows risk movement and decisions needed. Then identify one area where accountability is still blurry and fix it while the room is calm.
That is how you reduce avoidable surprises. That is how oversight becomes credible.
Tyson Martin advises boards and CEOs on cyber risk, technology governance, and decision-making under pressure. His work focuses on helping leaders make clearer, faster, and more defensible calls when risk, growth, and trust intersect.
Sources referenced in this article are drawn from TysonMartin.com board and governance resources.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
