When to Bring in a Board Cyber Risk Advisor, and What to Expect
Learn when to bring in a Board cyber risk advisor, what you'll gain in 90 days, and how stronger oversight improves board decisions before a crisis.


You should bring in a Board cyber risk advisor when cyber risk becomes a leadership, governance, or trust issue, not only an IT issue. In most companies, the trigger is simple: the board is accountable, but visibility is weak, ownership is blurry, business exposure is rising, or a major change has raised the stakes.
That point often arrives before a crisis. Growth, AI adoption, vendor dependence, executive turnover, and weak reporting can all push oversight behind reality. When that happens, more dashboards won't fix it. Better judgment will.
The goal is not drama. The goal is clarity, timing, and decisions you can defend.
Key takeaways for busy leaders
The best time to bring in a board cyber risk advisor is before a crisis forces the issue.
Common trigger moments include growth, M&A, incidents, leadership gaps, weak reporting, AI adoption, and rising vendor risk.
The advisor should improve decision quality and board visibility, not replace management.
A strong engagement should lead to clearer questions, better reporting, sharper priorities, and more defensible oversight.
If cyber is shaping trust, uptime, transactions, or board accountability, the issue is already bigger than IT.
The right time to bring in a board cyber risk advisor is usually earlier than you think
Most companies wait too long because cyber still gets framed as a technical topic. That framing is costly. By the time the board feels urgency, the business has often been carrying hidden exposure for months.
The better move is to act when oversight starts falling behind complexity. That may show up in confusing board materials, rising dependence on key vendors, or management teams that are moving fast without clear escalation rules. At that point, you do not have a tooling problem. You have a governance problem.
Bring one in when the board is accountable but cannot see clearly
If your board packet is full of activity but short on meaning, you are already in the zone where outside help can pay off. Many cyber updates are busy, yet not decision-useful. They show counts, projects, and program motion, but not trend, business impact, or what needs a board call.
That weak visibility leaves directors in a bad place. You cannot challenge management well. You also cannot support management well. You leave the meeting with more noise, not more clarity.
If the board can't see cyber risk in business terms, it can't govern it well.
This is often where sharper board cyber reporting in business terms becomes the first fix.
Bring one in when growth, AI, or vendor dependence changes the risk picture
Growth changes risk. So does AI. So does outsourcing core functions to a handful of vendors. None of that is bad on its own. The problem starts when business speed outpaces oversight maturity.
You may be adding systems, moving data faster, relying on outside platforms, or letting AI tools touch sensitive work before governance has caught up. In those moments, the board needs a better view of thresholds, tradeoffs, and what has become material. A useful starting point is clearer technology risk appetite for boards, because without it, management is left guessing where the guardrails really are.
The clearest trigger points are moments when the business cannot afford guesswork
When the cost of being wrong rises, the need for independent board-level cyber judgment usually rises with it. That is the simplest test.
You do not need a permanent advisor every time something changes. However, high-stakes moments often expose weak ownership, weak reporting, and weak assumptions all at once. That is exactly when boards benefit from a calm outside view.
After an incident, near miss, or hard question from the board
After an event, the risk is not only technical harm. The risk is confusion. Panic can distort judgment. Defensiveness can distort reporting. Leaders may promise fixes before they have named root causes.
A board cyber risk advisor helps you separate signal from noise. You get an independent read on what happened, what changed, what still feels untested, and whether lessons learned were real or only well-presented. This is also where stronger board incident response oversight can keep you from repeating the same decision failures under pressure.
During M&A, executive transition, fundraising, or major transformation
Transactions and transitions are where hidden cyber risk gets expensive fast. During M&A, the issue may be weak diligence or inherited vendor exposure. During an executive transition, it may be unclear ownership or missing judgment at the top. During fundraising, it may be trust, disclosure, or readiness under scrutiny.
These are not good moments for guesswork. An outside advisor can help the board test readiness, challenge soft assumptions, and identify what must be true before you move forward.
What a strong board cyber risk advisor should actually do for you
A good advisor improves oversight. They do not replace your CISO. They do not run tools. They do not arrive with a thick deck and more process for its own sake.
Instead, they help you ask better questions, interpret risk in business terms, tighten decision rights, and improve how management and the board work together. That is why the role sits closer to governance than operations. If you want a simple reference point, this is the practical value of a Board Cyber Risk Advisor.
Translate cyber risk into board decisions, not technical theater
The role should turn technical complexity into business consequences, tradeoffs, and choices. What matters now? What changed? What belongs with management, and what belongs with the board? Those are the questions that matter.
You should expect the advisor to reduce ambiguity. A useful discussion ends with clearer thresholds, cleaner options, and less confusion about who decides what. That is also the heart of stronger board cyber governance practices, because governance is not information volume. It is decision quality.
Improve reporting, accountability, and escalation paths
You should also expect practical outputs. Reporting should get shorter and more useful. Meeting agendas should become more focused. Ownership should get less blurry. Escalation should rely less on personalities and more on agreed triggers.
That is where value becomes visible. The board starts getting what it needs. Management starts understanding what the board needs. Friction drops, not because risk disappeared, but because accountability is clearer.
What to expect in the first 90 days, and how to tell if it is working
The first 90 days should not feel like a long audit. You should see visible progress early. The advisor will usually review reporting, governance structure, decision rights, incident readiness, major dependencies, and the way management currently describes cyber risk.
That early work should reveal where visibility is weak, where assumptions have not been tested, and where the board needs sharper questions.
Here is a simple way to think about the first phase:
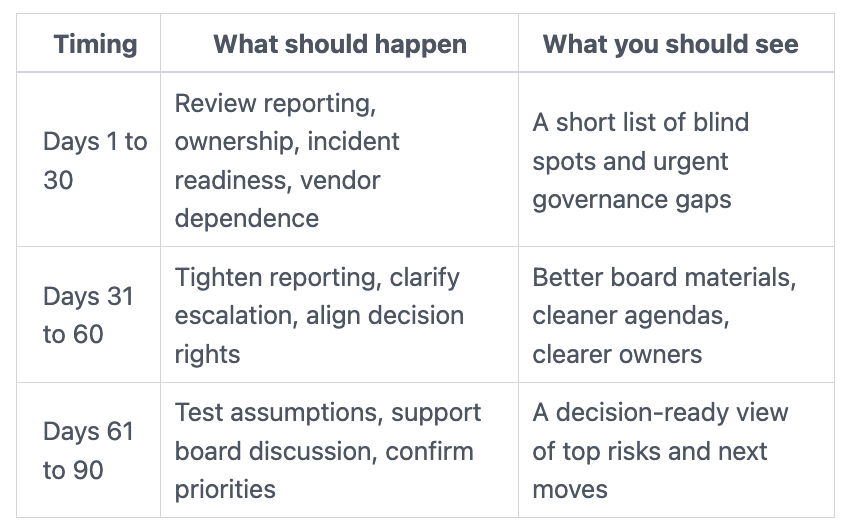
The point is not perfection. The point is a stronger operating picture.
What the first meetings and review work should uncover
Early meetings should show where reporting hides more than it reveals. They should expose where ownership is shared so widely that no one is truly accountable. They should also show whether incident readiness is a binder on a shelf or something leadership can actually execute.
In addition, you should learn how cyber risk connects to business exposure. Which vendors matter most? Which systems create trust risk, revenue risk, or downtime risk? Which issues are drifting upward without a clear decision? Those are board-level questions.
The signs the engagement is creating real value
You will know it is working when conversations get clearer. Reports usually get shorter. Management becomes more direct about tradeoffs. Priorities become easier to defend. Leaders feel less exposed to surprise.
Success does not look like more fear. It looks like more confidence grounded in evidence. If the role is working well, you spend less time trying to decode the story and more time making sound decisions.
Questions leaders often ask before bringing one in
Do you need a board cyber risk advisor if you already have a CISO or security team?
Sometimes, yes. The need is often not about operating the security program. It is about independent board-level interpretation, governance design, and decision support.
A good advisor should strengthen management, not undermine it. In many cases, they help the CISO communicate more clearly and help the board challenge more usefully. If your committee wants sharper prompts, focused cyber questions for the audit committee can help expose where oversight is still thin.
Should the advisor be temporary, ongoing, or tied to a specific event?
It depends on the trigger. Some companies need support through a transaction, incident recovery, or leadership gap. Others need periodic board support as complexity grows.
You should match scope to need. If the issue is a forcing event, a defined engagement may be enough. If the issue is persistent weak oversight, a steadier cadence often makes more sense.
Cyber risk becomes a board problem long before the crisis headline. Your next move is simple: assess whether the board has clear visibility, useful reporting, defined ownership, and enough independent judgment to govern cyber risk well.
If those pieces are weak, do not wait for the next incident, deal, or hard board question to expose it. If cyber risk is already shaping business decisions, trust, recovery, or board accountability, it is time to consider a Board cyber risk advisor before the next forcing event makes that choice for you.
Tyson Martin advises boards and CEOs on cyber risk, technology governance, AI oversight, and decision-making under pressure. His work helps leaders improve visibility, clarify ownership, and make clearer, faster, more defensible decisions when the stakes rise.
Providing plain-English technology oversight to help Boards and CEOs lead with confidence and make defensible risk decisions.
© 2026. All rights reserved.
Navigation
Free Resources
Contact


Stay ahead of your next board agenda
Sign up for Reports & Learnings From the Boardroom. Plain-English AI and cyber governance insights, biweekly. No pitch.
No spam. Unsubscribe anytime. · Or download the Director's AI Question Pack — 25 questions free
